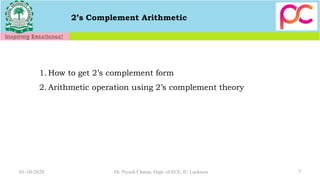
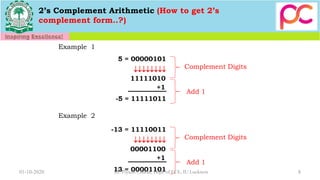
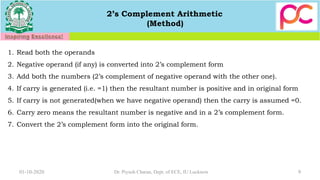
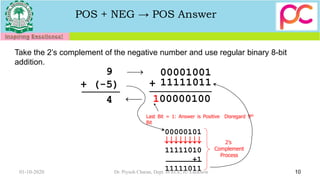
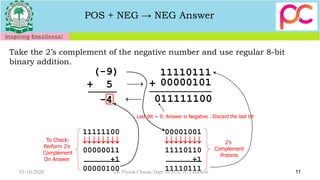
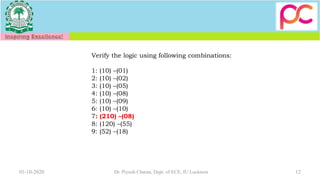
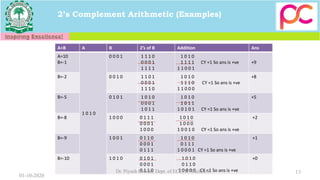
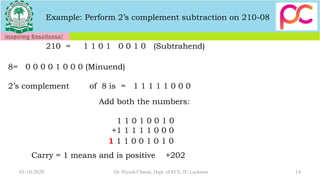
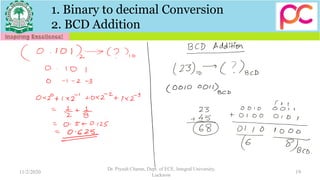
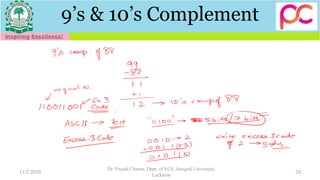
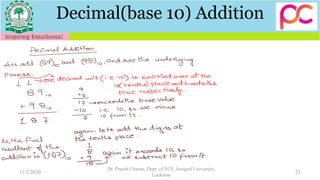
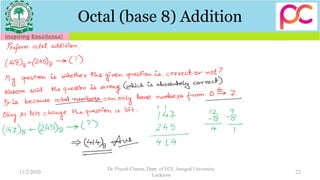
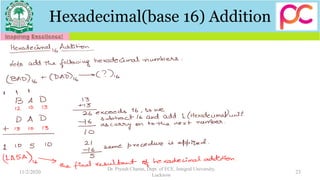
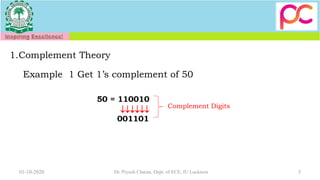
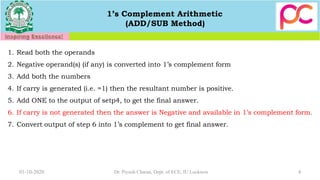
The document provides an educational resource on complement theory, including 1's and 2's complements, along with arithmetic operations such as addition and subtraction in various number systems (binary, decimal, octal, and hexadecimal). It contains examples demonstrating the operations of 1's and 2's complement arithmetic, as well as BCD addition. Additionally, the document outlines methods for converting between different number systems and performing arithmetic calculations using these complements.

![5
1. 1’s Complement Theory
Example 1 : Subtract 1010 from 1111 using 1’s complement theory. (15-10 Small negative)
1 0 1 0 0 1 0 1
1 1 1 1
0 1 0 1+
1] 0 1 0 0
+ 0 0 0 1
0 1 0 1 =(5)
1’s complement
Carry “1” means the answer is positive .
01-10-2020 Dr. Piyush Charan, Dept. of ECE, IU Lucknow](https://image.slidesharecdn.com/unit2datarepcontd-201105140621/85/Unit-2-Data-Representation-contd-5-320.jpg)
![6
1. 1’s Complement Theory
Example 2 : Subtract 1010 from 1000 using 1’s complement theory. (Large negative 8-10)
1 0 1 0 0 1 0 1
1 0 0 0
0 1 0 1+
0] 1 1 0 1
1’s complement
Carry “0” means the answer is negative and available in 1’s complement form.
1 1 0 1 0 0 1 0 = (2)
01-10-2020 Dr. Piyush Charan, Dept. of ECE, IU Lucknow](https://image.slidesharecdn.com/unit2datarepcontd-201105140621/85/Unit-2-Data-Representation-contd-6-320.jpg)