The document outlines exact exponential algorithms as discussed in Chapter 9 by Rohit Kumar Singh, covering various problems including the 2-table problem, subset sum, exact satisfiability, binary knapsack, k-table problem, and maximum cut. It provides definitions, examples, and complexities for each algorithm, emphasizing the methodological approach of splitting problems into sub-problems and combining solutions efficiently. Additionally, the document includes theorems and proofs demonstrating the solvability of these problems within specific time complexities.
![OUTLINE:
•Introduction
•Split and List [Williams, 2007]
•Sort and Search
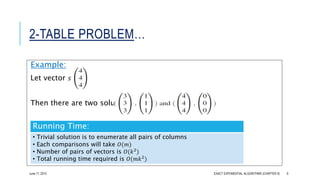
•2-TABLE Problem
•Subset Sum
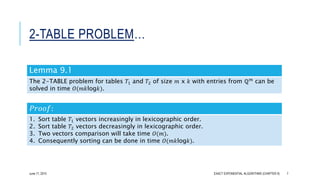
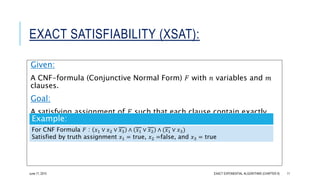
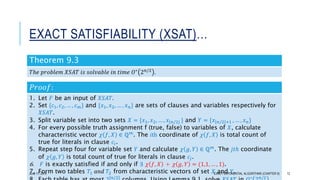
•Exact Satisfiability (XSAT)
•Binary Knapsack
•K-TABLE problem
•Maximum Cut
EXACT EXPONENTIAL ALGORITHMS (CHAPTER 9) 2June 17, 2015](https://image.slidesharecdn.com/splitandlist-150708131821-lva1-app6891/85/Split-and-list-technique-for-solving-hard-problems-2-320.jpg)


![SUBSET SUM:
[HOROWITZ, SAHNI, 1974]
Given:
Positive integers 𝑎1, 𝑎2, … , 𝑎 𝑛, and 𝑆
Goal:
Find a subset 𝐼 ⊆ {1,2, … 𝑛} such that
𝑖∈I
𝑎𝑖 = 𝑆,
Example:
𝑎1 = 5, 𝑎2 = 5, 𝑎3 = 10, 𝑎4 = 60, 𝑎5 = 61, and 𝑆 = 70, the solution is 𝐼 =
{1,2,4}
EXACT EXPONENTIAL ALGORITHMS (CHAPTER 9) 9June 17, 2015](https://image.slidesharecdn.com/splitandlist-150708131821-lva1-app6891/85/Split-and-list-technique-for-solving-hard-problems-9-320.jpg)
![SUBSET SUM…
[HOROWITZ, SAHNI, 1974]
Theorem 9.2
𝑇ℎ𝑒 𝑆𝑈𝐵𝑆𝐸𝑇 𝑆𝑈𝑀 𝑝𝑟𝑜𝑏𝑙𝑒𝑚 𝑐𝑎𝑛 𝑏𝑒 𝑠𝑜𝑙𝑣𝑒𝑑 𝑖𝑛 𝑡𝑖𝑚𝑒 𝑂(𝑛2 𝑛/2
).
𝑃𝑟𝑜𝑜𝑓:
