This document discusses open source security risks and provides recommendations. It contains 5 sections:
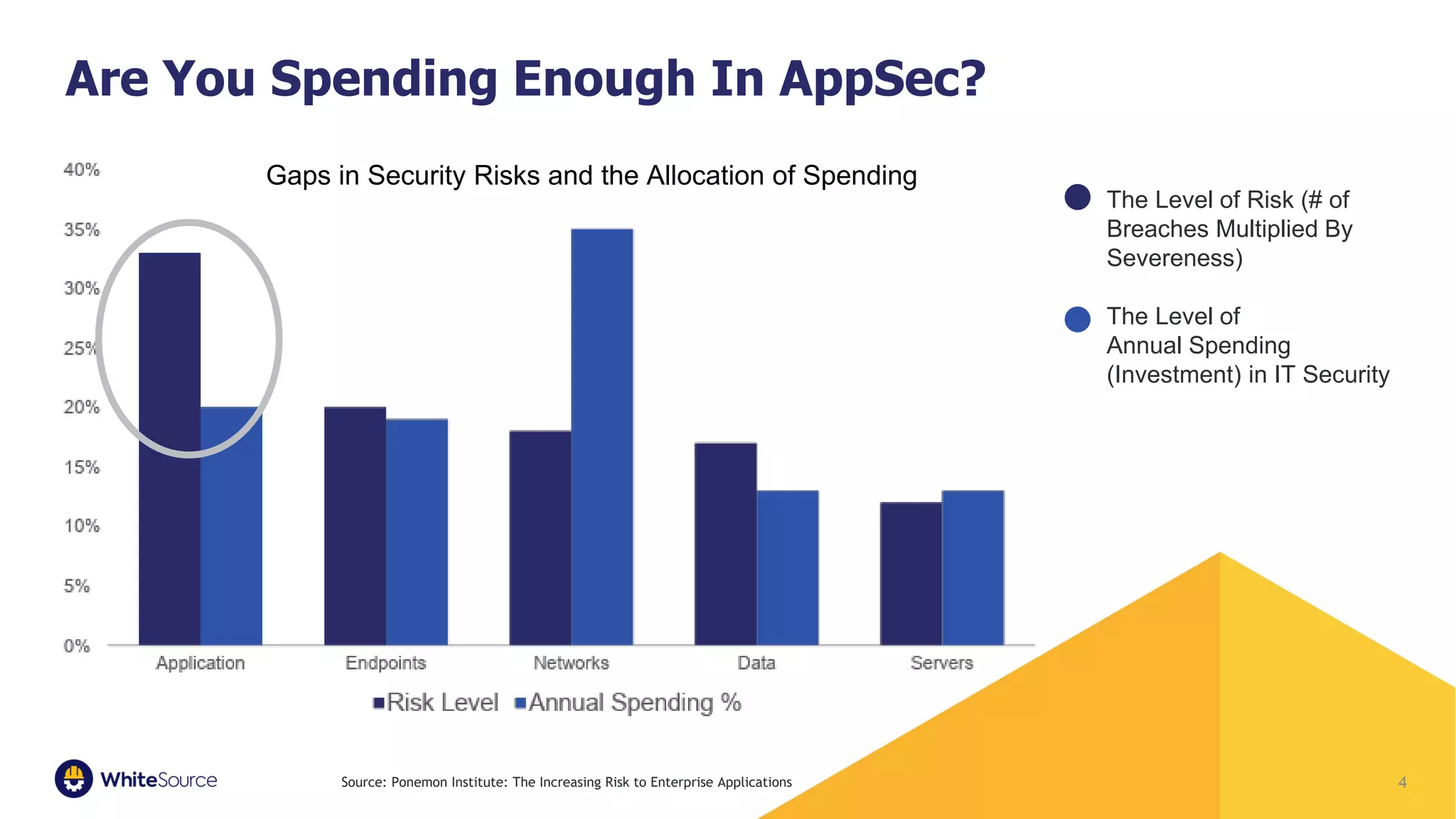
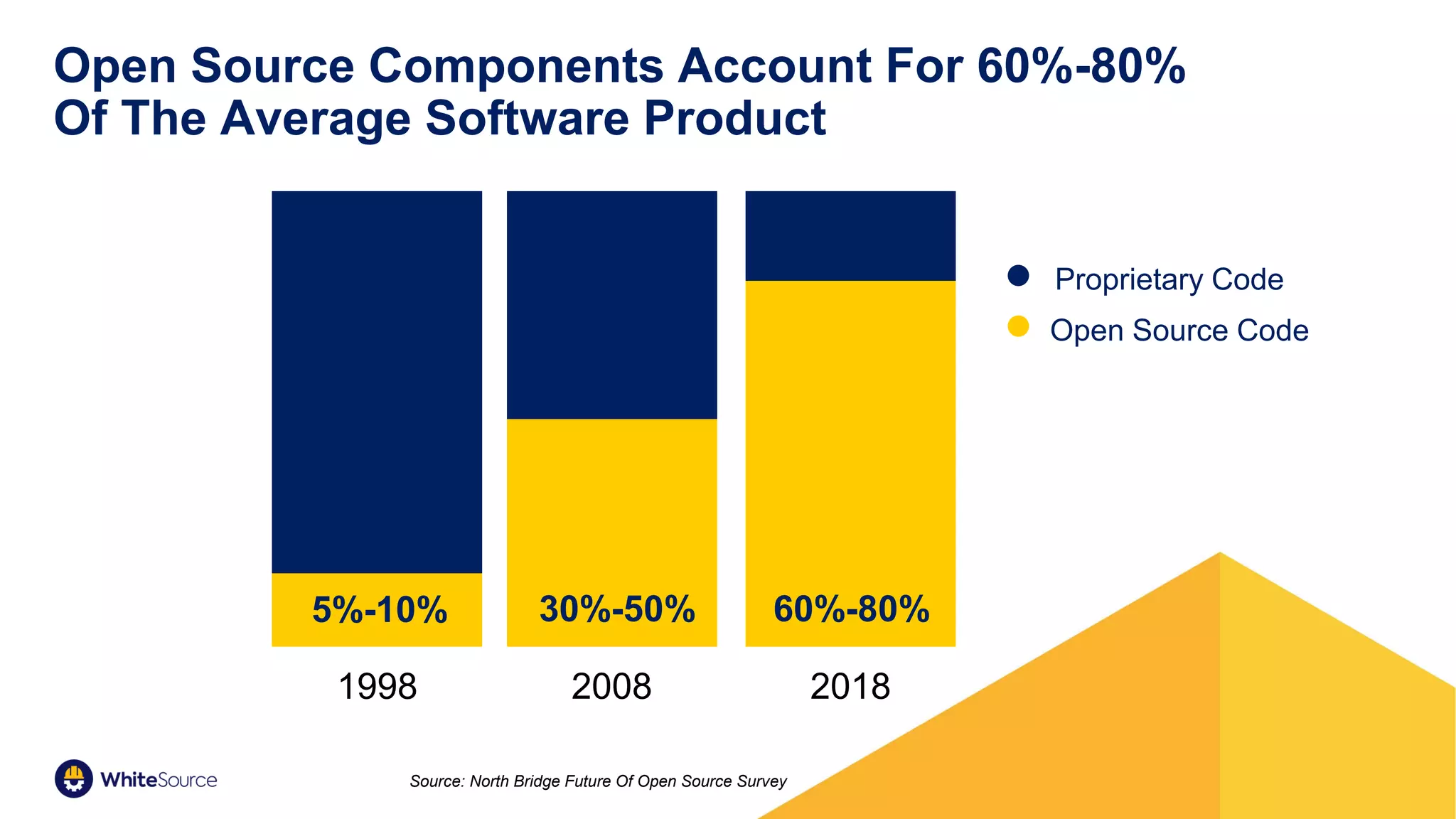
