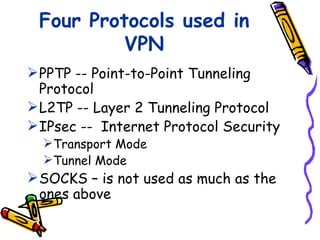
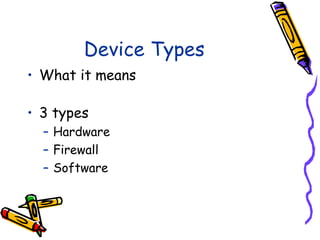
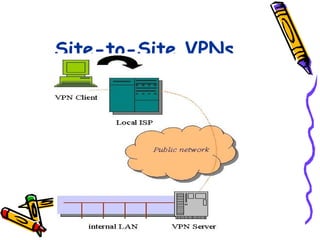
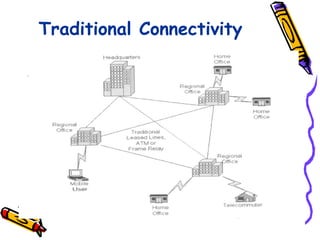
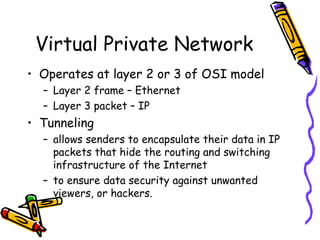
Tunneling in VPNs refers to the process of encapsulating VPN data packets within regular IP packets for transmission through a public network like the Internet. This encapsulation creates a "tunnel" between the VPN endpoints that provides security and allows private network traffic to be carried across a shared infrastructure.
![Tunneling
A virtual point-to-point connection
made through a public network. It
transports encapsulated datagrams.
Original Datagram
Encrypted Inner Datagram
Datagram Header Outer Datagram Data Area
Data Encapsulation [From Comer]
Two types of end points:
Remote Access
Site-to-Site](https://image.slidesharecdn.com/vpnnetworks-120508054611-phpapp01/85/Vpn-networks-kami-10-320.jpg)