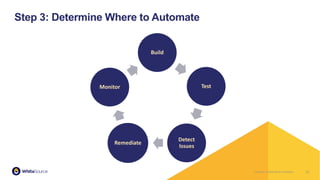
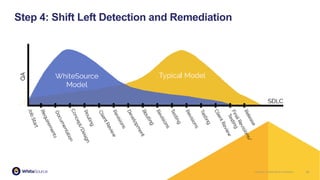
The document discusses the concept of DevSecOps, which integrates security practices within DevOps processes to enhance code delivery while ensuring security. It outlines the benefits, such as cost reduction and operational efficiency, alongside the challenges faced in scaling DevSecOps including cultural issues and automation hurdles. The document concludes with a five-step approach to implement and drive DevSecOps within organizations.