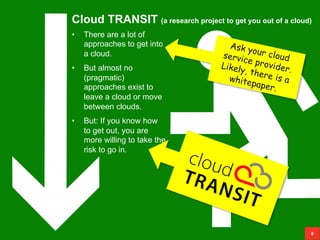
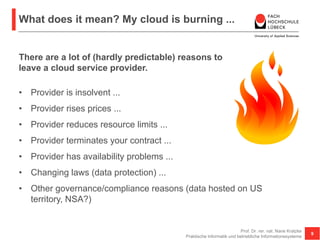
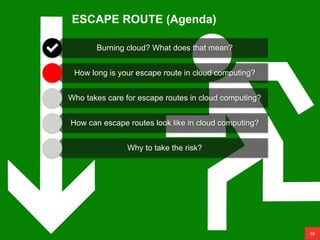
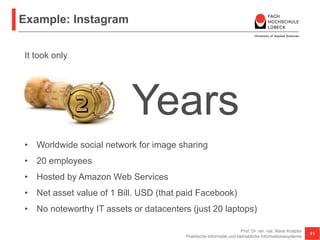
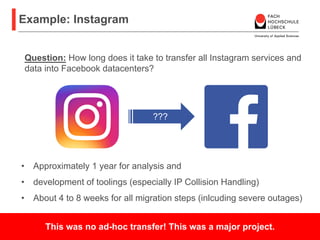
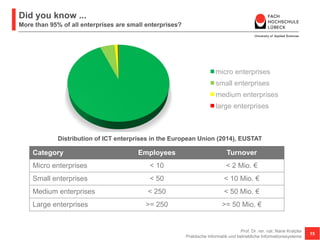
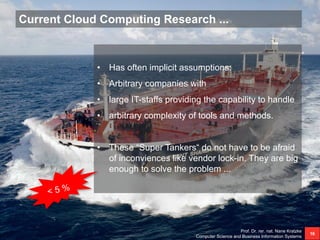
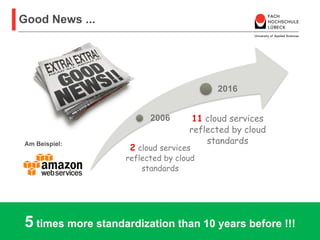
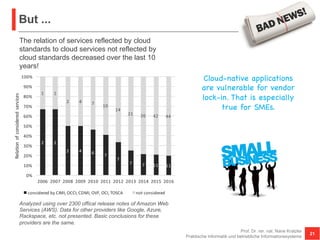
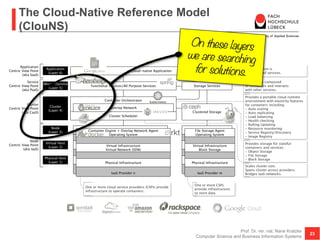
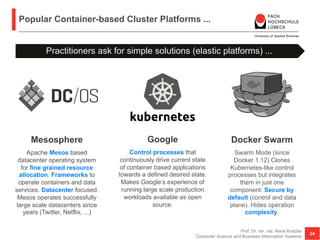
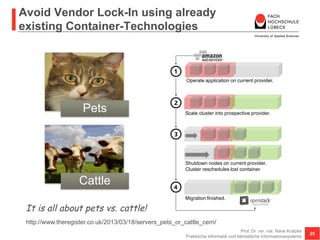
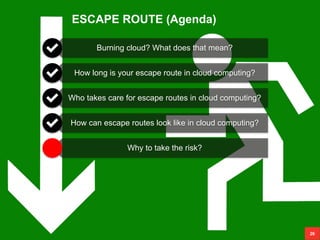
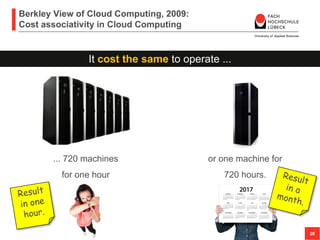
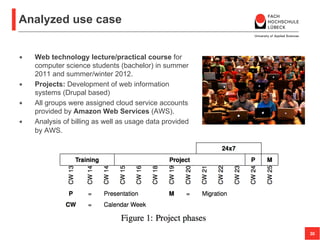
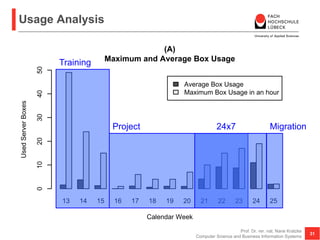
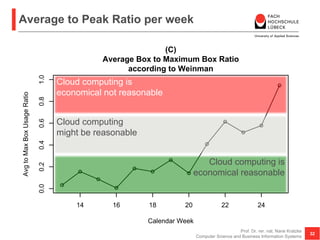
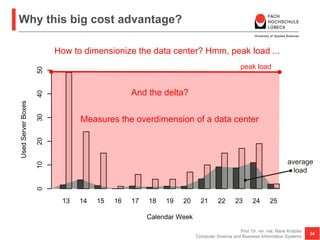
The document discusses the challenges and considerations of cloud computing, particularly focusing on the importance of having an escape route in case a cloud service becomes problematic. It highlights various risks associated with cloud providers, the lack of pragmatic approaches to exit clouds, and emphasizes the need for small and medium enterprises to adopt cloud-native applications while avoiding vendor lock-in. The research promotes the development of strategies and tools that can facilitate transitions between cloud services to ensure flexibility and risk management.