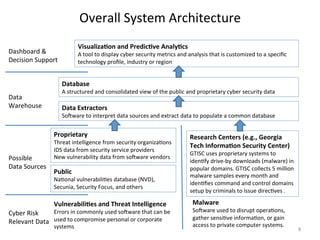
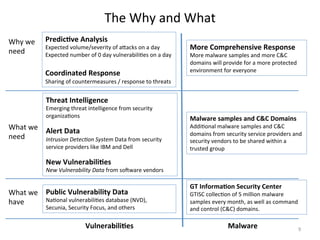
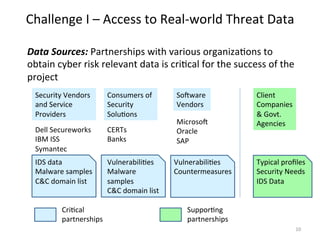
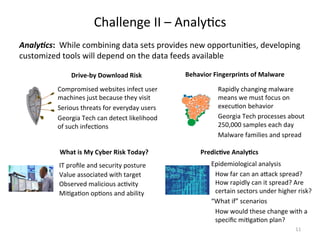
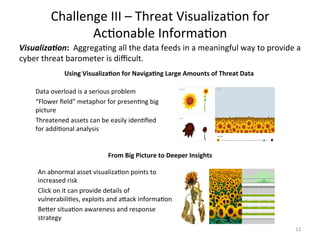
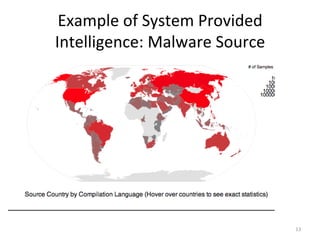
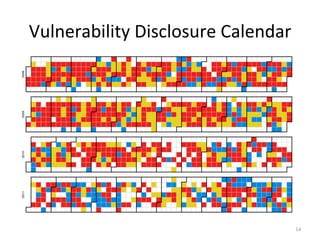
The document discusses the challenges in assessing and mitigating cyber risk, highlighting the need for a data-driven approach to enhance response to emerging threats. It emphasizes the importance of partnerships to collect cyber risk data from multiple sources and developing tools for threat analysis and visualization. Key questions are raised about relevant data, sources, and the value of cyber risk tools in providing actionable information for better understanding and managing these risks.

![Talking
About
Cyber
Risk
• Risk
=
Prob.[adverse
event]*Impact[adverse
event]
• AQacks
occur
when
threat
sources
exploit
vulnerabili;es
• Mean-‐;me-‐to-‐compromise?
• Mean-‐;me-‐to-‐recover?
(assuming
detec;on)
• Tradi;onal
assump;ons
and
solu;ons
do
not
apply.
3](https://image.slidesharecdn.com/ahamadcyber-risktalk-150411045324-conversion-gate01/85/Data-Driven-Assessment-of-Cyber-Risk-Challenges-in-Assessing-and-Migrating-Cyber-Risk-3-320.jpg)