1. Partition {𝑎1, 𝑎2, … , 𝑎 𝑛} into two sets X = {𝑎1, 𝑎2, … , 𝑎⌊𝑛/2⌋} and Y = {𝑎 𝑛/2 +1, … , 𝑎 𝑛}
2. Compute set of all possible subset sums for both sets 𝑋 and 𝑌 ≤ 2 𝑛/2+1
3. Let 𝐼 𝑋 = {𝑠1, 𝑠2, … , 𝑠 𝑘} and 𝐼 𝑌 = {𝑟1, 𝑟2, … , 𝑟𝑘} where 𝑠 𝑋 ∈ 𝐼 𝑋 and 𝑟𝑌 ∈ 𝐼 𝑌 such that 𝑠 𝑋 +
𝑟𝑌 = 𝑆
4. To find 𝑠 𝑋 and 𝑟𝑌 we reduce the problem into 2-TABLE problem.
5. Table 𝑇1 and 𝑇2 is formed by elements of 𝐼 𝑋 and 𝐼 𝑌
6. Both table sizes will be 𝑚 x 𝑘, where 𝑚 = 1 and 𝑘 ≤ 2 𝑛/2
7. Using Lemma 9.1, we can calculate two elements (𝑠 𝑋, 𝑟𝑌) in 𝑂(2 𝑛/2
𝑙𝑜𝑔2 𝑛/2
) =
𝑂(𝑛2 𝑛/2)
EXACT EXPONENTIAL ALGORITHMS (CHAPTER 9) 10June 17, 2015](https://image.slidesharecdn.com/splitandlist-150708131821-lva1-app6891/85/Split-and-list-technique-for-solving-hard-problems-10-320.jpg)

![BINARY KNAPSACK:
[SCHROEPPEL, SHAMIR, 1981]
Given:
Positive integer 𝑊 and 𝑛 items 𝑆 = {𝑠1, 𝑠2, … , 𝑠 𝑛},
Each item has value 𝑎𝑖 and its weight 𝑤𝑖 which are +𝑣𝑒 integers.
Goal:
Find 𝑆′
⊆ 𝑆 such that,
𝑖∈𝑆′ 𝑤𝑖 ≤ 𝑊 and 𝑖∈𝑆′ 𝑎𝑖 is maximized
EXACT EXPONENTIAL ALGORITHMS (CHAPTER 9) 14June 17, 2015](https://image.slidesharecdn.com/splitandlist-150708131821-lva1-app6891/85/Split-and-list-technique-for-solving-hard-problems-14-320.jpg)
![BINARY KNAPSACK…
[SCHROEPPEL, SHAMIR, 1981]
Theorem 9.4
𝑇ℎ𝑒 𝐵𝐼𝑁𝐴𝑅𝑌 𝐾𝑁𝐴𝑃𝑆𝐴𝐶𝐾 𝑝𝑟𝑜𝑏𝑒𝑙𝑚 𝑖𝑠 𝑠𝑜𝑙𝑣𝑎𝑏𝑙𝑒 𝑖𝑛 𝑡𝑖𝑚𝑒 𝑂∗
2 𝑛/2
.
𝑷𝒓𝒐𝒐𝒇:
1. Split the set of items in two subsets {𝑠1, 𝑠2, … , 𝑠⌊𝑛/2⌋} and 𝑠 𝑛/2 +1, … , 𝑠 𝑛 .
2. For each subset 𝐼 ⊆ {1,2, … , ⌊𝑛/2⌋ }, construct a couple 𝑥𝐼 = 𝐴𝐼, 𝑊𝐼 , where 𝐴𝐼 =
𝑖∈𝐼 𝑎𝑖, and 𝑊𝐼 = 𝑖∈𝐼 𝑤𝑖.
3. Put all couples in set 𝑋 whose cardinality is at most 2 𝑛/2
.
4. Repeat step two to construct 𝑦𝐽 = (𝐴𝐽, 𝑊𝐽) where 𝐽 ⊆ 𝑛/2 + 1, 𝑛/2 + 1 + 1, … , 𝑛
and step three to obtain couples set 𝑌.
5. Find couples 𝑥𝐼 ∈ 𝑋 and 𝑦𝐼 ∈ 𝑌 such that 𝐴𝐼 + 𝐴𝐽 is maximum and 𝑊𝐼 + 𝑊𝐽 ≤ 𝑊.
6. Remove couples dominated by other couples by preprocessing in order to convert
the instance into Modified 2-TABLE problem.
