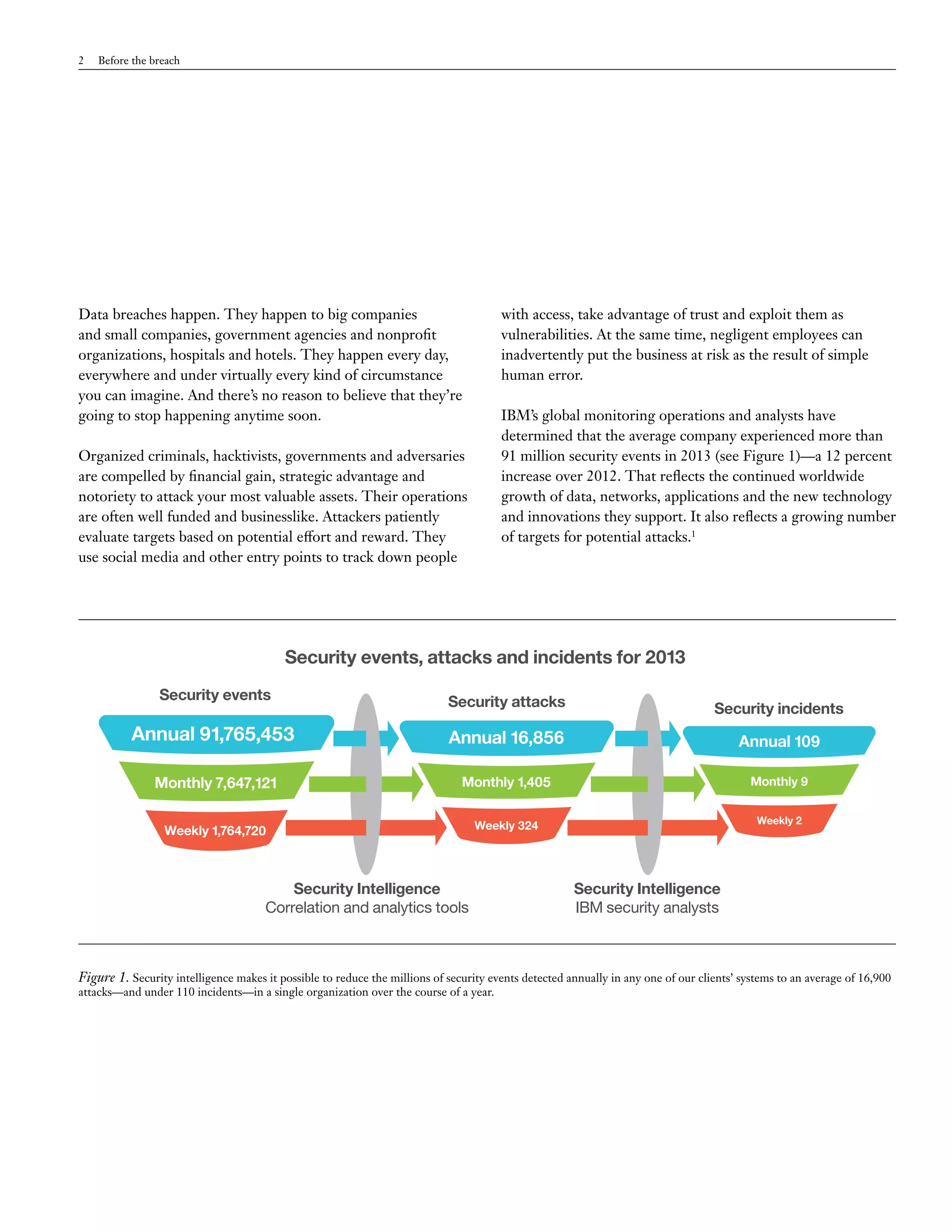
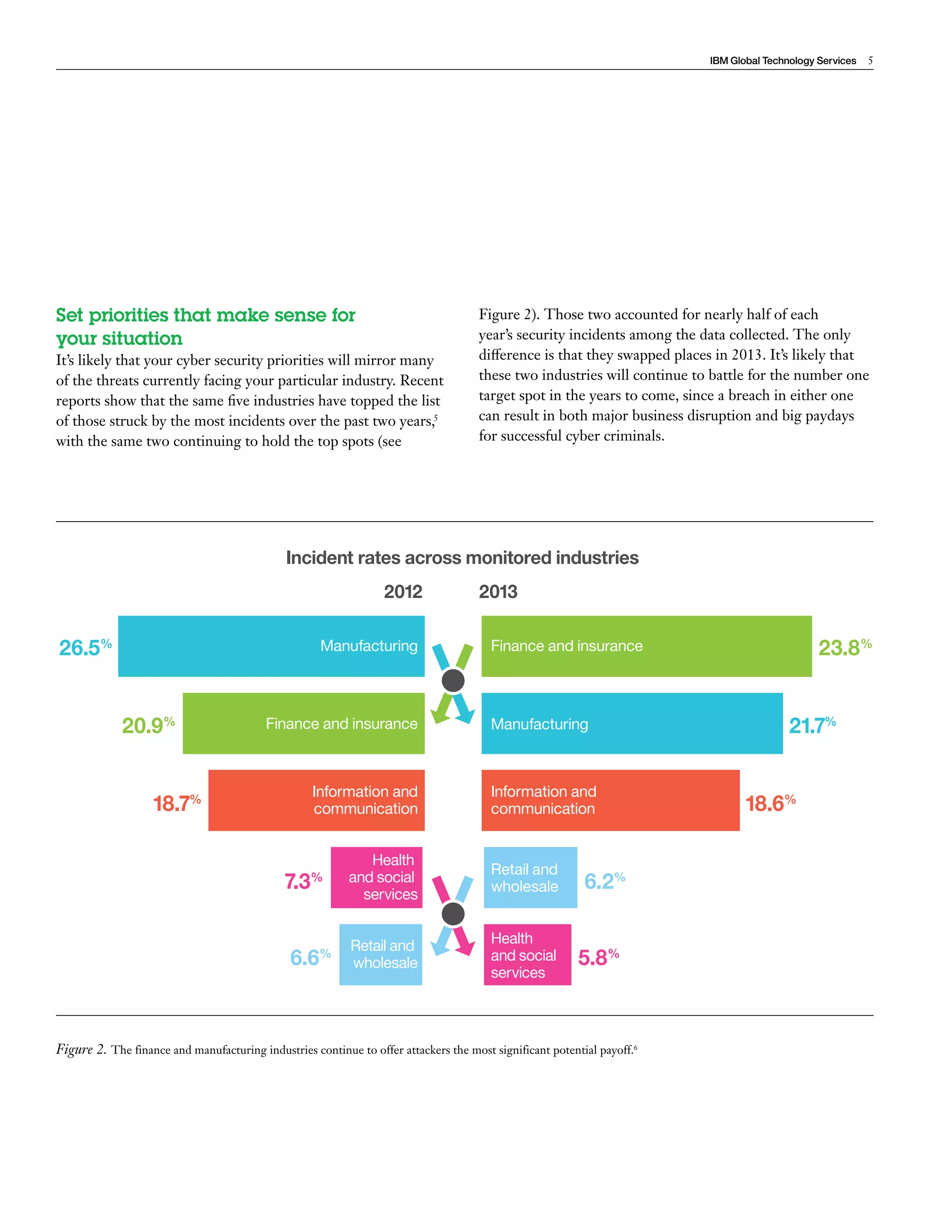
The document discusses the pervasive issue of data breaches facing organizations of all types and sizes, highlighting the motivations behind such attacks and the significant financial impacts they can cause. It emphasizes the importance of threat intelligence in proactively identifying and managing security risks, allowing organizations to better defend against sophisticated attackers. Finally, it outlines strategies for setting security priorities based on industry-specific threats and the value of conducting penetration testing to uncover vulnerabilities.