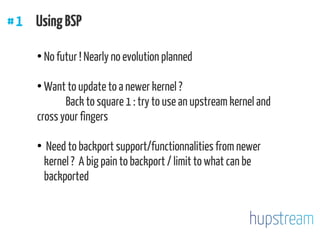
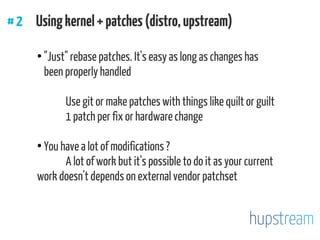
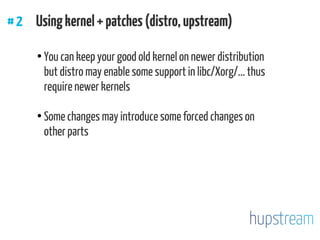
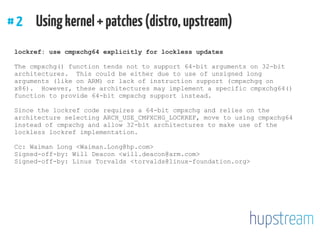
The document discusses considerations for selecting and using a kernel for specific hardware, emphasizing the importance of hardware support and integration with distributions. It highlights the pros and cons of using BSP kernels versus upstream kernels, as well as the challenges involved in maintaining and patching kernels. Best practices are suggested for ensuring successful kernel development and maintenance, including working with upstream and documenting changes.