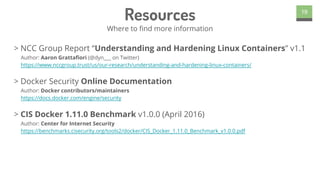
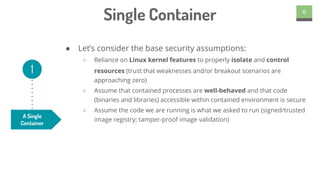
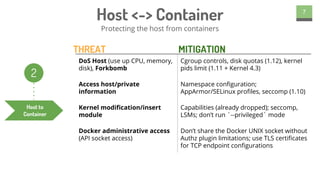
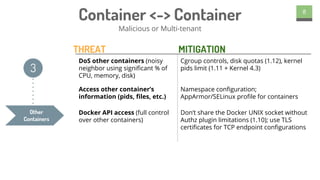
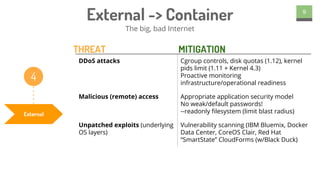
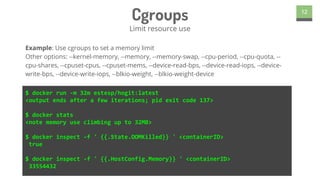
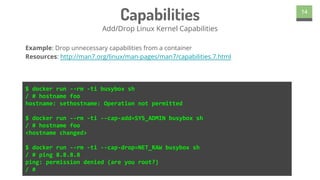
This document summarizes a presentation on container security given by Phil Estes. It identifies several threat vectors for containers including risks from individual containers, interactions between containers, external attacks, and application security issues. It then outlines various security tools and features in Docker like cgroups, Linux Security Modules, capabilities, seccomp, and user namespaces that can help mitigate these threats. Finally, it discusses some future directions for improving container security through more secure defaults, image signing, and network security enhancements.






![Seccomp
Linux Secure Computing
15
$ cat policy.json
{
"defaultAction": "SCMP_ACT_ALLOW",
"syscalls": [
{
"name": "chmod",
"action": "SCMP_ACT_ERRNO"
}
]
}
$ docker run --rm -it --security-opt seccomp:policy.json busybox chmod 640
/etc/resolv.conf
chmod: /etc/resolv.conf: Operation not permitted
Example: Block specific syscalls from being used by container binaries
Resources: https://github.com/docker/docker/blob/master/docs/security/seccomp.md
http://blog.aquasec.com/new-docker-security-features-and-what-they-mean-seccomp-
profiles](https://image.slidesharecdn.com/containersecurity-everythingyoushouldprobablyknow-160720212155/85/Docker-London-Container-Security-15-320.jpg)