The document discusses the key differences between the file-based data model and the relational data model (RDBMS). The file-based model stores data as files without relationships between data elements, while the RDBMS stores tabular data that is related and can be accessed simultaneously. The RDBMS supports features like normalization, distributed databases, and multiple users. It also discusses some basic concepts of RDBMS like tables, fields, tuples, keys, and normalization.
![a. CREATE It is used to create a new table in the database.
CREATE TABLE TABLE_NAME (COLUMN_NAME DATATYPES[,....]);
Ex:-CREATE TABLE EMPLOYEE(Name VARCHAR2(20), Email VARCHAR2(100),
DOB DATE);
b.ALTER: It is used to alter the structure of the database. This change could be either to modify
the characteristics of an existing attribute or probably to add a new attribute.
To add a new column in the table
ALTER TABLE table_name ADD column_name COLUMN-definition;
To modify existing column in the table:
ALTER TABLE table_name MODIFY(column_definitions....);
1. ALTER TABLE STU_DETAILS ADD(ADDRESS VARCHAR2(20));
2. ALTER TABLE STU_DETAILS MODIFY (NAME VARCHAR2(20));](https://image.slidesharecdn.com/unit2dbms-230206015153-21a52eaa/85/Unit-2-DBMS-pptx-48-320.jpg)
![a. INSERT: The INSERT statement is a SQL query. It is used to insert data into the row of a
table.
Syntax:-INSERT INTO TABLE_NAME VALUES (value1, value2, value3, .... valueN);
INSERT INTO javatpoint (Author, Subject) VALUES ("Sonoo", "DBMS");
INSERT INTO javatpoint values (“Sonoo”,”DBMS”);
b. UPDATE: This command is used to update or modify the value of a column in the table.
UPDATE table_name SET column_name=new_value WHERE column_name=some_value;
Syntax:- UPDATE students SET User_Name = 'Sonoo' WHERE Student_Id = '3'
c. DELETE: It is used to remove one or more row from a table.
DELETE FROM table_name [WHERE condition];
DELETE FROM javatpoint WHERE Author="Sonoo";](https://image.slidesharecdn.com/unit2dbms-230206015153-21a52eaa/85/Unit-2-DBMS-pptx-57-320.jpg)
![3. Data Control Language
DCL commands are used to grant and take back authority from any database user. DCL commands
are related to the security of the database.
Here are some commands that come under DCL:
● Grant
● Revoke
a. Grant:The objects created by one user are not accessible by another user unless the owner of
those object gives such permission to the other user.It is used to give user access privileges to a
database. List of object are ALTER, DELETE, INSERT, SELECT,UPDATE with GRANT
OPTION
Syntax: Grant {object privileges} ON object name TO user name [with GRANT OPTION]
Syntax:-GRANT SELECT, UPDATE ON MY_TABLE TO SOME_USER;
GRANT ALL ON student TO Sachin;](https://image.slidesharecdn.com/unit2dbms-230206015153-21a52eaa/85/Unit-2-DBMS-pptx-58-320.jpg)
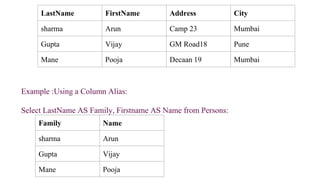
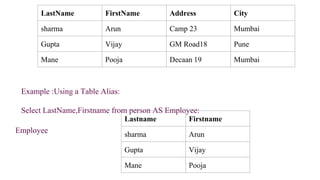
![SQL Aliases
SQL aliases are used to give a table, or a column in a table, a temporary name.
Aliases are often used to make column names more readable.
An alias only exists for the duration of that query.
An alias is created with the AS keyword.
Syntax
The basic syntax of a table alias is as follows.
SELECT column1, column2....FROM table_name AS alias_name WHERE [condition];
The basic syntax of a column alias is as follows.
SELECT column_name AS alias_name FROM table_name WHERE [condition];](https://image.slidesharecdn.com/unit2dbms-230206015153-21a52eaa/85/Unit-2-DBMS-pptx-81-320.jpg)