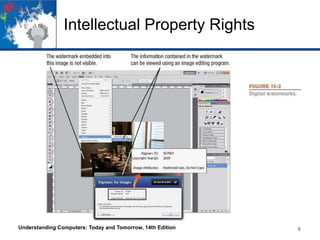
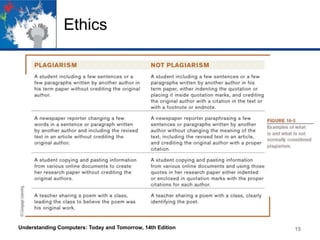
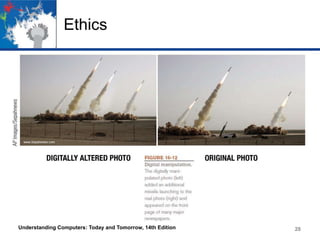
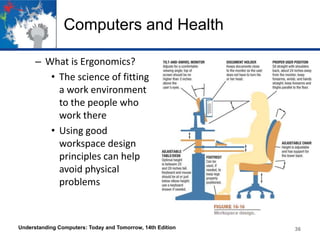
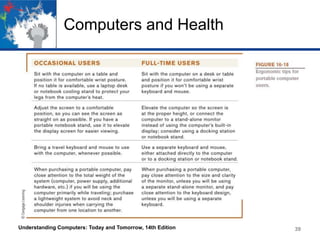
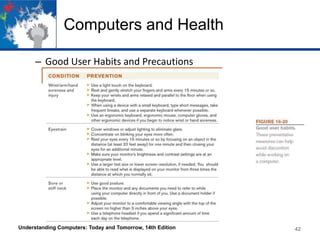
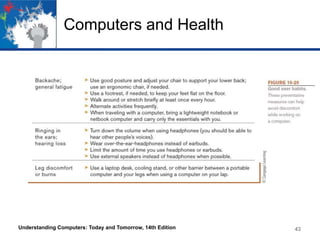
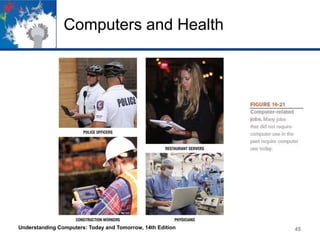
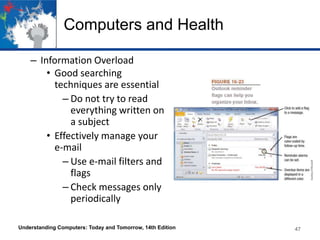
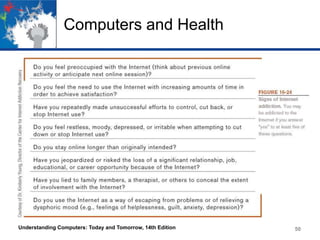
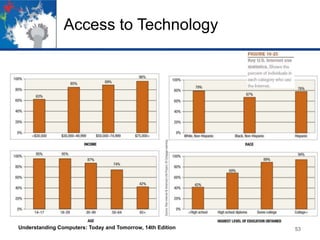
This chapter discusses intellectual property rights, ethics, health issues related to computer use, access to technology, and environmental impacts. It covers various types of intellectual property including copyrights, trademarks, patents, and digital rights management. Ethics topics include proper use of copyrighted material, information resources, and addressing issues like digital manipulation. Health sections explore physical risks from improper ergonomics as well as emotional stressors. Access barriers like the digital divide within and between countries are also examined.