Embed presentation
Download to read offline
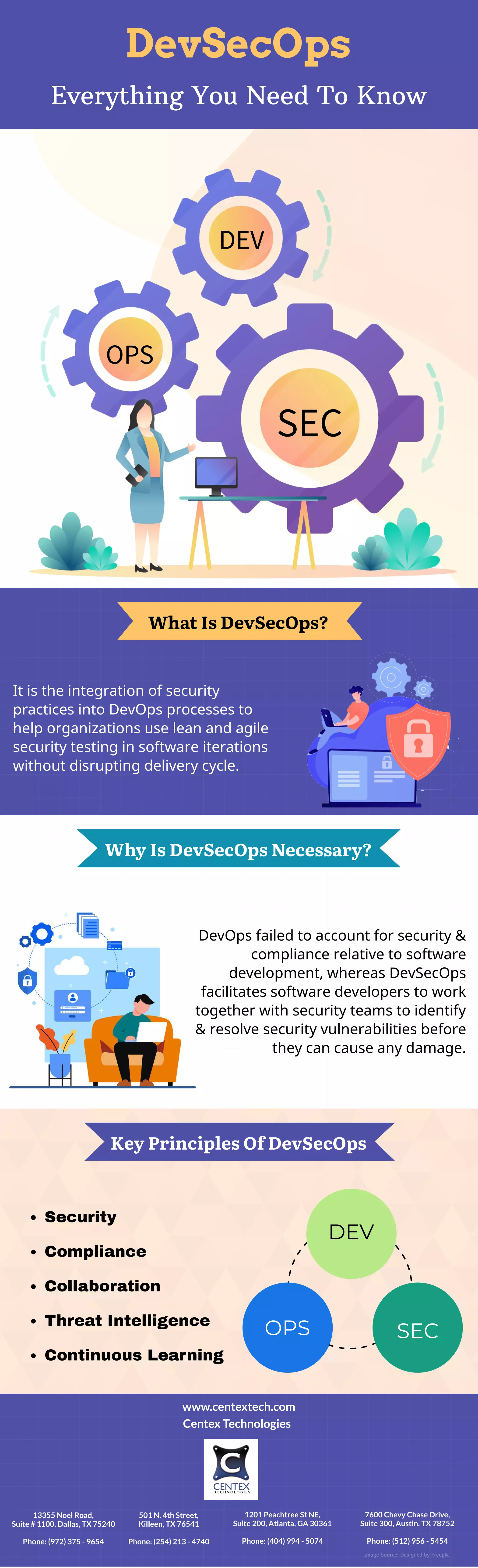
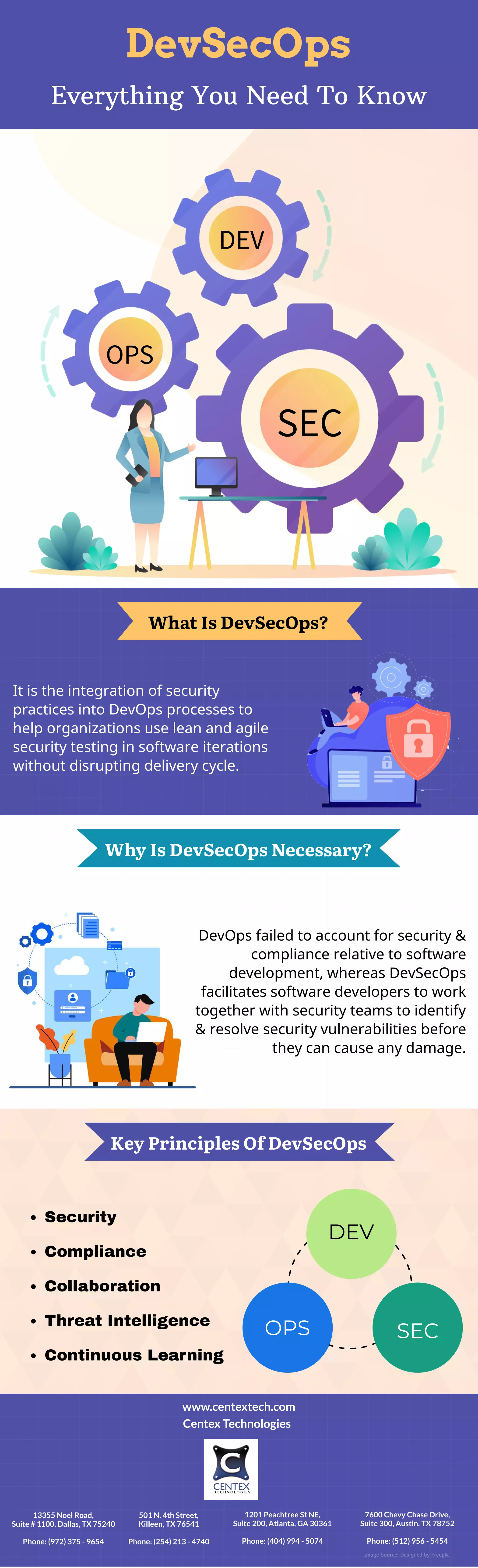
DevSecOps integrates security practices into DevOps processes to allow for lean and agile security testing throughout software development without disrupting delivery cycles. It is necessary because DevOps failed to properly account for security and compliance issues, whereas DevSecOps facilitates collaboration between developers and security teams to identify and resolve vulnerabilities early. Key principles of DevSecOps include security, compliance, collaboration, threat intelligence, and continuous learning.