Embed presentation
Download to read offline
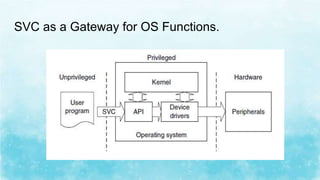
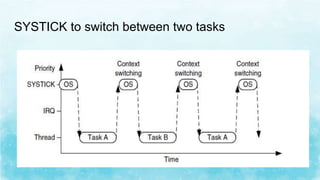
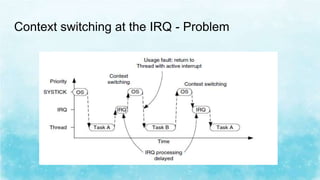
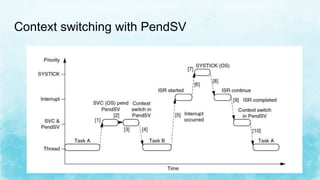
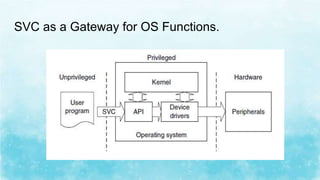
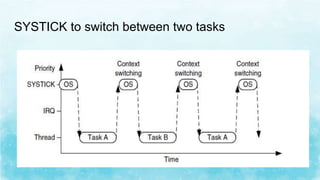
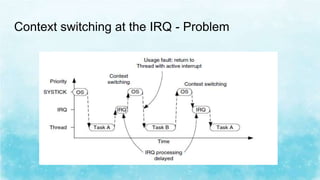
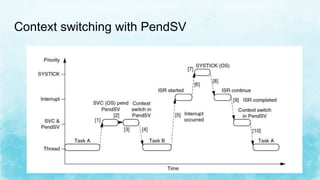
The document discusses two software exceptions - Supervisor Call (SVC) and Pendable Service Call (PendSV). SVC generates system function calls when a user program wants to use hardware. It executes the operating system exception handler to provide requested services. PendSV can pend an exception so the OS can perform an action after important tasks. For example, it is used for context switching between two active tasks triggered by an SVC call or timer interrupt. The OS prepares for switching, pends PendSV, then it performs the switch when PendSV is entered.