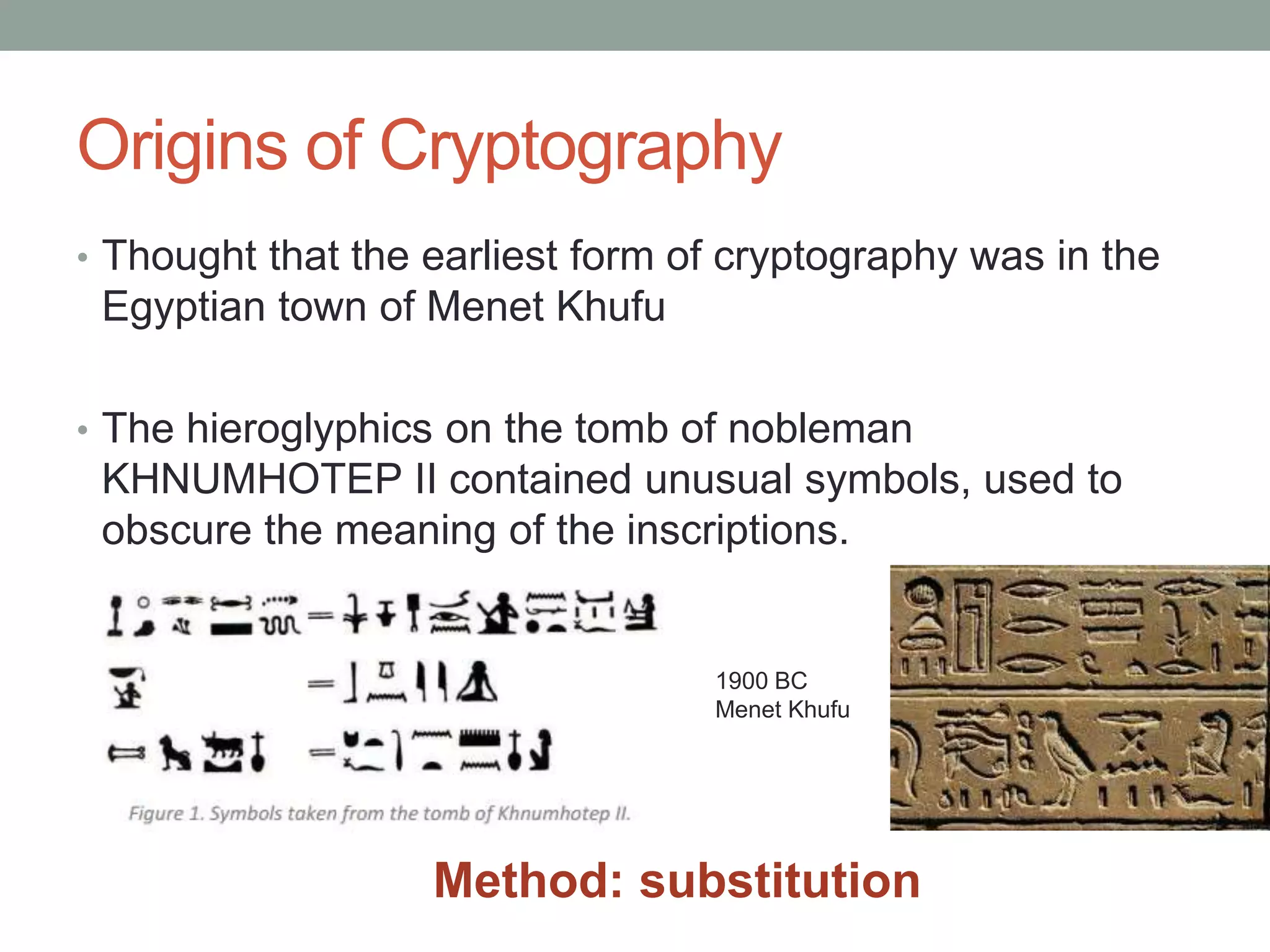
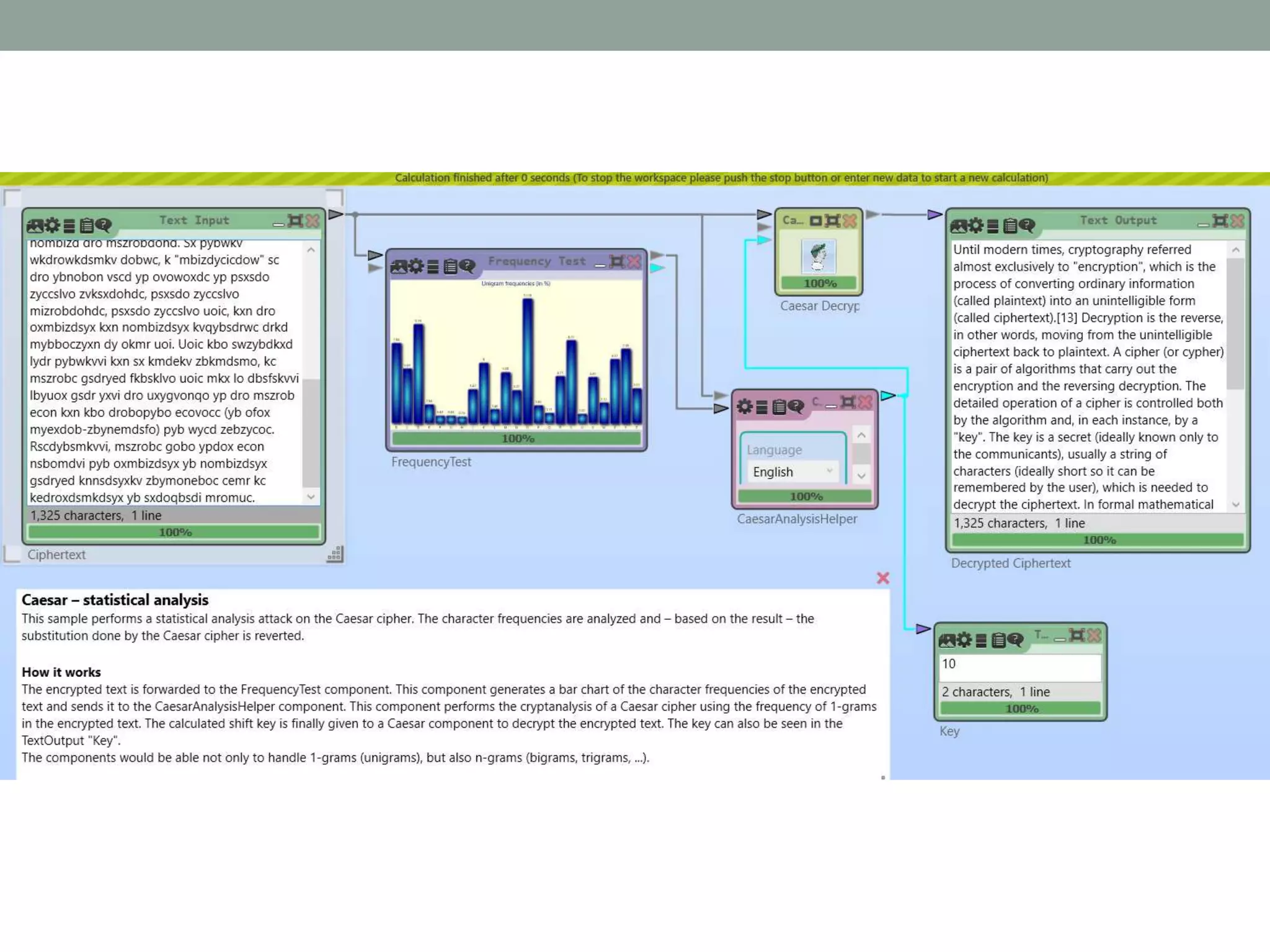
Cryptography involves encrypting information to ensure confidentiality, integrity, authentication and non-repudiation. The document discusses the history of cryptography from ancient methods like the Spartan Scytale to modern techniques like the RSA algorithm. It outlines ciphers like the Caesar cipher and Vigenere cipher, explaining how they work and can be broken through frequency analysis and determining the keyword length. The origins and workings of public key cryptography using prime number factorization with RSA is presented. Current cryptography is discussed with examples of its applications and the ongoing need to increase key lengths due to brute force attacks.










