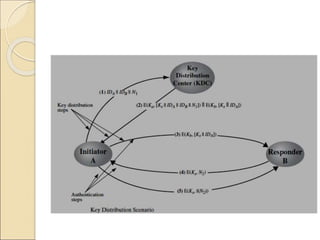
The document discusses various authentication applications and protocols including Kerberos, X.509, PKI, PGP, and S/MIME. It provides details on:
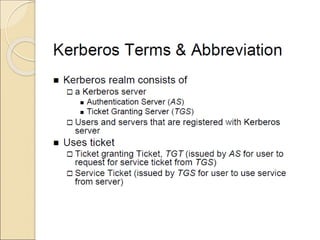
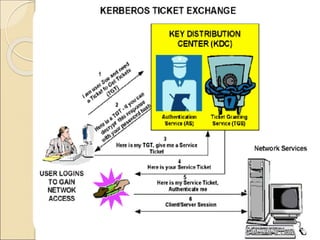
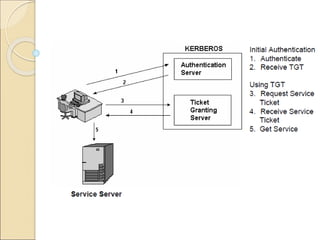
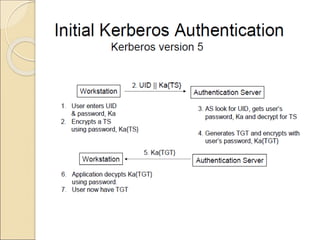
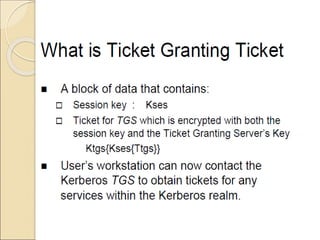
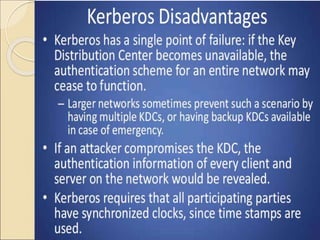
- Kerberos uses tickets to allow secure communication over non-secure networks.
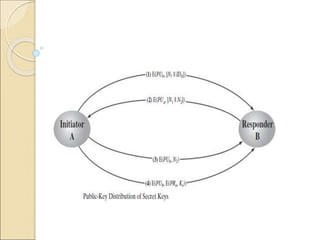
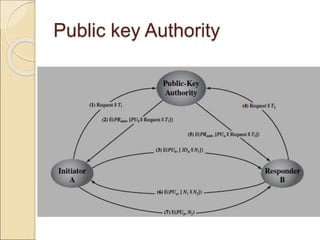
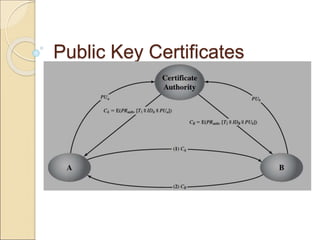
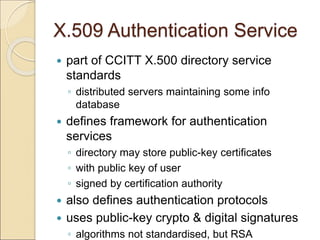
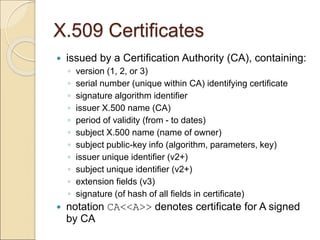
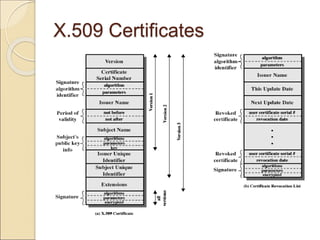
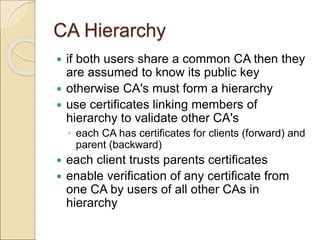
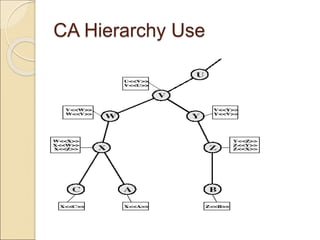
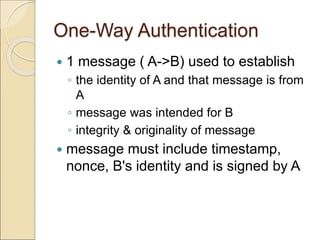
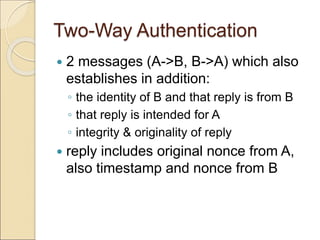
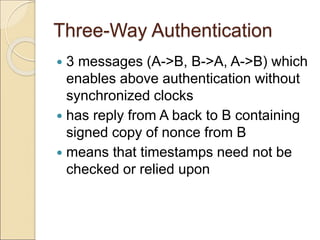
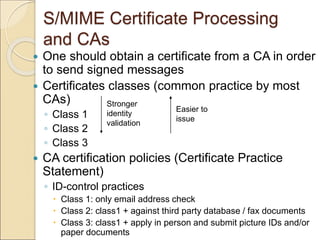
- X.509 defines a framework for authentication using public key certificates signed by certification authorities (CAs) and stored in directories. It includes one-way, two-way, and three-way authentication protocols.