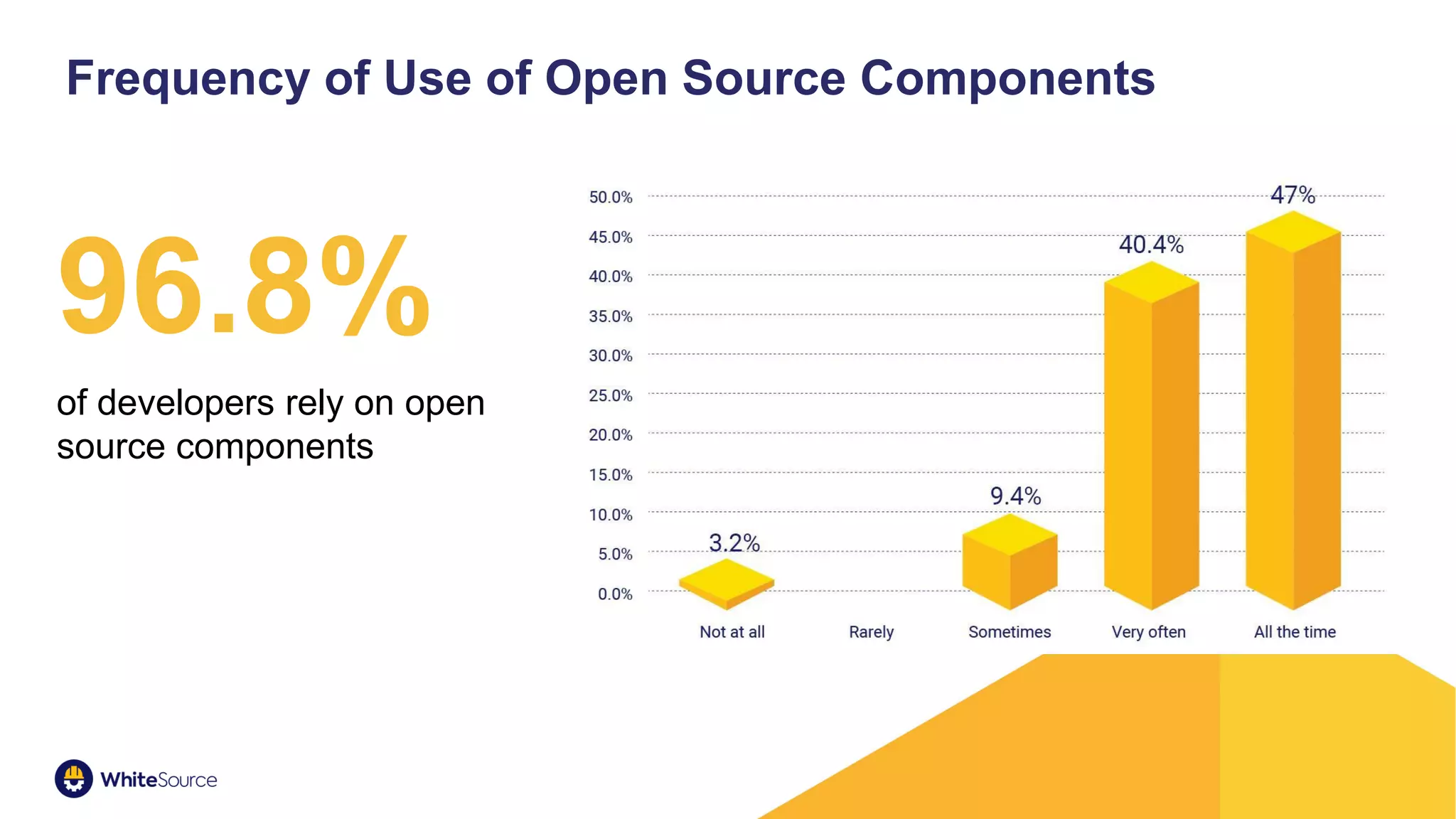
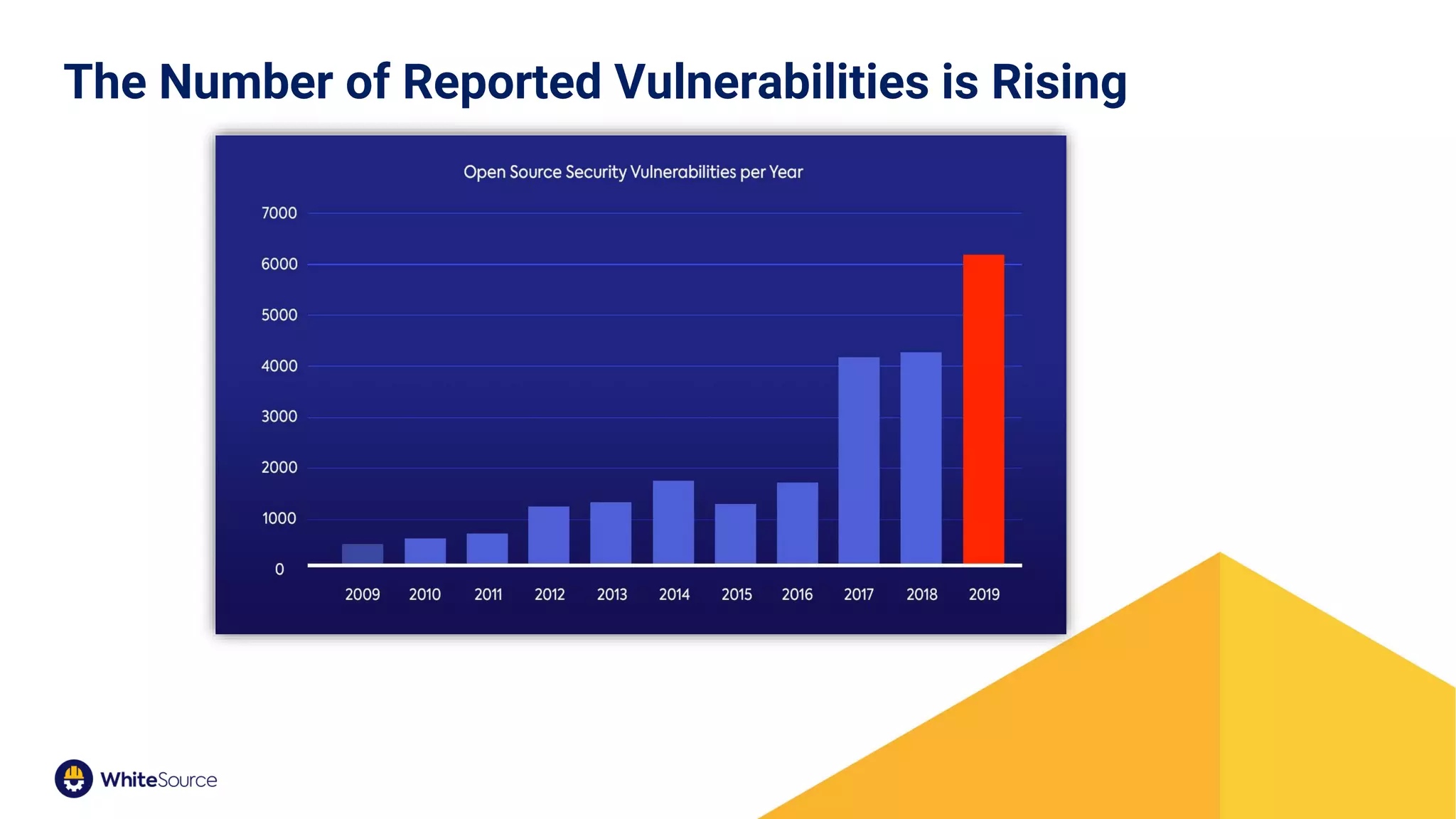
1. Open source risk is on the rise as open source code accounts for 60-80% of software and reported vulnerabilities are increasing.