EXACT EXPONENTIAL ALGORITHMS (CHAPTER 9) 17June 17, 2015](https://image.slidesharecdn.com/splitandlist-150708131821-lva1-app6891/85/Split-and-list-technique-for-solving-hard-problems-17-320.jpg)
![BINARY KNAPSACK…
[SCHROEPPEL, SHAMIR, 1981]
𝑃𝑟𝑜𝑜𝑓…
Preprocessing Steps:
1. Sort items of 𝑋 in increasing order of their weight { 𝐴1, 𝑊1 , 𝐴2, 𝑊2 , … , (𝐴 𝑘, 𝑊𝑘)},
where 𝑘 ≤ 2 𝑛/2.
2. For every 1 ≤ 𝑖 < 𝑗 ≤ 𝑘, 𝑊𝑖 ≤ 𝑊𝑗, we define 𝐴 ≔ 𝐴1 and move into the list from 1 to
𝑘.
3. If 𝐴𝑖 > 𝐴, replace 𝐴 ≔ 𝐴𝑖 otherwise (𝐴𝑖 ≤ 𝐴), we remove (𝐴𝑖, 𝑊𝑖).
4. Step 1-3 is repeated for set 𝑌.
1. We have 𝐴𝐼, 𝑊𝐼 ∈ 𝑋 and 𝐴𝐽, 𝑊𝐽 ∈ 𝑌, and maximum sum 𝐴𝐼 + 𝐴𝐽 subject to 𝑊𝐼 +
𝑊𝐽 ≤ 𝑊.
2. Construct a table of size 2x2 𝑛/2
and 𝑇1 = 𝑠𝑒𝑡 𝑋 and 𝑇2 = 𝑠𝑒𝑡 𝑌 to implement
MODIFIED 2-TABLE.
3. Total running time = Sorting time O(𝑘𝑙𝑜𝑔𝑘) + finding set with no dominant couple
in time 𝑂(𝑘). EXACT EXPONENTIAL ALGORITHMS (CHAPTER 9) 18June 17, 2015](https://image.slidesharecdn.com/splitandlist-150708131821-lva1-app6891/85/Split-and-list-technique-for-solving-hard-problems-18-320.jpg)
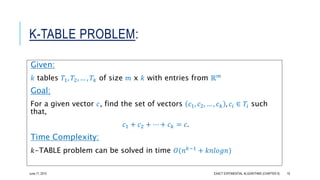
![K-TABLE PROBLEM…
•2-TABLE problem uses 𝑘 = 2 𝑛/2 and hence useful in reducing space
requirement by algorithms we discussed.
•𝑘-TABLE problem is used by [Schroeppel, Shamir, 81] to reduce the
space requirement to 2 𝑛/4
Example:
• Problem like 𝑋𝑆𝐴𝑇 can be split into 𝑘 subsets.
• Then construct 2 𝑛/𝑘
sets of vector for each table.
• By using 2-TABLE algorithm recursively, 𝑘-TABLE problem of 𝑋𝑆𝐴𝑇 can be solved
in time 𝑂∗
(2 𝑘−1 𝑛/𝑘
)
EXACT EXPONENTIAL ALGORITHMS (CHAPTER 9) 20June 17, 2015](https://image.slidesharecdn.com/splitandlist-150708131821-lva1-app6891/85/Split-and-list-technique-for-solving-hard-problems-20-320.jpg)
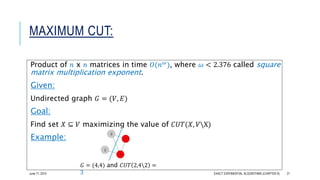
![MAXIMUM CUT…
Theorem 9.5 [Itai, Rodeh, 1978]
𝐴 𝑡𝑟𝑖𝑎𝑛𝑔𝑙𝑒 𝑖𝑛 𝑎 𝑔𝑟𝑎𝑝ℎ 𝑜𝑛 𝑎 𝑛 𝑣𝑒𝑟𝑡𝑖𝑐𝑒𝑠 𝑐𝑎𝑛 𝑏𝑒 𝑓𝑜𝑢𝑛𝑑 𝑖𝑛 𝑡𝑖𝑚𝑒 𝑂 𝑛 𝜔 𝑎𝑛𝑑 𝑖𝑛 𝑂 𝑛2 𝑠𝑝𝑎𝑐𝑒.
