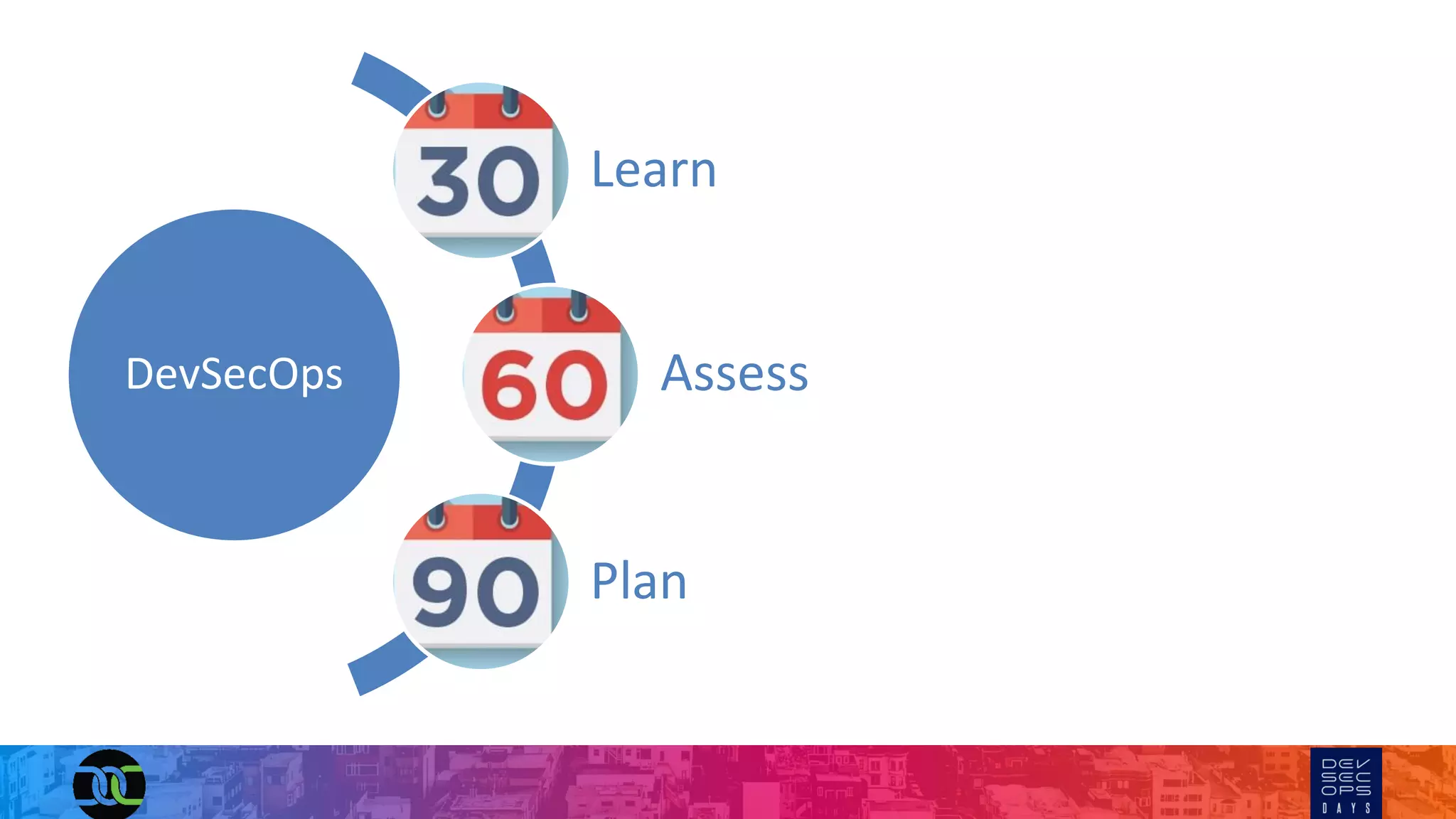
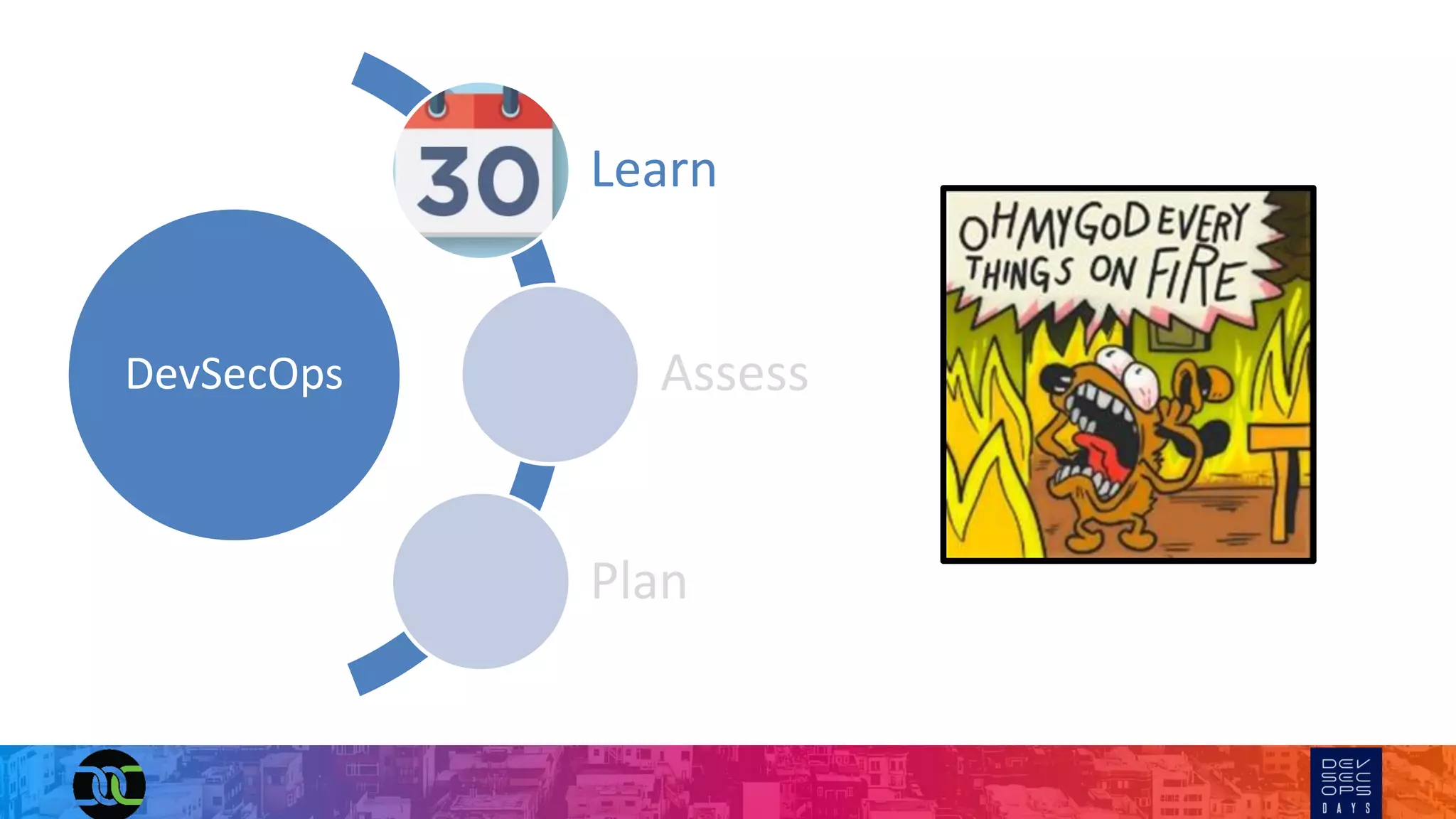
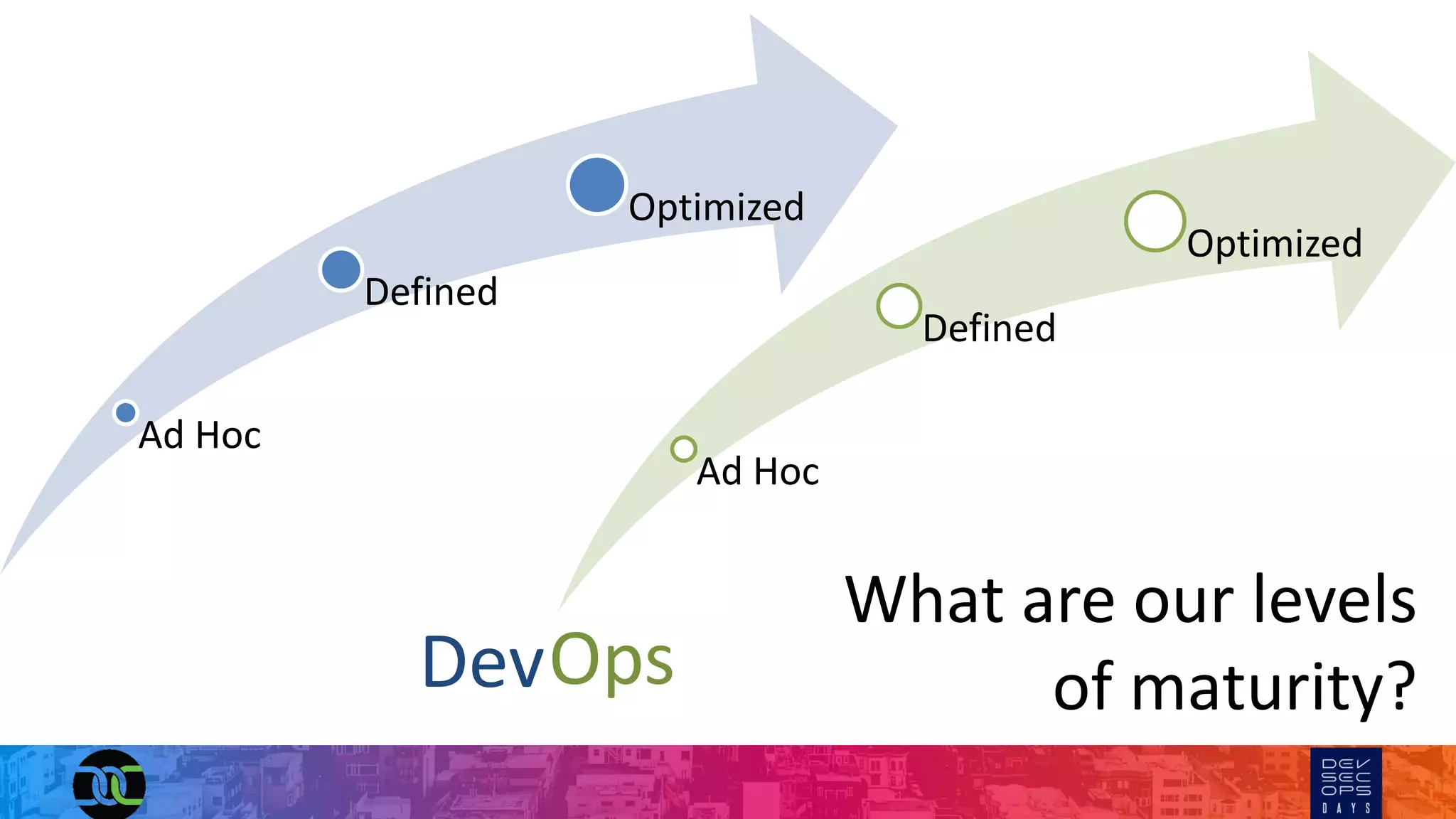
