1) The document discusses Samsung KNOX, a mobile security platform that provides enhanced security and management capabilities for enterprises. It addresses challenges for enterprises around evolving mobility needs and changing employee device preferences.
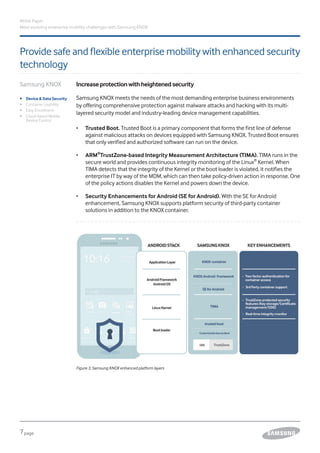
2) Samsung KNOX offers enhanced security features like Trusted Boot and ARM TrustZone to protect devices and data. It also provides improved usability through flexible container usage and easy enrollment processes.
3) The platform provides cloud-based mobile device management and a marketplace for purchasing business apps and KNOX licenses, addressing enterprise security, management and procurement needs from a single source.