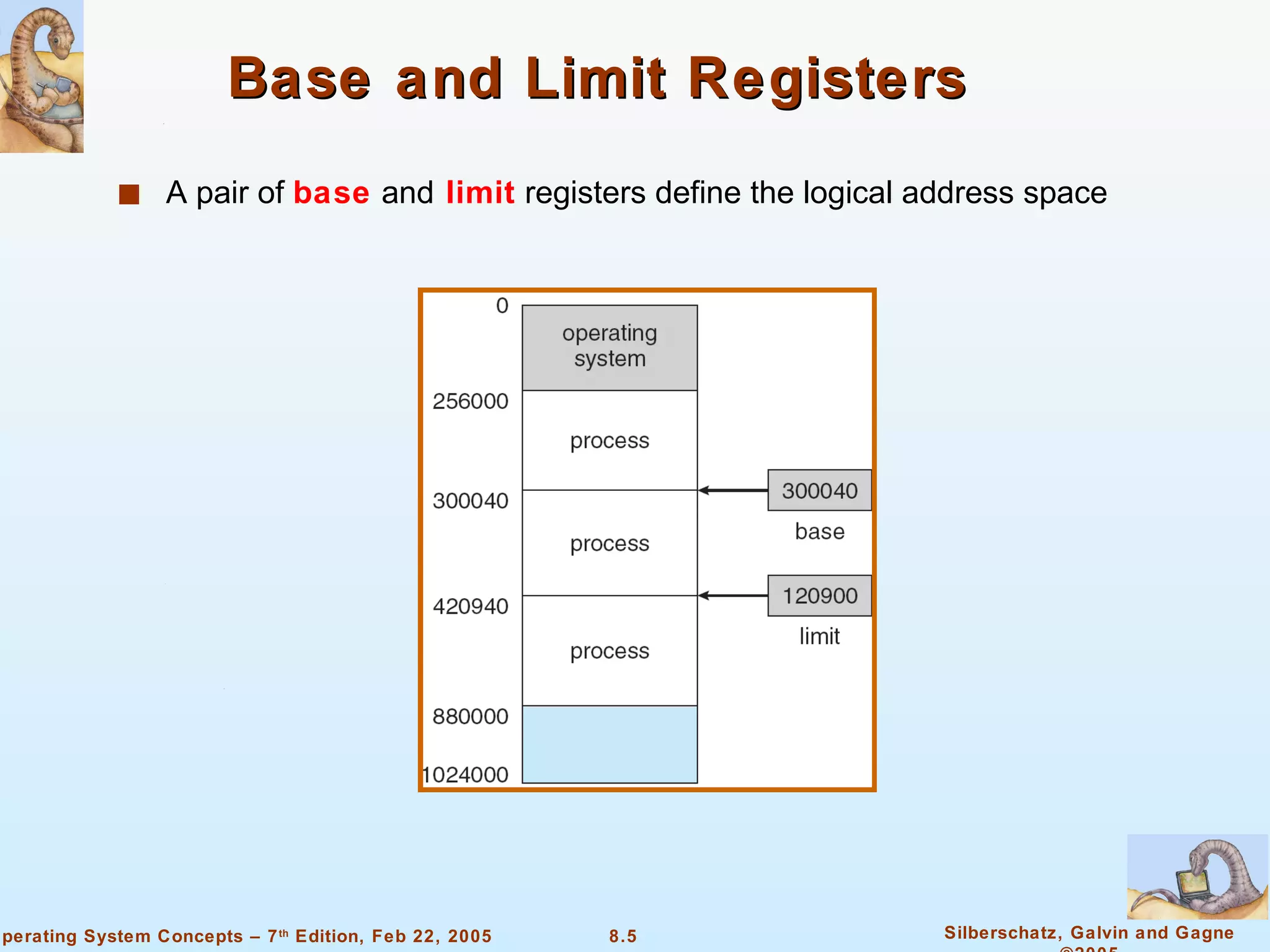
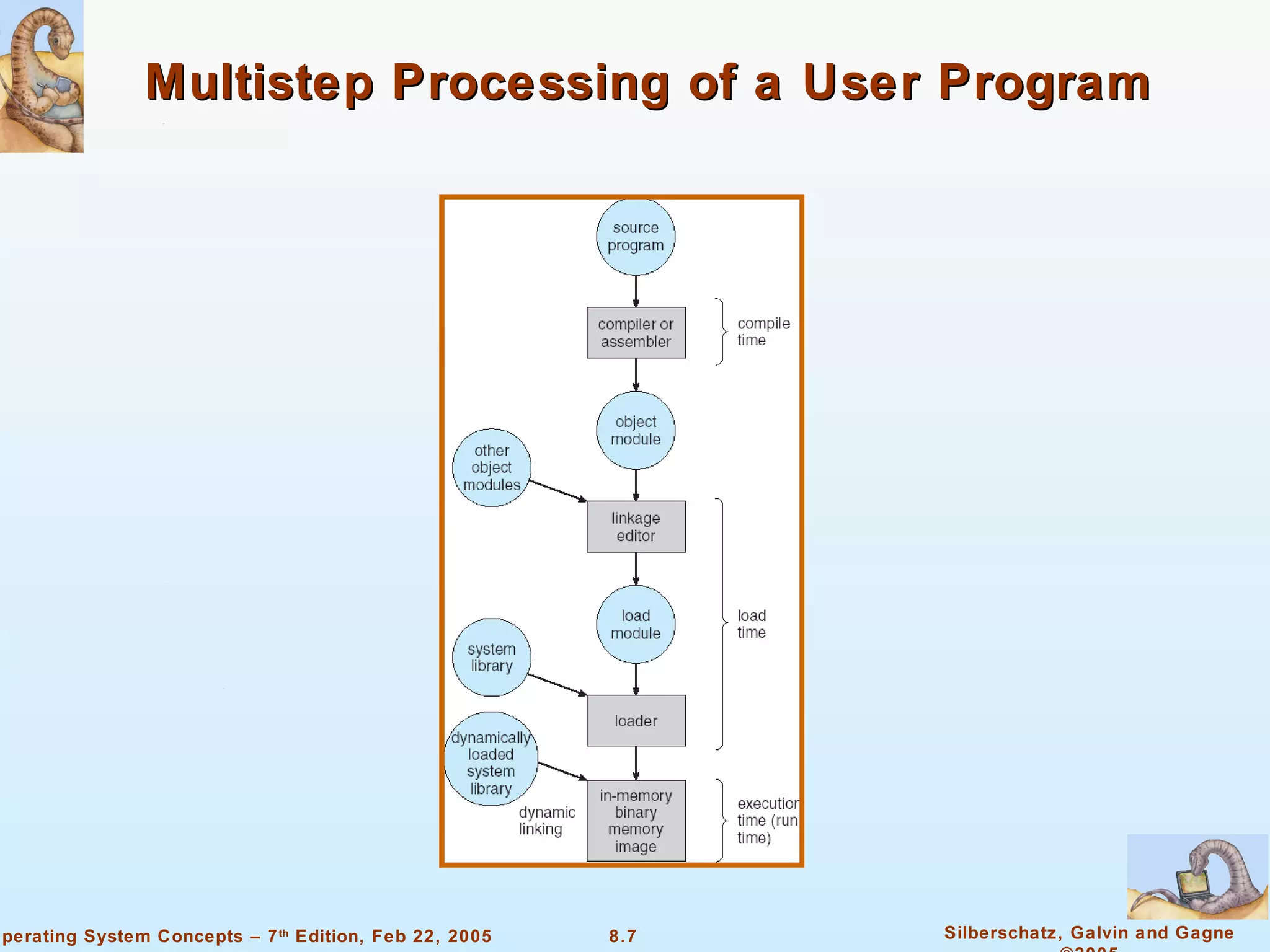
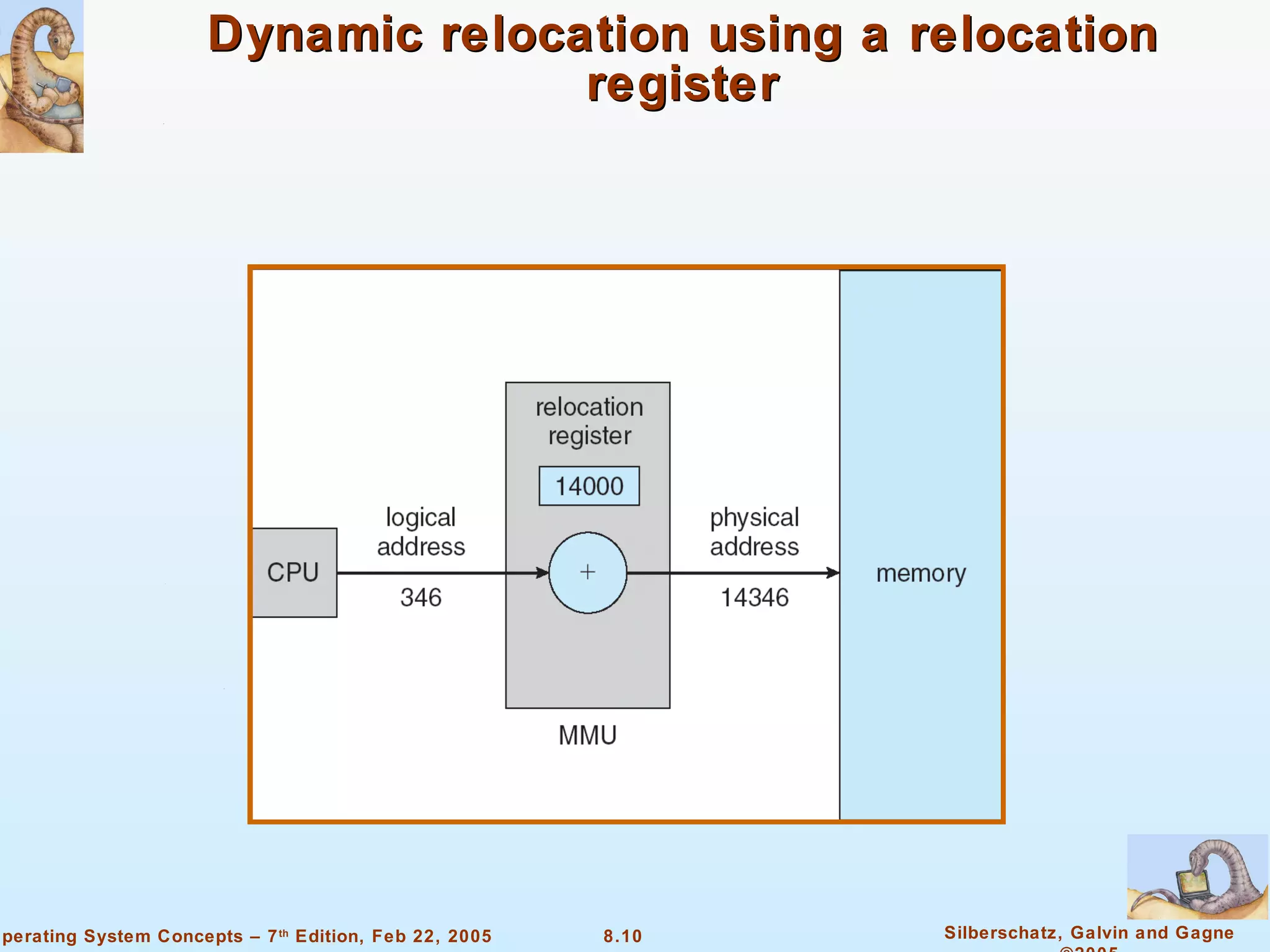
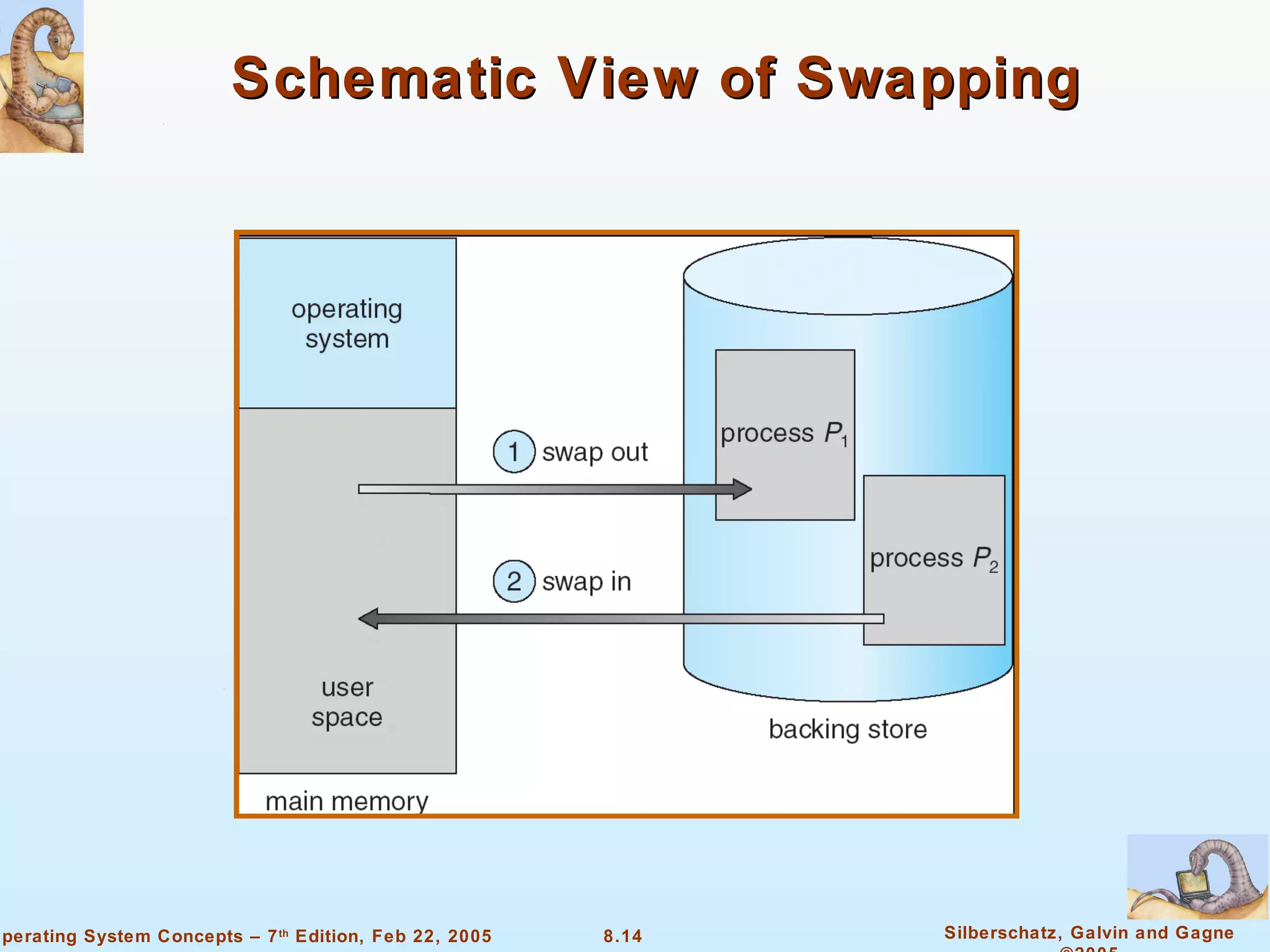
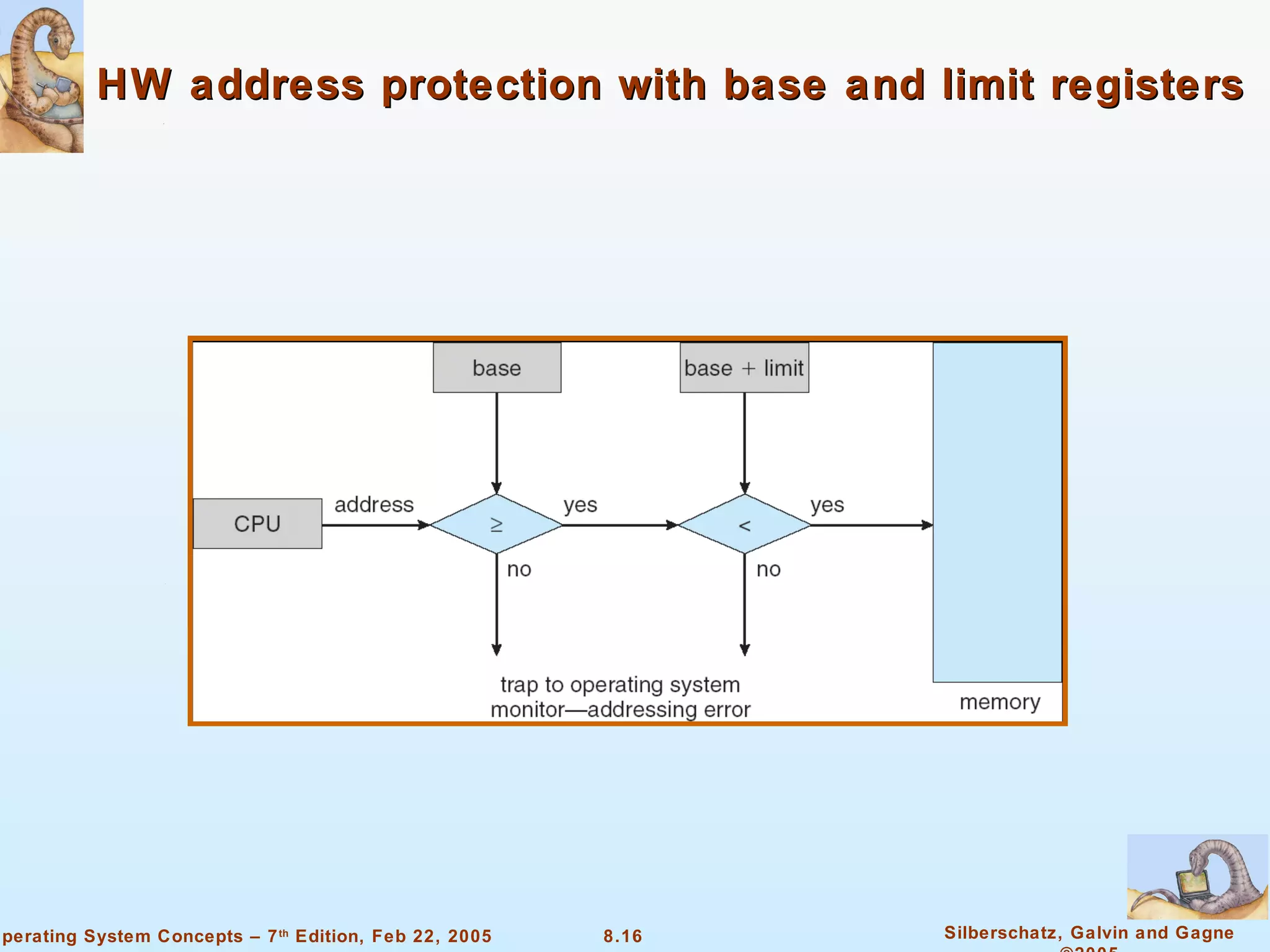