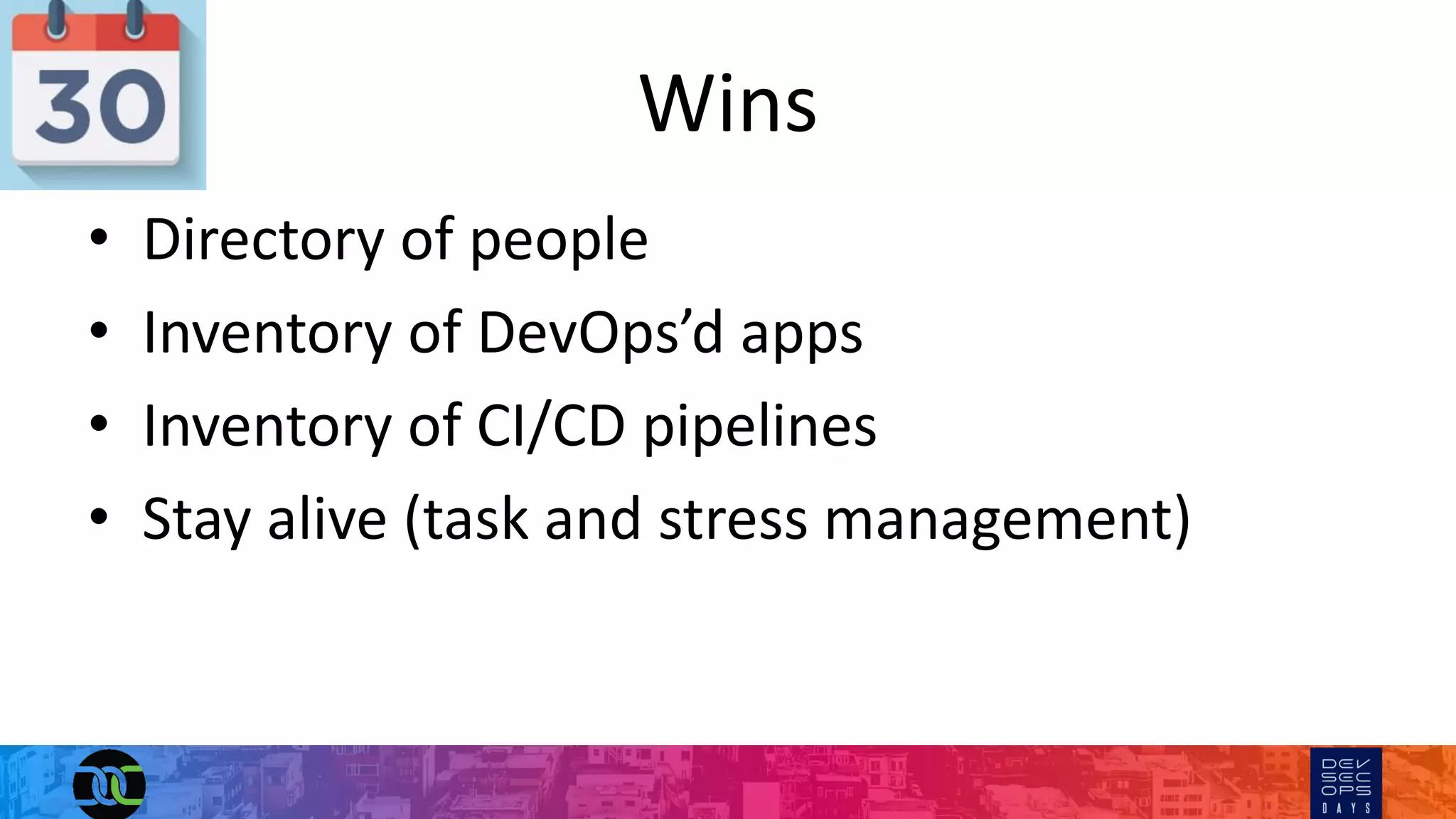
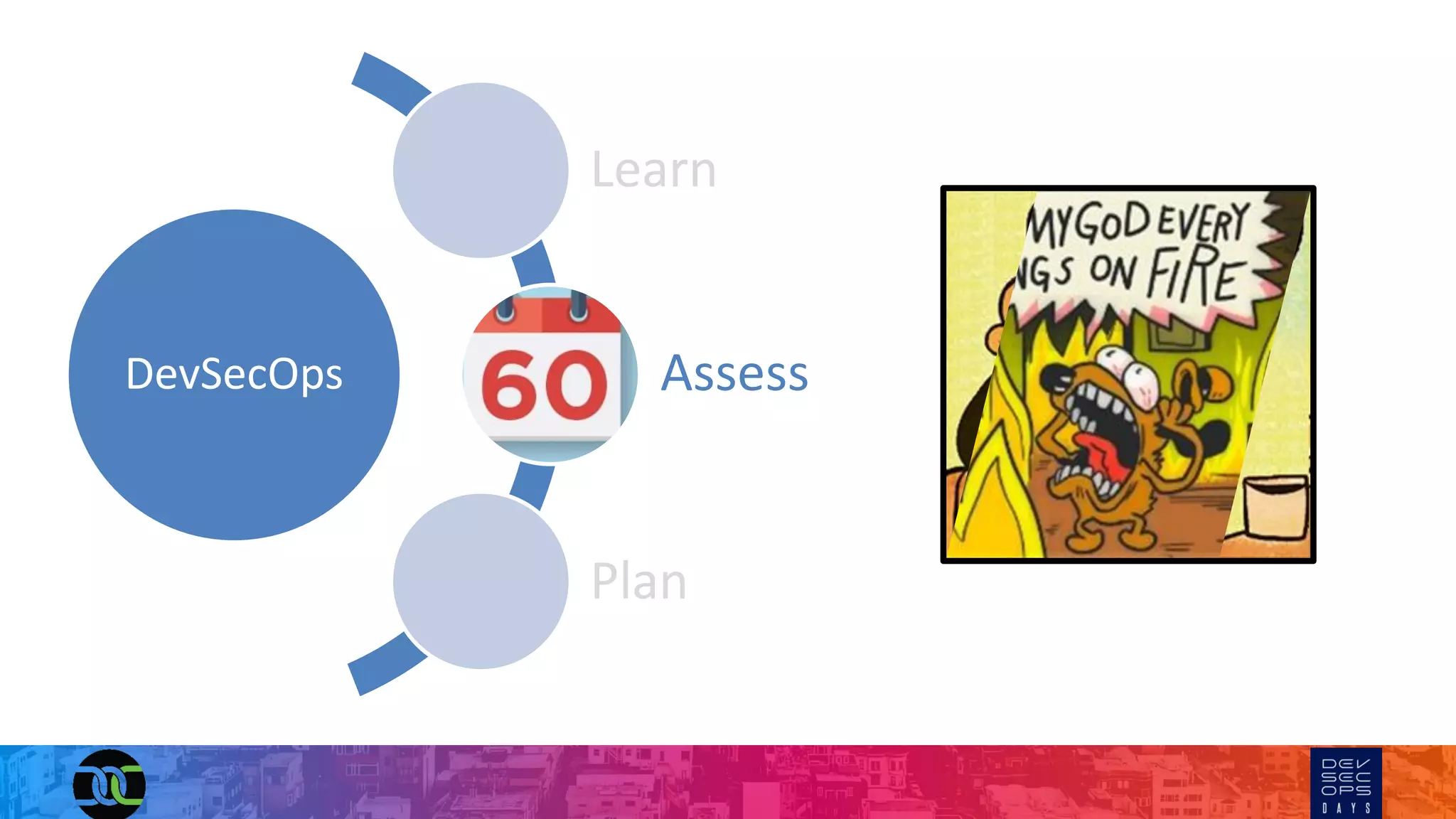
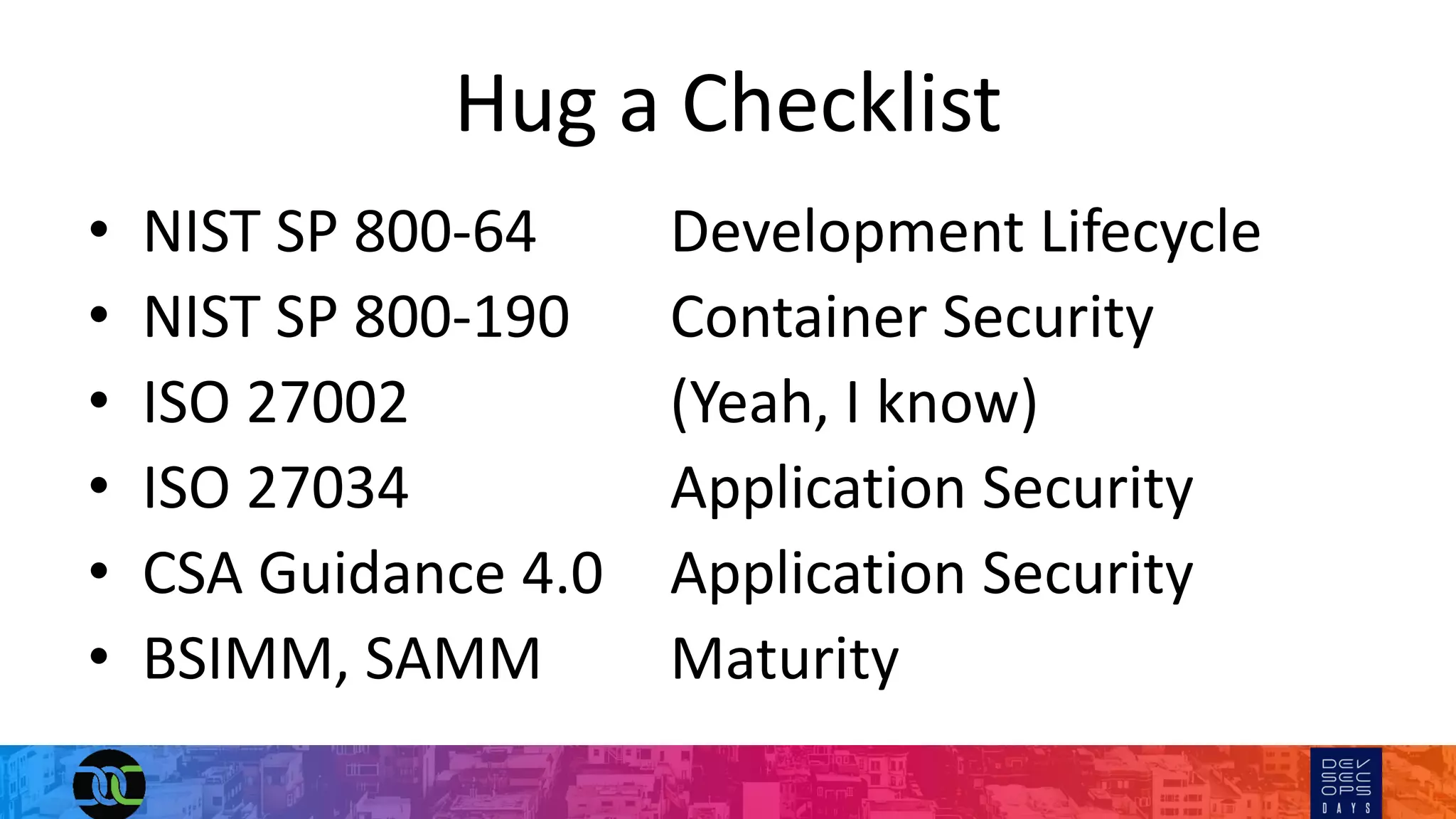
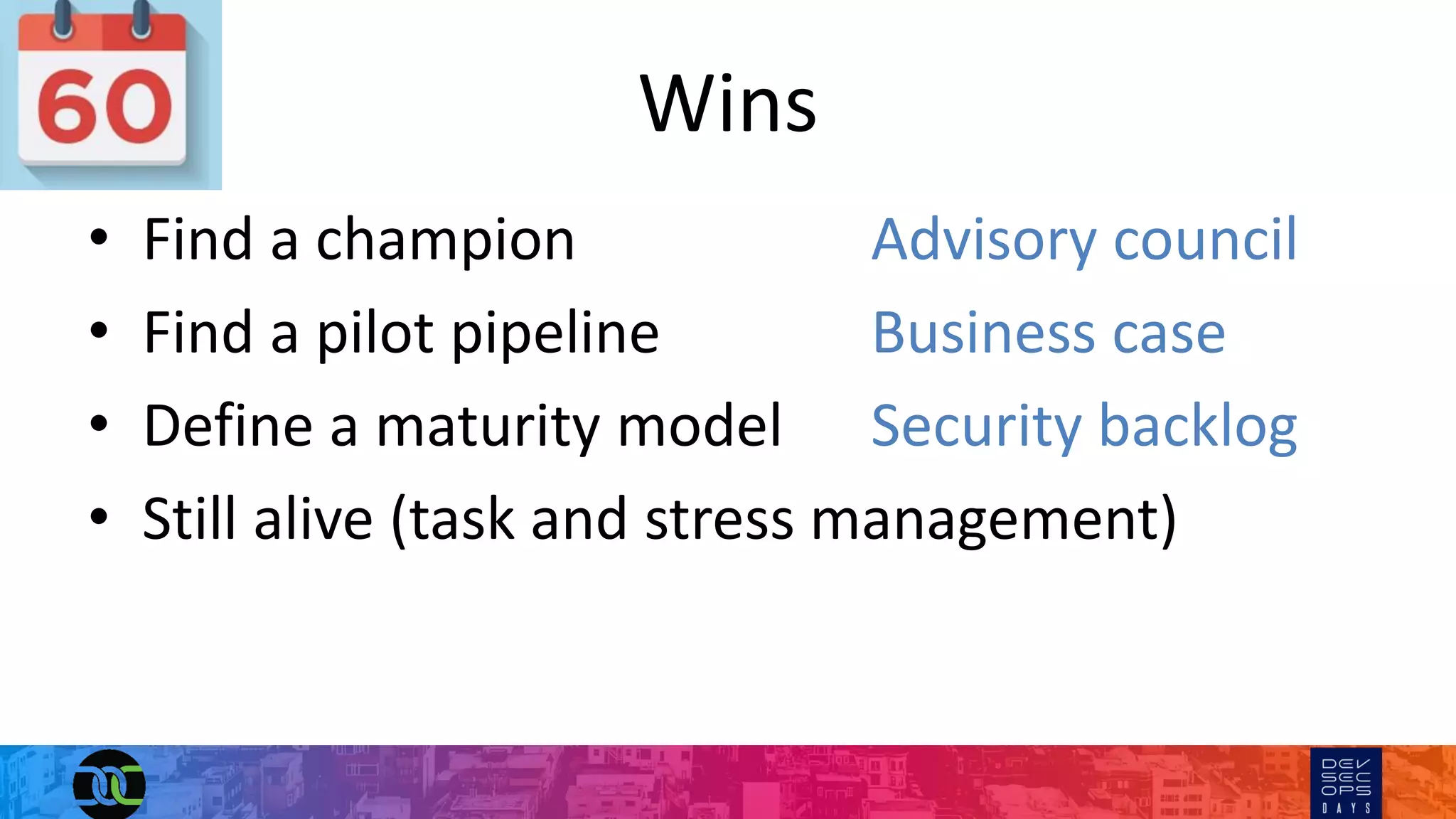
