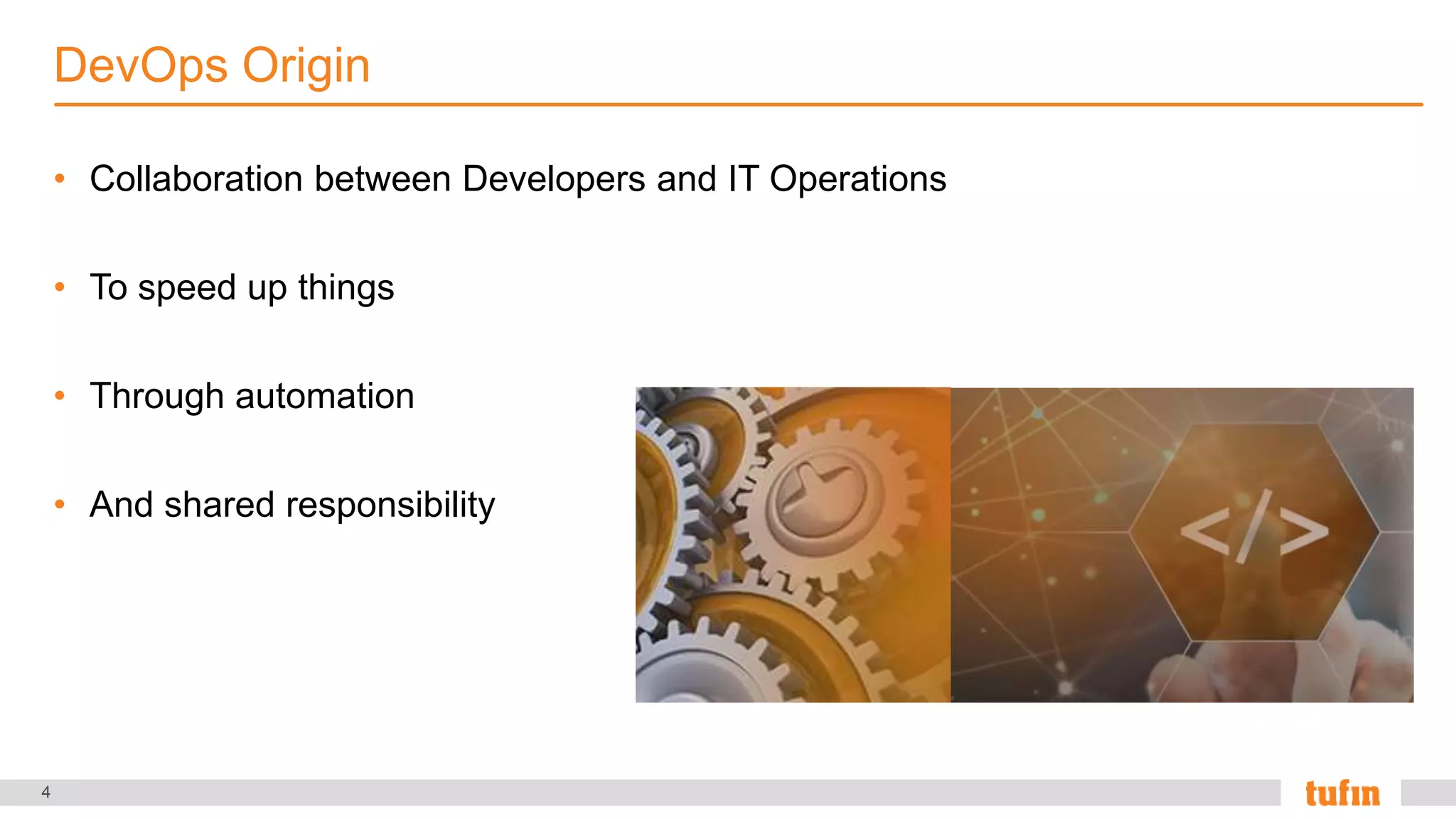
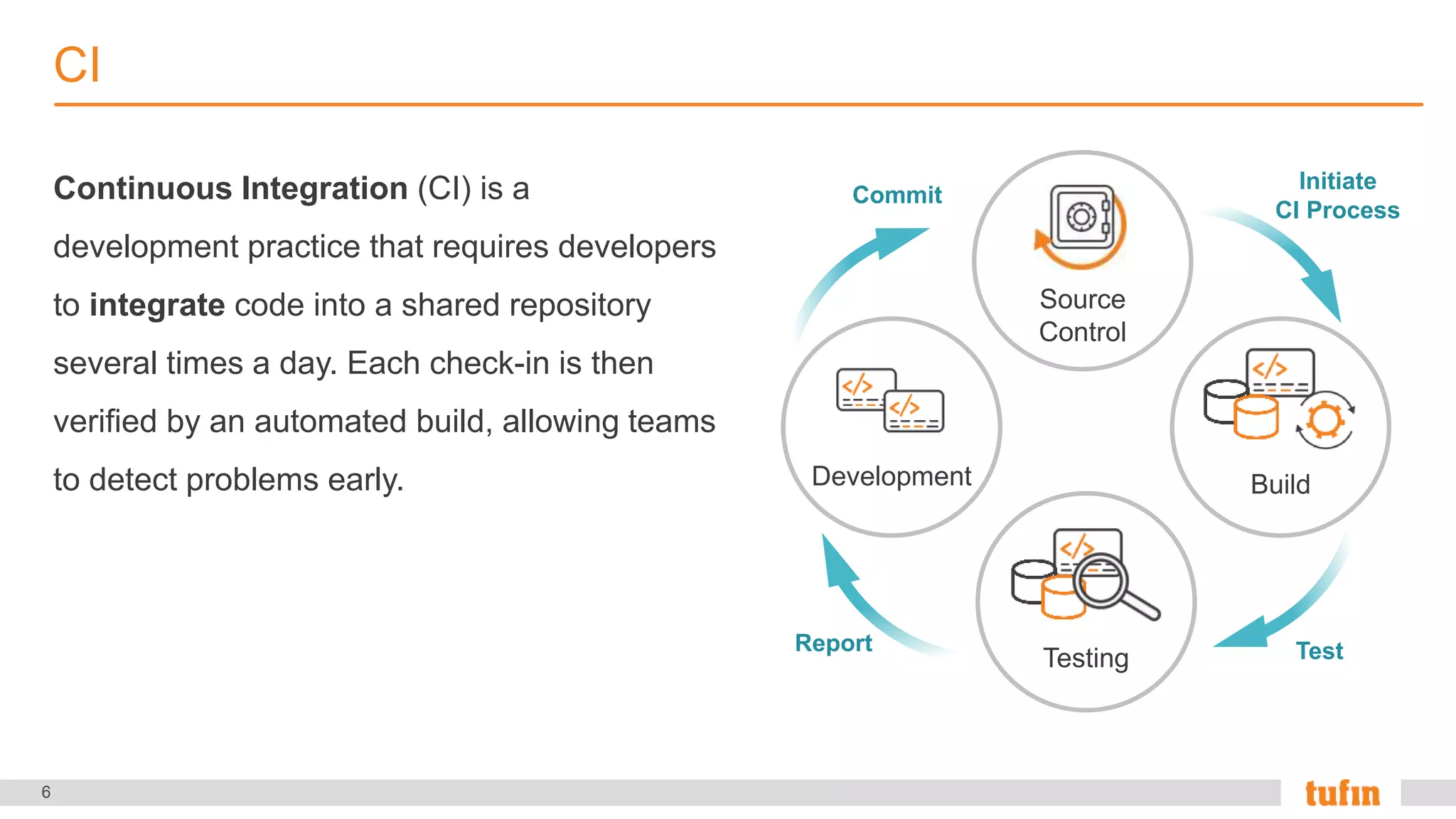
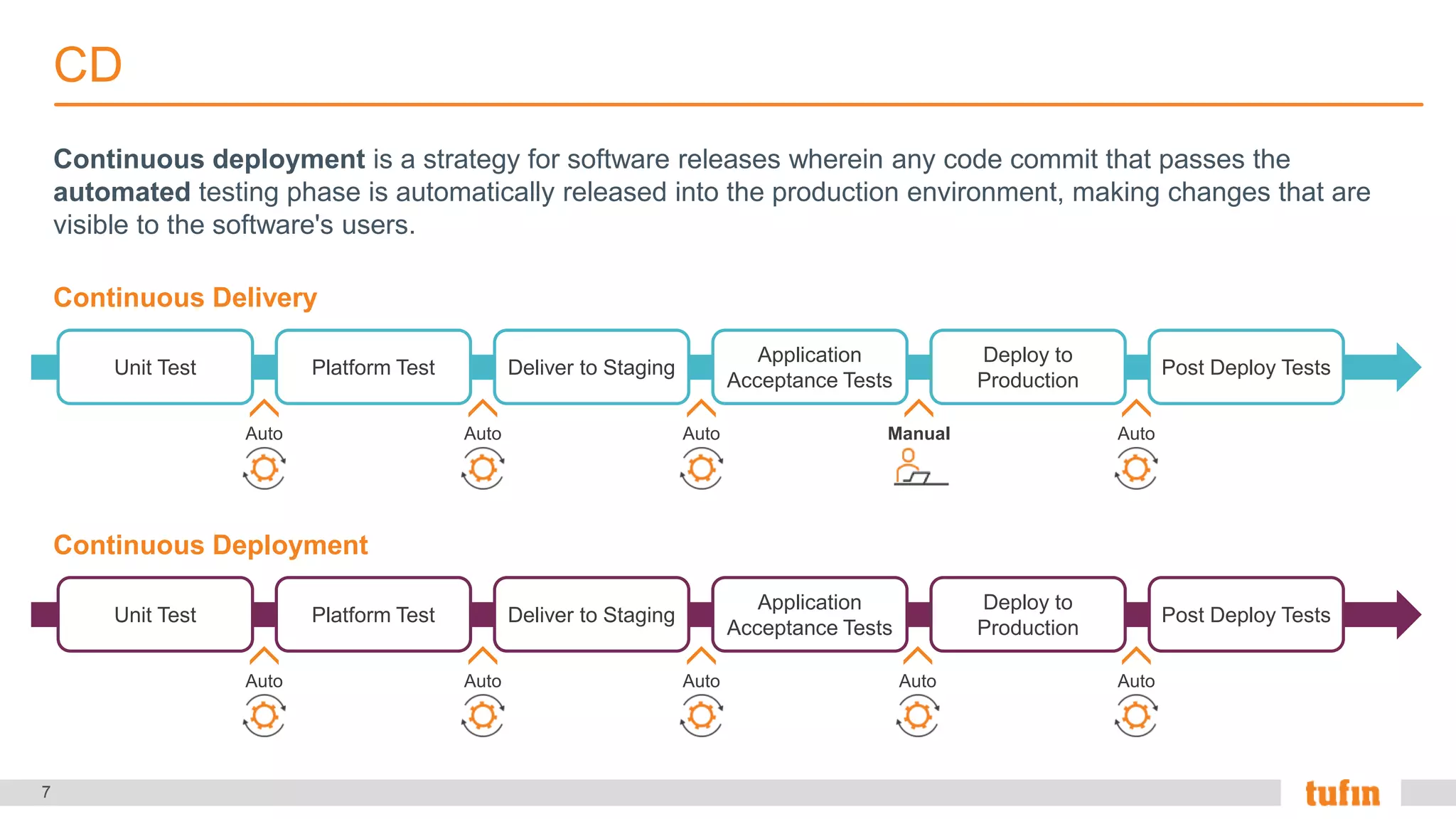
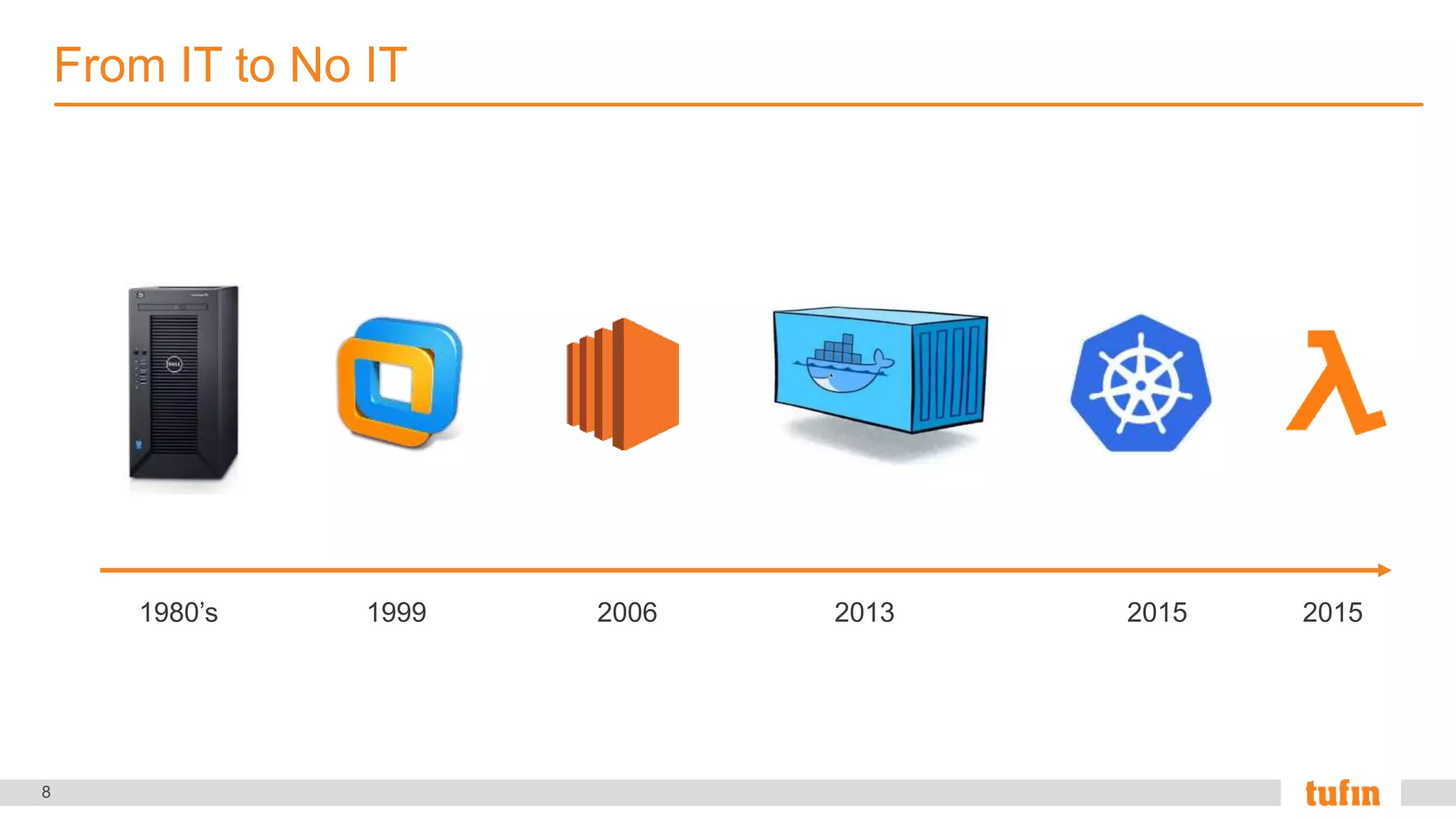
