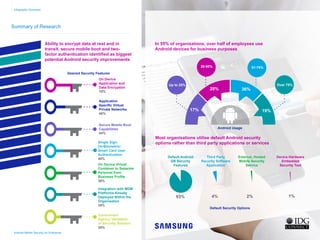
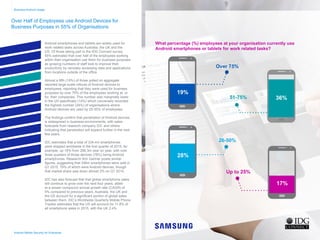
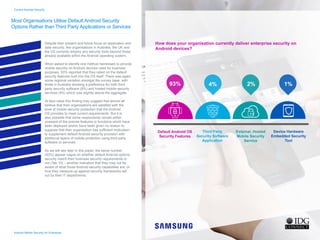
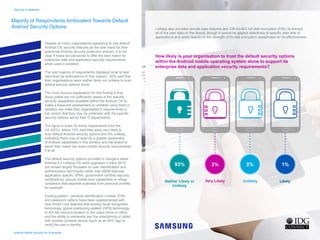
A survey by IDG Connect highlighted that over half of organizations in Australia, the UK, and the US rely on default Android security features for business purposes, with 93% utilizing these built-in options. However, there is a clear demand for improved security measures, such as data encryption and secure mobile boot capabilities, indicating a recognition of potential vulnerabilities in default settings. Despite acknowledging Android's prevalent use in business, organizations express ambivalence regarding the adequacy of current security provisions, emphasizing a critical need for enhanced mobile security strategies.