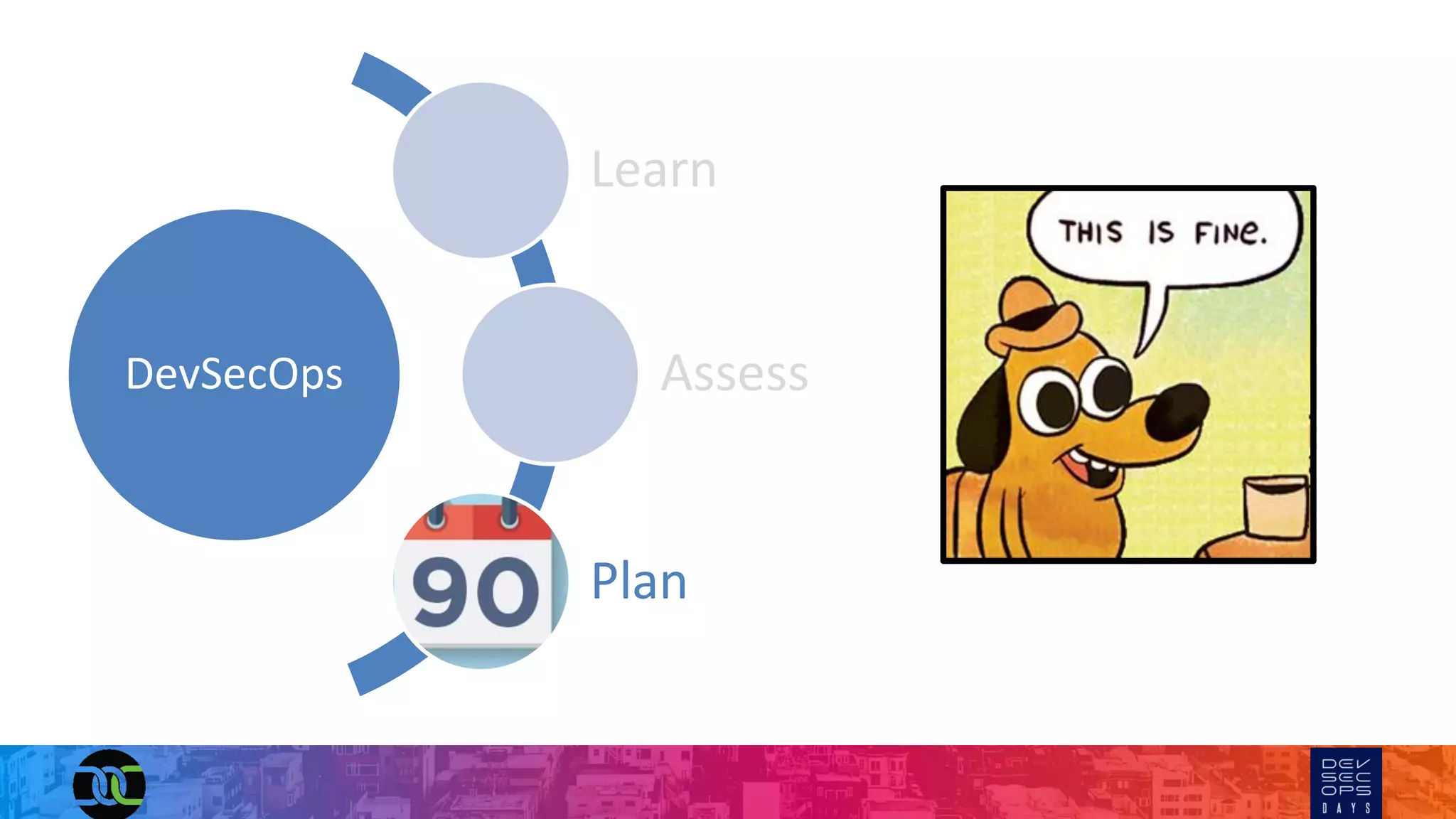
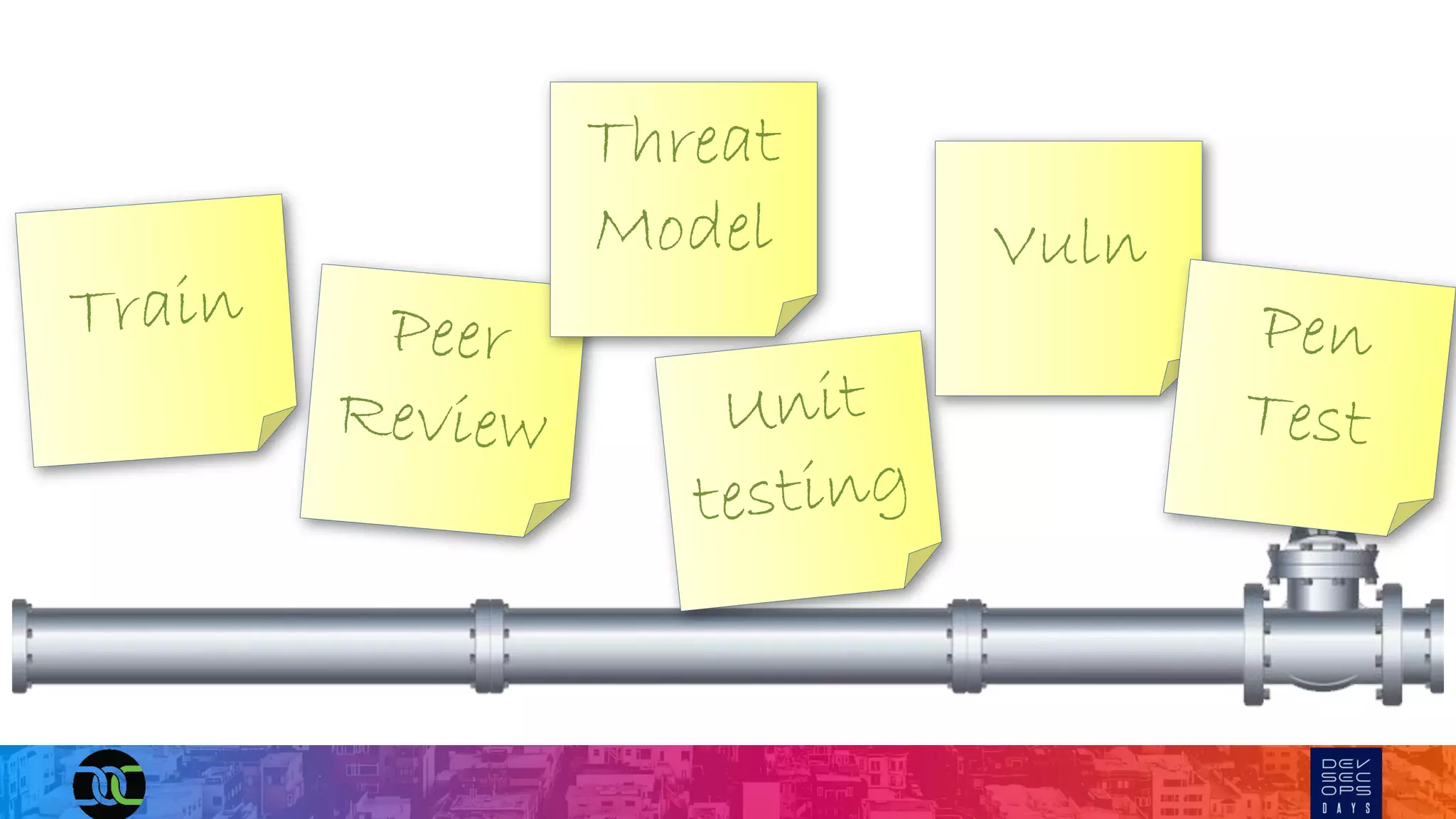
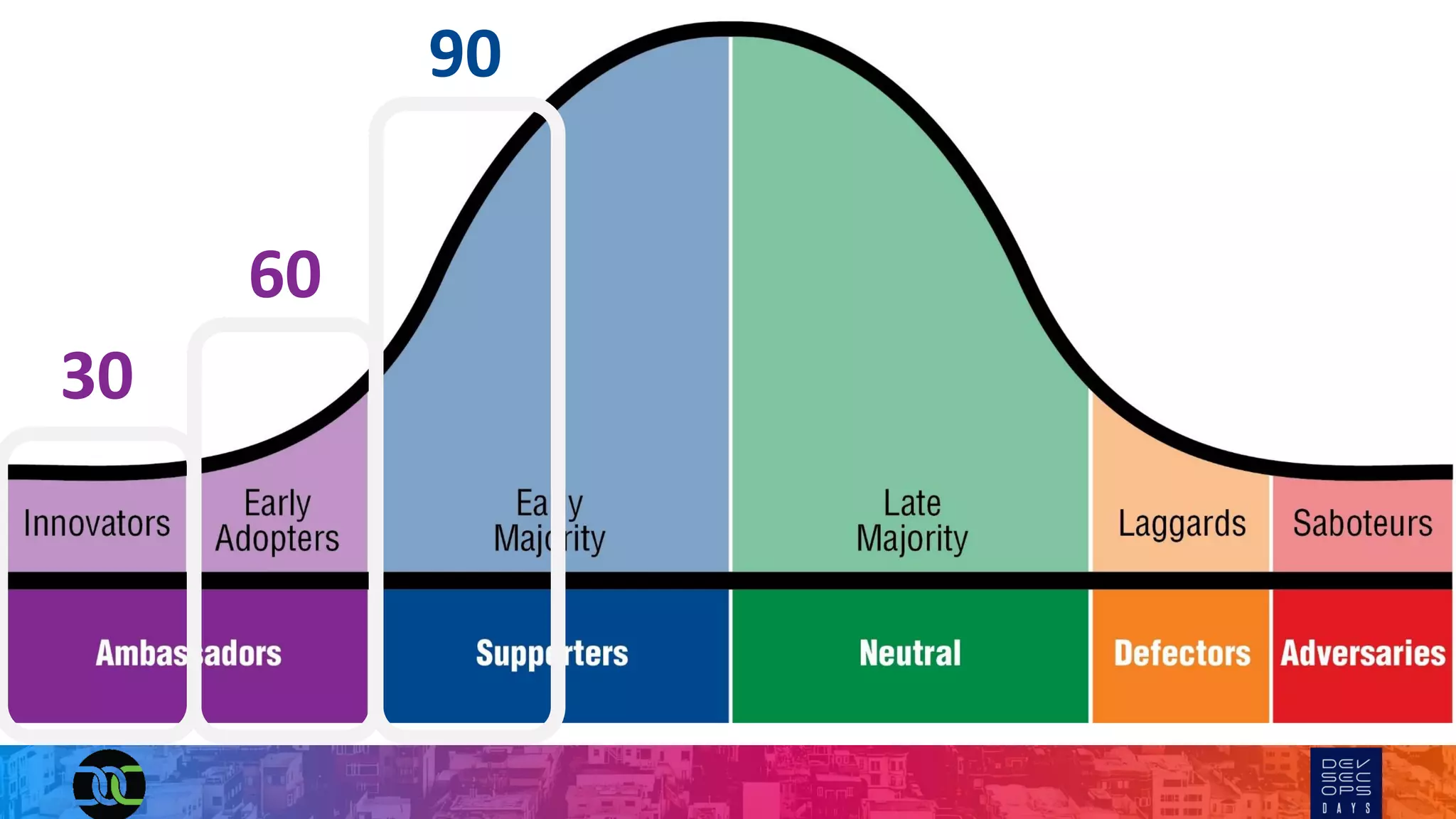