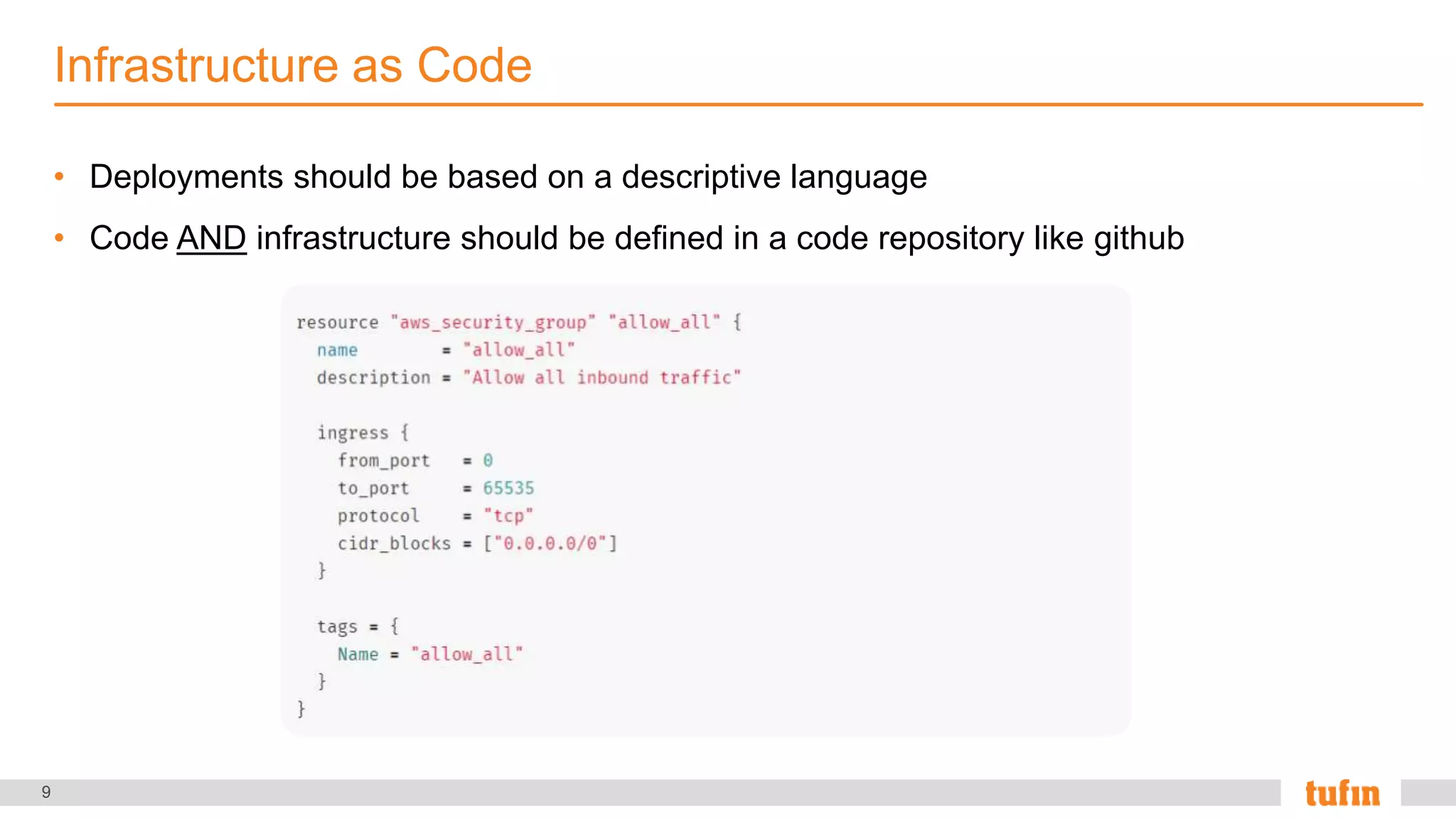
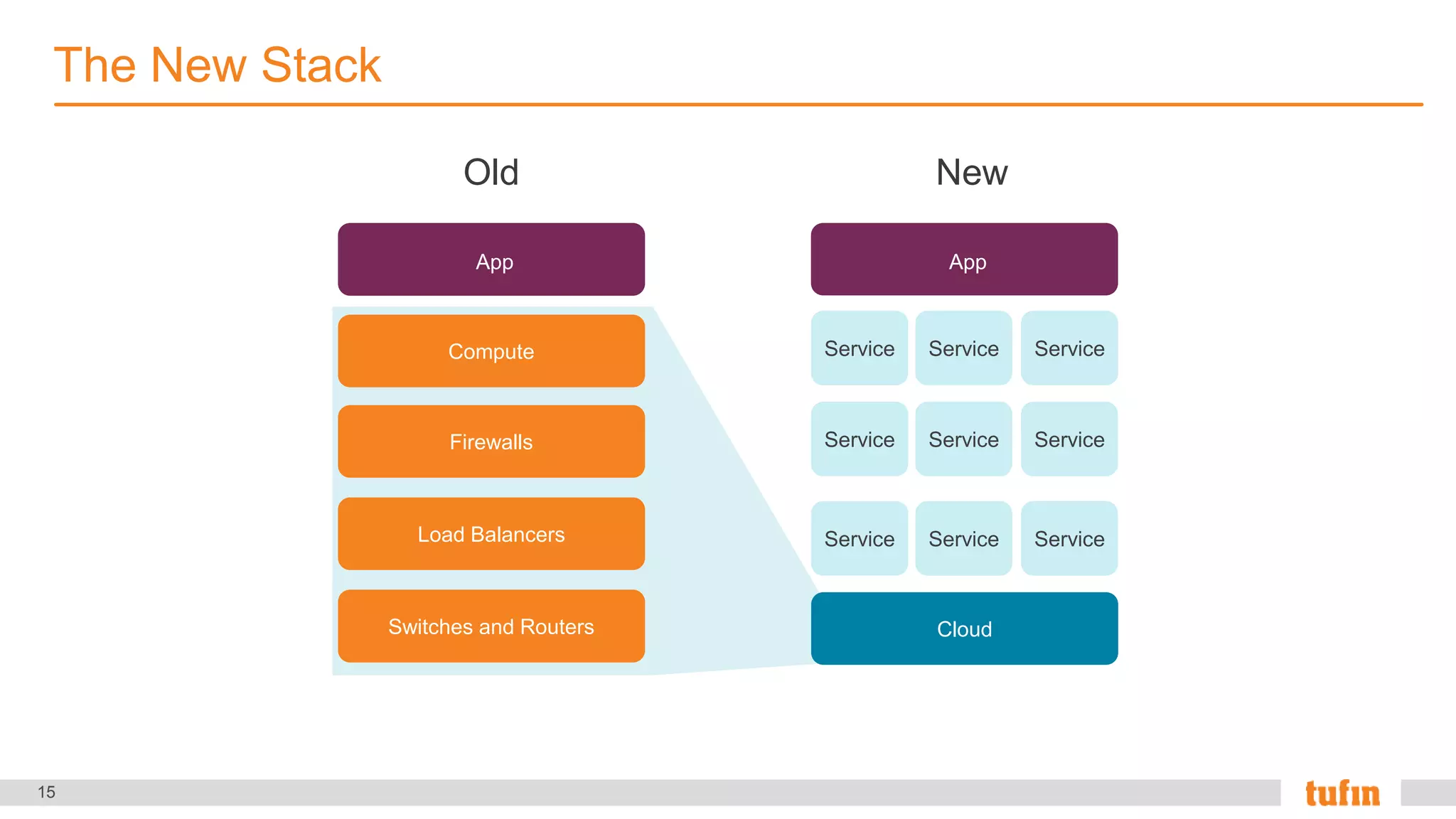
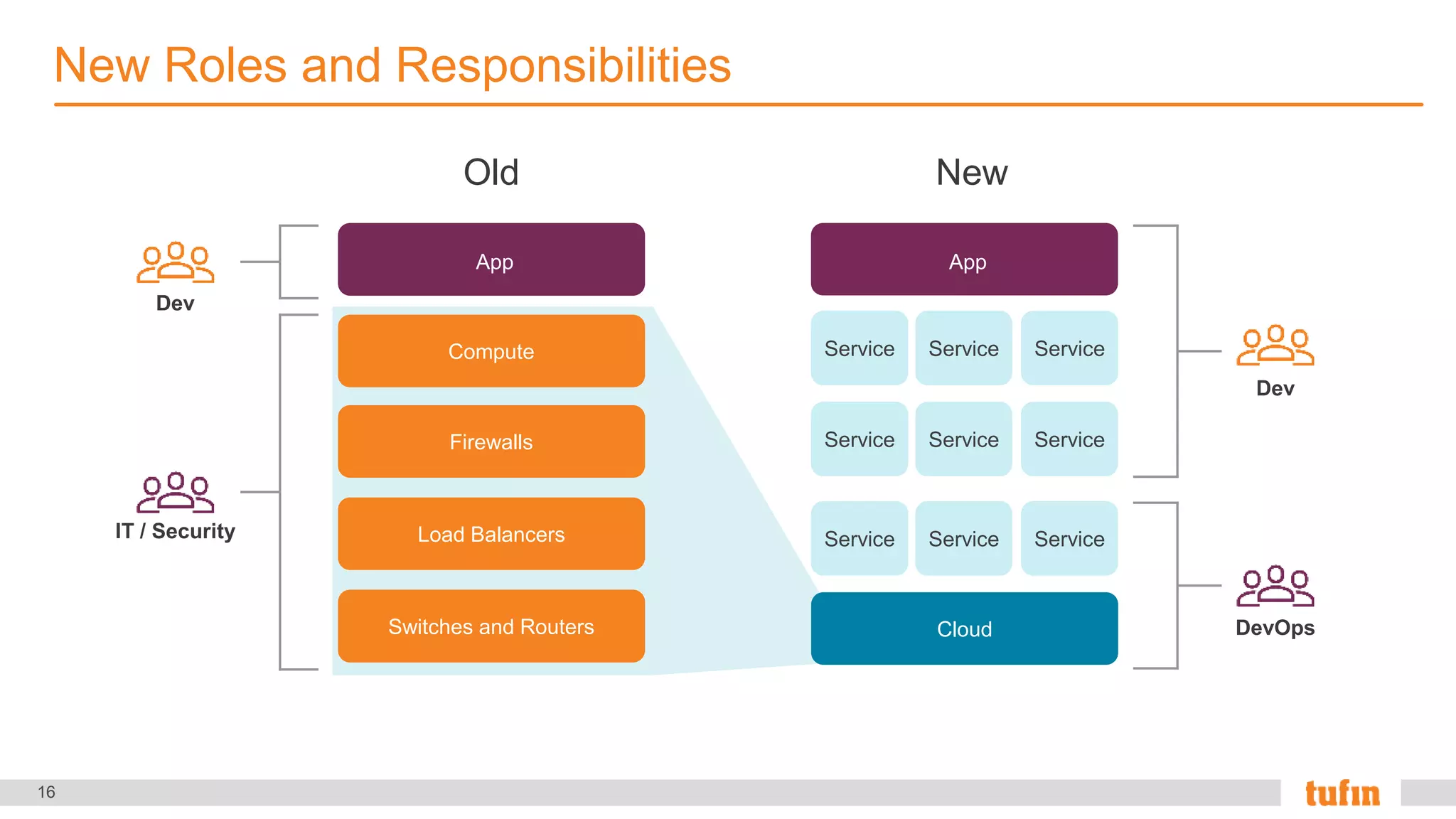
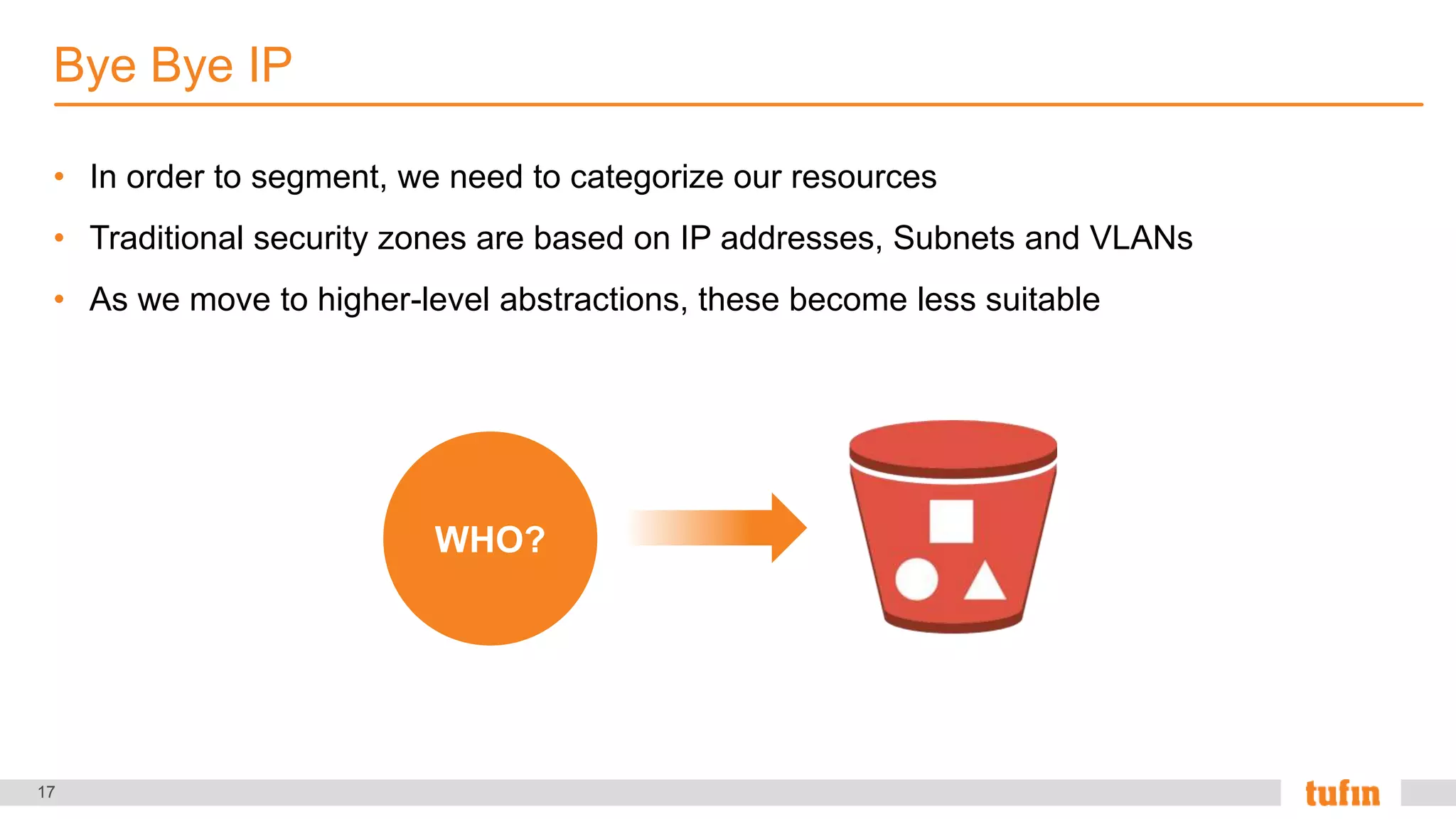
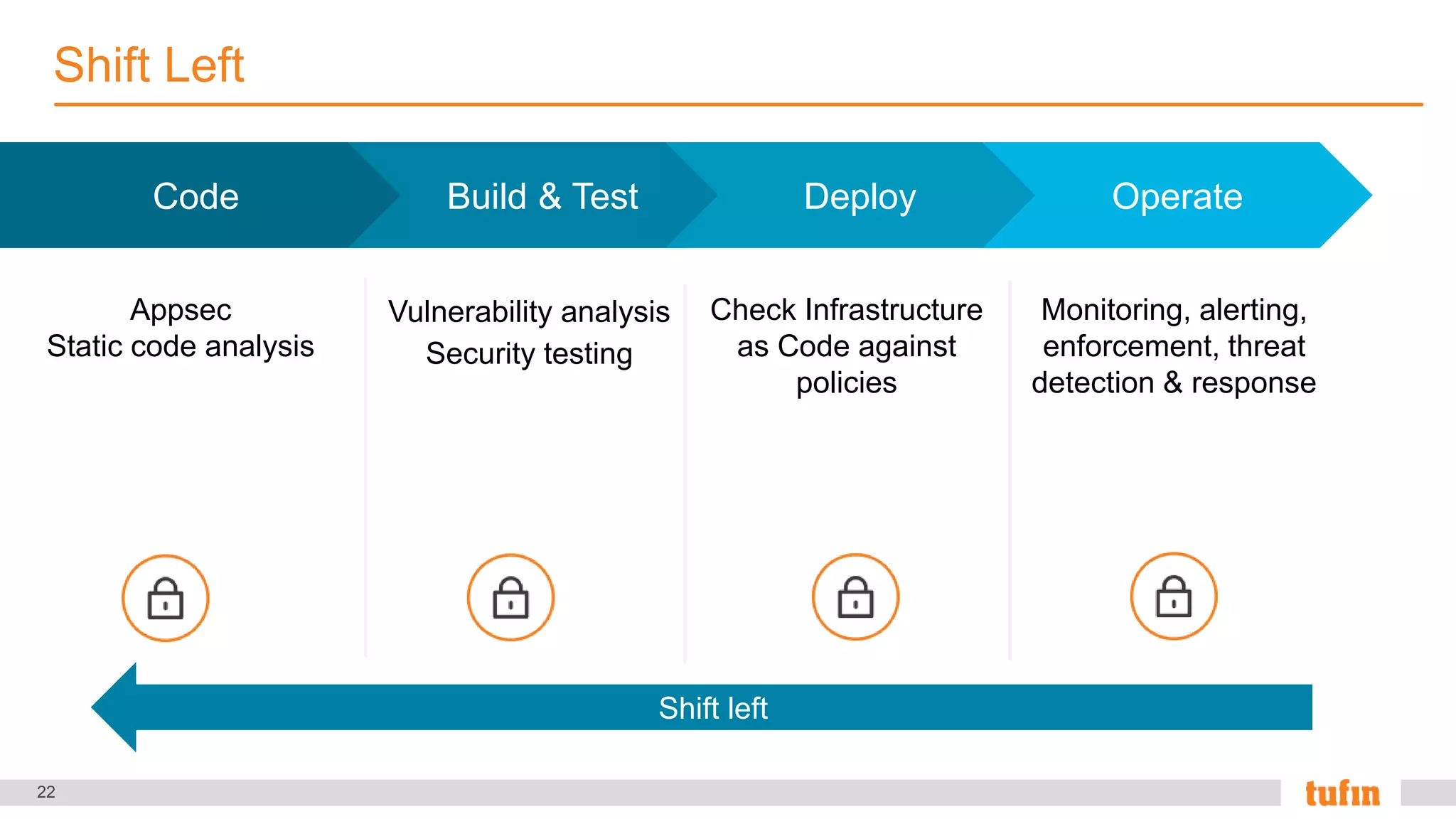