𝑃𝑟𝑜𝑜𝑓:
1. Let 𝐴(𝐺) be the adjacency matrix of G.
2. 𝑘𝑡ℎ power of 𝐴 𝐺
𝑘
of 𝐴(𝐺) the entry 𝐴 𝐺
𝑘
⌊𝑖, 𝑖⌋ on the main diagonal of 𝐴 𝐺
𝑘
is equal to number of walks of length 𝑘 which starts and ends at vertex 𝑖.
3. A walk of length 3 = triangle, so non-zero entries at the diagonals of 𝐴 𝐺
3
assures triangles in G.
4. Time required is 𝑂(𝑛 𝜔).
5. Space requirement is proportional to size of 𝐴(𝐺), which is 𝑛2
.
EXACT EXPONENTIAL ALGORITHMS (CHAPTER 9) 22June 17, 2015](https://image.slidesharecdn.com/splitandlist-150708131821-lva1-app6891/85/Split-and-list-technique-for-solving-hard-problems-22-320.jpg)
![MAXIMUM CUT…
[WILLIAMS, 2007]
Theorem 9.6
𝑇ℎ𝑒 𝑀𝐴𝑋𝐼𝑀𝑈𝑀 𝐶𝑈𝑇 𝑝𝑟𝑜𝑏𝑙𝑒𝑚 𝑜𝑛 𝑛-𝑣𝑒𝑟𝑡𝑒𝑥 𝑔𝑟𝑎𝑝ℎ𝑠 𝑖𝑠 𝑠𝑜𝑙𝑣𝑎𝑏𝑙𝑒 𝑖𝑛 𝑡𝑖𝑚𝑒 𝑂∗ 2 𝜔𝑛/3 =
O 1.7315n
, where 𝜔 < 2.376 𝑖𝑠 𝑠𝑞𝑢𝑎𝑟𝑒 𝑚𝑎𝑡𝑟𝑖𝑥 𝑚𝑢𝑙𝑡𝑖𝑝𝑙𝑖𝑐𝑎𝑡𝑖𝑜𝑛 𝑒𝑥𝑝𝑜𝑛𝑒𝑛𝑡.
[Coppersmith, Winograd, 1990]
𝑃𝑟𝑜𝑜𝑓:
• Let 𝐺(𝑉, 𝐸) is a graph on 𝑛 vertices and
n
3
= 0. Let 𝑉0, 𝑉1, 𝑉2 are partitions of 𝑉 into
sets of sizes
𝑛
3
.
• Construct a auxiliary weighted directed graph 𝐴 𝐺 as follow:
1. ∀ subset 𝑋 ⊆ 𝑉𝑖, 0 ≤ 𝑖 ≤ 2, graph 𝐴(𝐺) has vertex 𝑋.
2. Total vertices in 𝐴(𝐺) is 3 x 2 𝑛/3.
3. 𝐴 𝐺 has all possible pairs of arcs between (𝑋, 𝑌) where 𝑋 ⊆ 𝑉𝑖, 𝑌 ⊆ 𝑉𝑗, and 𝑗 = 𝑖 +
1(𝑚𝑜𝑑3).
4. Total number of arcs in 𝐴 𝐺 = 3 x (22𝑛/3
).