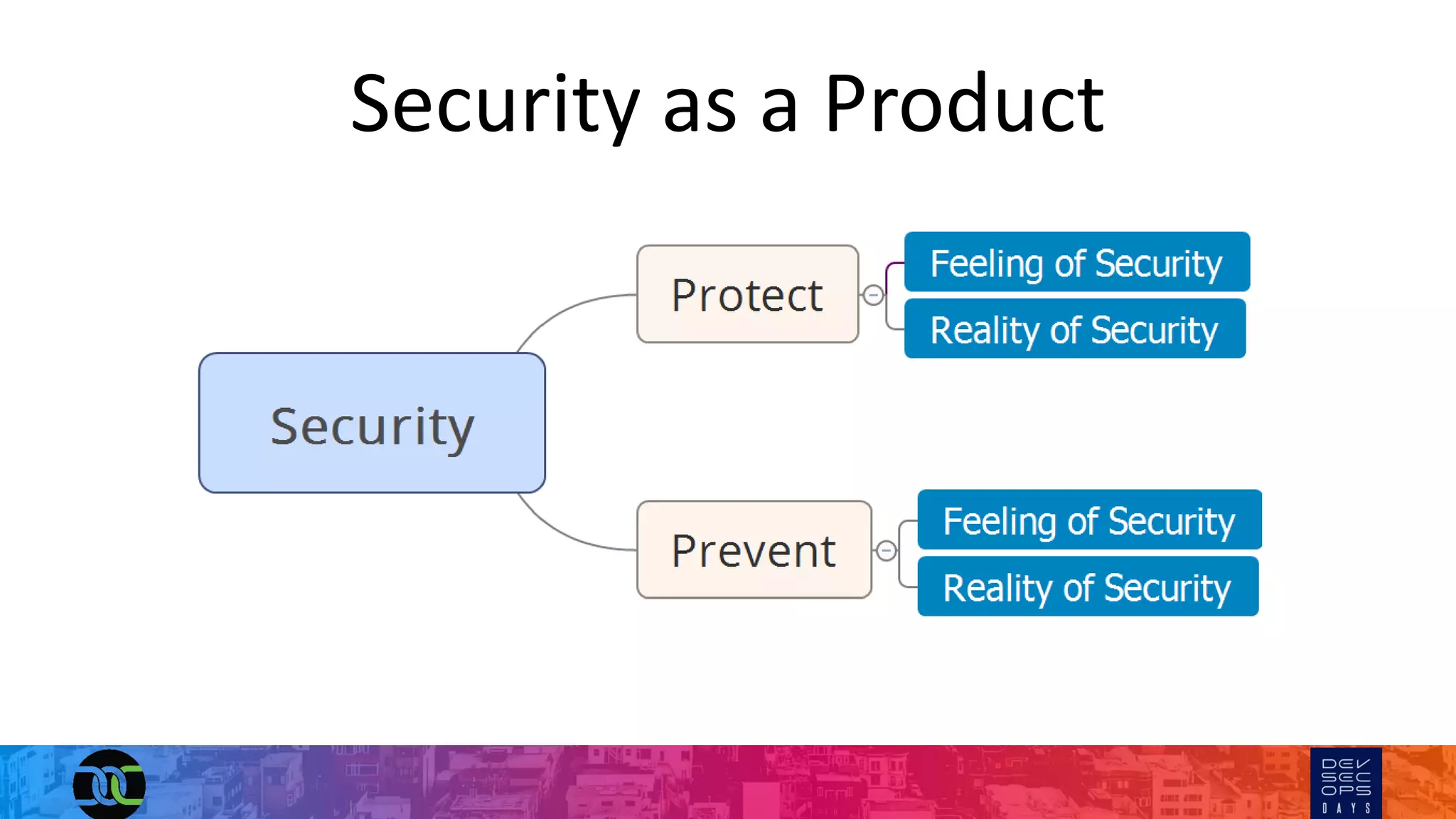
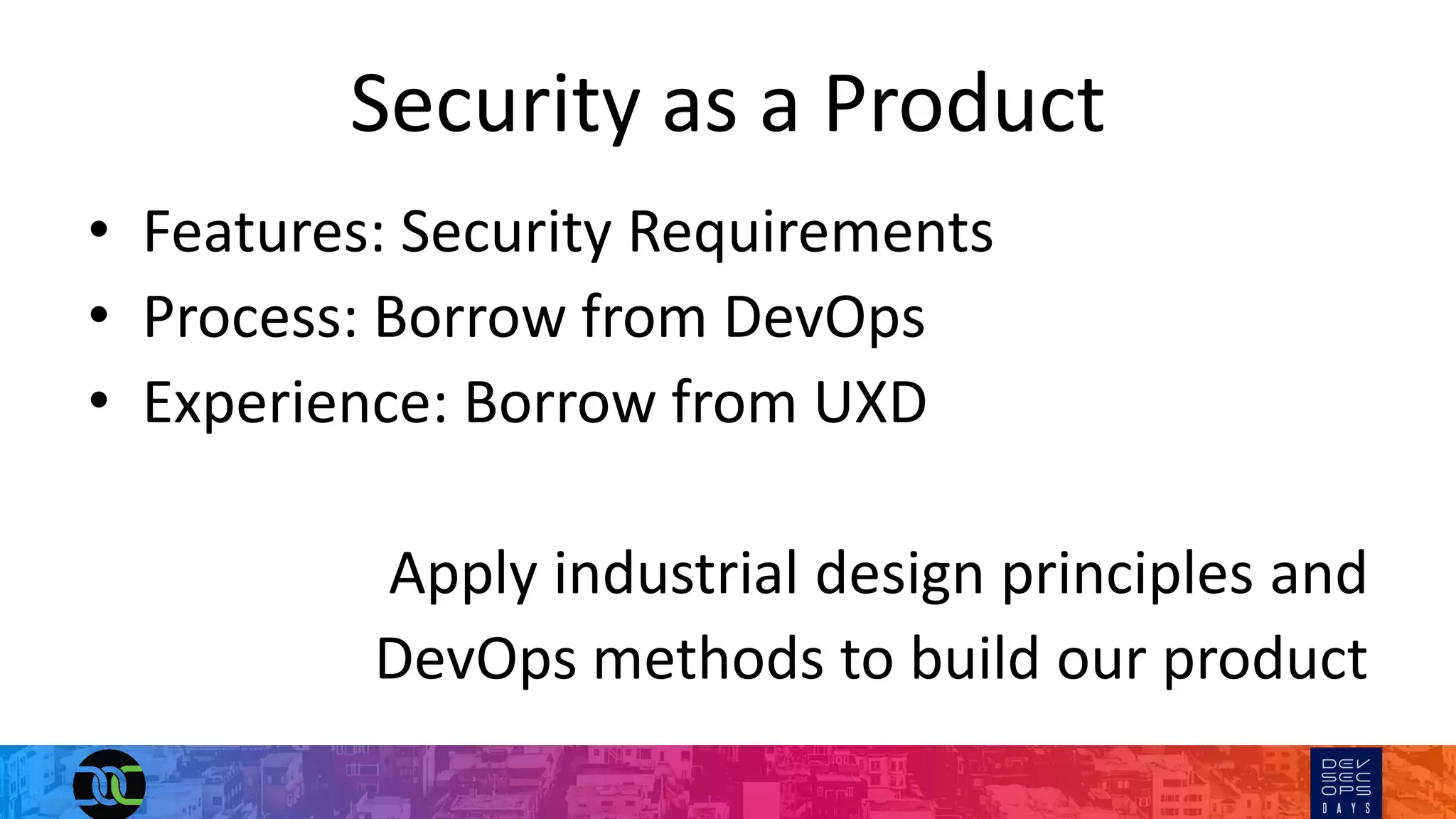
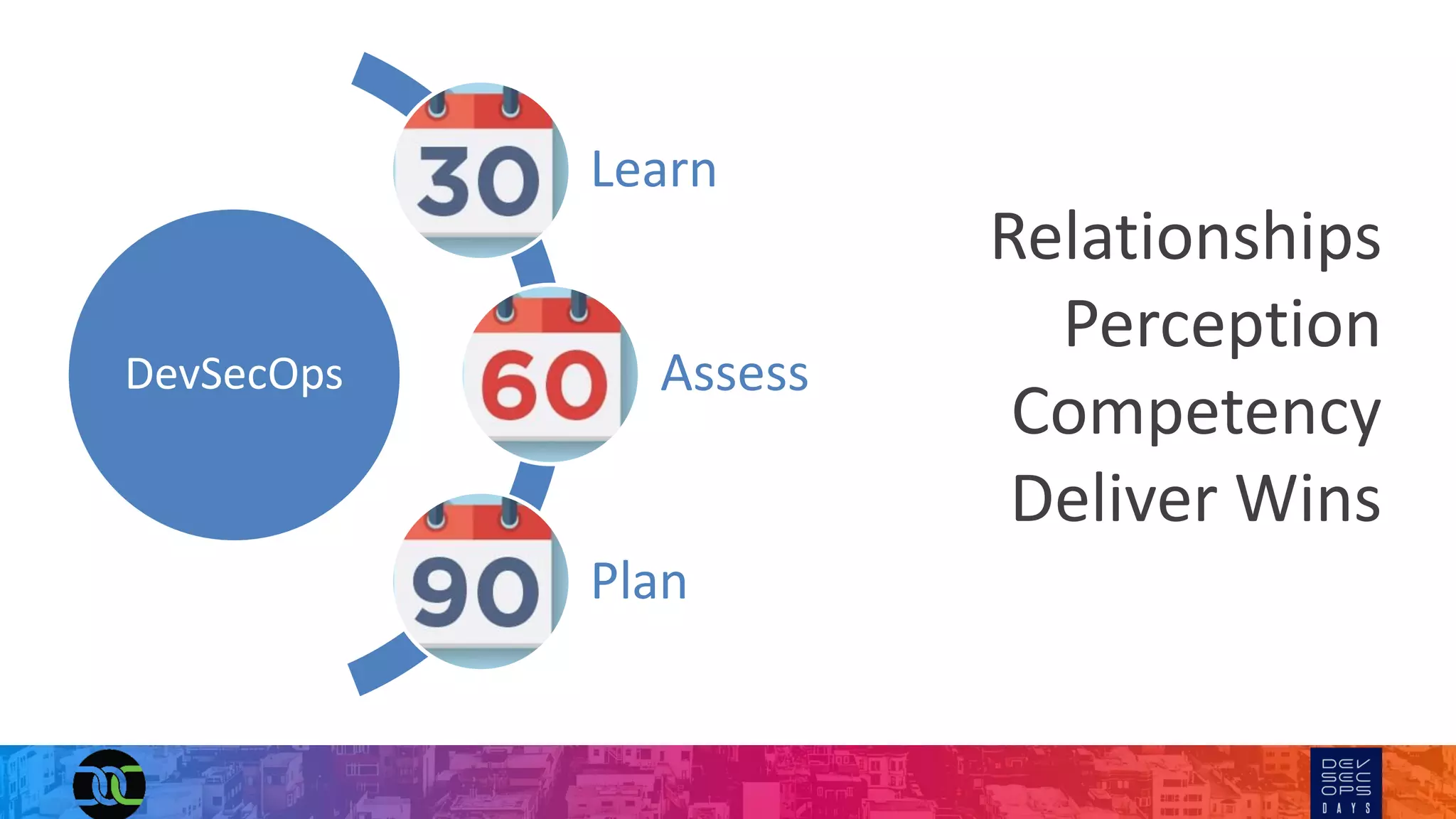