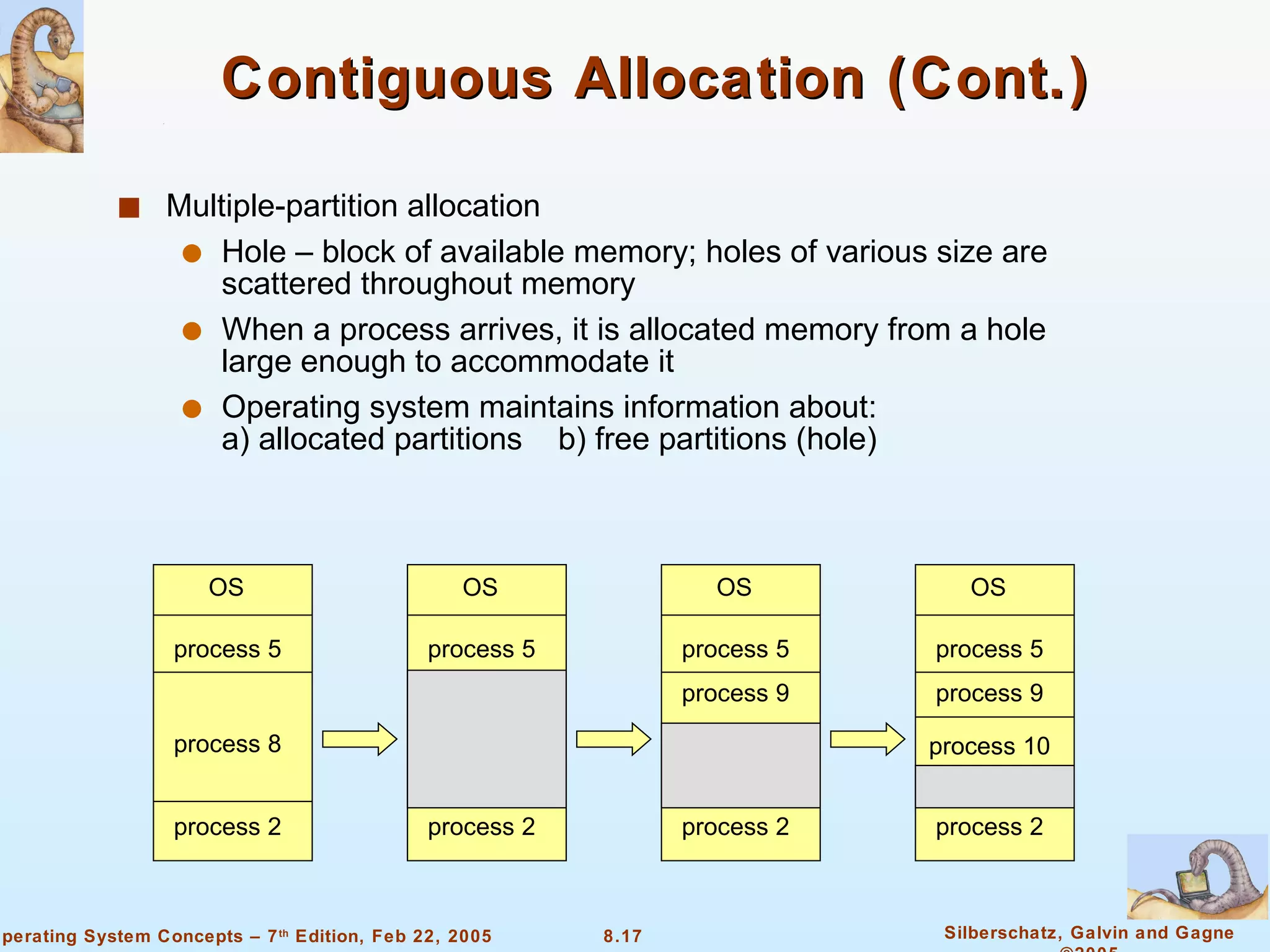
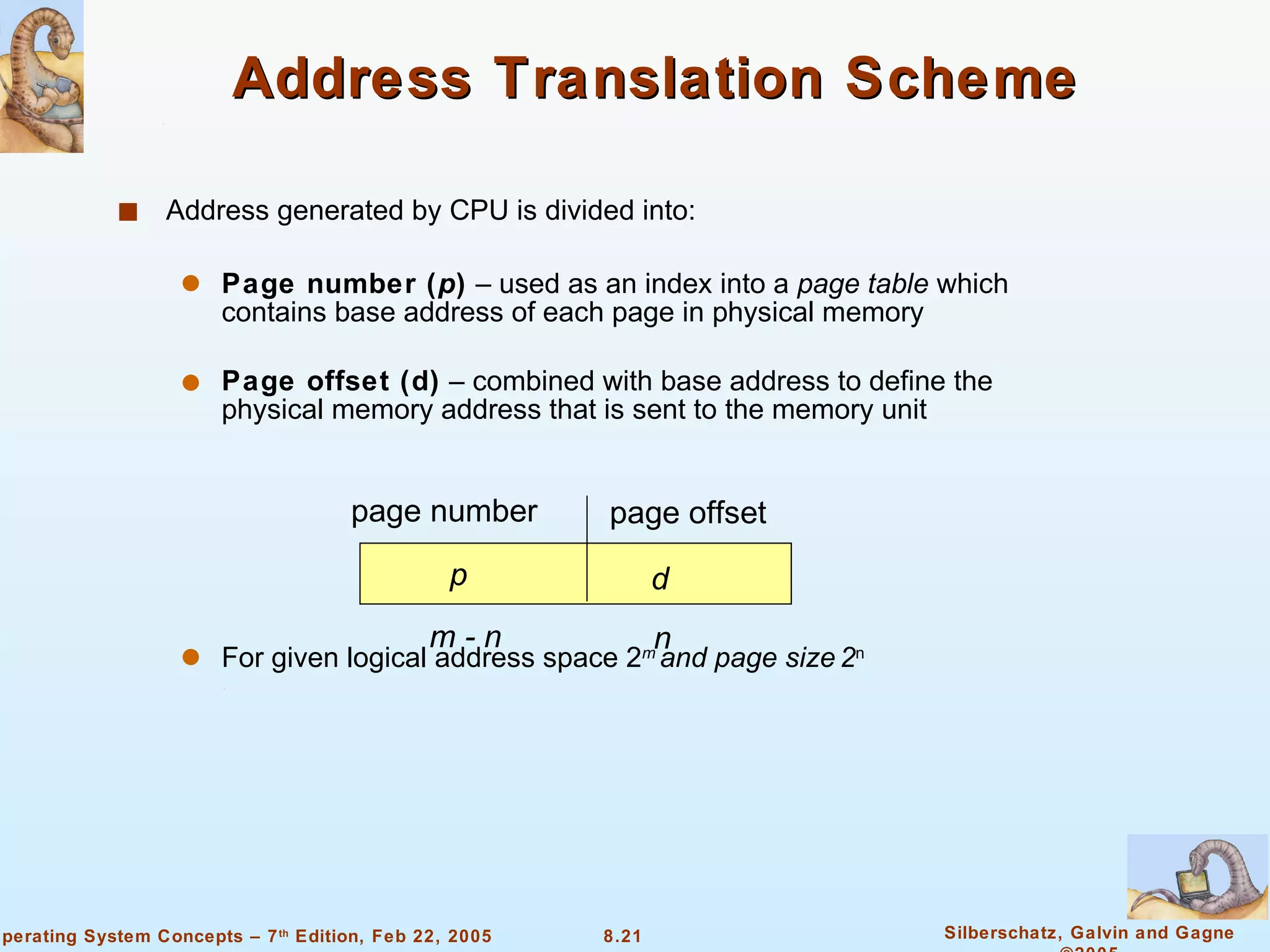
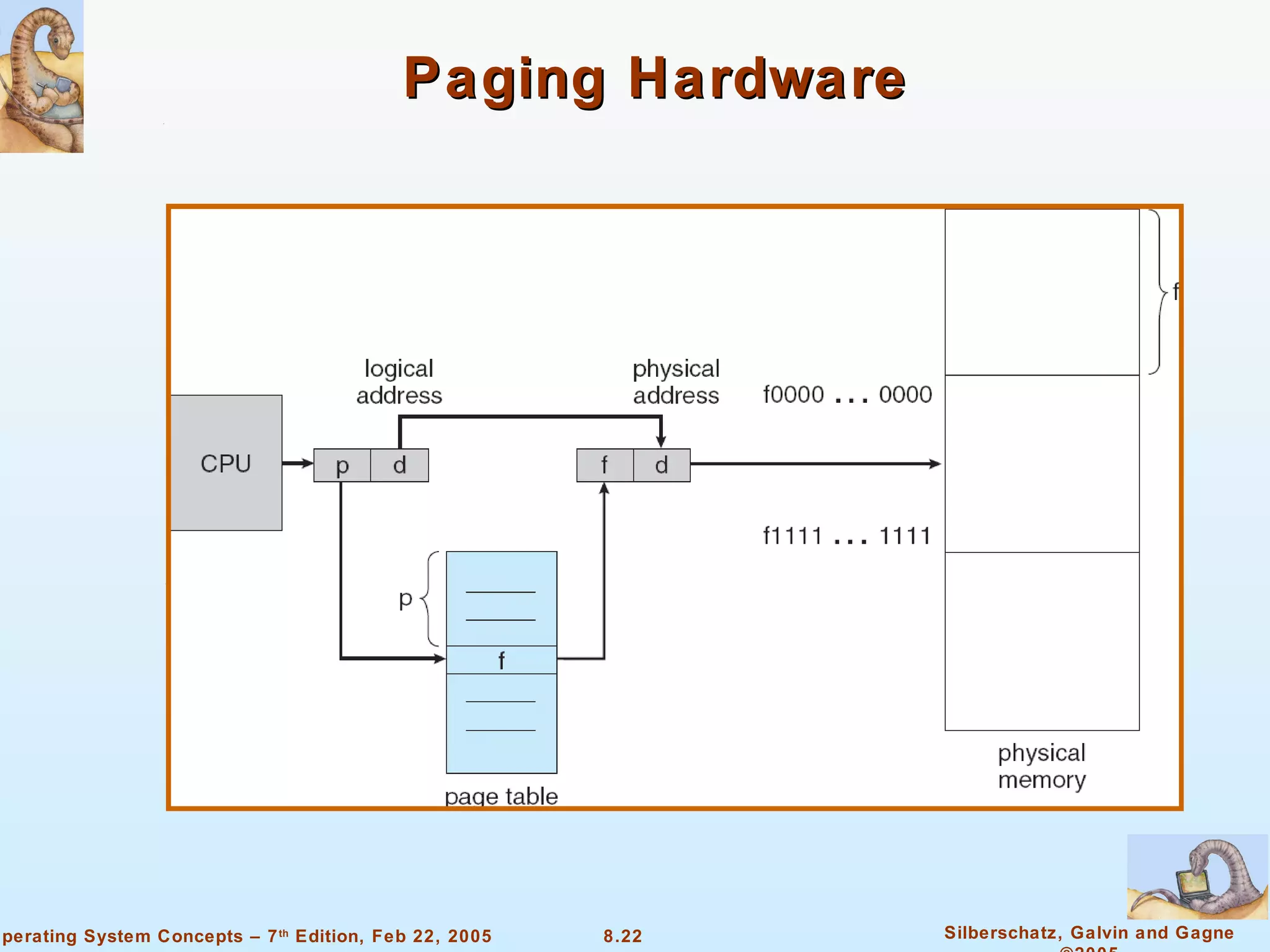
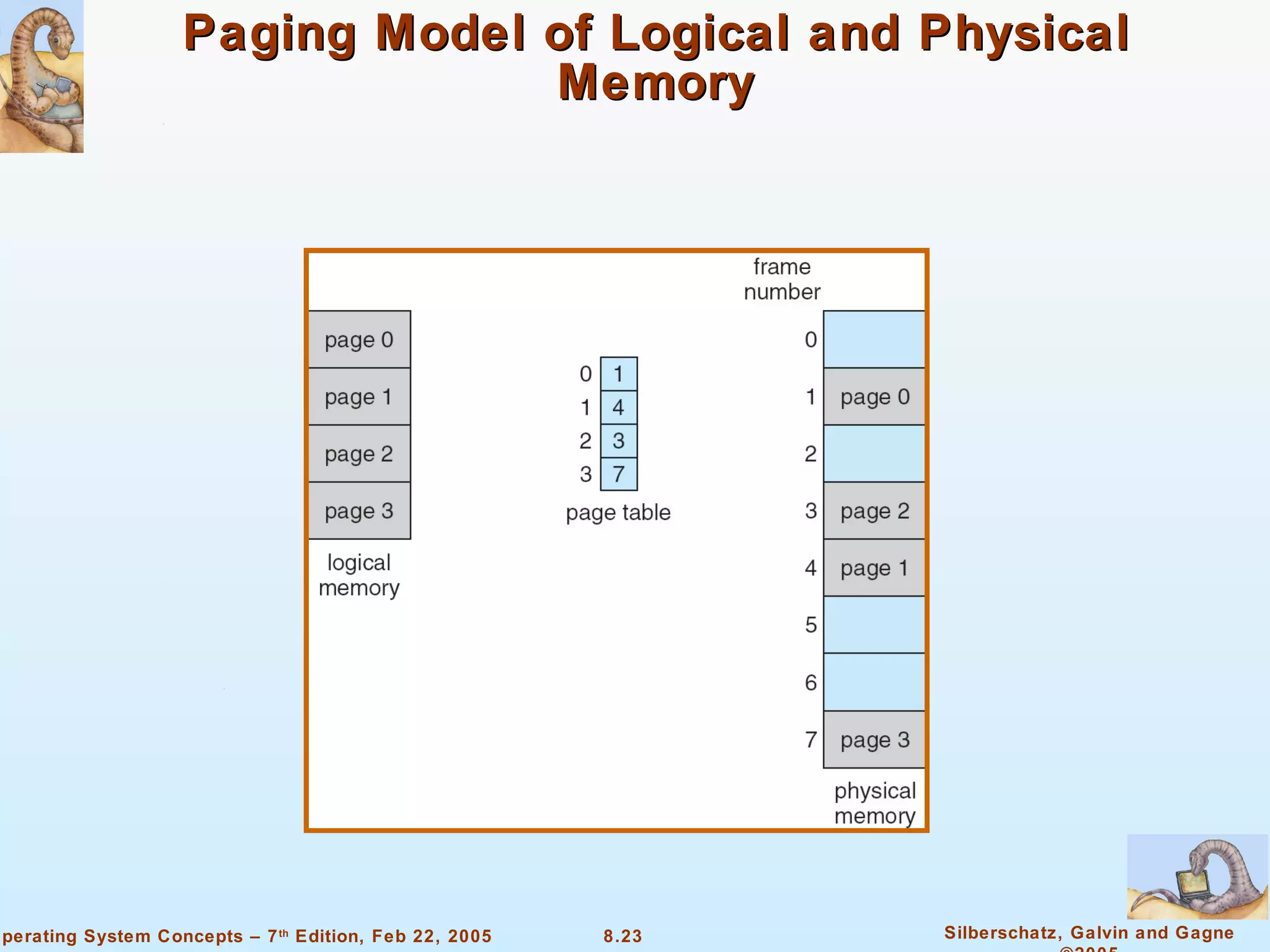
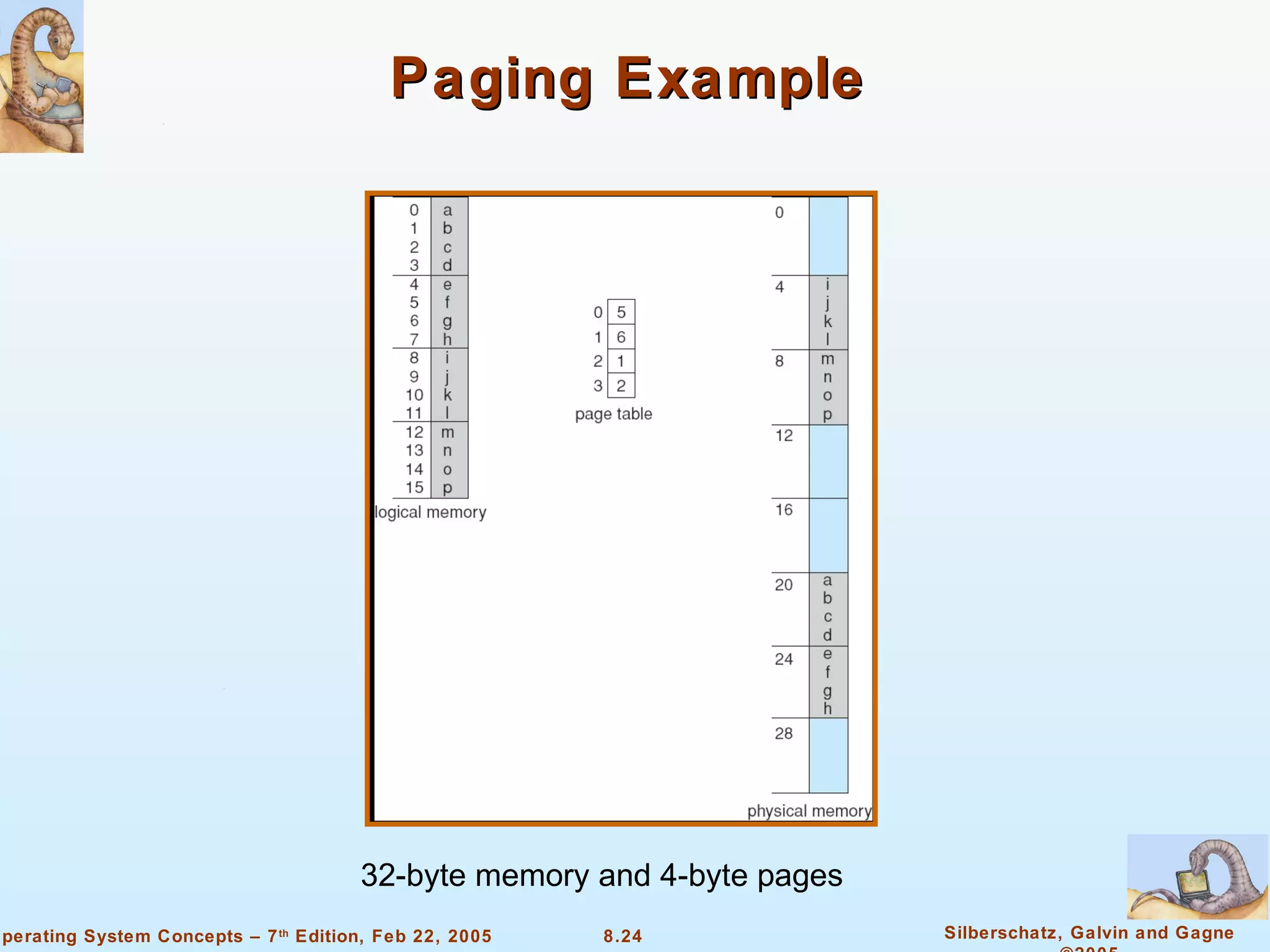