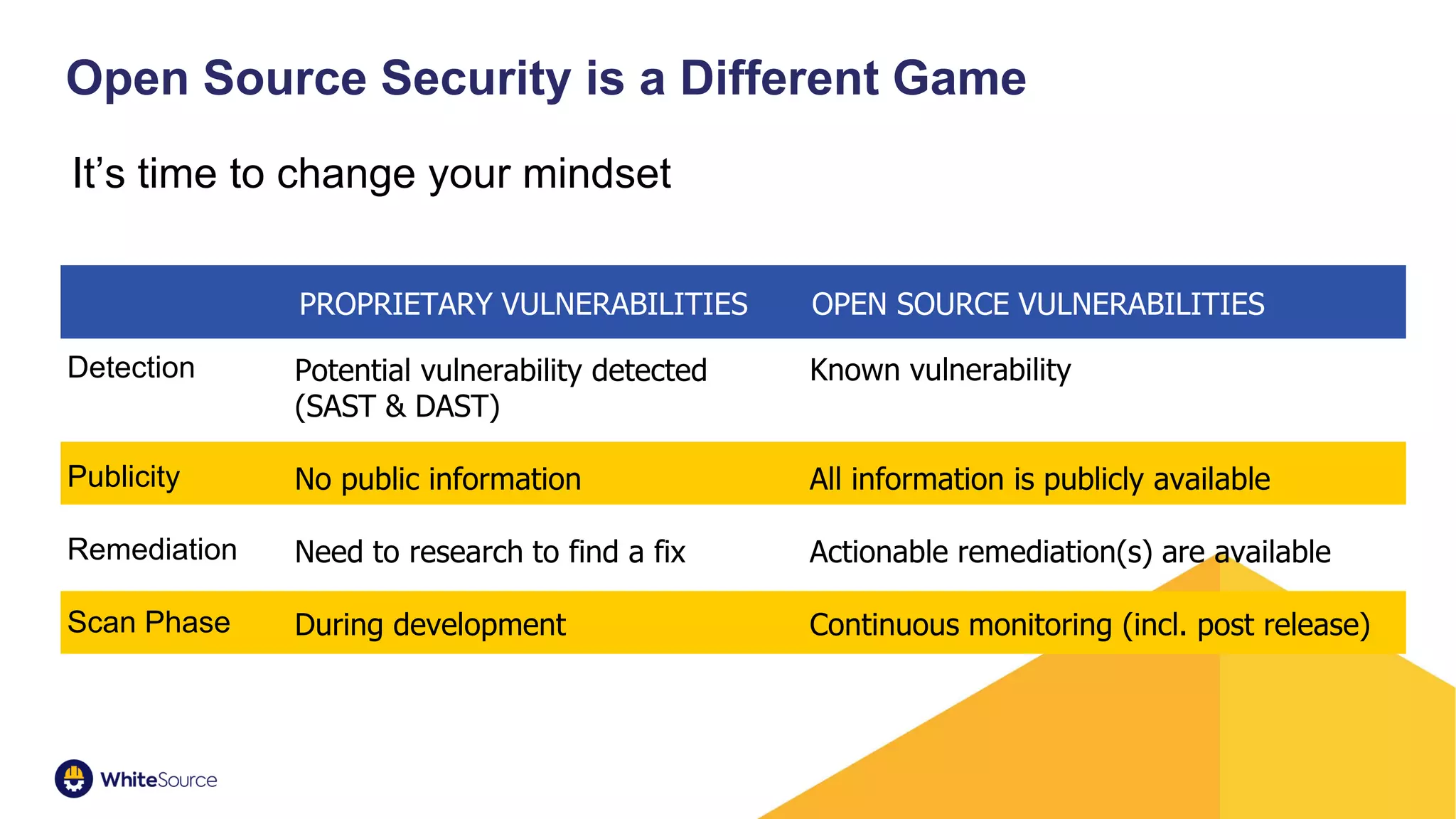
2. Developers must change their mindset as open source vulnerabilities differ from proprietary vulnerabilities in detection, publicity and remediation.
