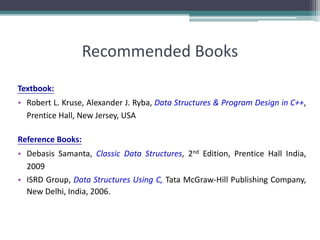
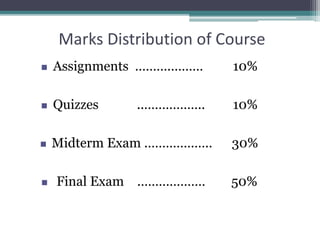
The document outlines a course on Data Structures and Algorithms, detailing course objectives, goals, and a comprehensive outline of topics to be covered, including different data structures, algorithms, and their applications. It highlights the importance of systematic programming approaches and methodologies for managing complex data in engineering projects. Additionally, it discusses course assessments and recommended textbooks for further reading.
![Introducing Arrays
Array is a data structure that represents a collection
of the same types of data.
myList[0]
myList[1]
myList[2]
myList[3]
myList[4]
myList[5]
myList[6]
myList[7]
myList[8]
myList[9]
double[] myList = new double[10];
myList reference
An Array of 10
Elements
of type double](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-18-320.jpg)
![Declaring Array Variables
• datatype[] arrayname;
Example:
double[] myList;
• datatype arrayname[];
Example:
double myList[];](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-19-320.jpg)
![Creating Arrays
arrayName = new datatype[arraySize];
Example:
myList = new double[10];
myList[0] references the first element in the array.
myList[9] references the last element in the array.](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-20-320.jpg)
![Declaring and Creating in One Step
• datatype[] arrayname = new
datatype[arraySize];
double[] myList = new double[10];
• datatype arrayname[] = new
datatype[arraySize];
double myList[] = new double[10];](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-21-320.jpg)
![Initializing Arrays
• Using a loop:
for (int i = 0; i < myList.length; i++)
myList[i] = i;
• Declaring, creating, initializing in one step:
double[] myList = {1.9, 2.9, 3.4, 3.5};
This shorthand syntax must be in one statement.](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-23-320.jpg)
![Declaring, creating, initializing Using the
Shorthand Notation
double[] myList = {1.9, 2.9, 3.4, 3.5};
This shorthand notation is equivalent to the following
statements:
double[] myList = new double[4];
myList[0] = 1.9;
myList[1] = 2.9;
myList[2] = 3.4;
myList[3] = 3.5;](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-24-320.jpg)
![CAUTION
Using the shorthand notation, you have to
declare, create, and initialize the array all in
one statement. Splitting it would cause a
syntax error. For example, the following is
wrong:
double[] myList;
myList = {1.9, 2.9, 3.4, 3.5};](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-25-320.jpg)
![Example
swapFirstTwoInArray(a)
swapFirstTwoInArray(array)
Pass by value (Reference value)
a Reference
:
a[0]
a[1]
array Reference
swap(a[0], a[1])
swap( n1, n2)
Pass by value
a[0] 1 2
n1 n21 2
a[1]](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-29-320.jpg)
![Copying Arrays
Using a loop:
int[] sourceArray = {2, 3, 1, 5, 10};
int[] targetArray = new int[sourceArray.length];
for (int i = 0; i < sourceArrays.length; i++)
targetArray[i] = sourceArray[i];](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-32-320.jpg)
![Multidimensional Arrays
Declaring Variables of Multidimensional Arrays and Creating
Multidimensional Arrays
int[][] matrix = new int[10][10];
or
int matrix[][] = new int[10][10];
matrix[0][0] = 3;
for (int i=0; i<matrix.length; i++)
for (int j=0; j<matrix[i].length; j++)
{
matrix[i][j] = (int)(Math.random()*1000);
}
double[][] x;](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-33-320.jpg)
![Multidimensional Array Illustration
0 1 2 3 4
0
7
0 1 2 3 4
1
2
3
4
0
1
2
3
4
matrix[2][1] = 7;matrix = new int[5][5];
3
7
0 1 2
0
1
2
int[][] array = {
{1, 2, 3},
{4, 5, 6},
{7, 8, 9},
{10, 11, 12}
};
1 2 3
4 5 6
8 9
10 11 12](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-34-320.jpg)
![Declaring, Creating, and Initializing Using Shorthand
Notations
You can also use a shorthand notation to declare, create and initialize a two-dimensional
array. For example,
int[][] array = {
{1, 2, 3},
{4, 5, 6},
{7, 8, 9},
{10, 11, 12}
};
This is equivalent to the following statements:
int[][] array = new int[4][3];
array[0][0] = 1; array[0][1] = 2; array[0][2] = 3;
array[1][0] = 4; array[1][1] = 5; array[1][2] = 6;
array[2][0] = 7; array[2][1] = 8; array[2][2] = 9;
array[3][0] = 10; array[3][1] = 11; array[3][2] = 12;](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-35-320.jpg)
![Lengths of Multidimensional Arrays
int[][] array = {
{1, 2, 3},
{4, 5, 6},
{7, 8, 9},
{10, 11, 12}
};
array.length
array[0].length
array[1].length
array[2].length](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-36-320.jpg)
![Arrays and Pointers
• Arrays and pointers are closely related in C
▫ In fact, they are essentially the same thing!
▫ Esp. when used as parameters of functions
• int A[10];
int *p;
▫ Type of A is int *
▫ p = A; and A = p; are legal assignments
▫ *p refers to A[0]
*(p + n) refers to A[n]
▫ p = &A[5]; is the same as p = A + 5;](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-47-320.jpg)
![Arrays and Pointers (continued)
• double A[10]; vs. double *A;
• Only difference:–
▫ double A[10] sets aside ten units of memory, each large
enough to hold a double
▫ double *A sets aside one pointer-sized unit of memory
You are expected to come up with the memory elsewhere!
▫ Note:– all pointer variables are the same size in any given
machine architecture
Regardless of what types they point to](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-48-320.jpg)
![Note
• C does not assign arrays to each other
• E.g,
▫ double A[10];
double B[10];
A = B;
assigns the pointer value B to the pointer value A
Contents of array A are untouched](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-49-320.jpg)
![Arrays as Function Parameters
• void init(float A[], int arraySize);
void init(float *A, int arraySize);
• Are identical function prototypes!
• Pointer is passed by value
• I.e. caller copies the value of a pointer to float into the
parameter A
• Called function can reference through that pointer to
reach thing pointed to](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-50-320.jpg)
![Arrays as Function Parameters (continued)
• void init(float A[], int arraySize){
int n;
for(n = 0; n < arraySize; n++)
A[n] = (float)n;
} //init
• Assigns values to the array A in place
▫ So that caller can see the changes!](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-51-320.jpg)
![Examples
while ((rc = scanf("%lf", &array[count])) !=EOF && rc==0)
…
double getLargest(const double A[], const int sizeA) {
double d;
if (sizeA > 0) {
d = getLargest(&A[1], sizeA-1);
return (d > A[0]) ? d : A[0];
} else
return A[0];
} // getLargest](https://image.slidesharecdn.com/week1-introtodatastructuresalgorithms-191013065805/85/Introduction-to-Data-Structures-Algorithms-52-320.jpg)