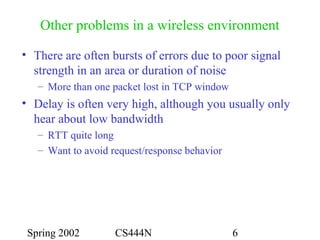
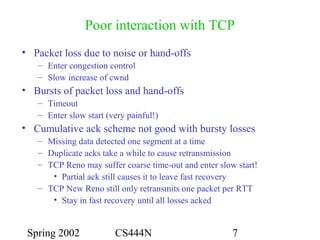
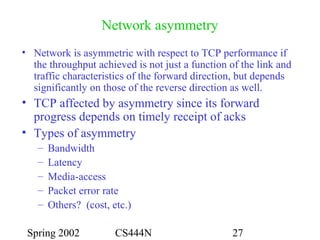
1) TCP performs poorly over wireless networks due to assuming packet loss is from congestion and responding aggressively by shrinking the congestion window.
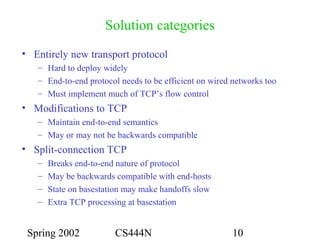
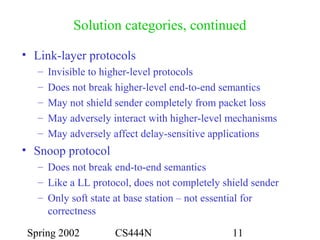
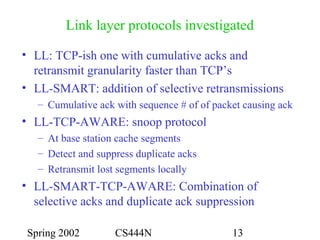
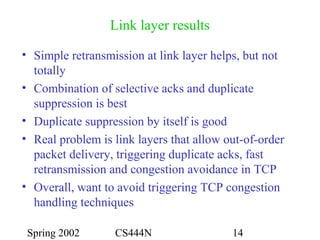
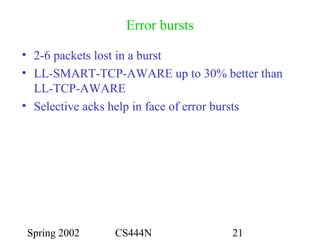
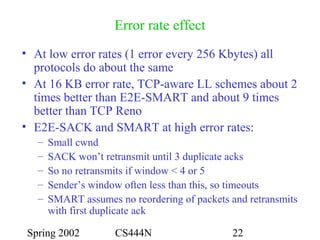
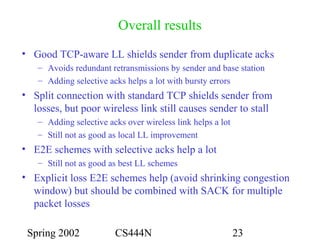
2) Link layer protocols that detect packet loss and retransmit locally without informing TCP can shield TCP from wireless losses and avoid unnecessary congestion responses. The best approach uses selective acknowledgements and suppresses duplicate ACKs.
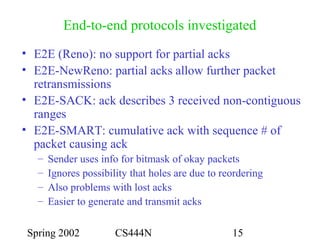
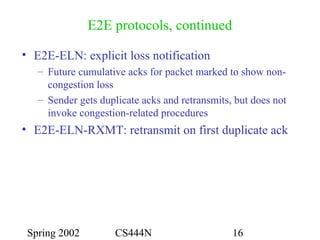
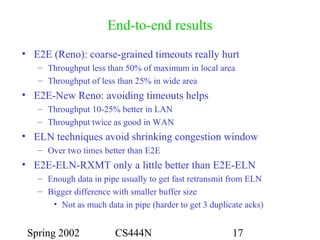
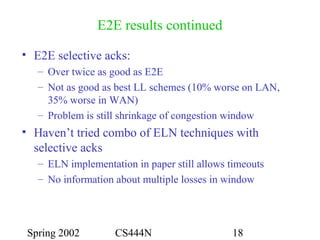
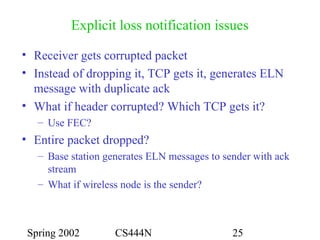
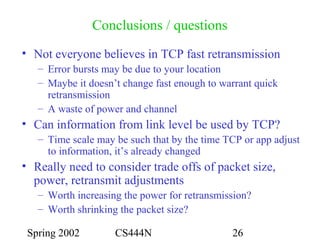
3) End-to-end protocols that explicitly notify TCP of non-congestion losses without shrinking the congestion window work better than standard TCP, but not as well as link layer approaches.