![Exdsv wynobx dswoc, mbizdyqbkzri bopobbon kvwycd ohmvecsfovi dy
"oxmbizdsyx", grsmr sc dro zbymocc yp myxfobdsxq ybnsxkbi sxpybwkdsyx (mkvvon
zvksxdohd) sxdy kx exsxdovvsqslvo pybw (mkvvon mszrobdohd).[13] Nombizdsyx sc
dro bofobco, sx ydrob gybnc, wyfsxq pbyw dro exsxdovvsqslvo mszrobdohd lkmu dy
zvksxdohd. K mszrob (yb mizrob) sc k zksb yp kvqybsdrwc drkd mkbbi yed dro
oxmbizdsyx kxn dro bofobcsxq nombizdsyx. Dro nodksvon yzobkdsyx yp k mszrob sc
myxdbyvvon lydr li dro kvqybsdrw kxn, sx okmr sxcdkxmo, li k "uoi". Dro uoi sc k
combod (snokvvi uxygx yxvi dy dro mywwexsmkxdc), ecekvvi k cdbsxq yp
mrkbkmdobc (snokvvi crybd cy sd mkx lo bowowlobon li dro ecob), grsmr sc xoonon
dy nombizd dro mszrobdohd. Sx pybwkv wkdrowkdsmkv dobwc, k "mbizdycicdow"
sc dro ybnobon vscd yp ovowoxdc yp psxsdo zyccslvo zvksxdohdc, psxsdo zyccslvo
mizrobdohdc, psxsdo zyccslvo uoic, kxn dro oxmbizdsyx kxn nombizdsyx kvqybsdrwc
drkd mybboczyxn dy okmr uoi. Uoic kbo swzybdkxd lydr pybwkvvi kxn sx kmdekv
zbkmdsmo, kc mszrobc gsdryed fkbsklvo uoic mkx lo dbsfskvvi lbyuox gsdr yxvi dro
uxygvonqo yp dro mszrob econ kxn kbo drobopybo ecovocc (yb ofox myexdob-
zbynemdsfo) pyb wycd zebzycoc. Rscdybsmkvvi, mszrobc gobo ypdox econ
nsbomdvi pyb oxmbizdsyx yb nombizdsyx gsdryed knnsdsyxkv zbymoneboc cemr kc
kedroxdsmkdsyx yb sxdoqbsdi mromuc.
13](https://image.slidesharecdn.com/cryptov4-230713173411-06b08f1c/75/Cryptography-13-2048.jpg)
![Until modern times, cryptography referred almost exclusively to "encryption",
which is the process of converting ordinary information (called plaintext) into an
unintelligible form (called ciphertext).[13] Decryption is the reverse, in other words,
moving from the unintelligible ciphertext back to plaintext. A cipher (or cypher) is a
pair of algorithms that carry out the encryption and the reversing decryption. The
detailed operation of a cipher is controlled both by the algorithm and, in each
instance, by a "key". The key is a secret (ideally known only to the communicants),
usually a string of characters (ideally short so it can be remembered by the user),
which is needed to decrypt the ciphertext. In formal mathematical terms, a
"cryptosystem" is the ordered list of elements of finite possible plaintexts, finite
possible cyphertexts, finite possible keys, and the encryption and decryption
algorithms that correspond to each key. Keys are important both formally and in
actual practice, as ciphers without variable keys can be trivially broken with only the
knowledge of the cipher used and are therefore useless (or even counter-
productive) for most purposes. Historically, ciphers were often used directly for
encryption or decryption without additional procedures such as authentication or
integrity checks.
15
https://en.wikipedia.org/wiki/Cryptography](https://image.slidesharecdn.com/cryptov4-230713173411-06b08f1c/75/Cryptography-15-2048.jpg)