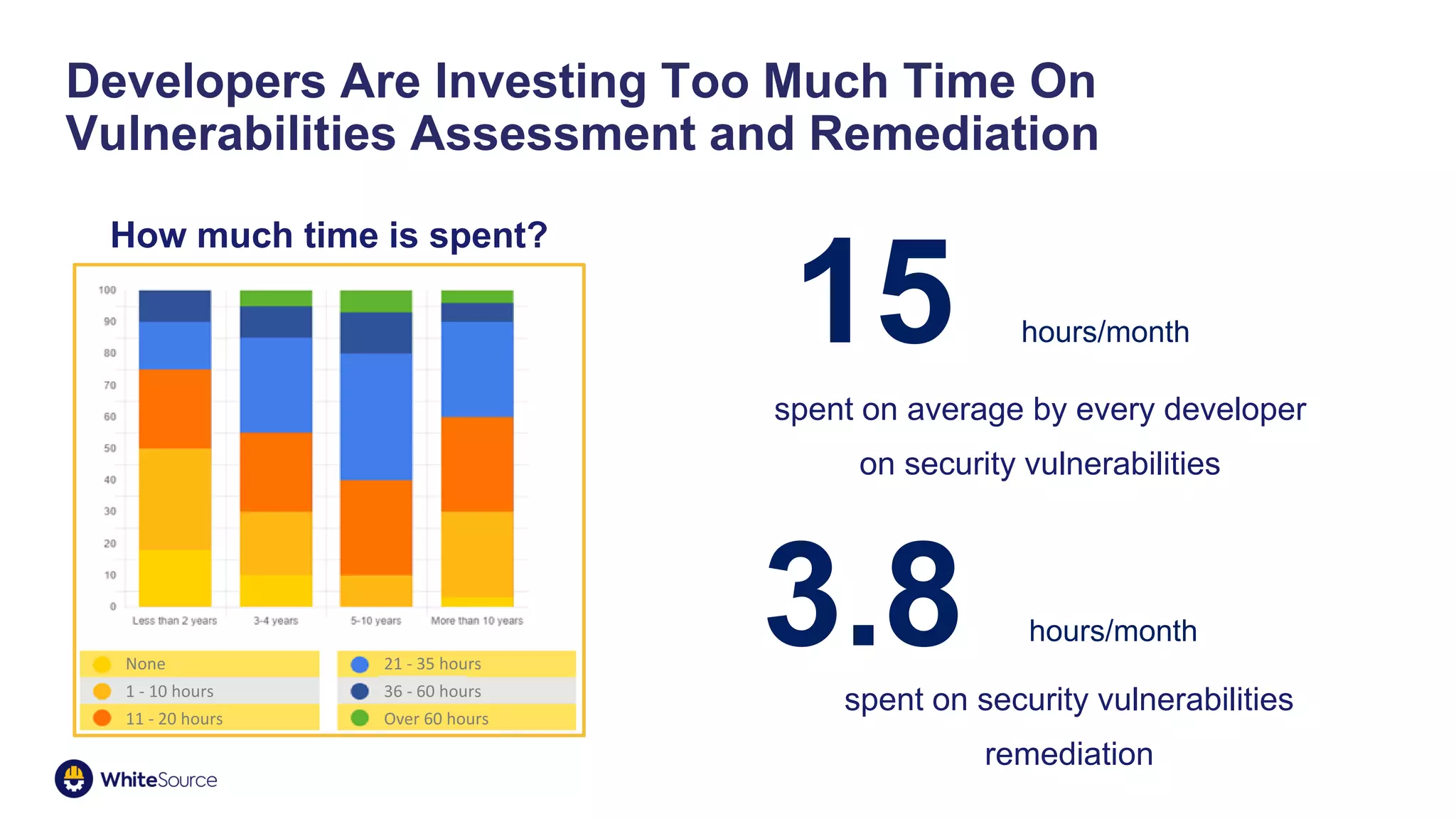
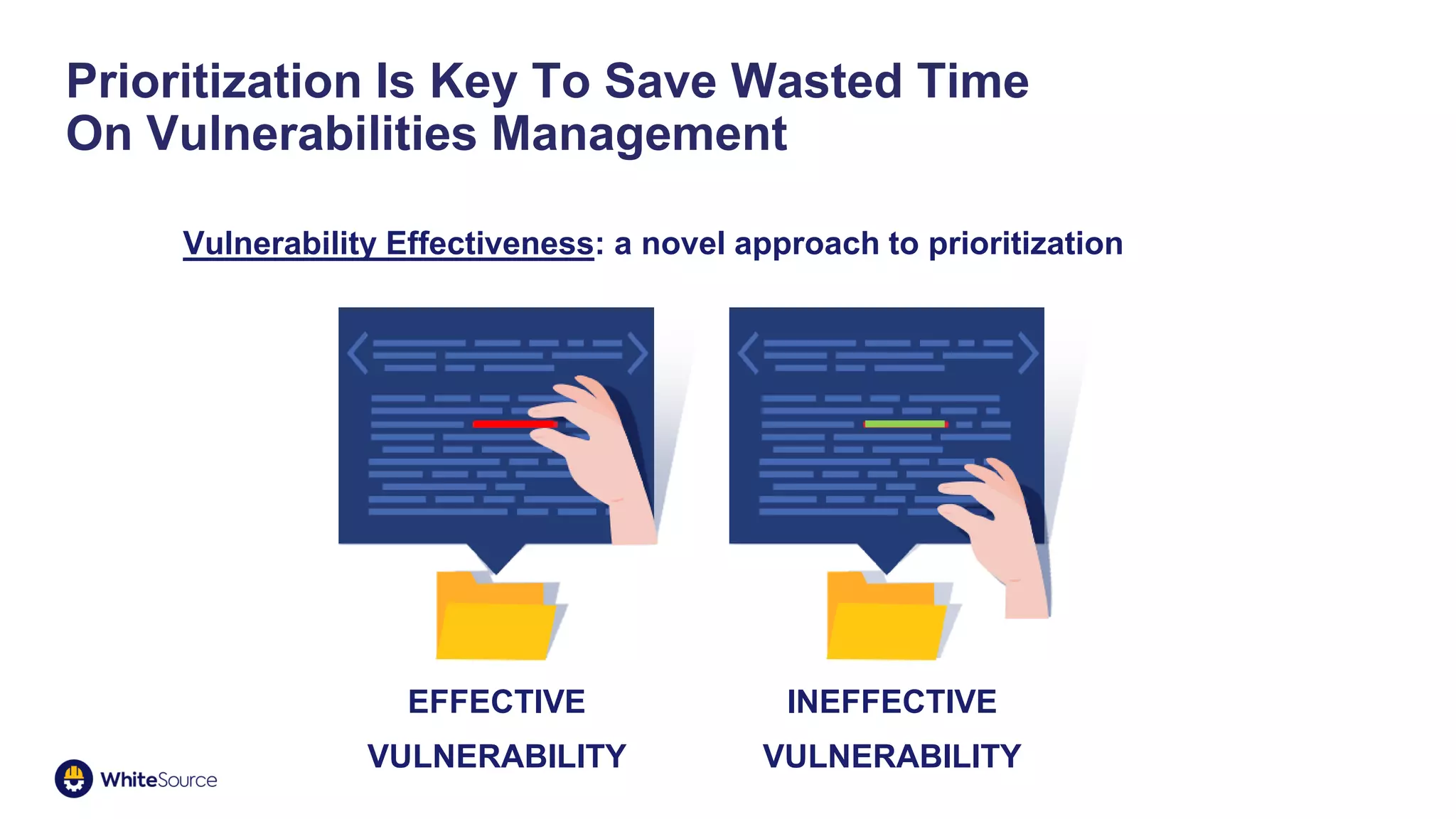
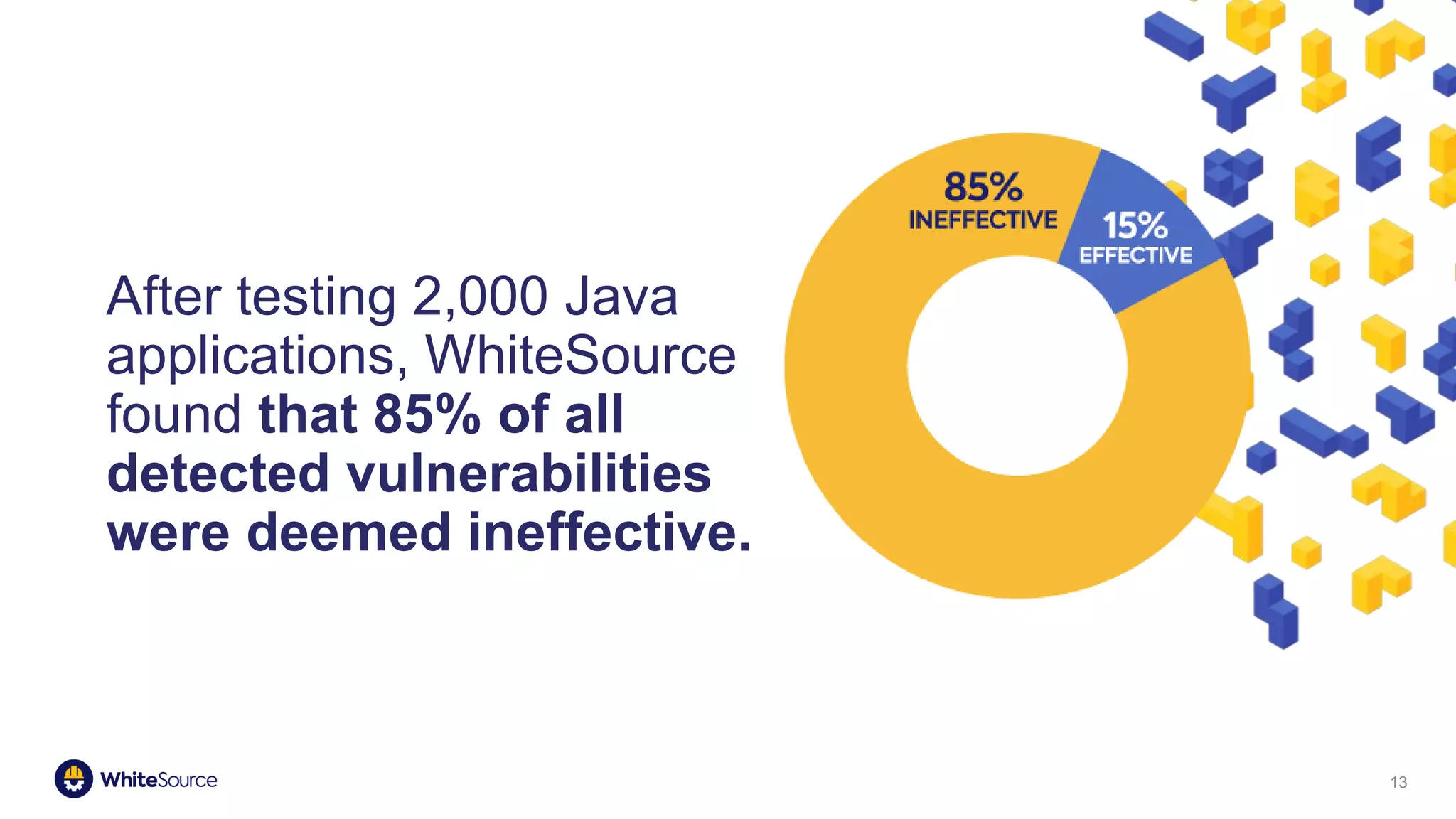
