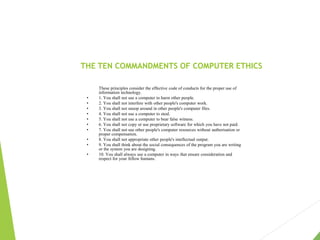
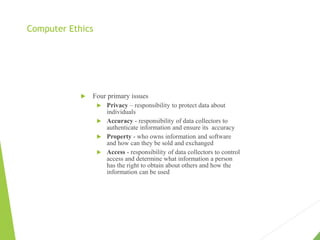
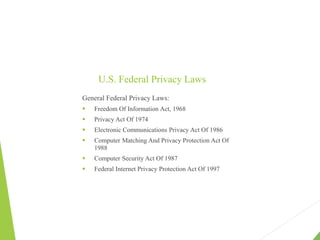
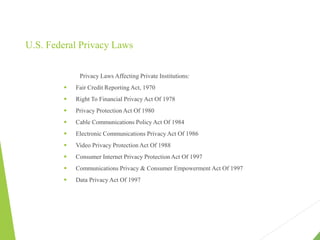
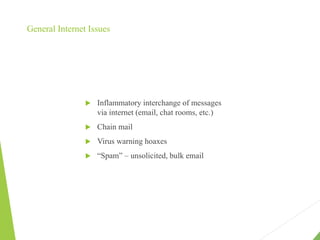
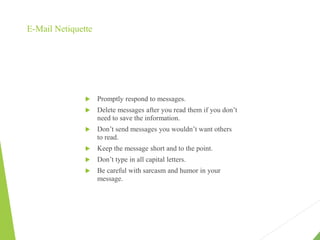
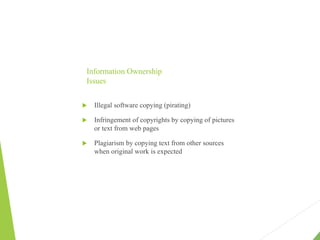
This document discusses several moral and legal issues related to computer ethics. It begins by noting that computers are involved in many aspects of modern life and often perform critical tasks, but the computer industry is not as highly regulated as other industries like medicine or transportation. It then outlines 10 principles or "commandments" of computer ethics related to issues like privacy, accuracy of information, intellectual property, and social impact of technology. The document also discusses concepts like ethics, ethical principles to consider when making decisions, and four primary issues in computer ethics around privacy, accuracy, property and access. It provides examples of problems that can arise with large databases and private networks, as well as laws related to privacy and intellectual property.