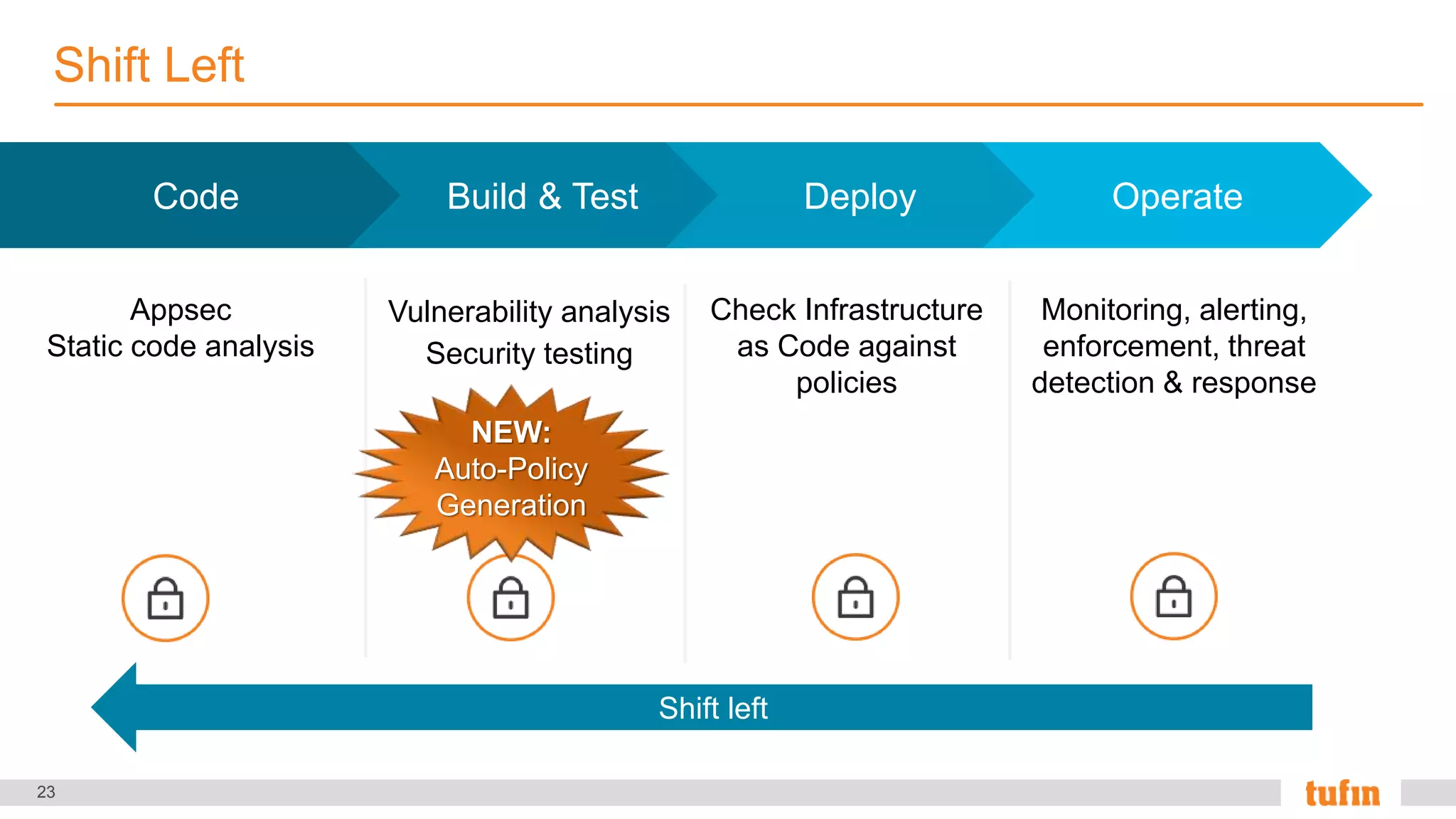
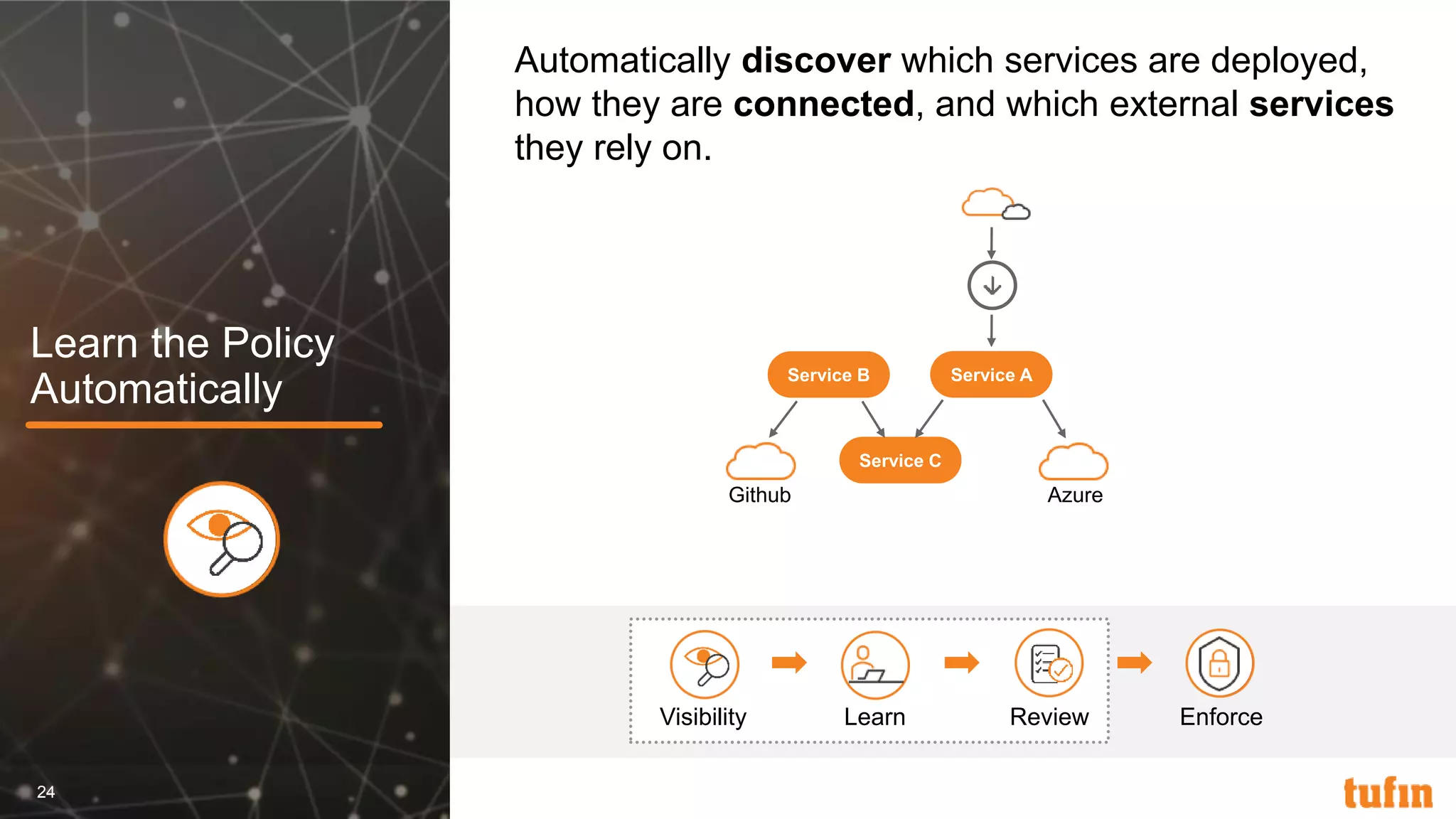
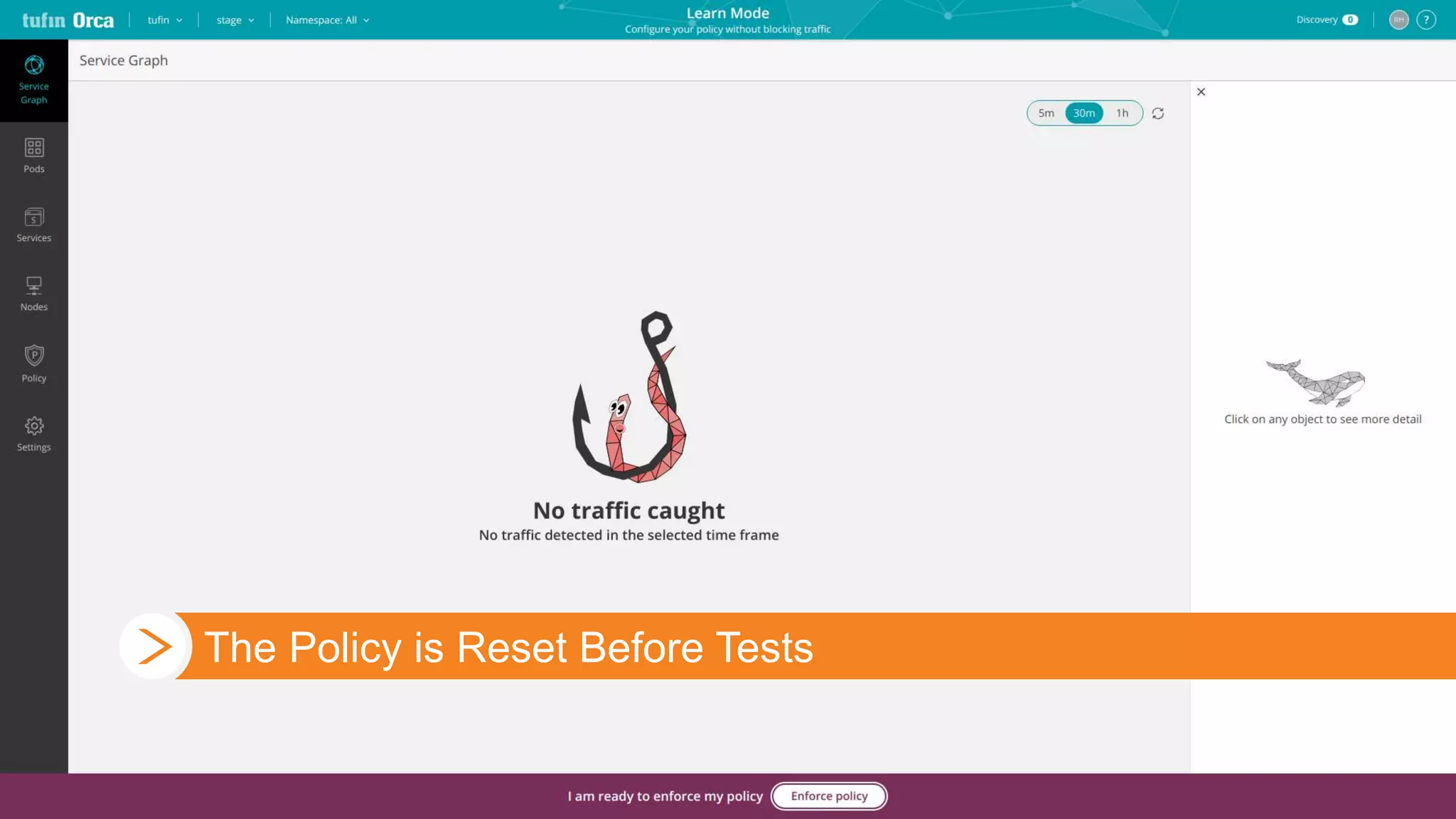
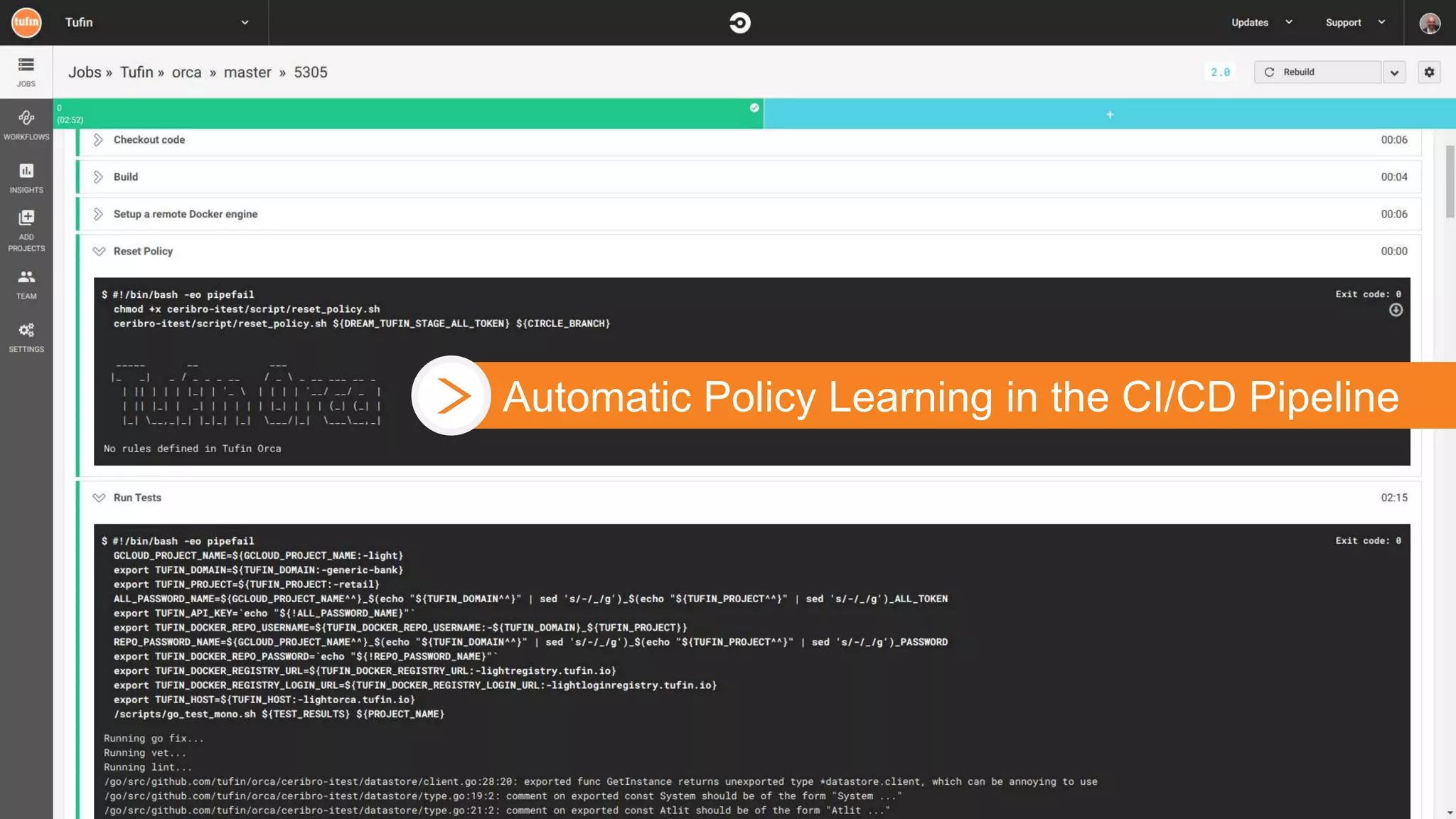
