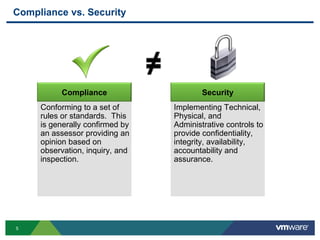
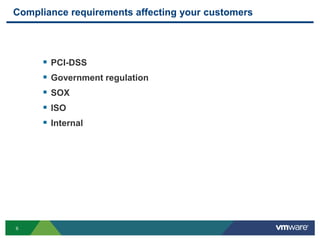
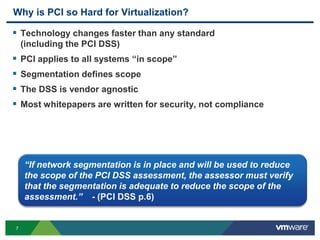
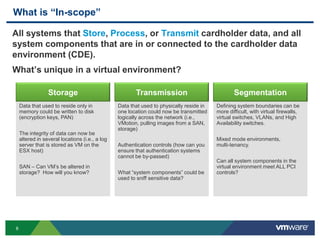
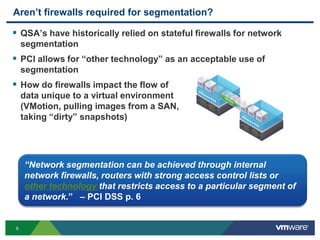
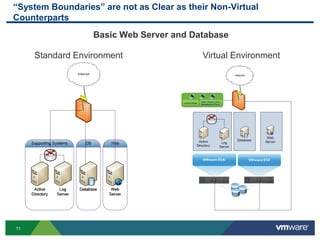
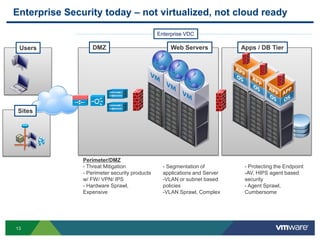
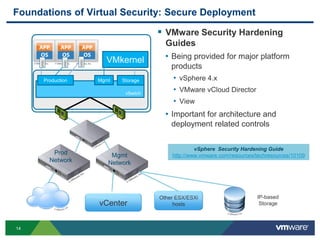
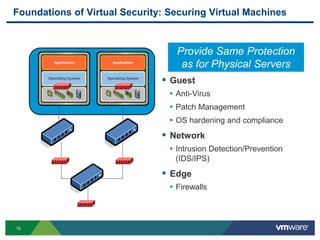
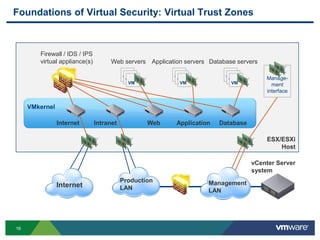
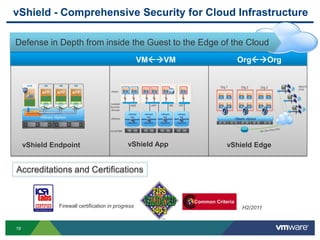
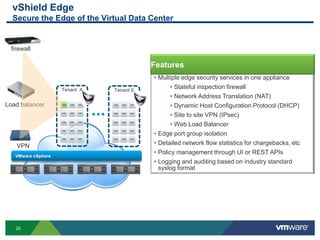
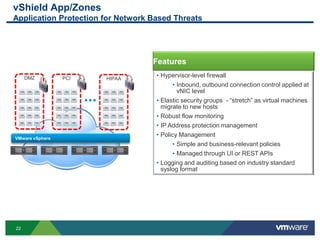
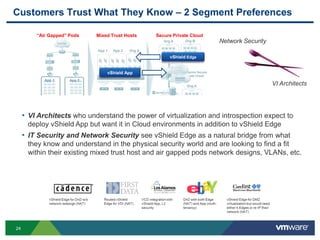
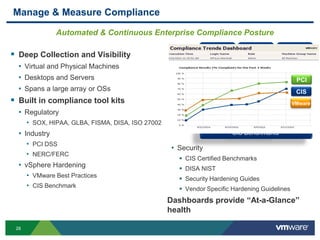
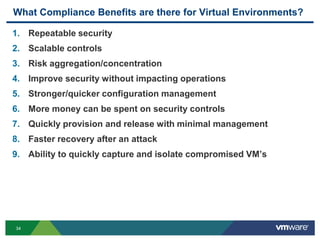
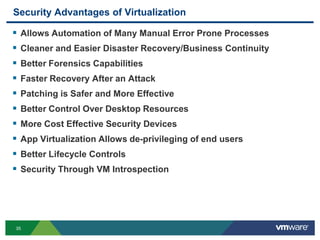
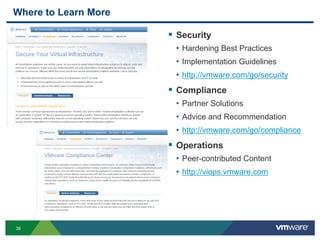
The document discusses security and compliance requirements for cloud computing. It provides an overview of key compliance standards and regulations that affect customers. It then discusses some of the unique security challenges that virtualized and cloud environments can present compared to traditional IT environments. Specifically, it notes that system boundaries are less clear in virtual systems and that more components and complexity are involved. Finally, it outlines some of the foundations that VMware and its partners are providing to help address these challenges, such as security hardening guides, virtual trust zones, and network segmentation controls.