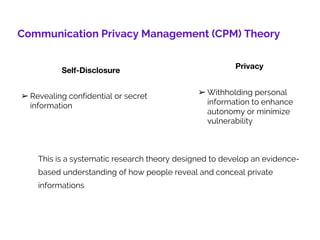
Communication Privacy Management (CPM) Theory proposes a framework for understanding how people decide to disclose or conceal private information. It contains three main parts: privacy ownership of information only known to oneself, privacy control in deciding to share information with others, and privacy turbulence when privacy management does not go as expected. The theory addresses the tension between disclosure and privacy, known as the disclosure-privacy dialectic. It also outlines five principles of disclosure: that people own private information, have boundaries around it, control it through rules, and have ownership over it. CPM Theory aims to understand how people balance disclosure and privacy in relationships.
![Bibliography
1. petronio, s. and durham, w. (2015). Communication management privacy
theory. [online] In.sagepub.com. Available at:
https://in.sagepub.com/sites/default/files/upm-
binaries/64506_Braithwaite_Chapter_25.pdf [Accessed 26 Oct. 2018].
2. petronio, s. (2012). Boundaries of Privacy. [online] Sunypress.edu.
Available at: http://www.sunypress.edu/p-3659-boundaries-of-
privacy.aspx [Accessed 26 Oct. 2018].
14](https://image.slidesharecdn.com/cpm-190407144420/85/Communication-Privacy-Management-Theory-CPM-14-320.jpg)