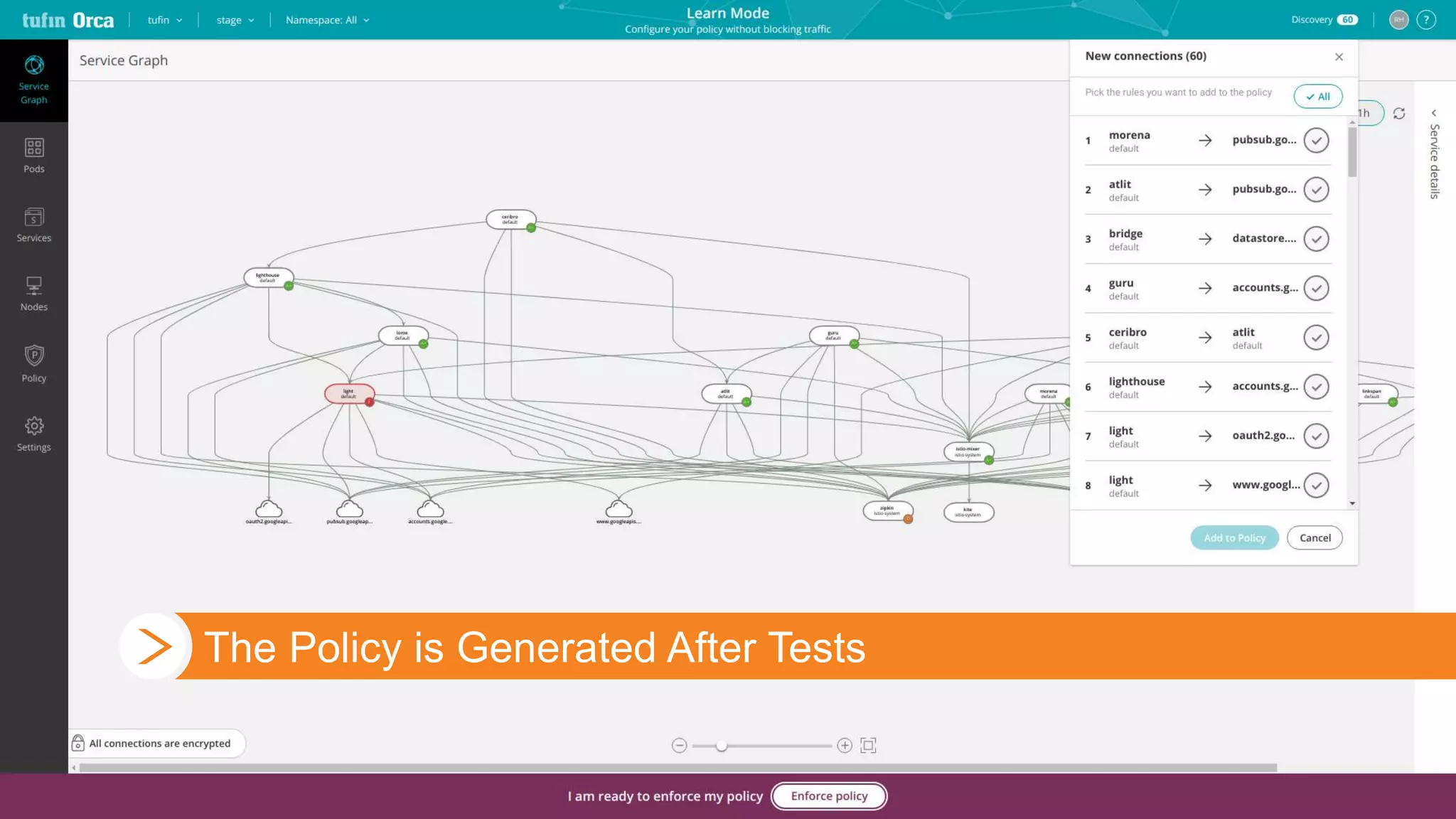
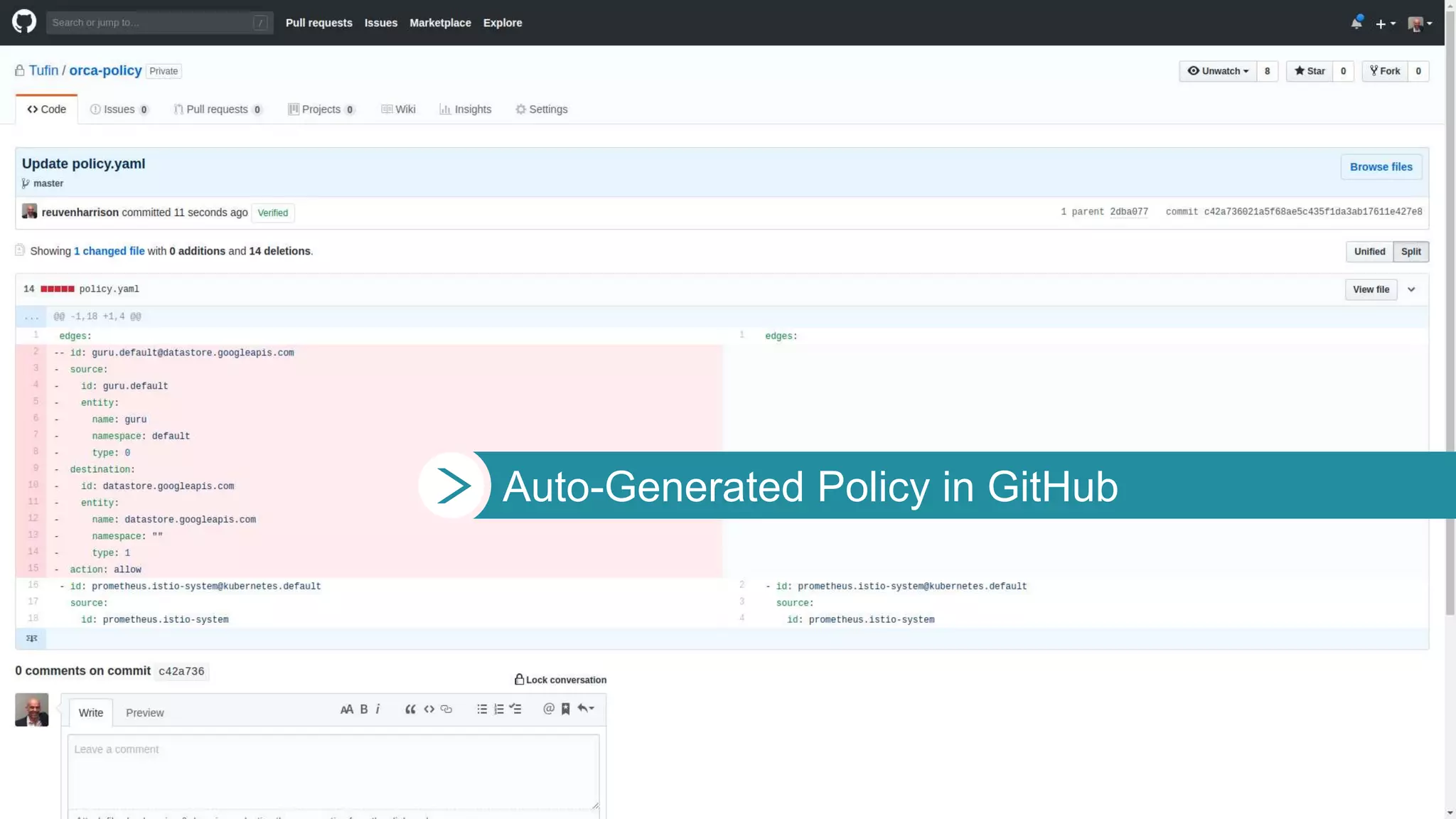
The document discusses the relationship between DevOps and security teams, highlighting the need for collaboration to enhance security within the DevOps framework. It explains DevOps concepts such as continuous integration and continuous deployment, and emphasizes the importance of adopting new security practices suited for cloud-native environments. The document advocates for integrating security into DevOps processes through automated policy generation and collaboration to improve overall security effectiveness.

![2
Yes, we have a DevOps team. I have no idea
what they’re up to, but my team [Security] is
responsible for securing their apps.
“
”
—Tufin Customer
2018](https://image.slidesharecdn.com/devopsvssecurity-190308011259/75/Are-your-DevOps-and-Security-teams-friends-or-foes-2-2048.jpg)