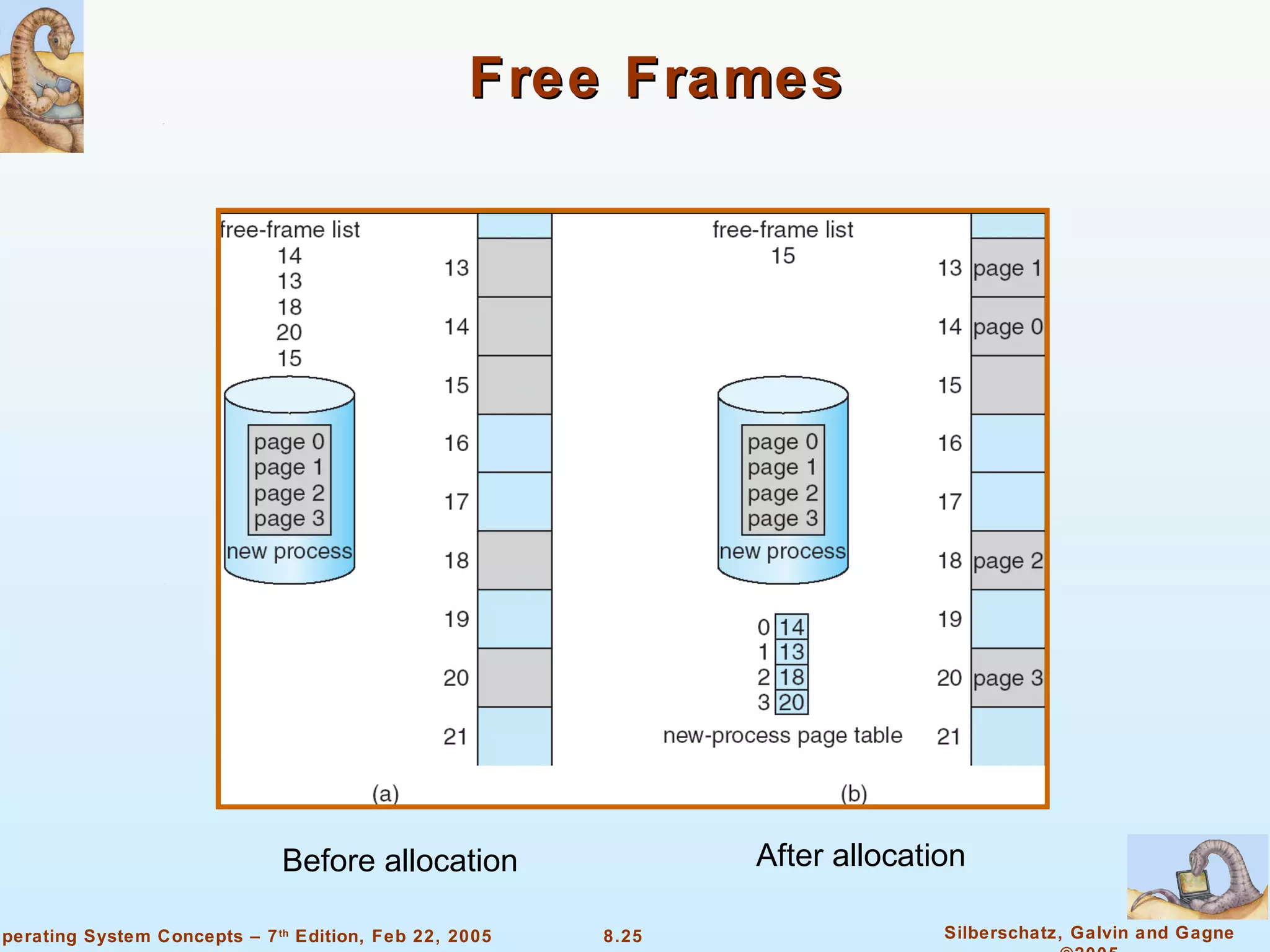
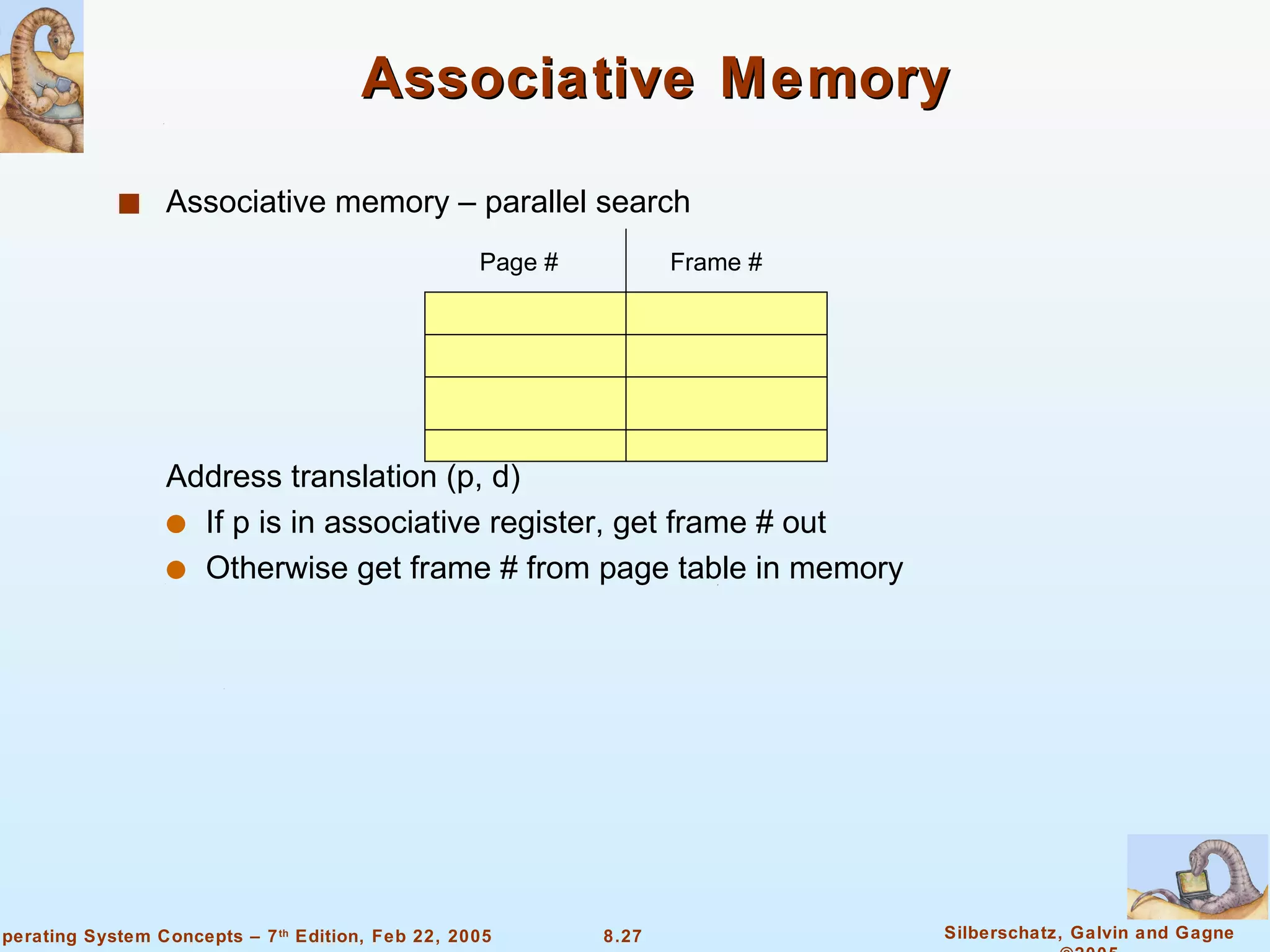
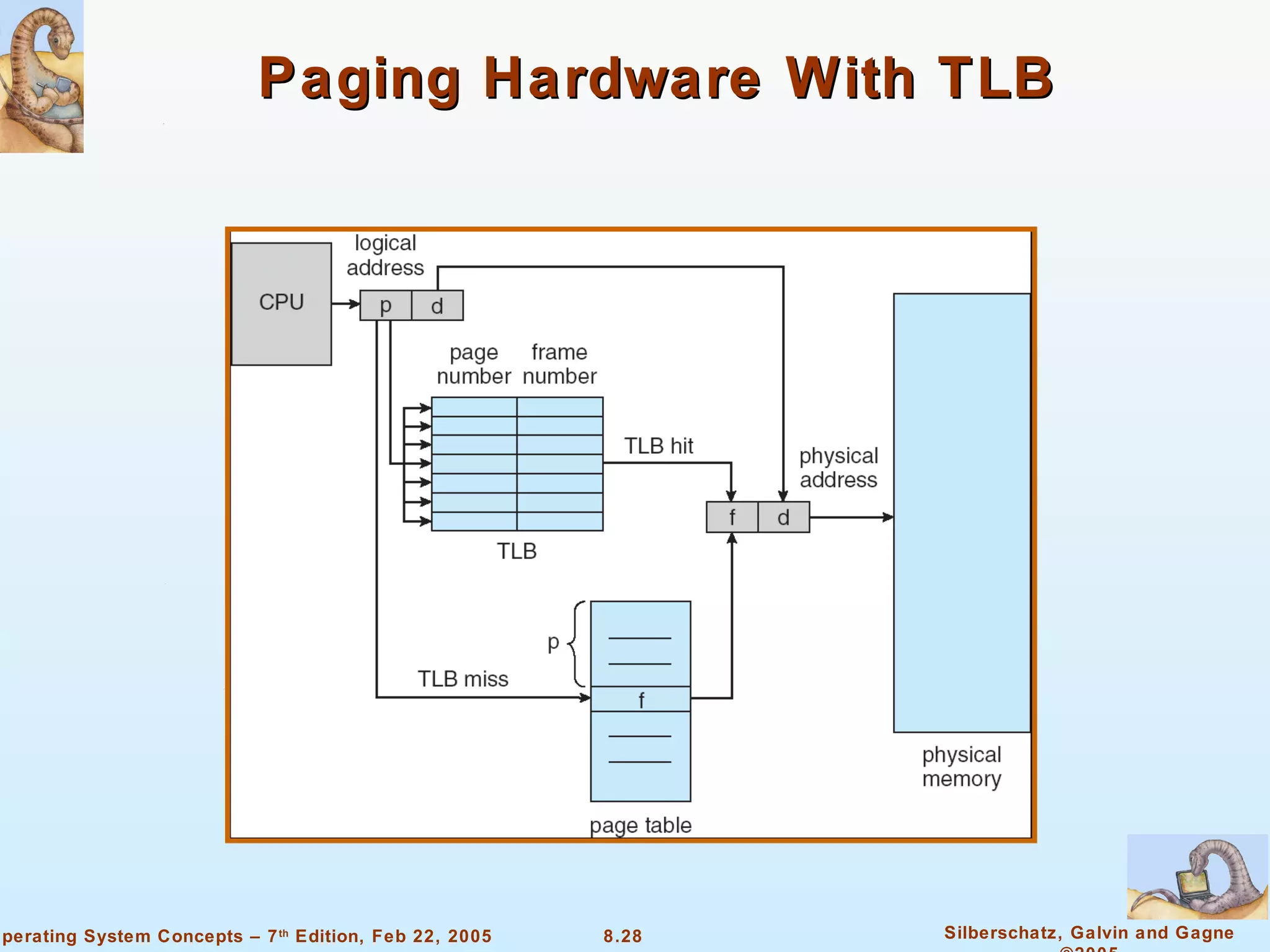
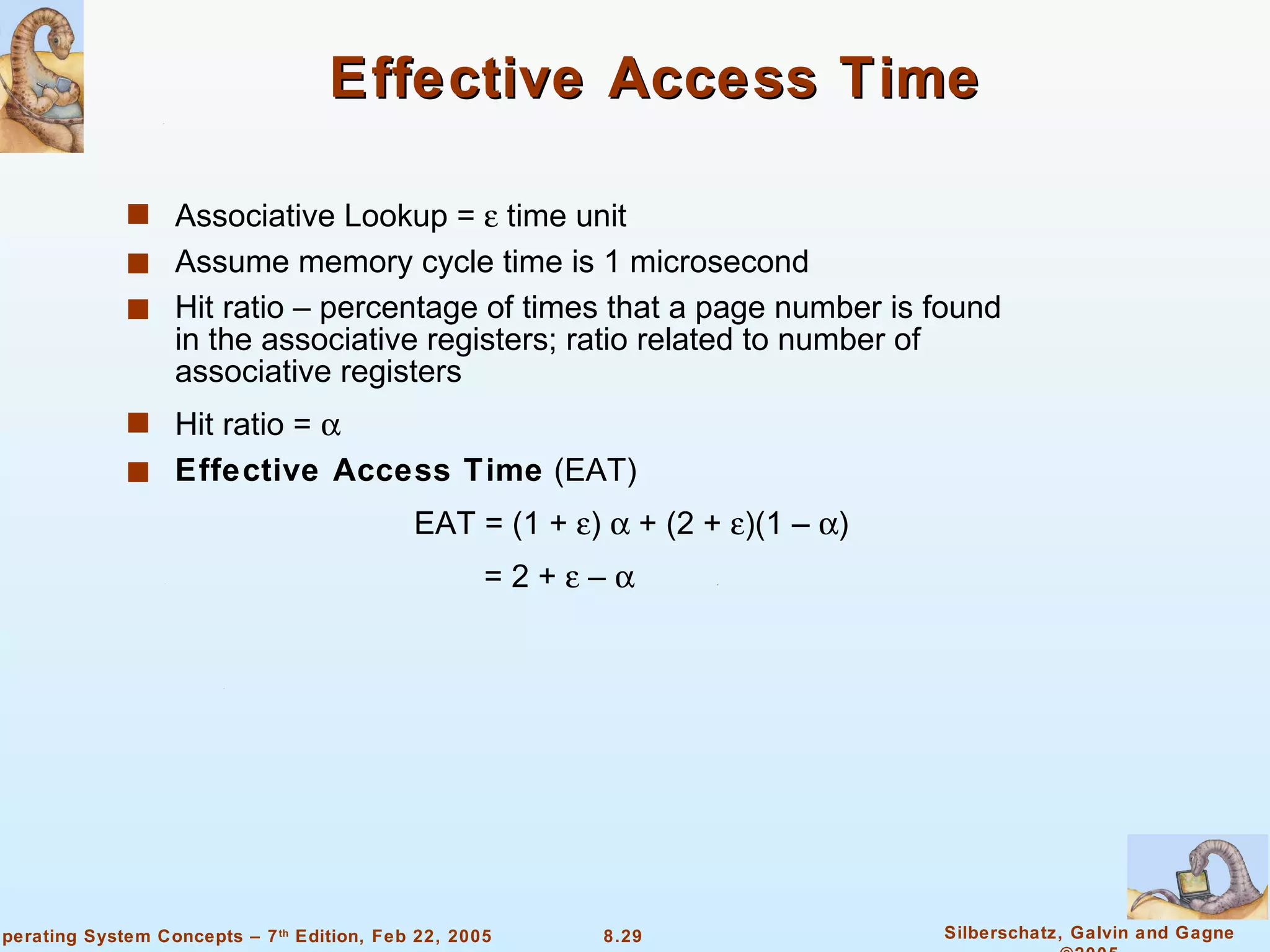
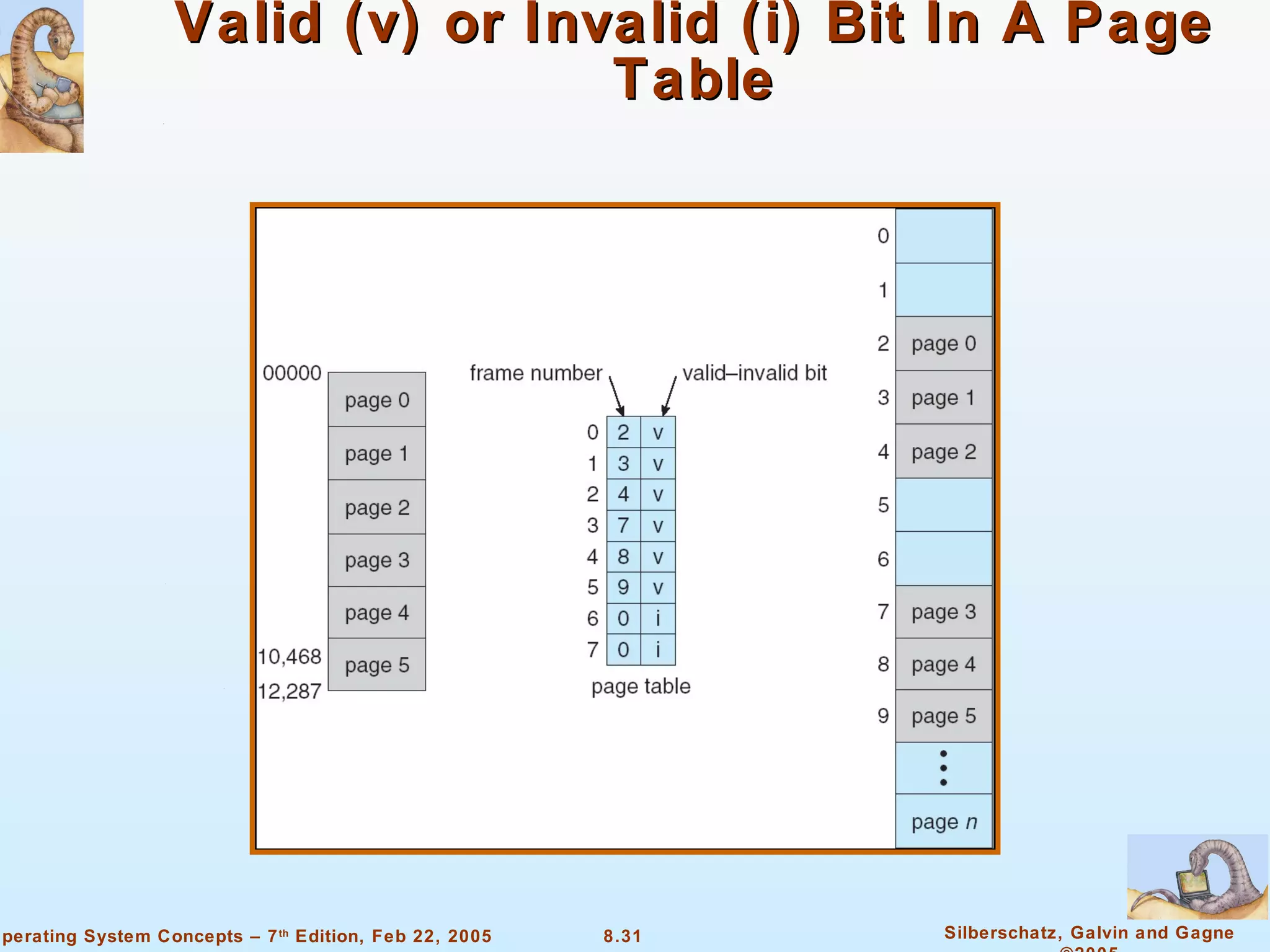