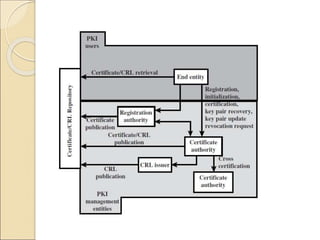
- PKI refers to the hardware, software, policies and procedures for managing digital certificates based on public key cryptography.
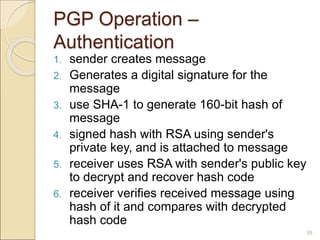
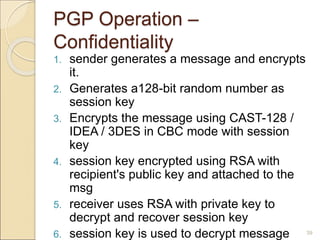
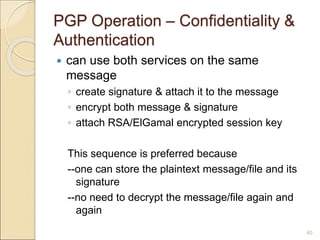
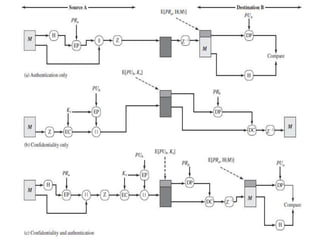
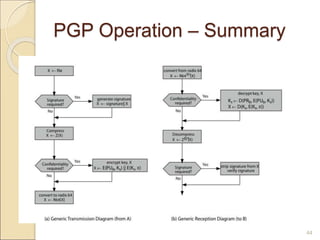
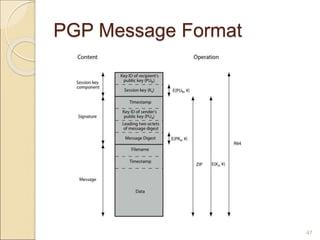
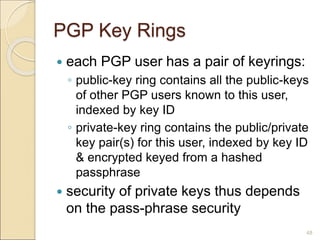
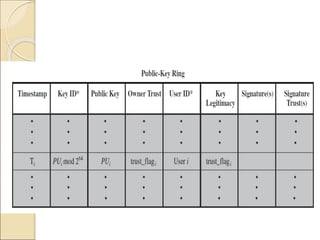
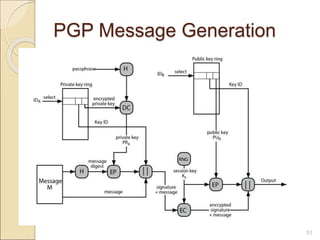
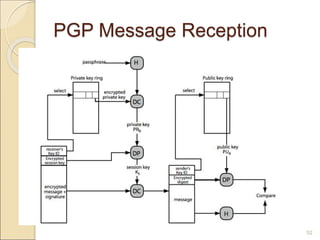
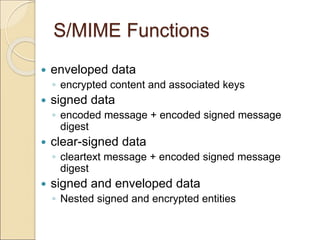
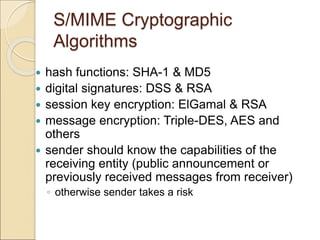
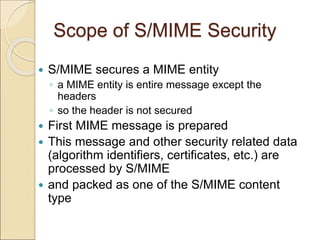
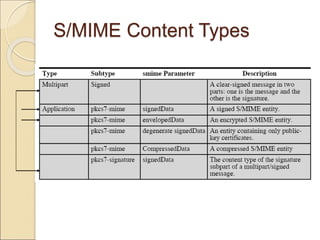
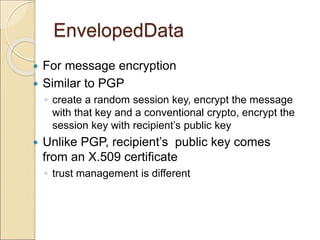
- PGP and S/MIME provide email security through encryption, signatures, and integrity checks using symmetric and asymmetric cryptography. While