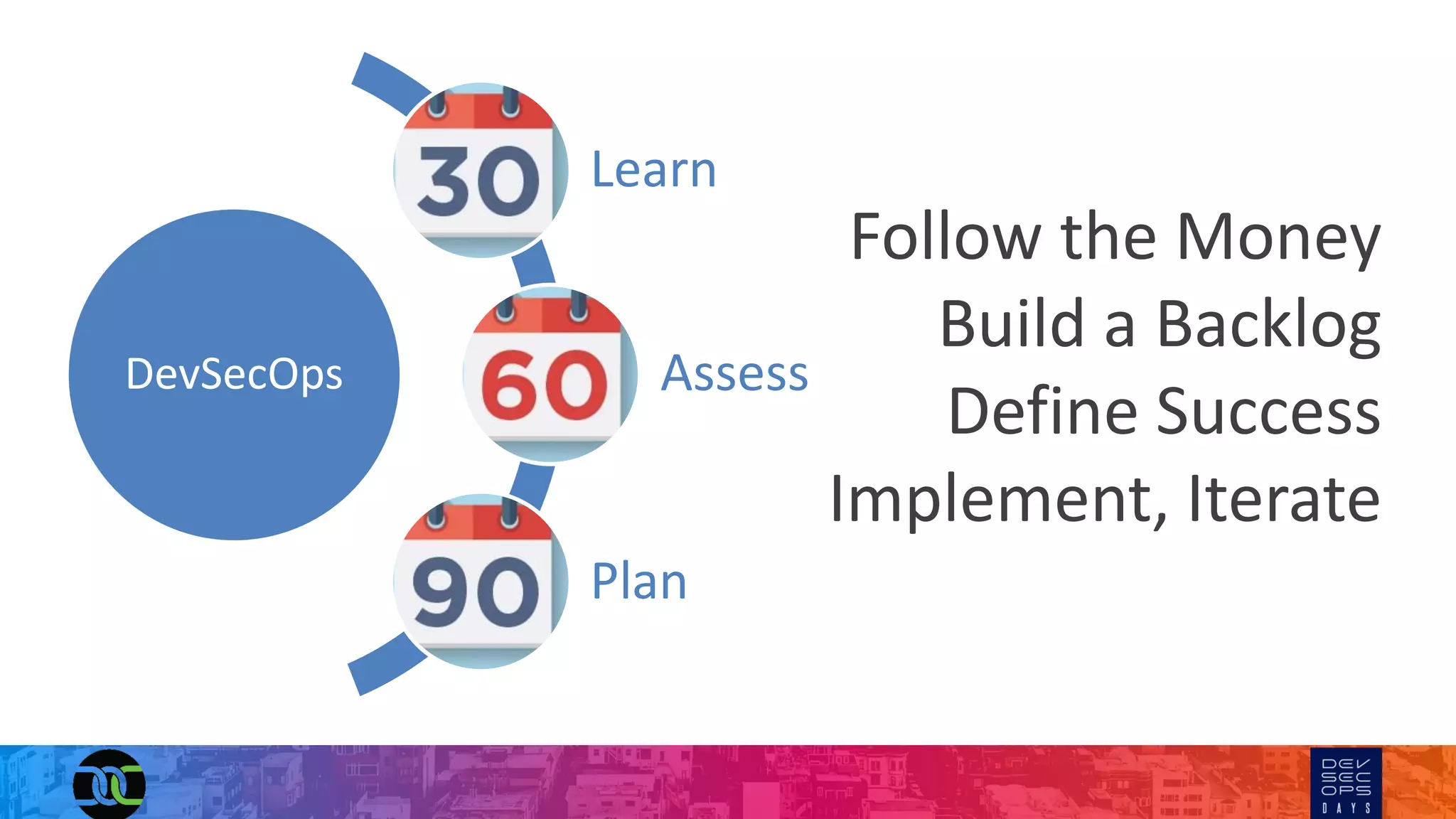
The document outlines strategies for integrating DevSecOps effectively within organizations, emphasizing the importance of relationships, maturity assessment, and a culture of security. It highlights the need for defined processes, checklists, and metrics to measure success while navigating the transition from DevOps to DevSecOps. The author, J. Wolfgang Goerlich, stresses the significance of collaboration and communication to achieve security as a product throughout the development lifecycle.