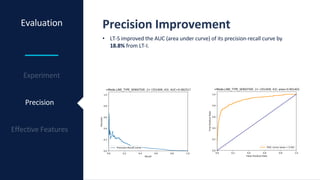
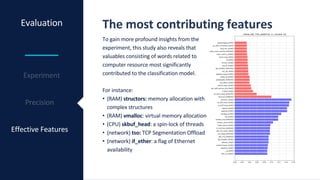
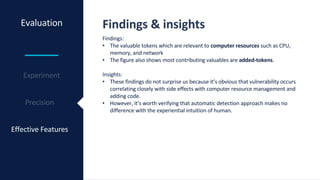
This document discusses a methodology for detecting vulnerabilities in software based on analysis of the project's Git history. It proposes an approach called HVD that considers whether lines of code were added or removed in code changes, which could improve precision over existing techniques. An evaluation using a dataset of over 350,000 commits found that HVD increased the area under the precision-recall curve by 18.8% compared to a baseline that ignores line additions and removals. Features related to computer resources like memory, CPU and networking were found to most significantly contribute to the classification model. The study demonstrates that automatically detecting vulnerabilities from Git data can produce results aligned with human intuition.

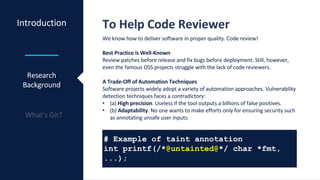
![Introduction
Research
Background
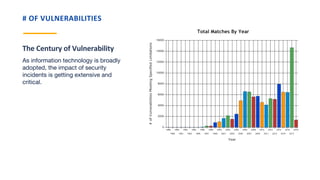
The Trend of Security Incidents
Key facts. Why this research is important:
In Quantity
# of CVE reports: 1,020 (2000) → 14,643 (2017) [NVD]
In Quality
• Equifax exposed 143M consumers’ data due to website application
vulnerability (2017)
• Yahoo breached 3B users’ account information (2013)](https://image.slidesharecdn.com/jp2nklqragif0gp7vwf7-signature-da1fe7642b741c6924a84a6a9dedce997f29c79b7e1267a8b6d00d6ecbe38b5d-poli-180402033406/85/Vulnerability-Detection-Based-on-Git-History-3-320.jpg)
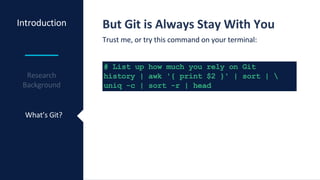
![Introduction
What’s Git?
Git for Machine Learning
Git provides what machine learning requires; good data:
• Adopted by 69.2% of 30K developers [StackOverfow]
• Trusted by most prominent OSS projects such as Linux
Kernel, OpenSSL, FFmpeg, PostgreSQL, Chrome V8, and
Apache HTTPD.](https://image.slidesharecdn.com/jp2nklqragif0gp7vwf7-signature-da1fe7642b741c6924a84a6a9dedce997f29c79b7e1267a8b6d00d6ecbe38b5d-poli-180402033406/85/Vulnerability-Detection-Based-on-Git-History-9-320.jpg)

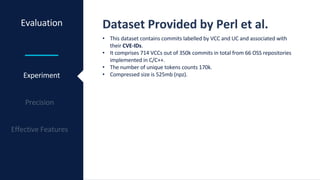
![Methodology Proposal Approach
Concept
• This research proposes the approach which aims to
reduce the false positive rate compared to VCCFinder
[Perl et al] without sacrificing adaptability.
• The data source is the same to VCCFinder but this
approach takes account of added-lines and removed-
lines in patch feature while VCCFinder doesn’t.](https://image.slidesharecdn.com/jp2nklqragif0gp7vwf7-signature-da1fe7642b741c6924a84a6a9dedce997f29c79b7e1267a8b6d00d6ecbe38b5d-poli-180402033406/85/Vulnerability-Detection-Based-on-Git-History-14-320.jpg)