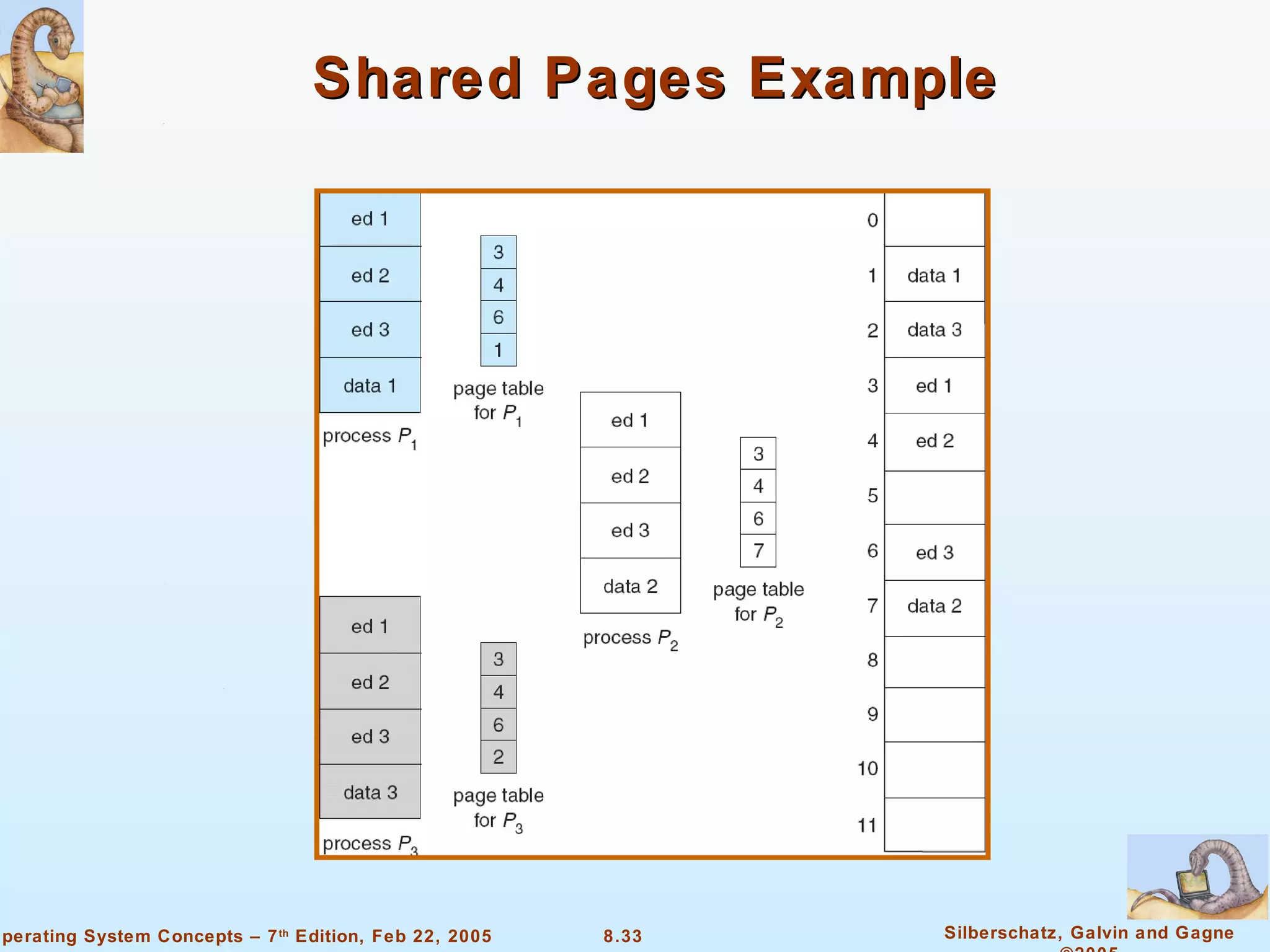
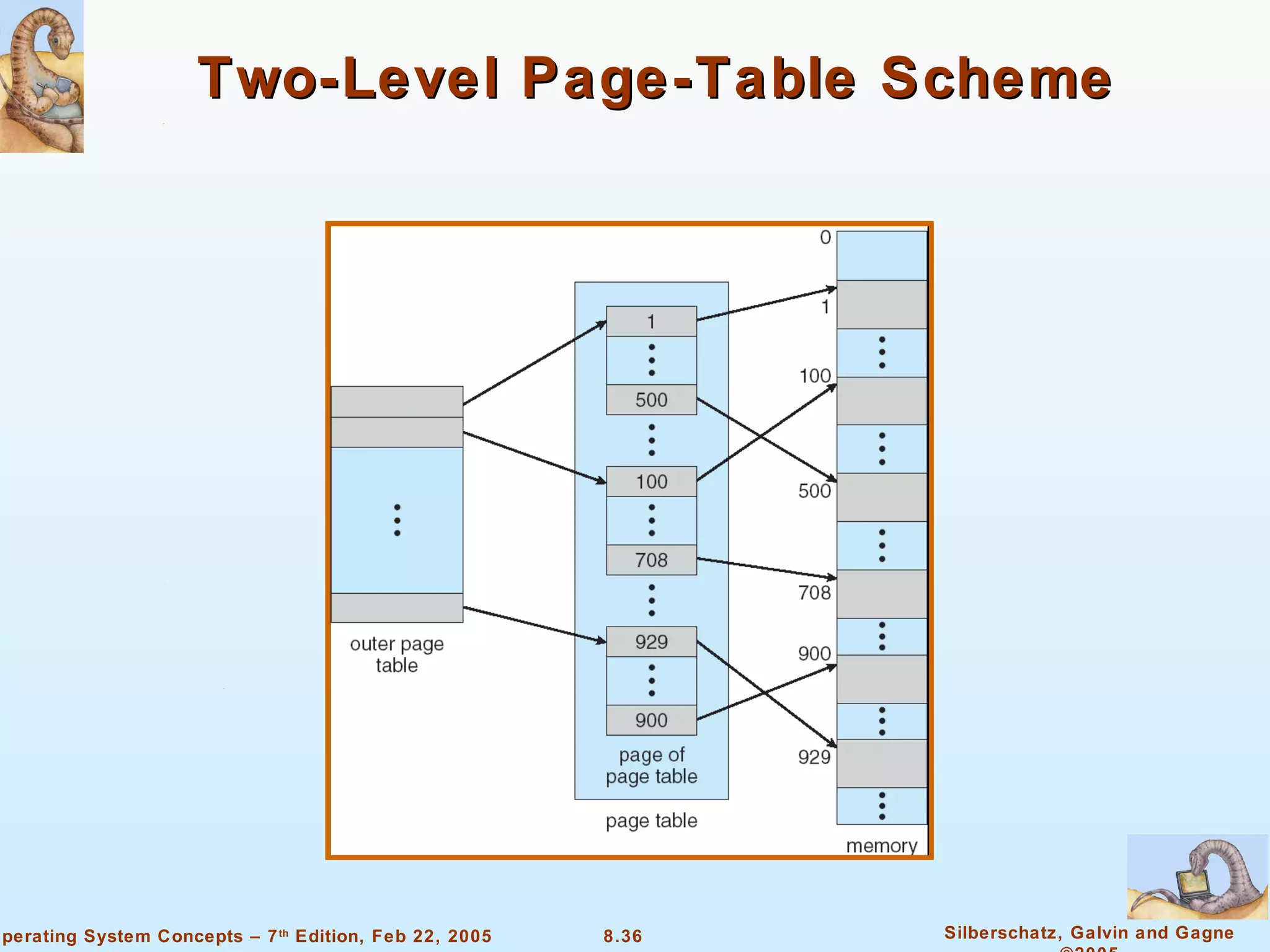
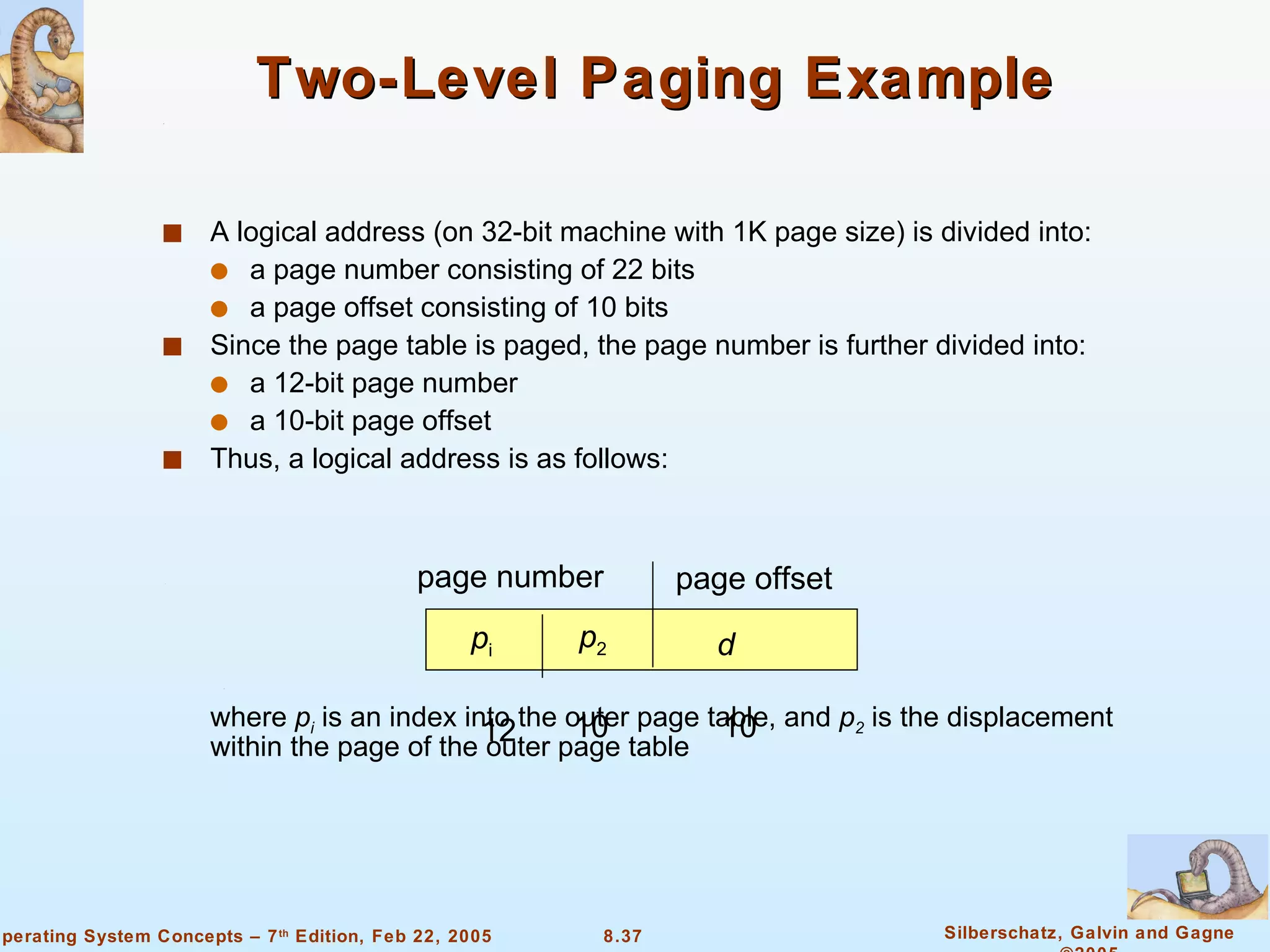
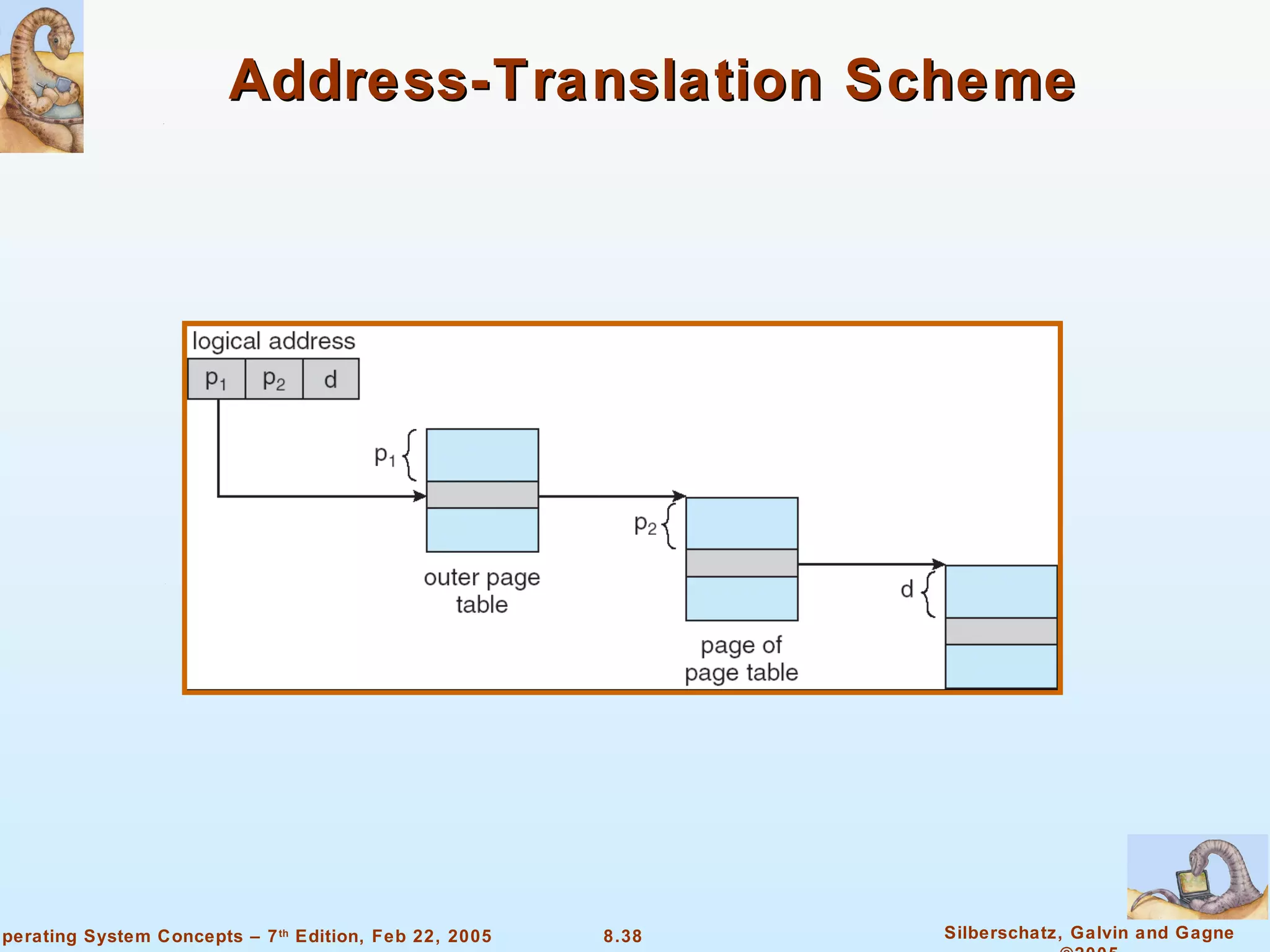
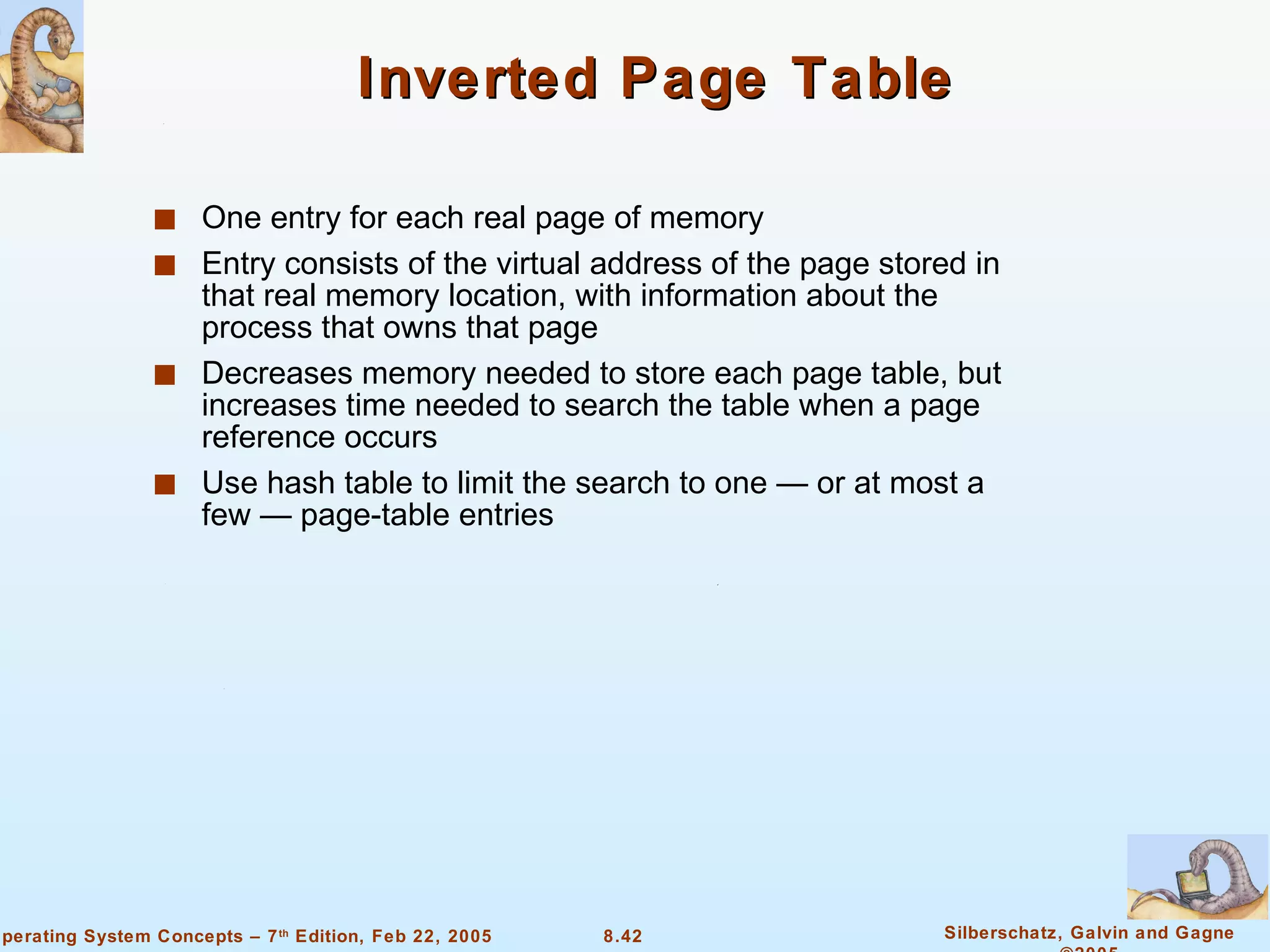
