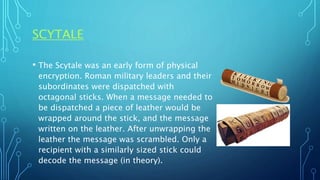
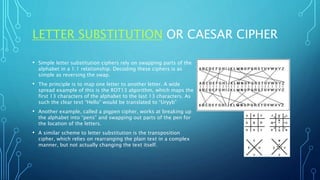
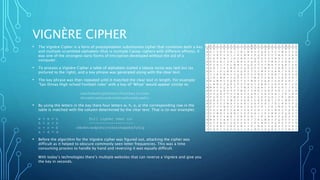
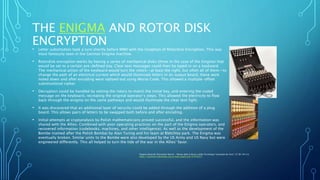
This document provides an overview of cryptography from a historical and practical perspective. It discusses early crypto systems like the Scytale and Caesar cipher. Modern systems like the Enigma machine and the One-Time Pad are explained. It also summarizes public key cryptography pioneers like PGP and the "Crypto Wars" debates around government access to encrypted communications and privacy rights.