5. Define weight for for every arc (𝑋, 𝑌), 𝑋 ⊆ 𝑉𝑖 and 𝑌 ⊆ 𝑉𝑗, 𝑖 ≠ 𝑗 asEXACT EXPONENTIAL ALGORITHMS (CHAPTER 9) 23June 17, 2015](https://image.slidesharecdn.com/splitandlist-150708131821-lva1-app6891/85/Split-and-list-technique-for-solving-hard-problems-23-320.jpg)
![MAXIMUM CUT…
[WILLIAMS, 2007]
𝑃𝑟𝑜𝑜𝑓 …
Claim: The following properties are equivalent
(𝑖) There is 𝑋 ⊆ 𝑉 such that 𝐶𝑈𝑇 𝑋, 𝑉X = 𝑡.
(𝑖𝑖) The 𝐴(𝐺) contains directed triangle 𝑋0, 𝑋1, 𝑋2, 𝑋𝑖 ⊆ 𝑉𝑖, 0 ≤ 𝑖 ≤ 2, such that
𝑡 = 𝑤 𝑋0, 𝑋1 + 𝑤 𝑋1, 𝑋2 + 𝑤(𝑋2, 𝑋0)
𝑃𝑟𝑜𝑜𝑓 𝑜𝑓 𝑐𝑙𝑎𝑖𝑚𝑠:
1. 𝑖 ⇒ 𝑖𝑖 , put 𝑋𝑖 = 𝑋 ∩ 𝑉𝑖, 0 ≤ 𝑖 ≤ 2
2. Every edge 𝑒 = 1 if 𝑒 is edge between 𝑋 and VX otherwise 0 to the sum
𝑤 𝑋0, 𝑋1 + 𝑤 𝑋1, 𝑋2 + 𝑤(𝑋2, 𝑋0)
1. 𝑖𝑖 ⇒ 𝑖 , put 𝑋 = 𝑋0 ∪ 𝑋1 ∪ 𝑋2,
2. Every edge e counted in 𝐶𝑈𝑇 𝑋, 𝑉X is same as counted in sum
𝑤 𝑋0, 𝑋1 + 𝑤 𝑋1, 𝑋2 + 𝑤(𝑋2, 𝑋0)
EXACT EXPONENTIAL ALGORITHMS (CHAPTER 9) 24June 17, 2015](https://image.slidesharecdn.com/splitandlist-150708131821-lva1-app6891/85/Split-and-list-technique-for-solving-hard-problems-24-320.jpg)
![MAXIMUM CUT…
[WILLIAMS, 2007]
𝑃𝑟𝑜𝑜𝑓 …
1. To proof claim 𝑖𝑖 holds, we try all possible values of 𝑤 𝑋𝑖, 𝑋𝑗 , 𝑗 = 𝑖 + 1(𝑚𝑜𝑑3).
2. For every triple 𝑊 = (𝑤01, 𝑊12, 𝑊20) such that 𝑤 = 𝑤01 + 𝑤12 + 𝑤20, construct
subgraph 𝐴 𝐺, 𝑊 of 𝐴(𝐺) having only arcs of weight 𝑤𝑖𝑗 from 𝑋𝑖 ⊆ 𝑉𝑖 to 𝑋𝑗 ⊆ 𝑉𝑗.
3. For ∀ 𝑡, number of such triples is 𝑡3.
4. The subgraph 𝐴(𝐺, 𝑊) for all arcs of 𝐴(𝐺) can be constructed in time 𝑂∗
2 𝑛/3 2
.
5. 𝐴 𝐺, 𝑊 contains triangle can be verified in time 𝑂∗
2 𝑛/3 𝜔
using Theorem 9.5 .
6. The total running time is 𝑂∗(𝑡. t3 22𝑛/3 + 2 𝑛𝜔/3 ) = 𝑂∗(2 𝜔𝑛/3).
June 17, 2015 EXACT EXPONENTIAL ALGORITHMS (CHAPTER 9) 25](https://image.slidesharecdn.com/splitandlist-150708131821-lva1-app6891/85/Split-and-list-technique-for-solving-hard-problems-25-320.jpg)