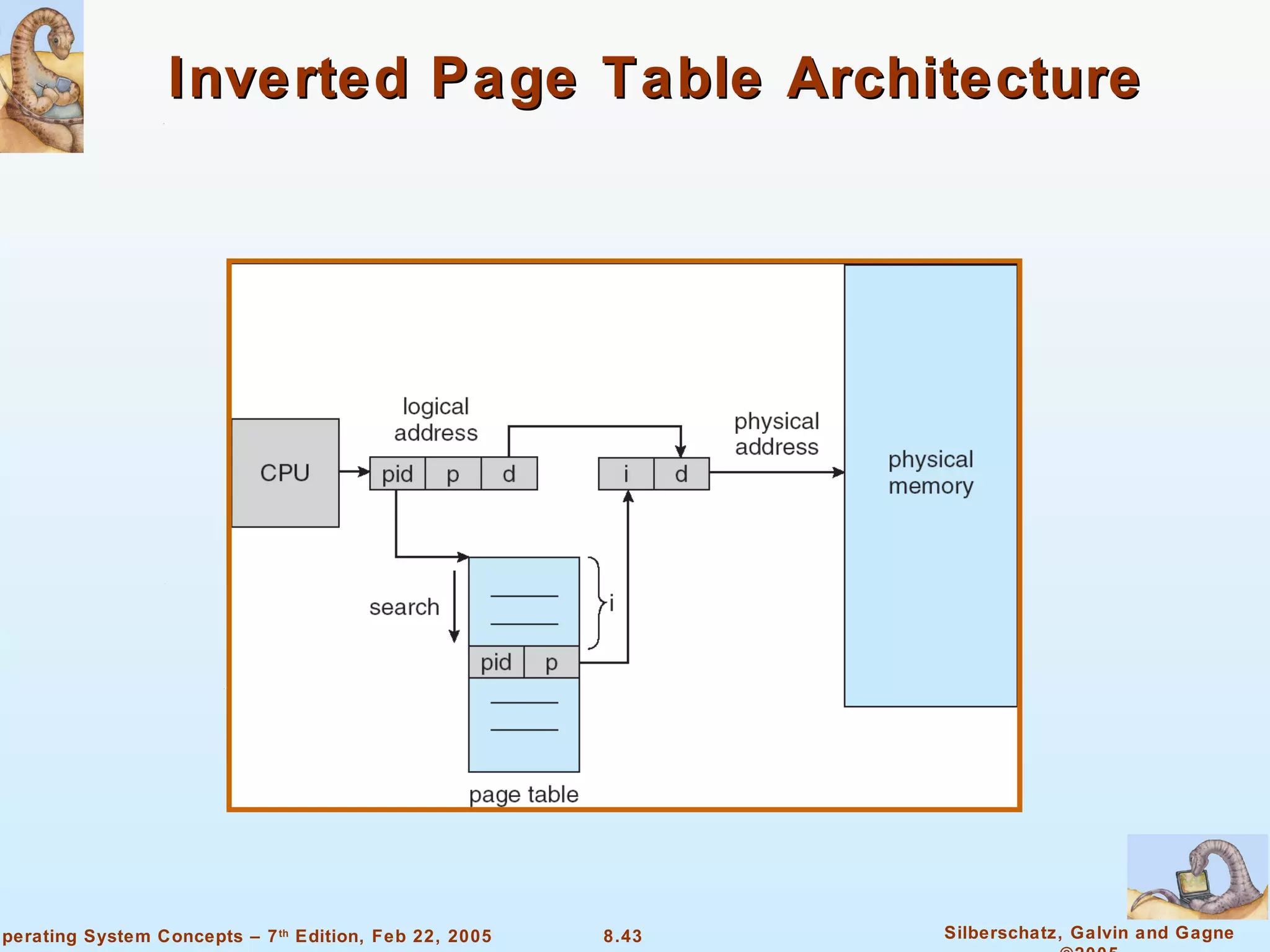
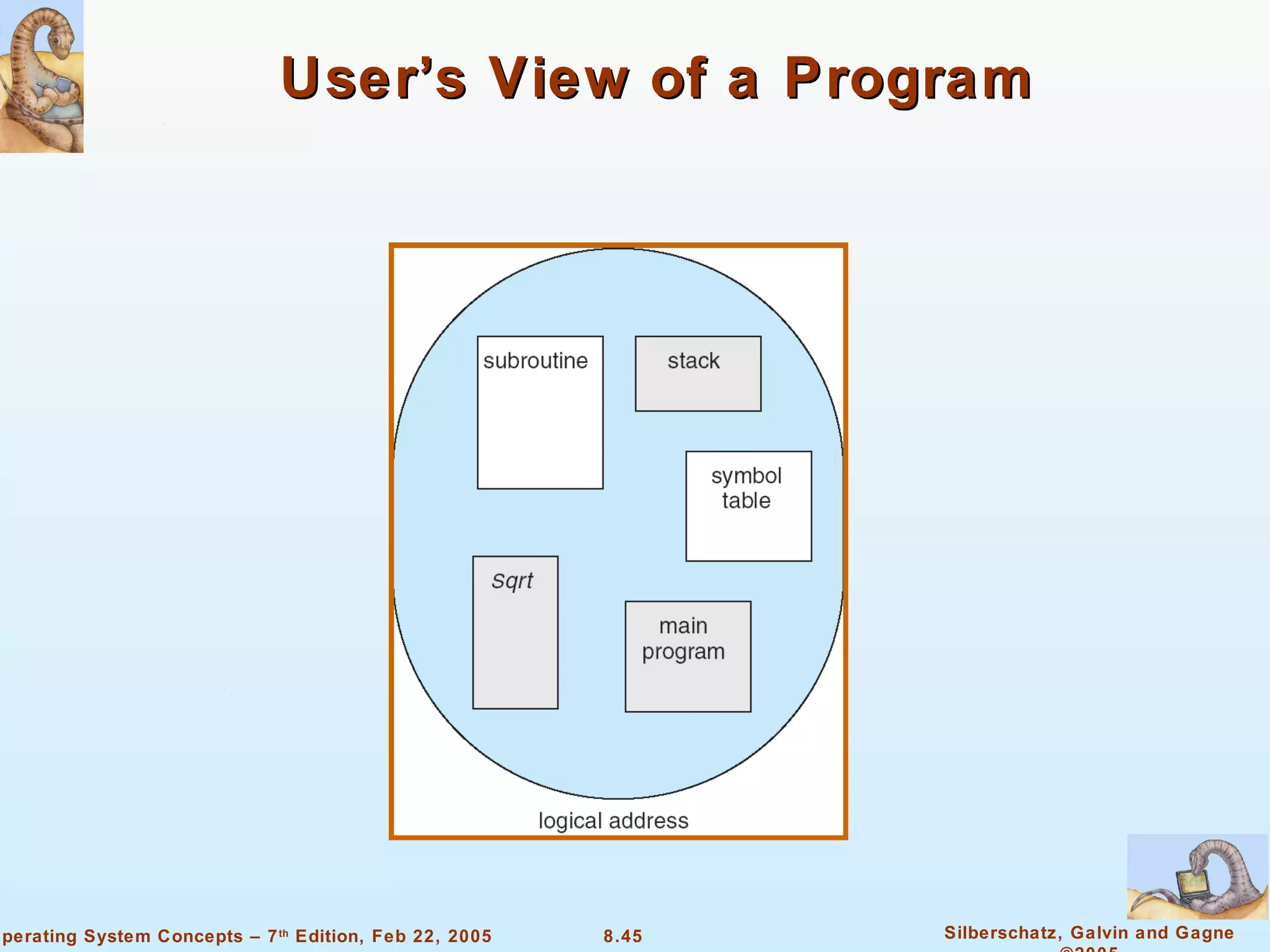
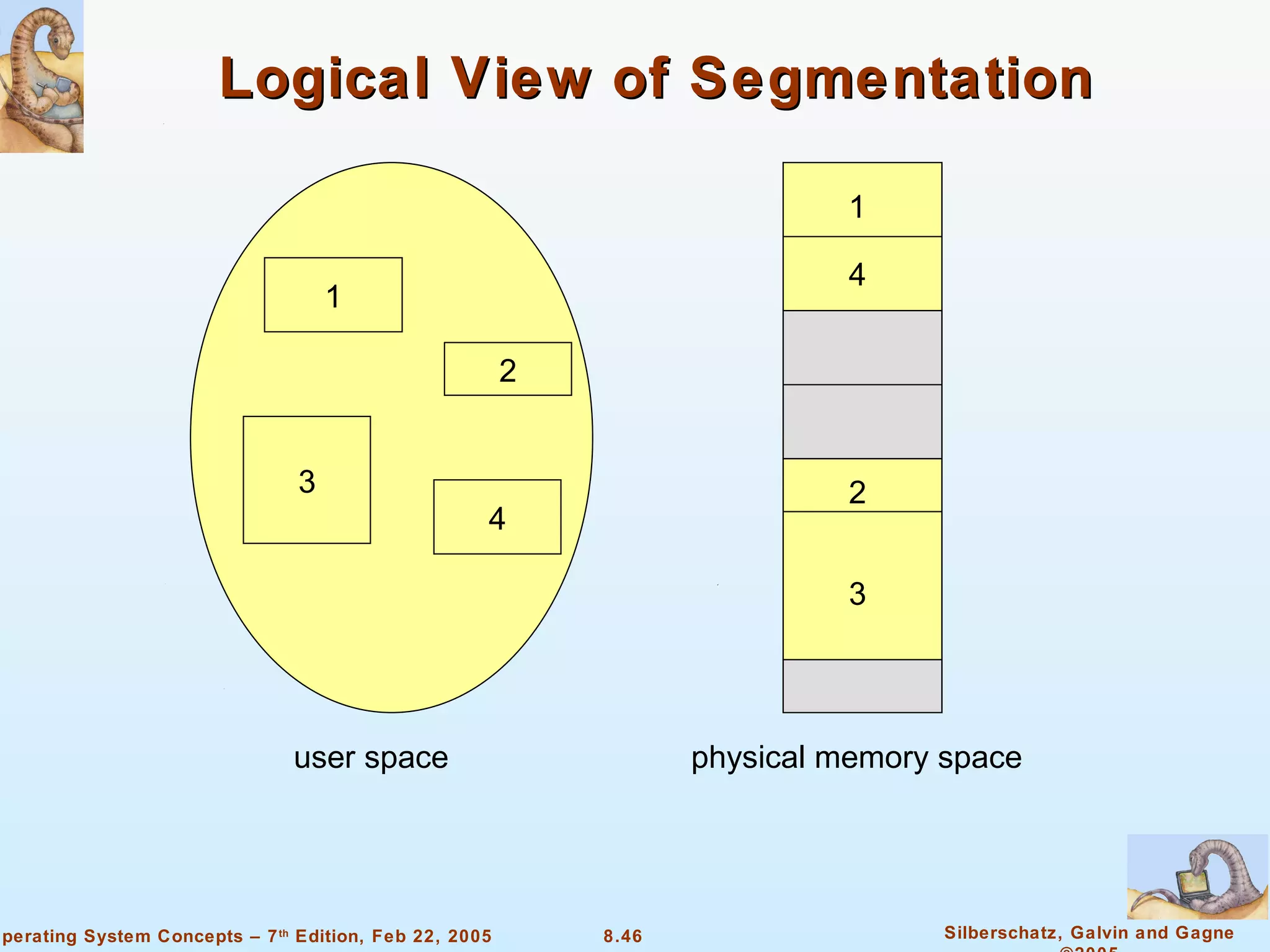
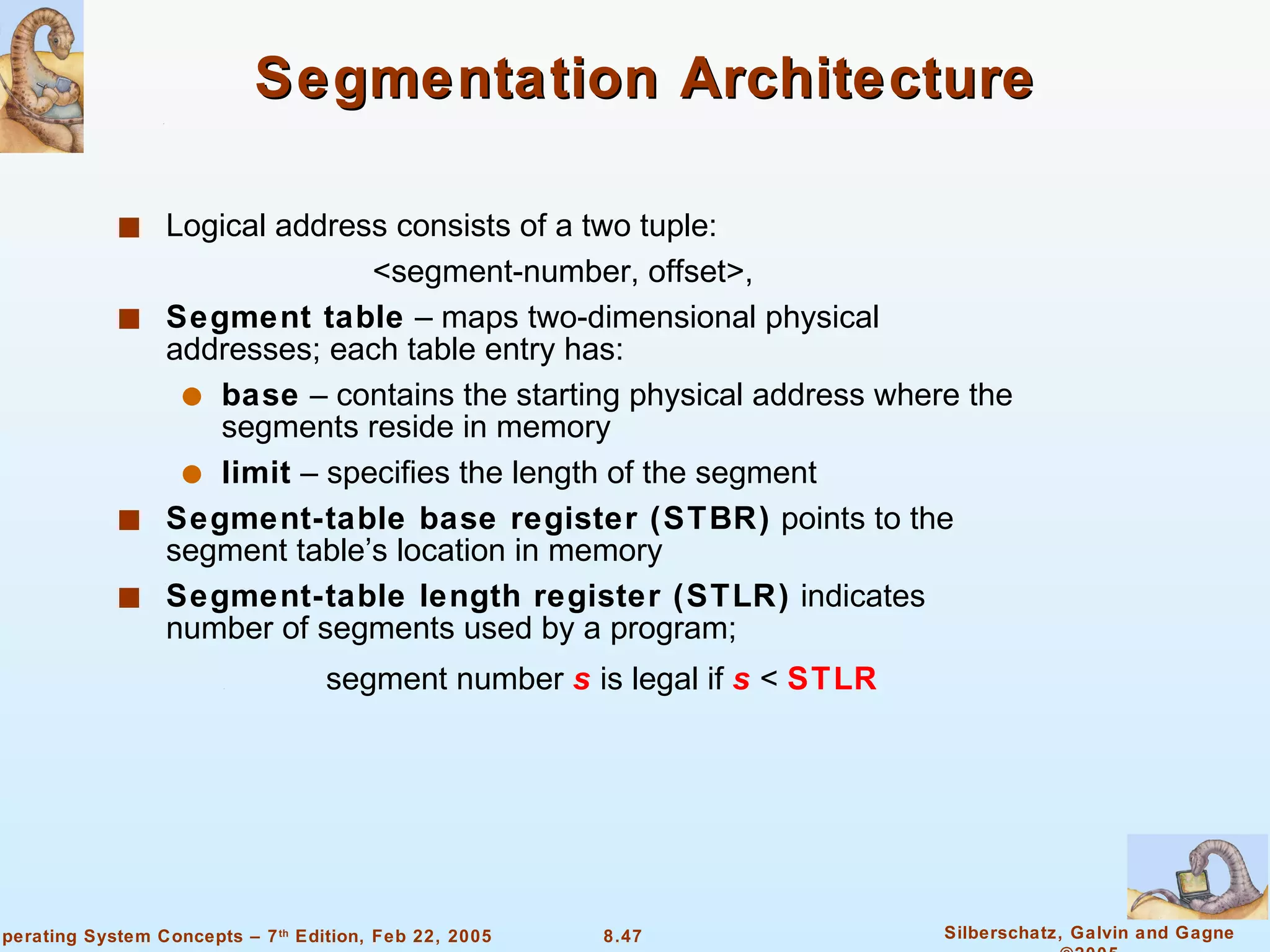
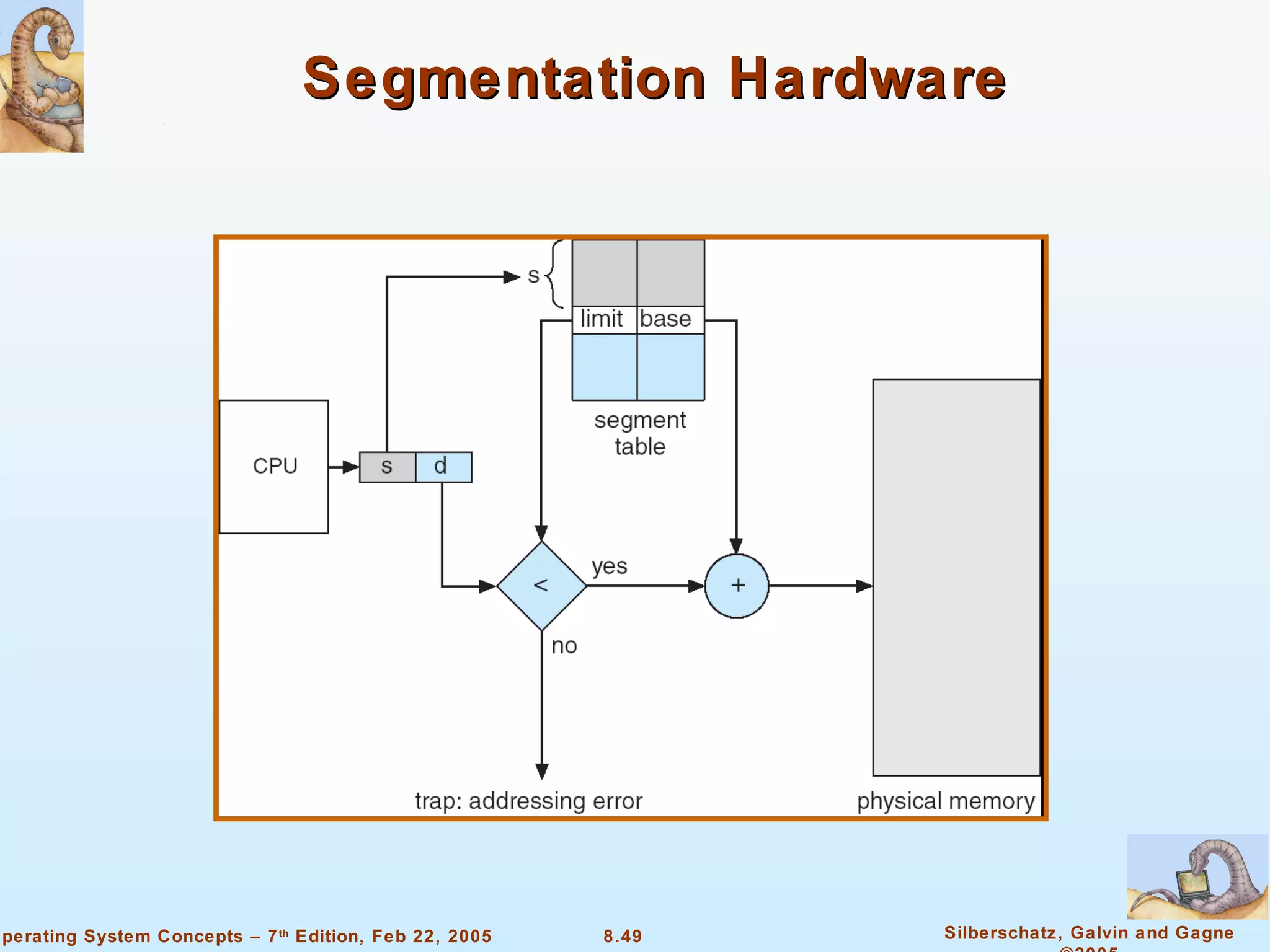
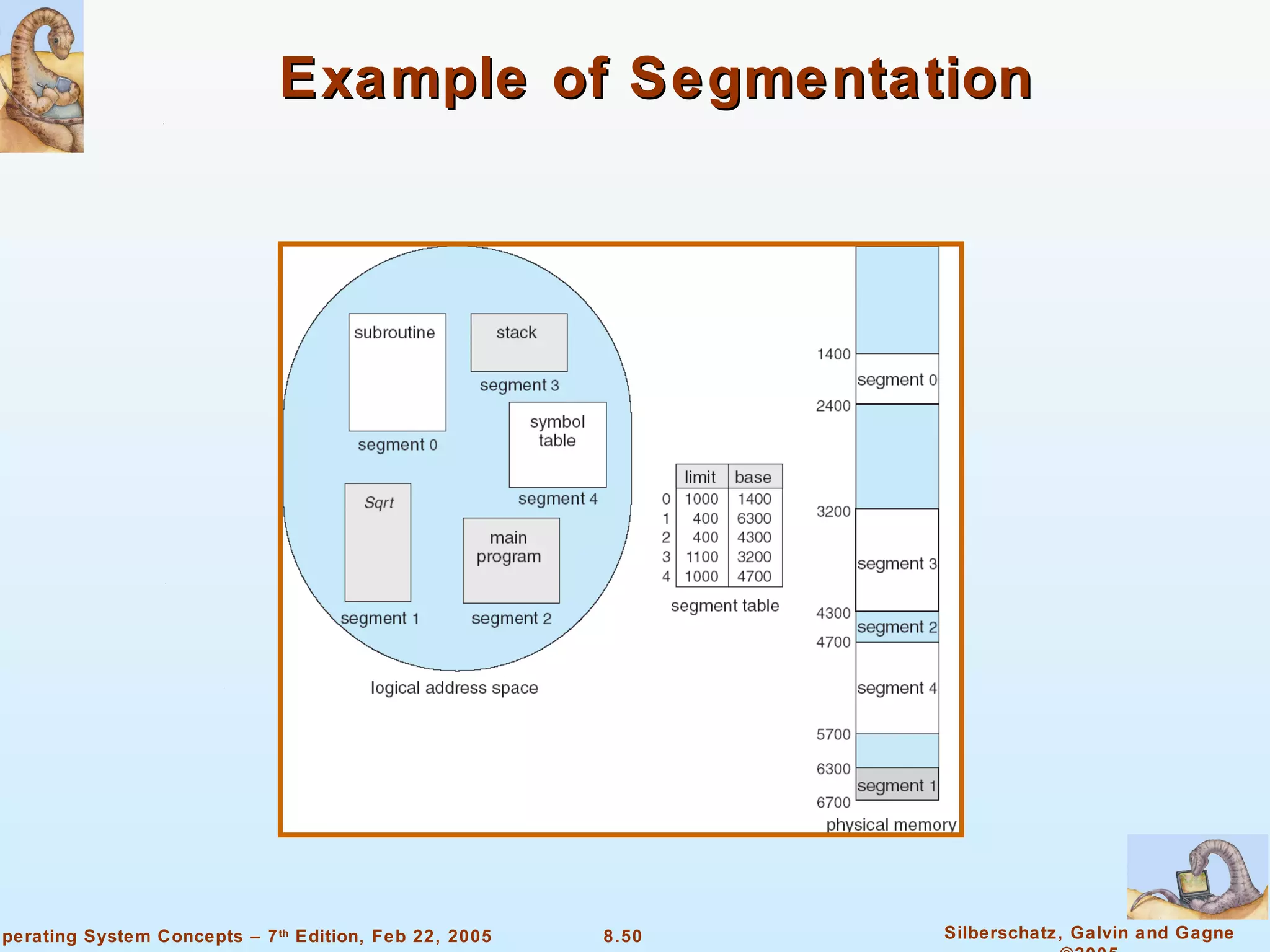
