Embed presentation

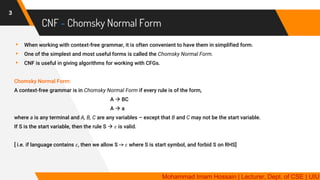
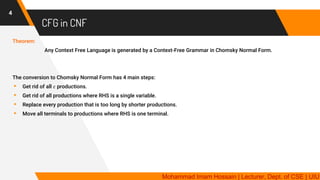
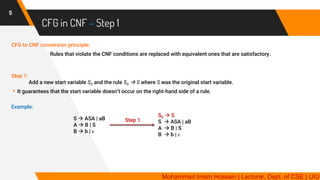
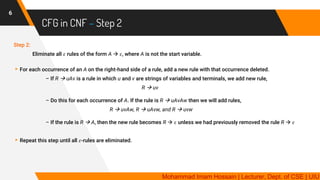
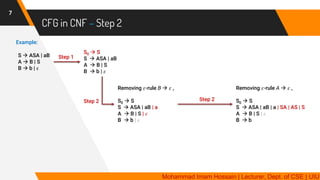
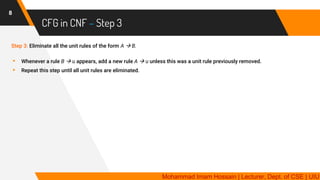
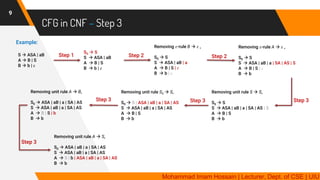
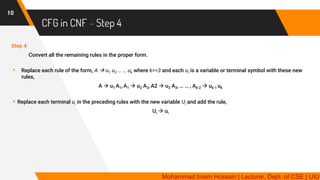
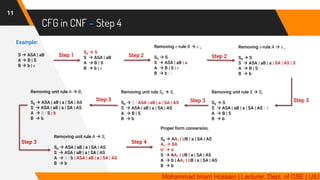
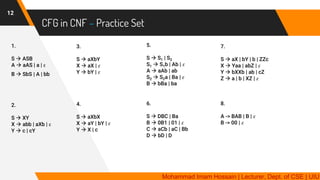

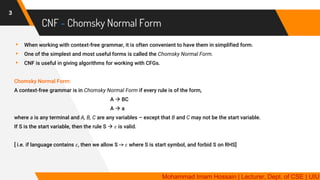
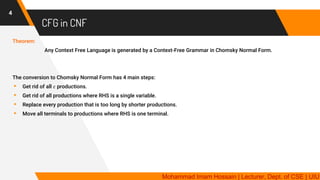
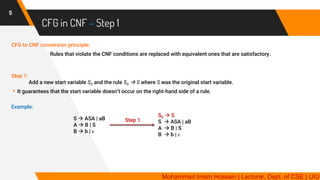
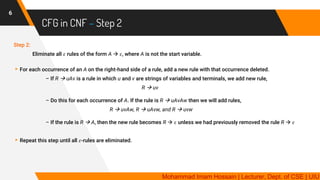
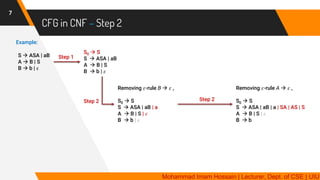
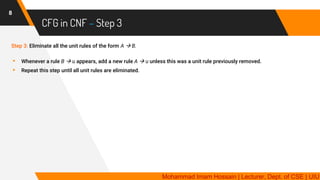
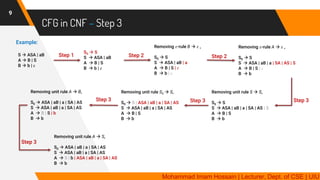
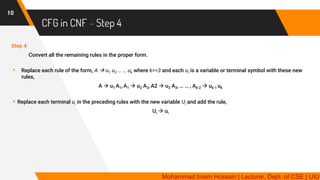
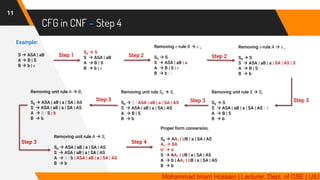
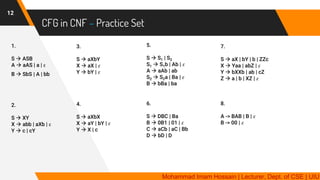
The document provides a detailed explanation of context-free grammar (CFG), including its structure and the Chomsky Normal Form (CNF). It outlines the steps necessary for converting CFG to CNF, which involves eliminating ε-productions, unit productions, and adjusting rules to fit the CNF requirements. Additionally, the document includes practical examples and references for further study.