3. Prioritizing security vulnerabilities is key as developers spend too much time on ineffective vulnerabilities.
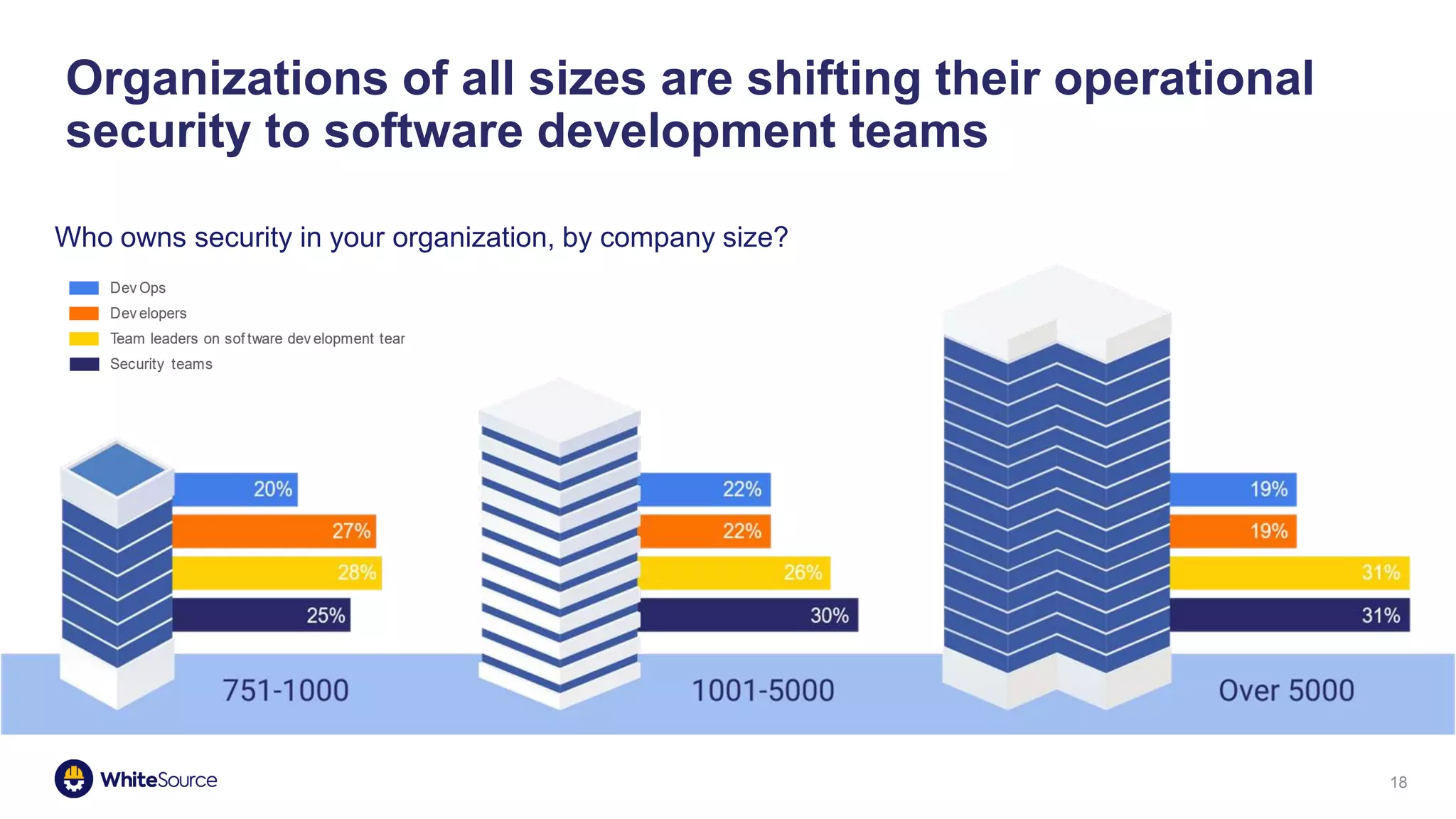