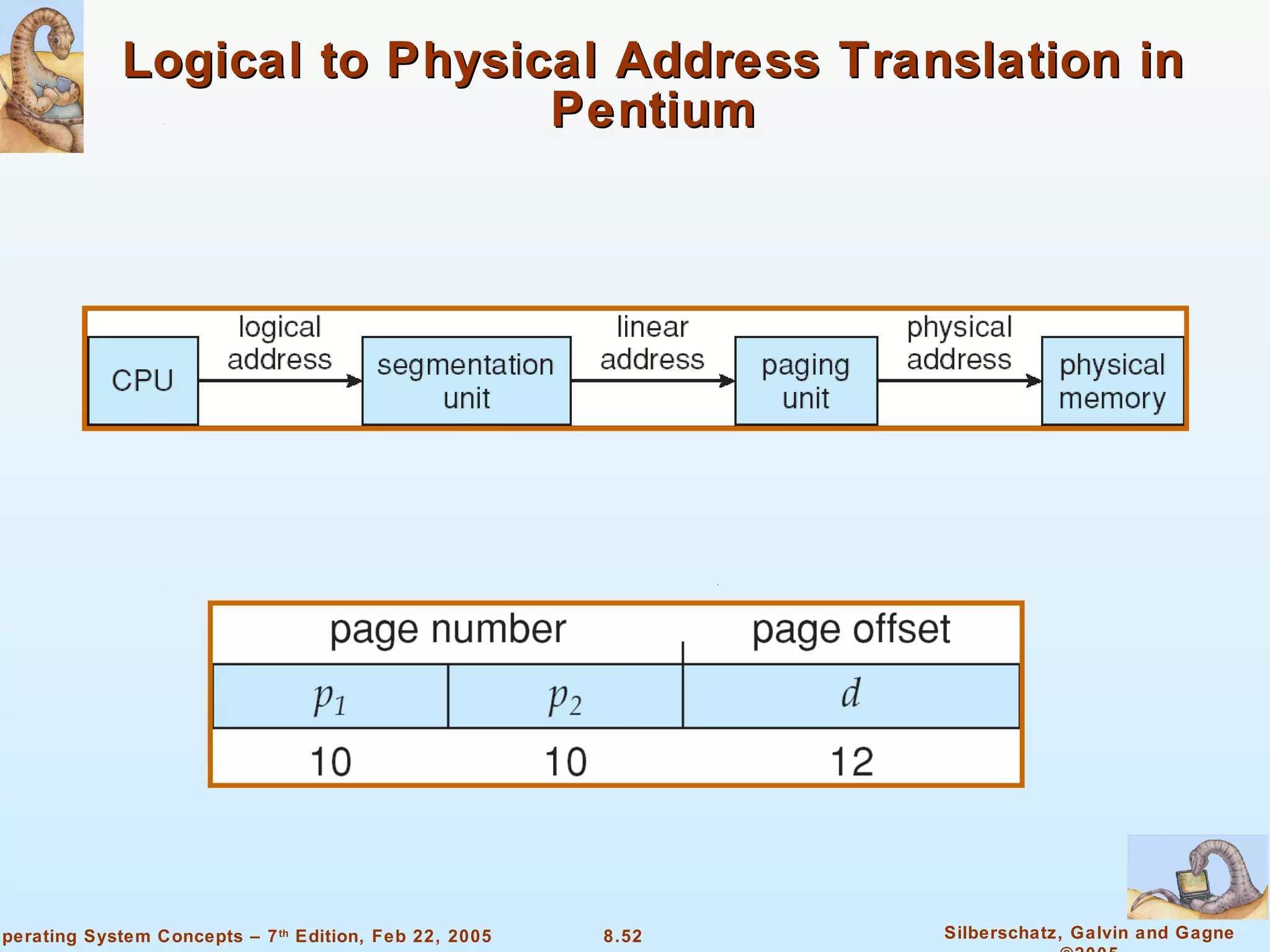
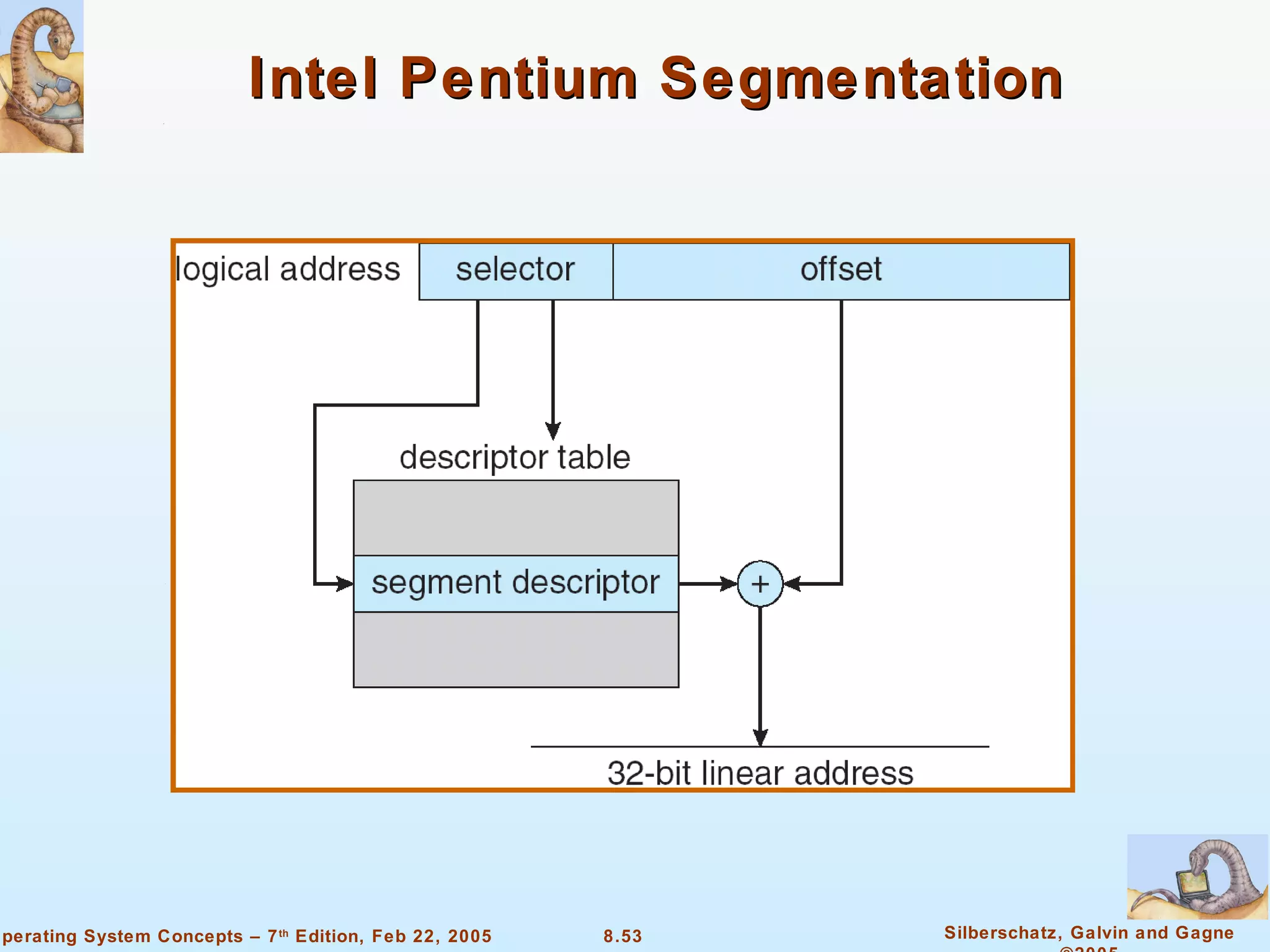
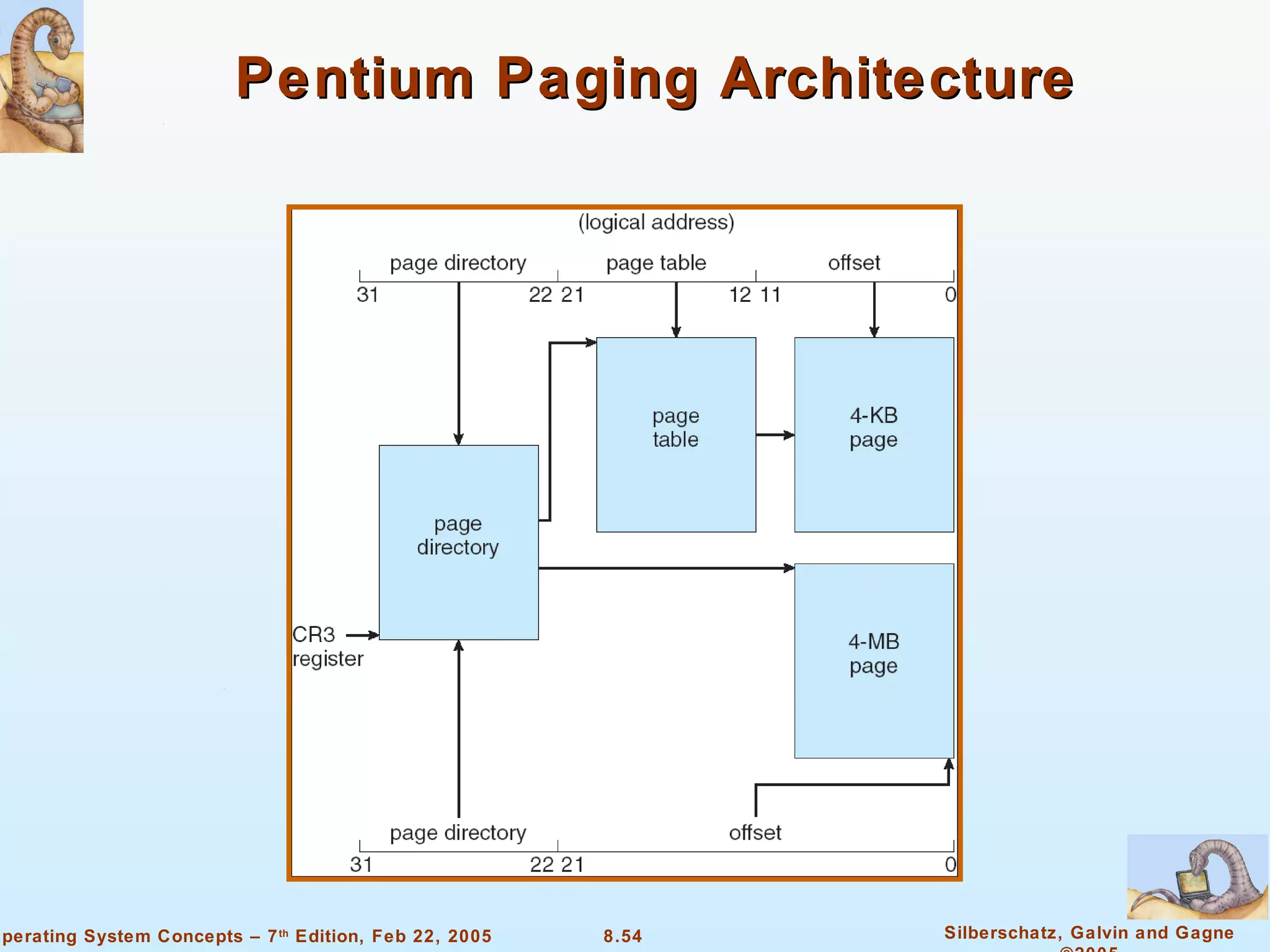
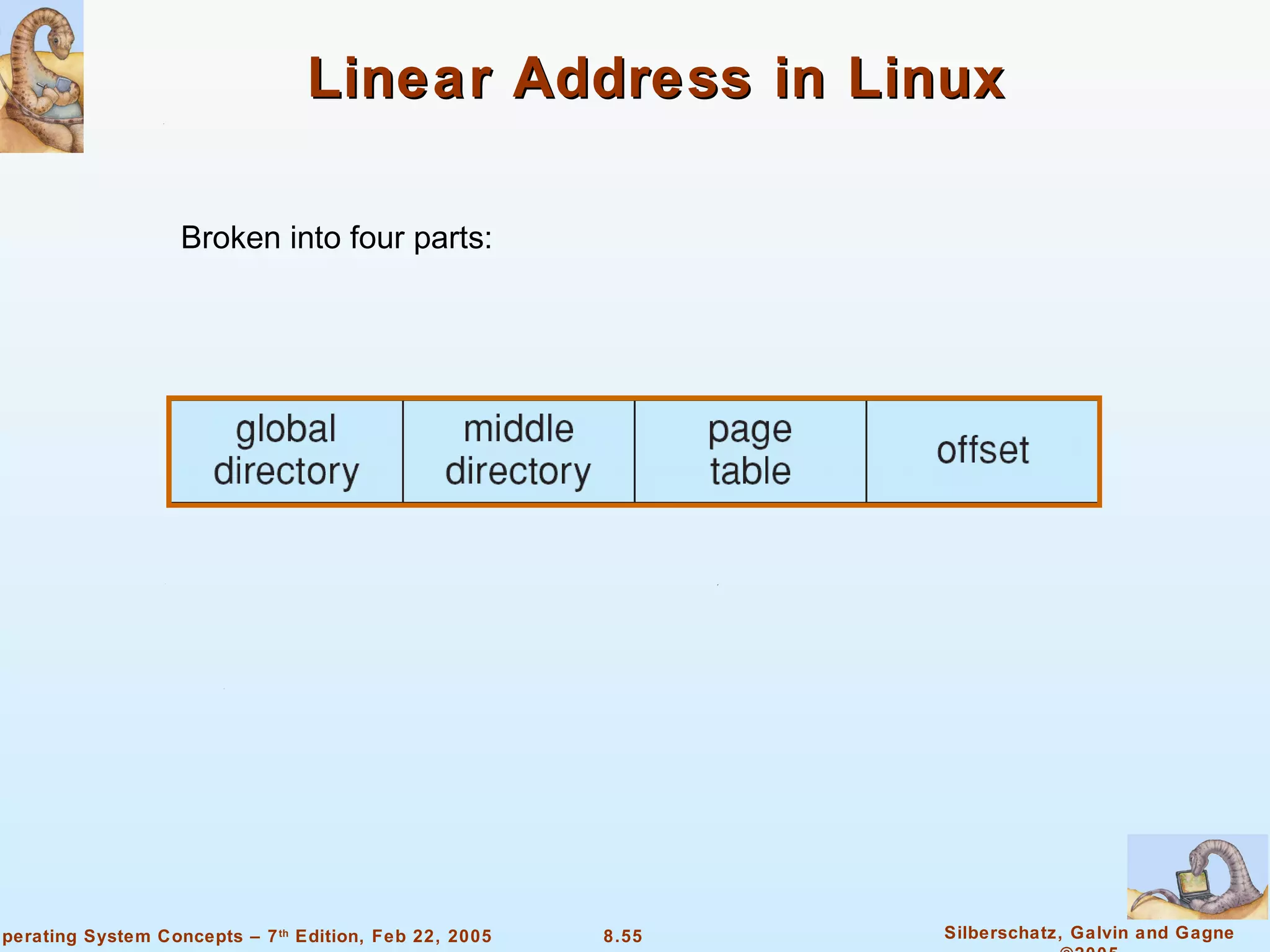
Chapter 8 discusses various memory management techniques such as swapping, paging, and segmentation, detailing how processes are managed in memory. It covers the concepts of logical and physical address space, dynamic memory allocation methods, and the impact of fragmentation on memory utilization. The chapter also provides an overview of the Intel Pentium architecture, which supports both segmentation and paging for effective memory management.