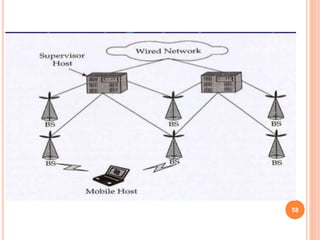
This document discusses Mobile Internet Protocol (Mobile IP) and how it allows mobile devices to stay connected to the internet without changing their IP address as they move between different networks. It covers key topics such as:
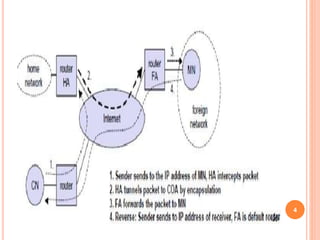
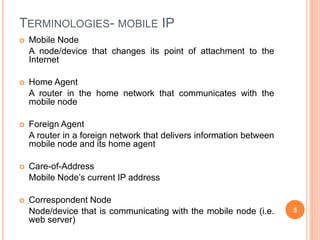
- The basics of Mobile IP including definitions of terms like home agent, foreign agent, and care-of-address.
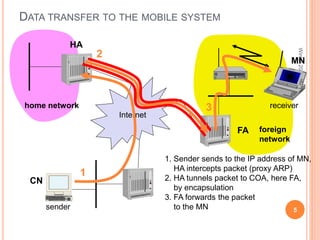
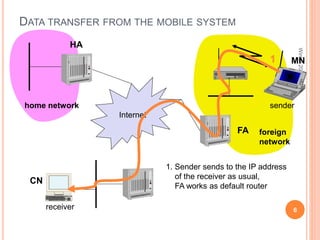
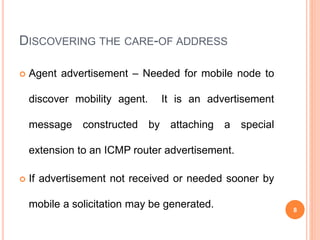
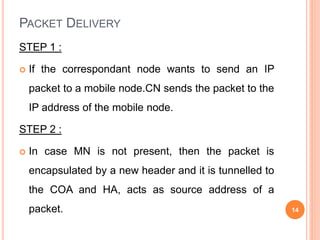
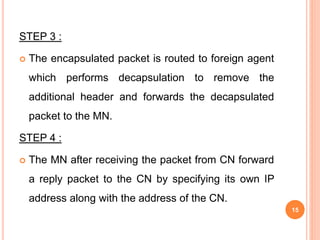
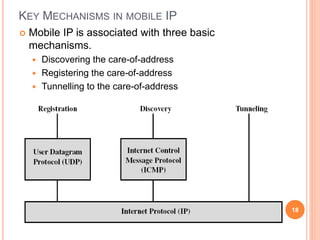
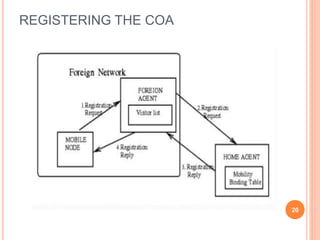
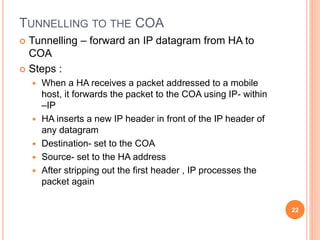
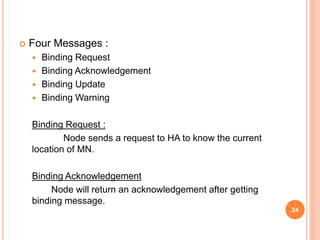
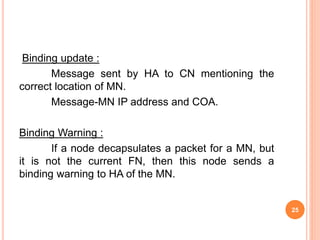
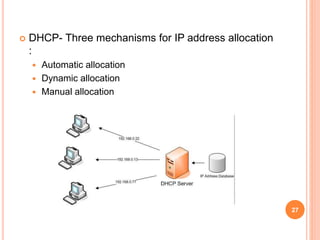
- How Mobile IP works including the process of discovering the care-of-address, registering with foreign agents, and tunneling packets to the mobile node's current location.
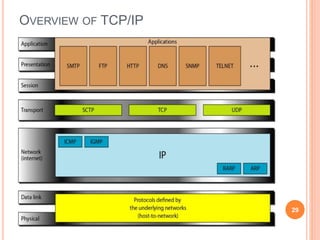
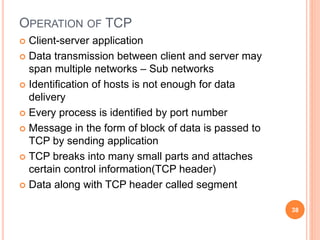
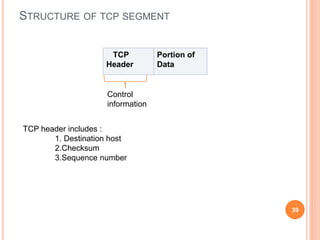
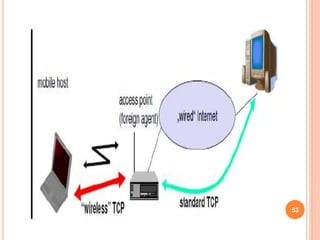
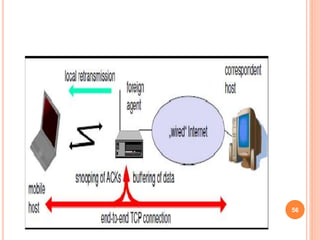
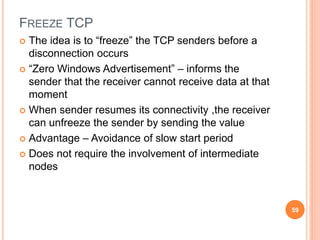
- Adaptations made to transport protocols like TCP to improve performance over wireless networks.