4. Security responsibilities must be delegated between security, DevOps and developers to bridge gaps.
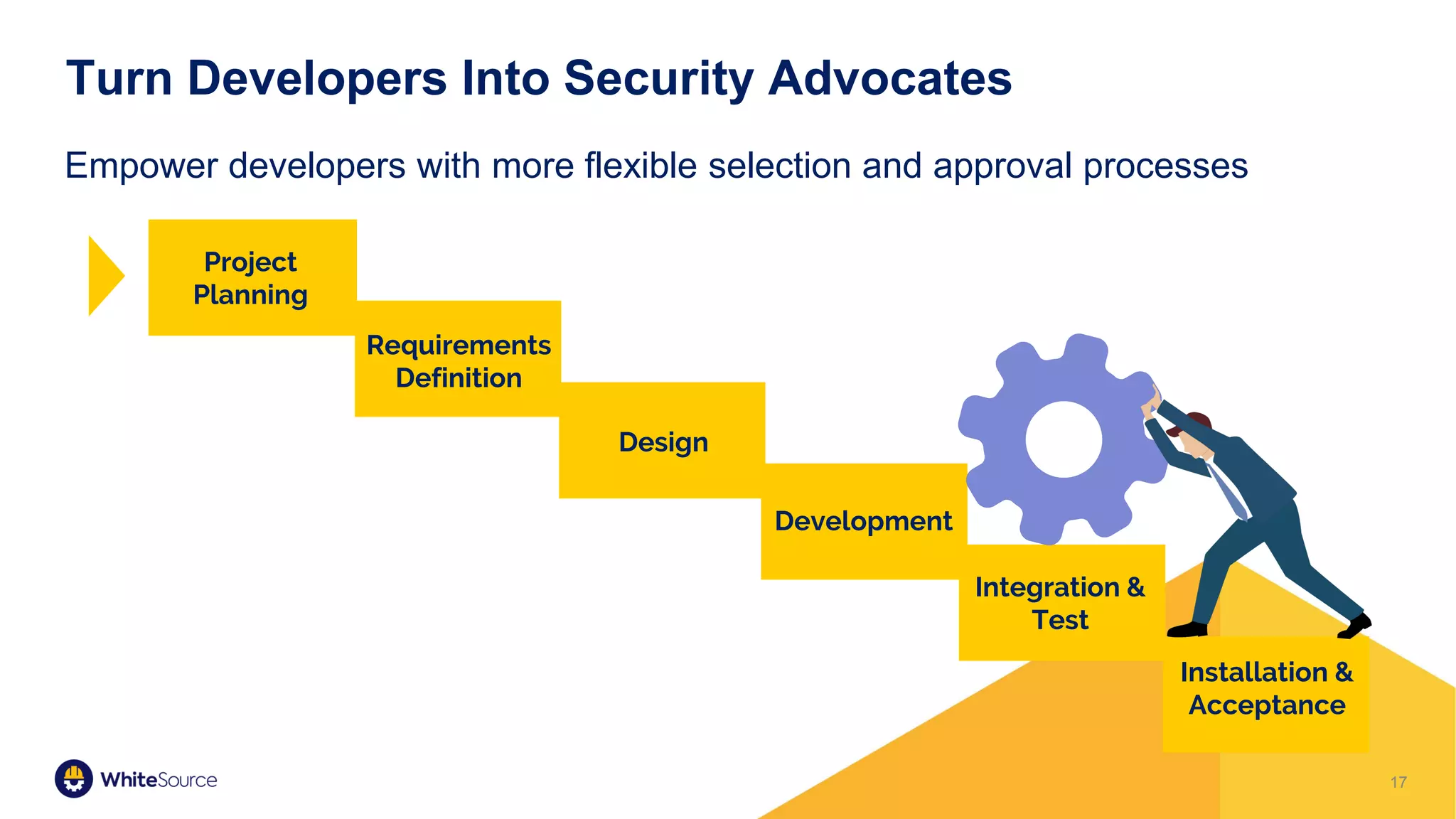
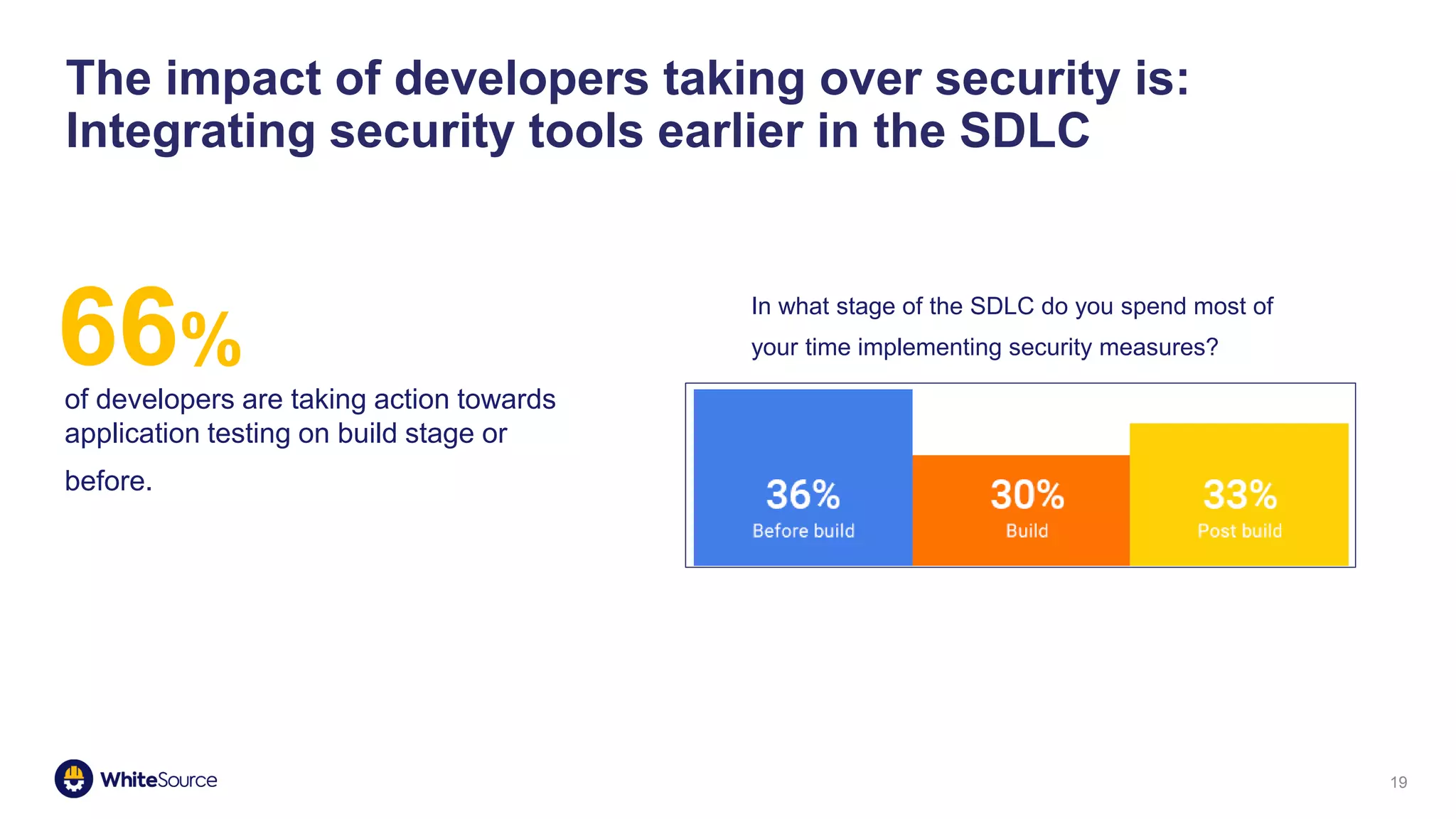
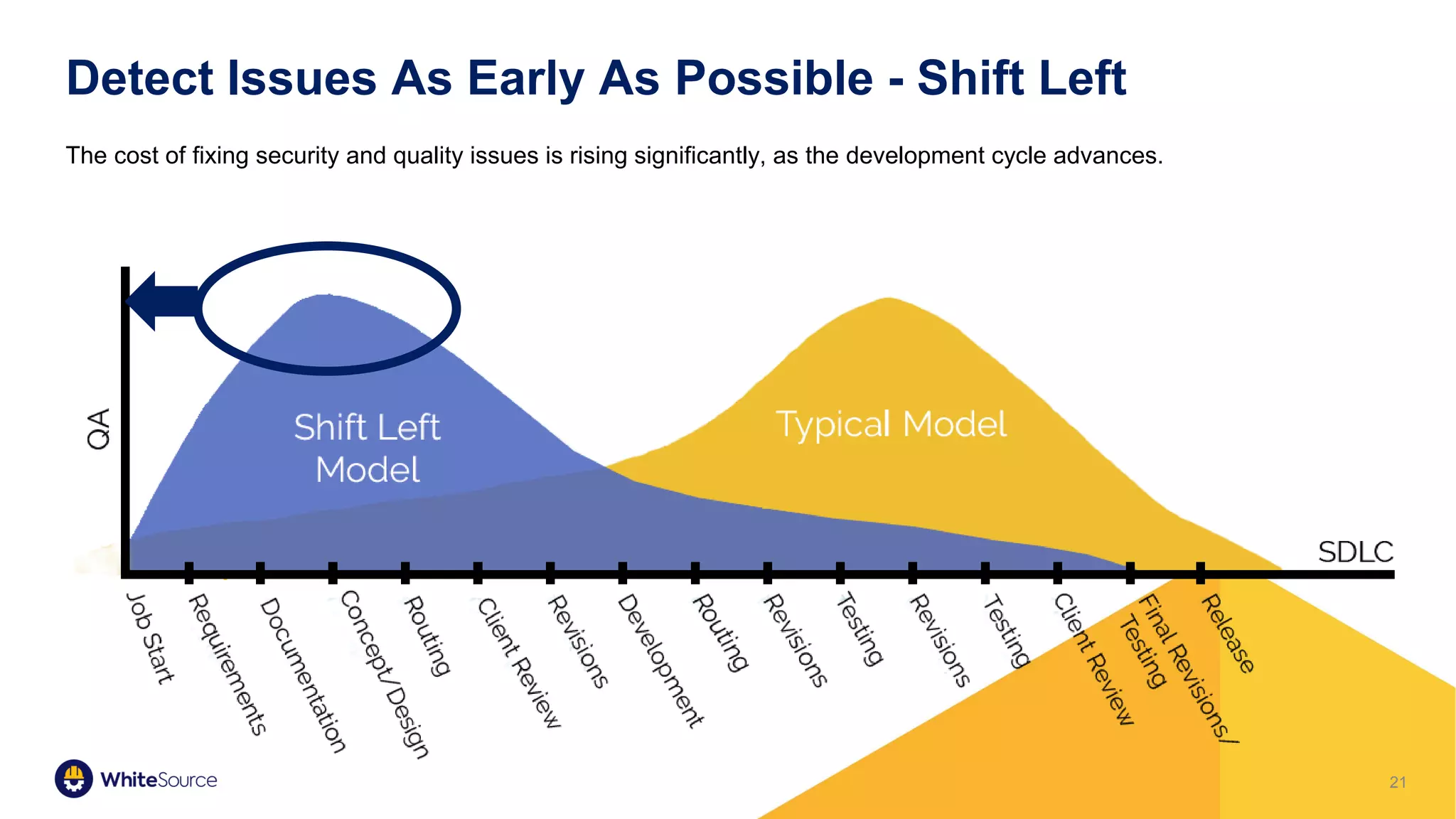
5. Shifting security left by empowering developers and integrating tools earlier can turn developers into advocates and detect issues cheaper.