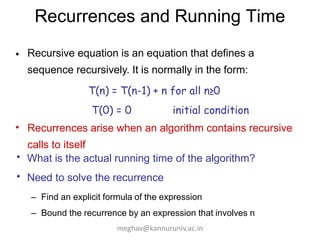
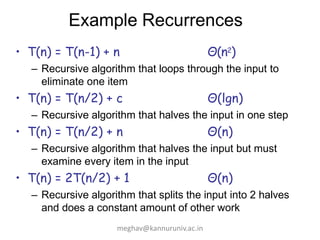
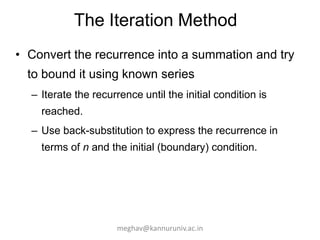
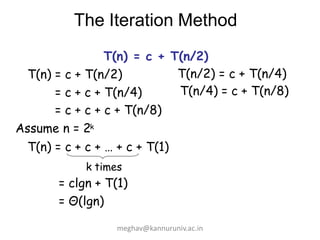
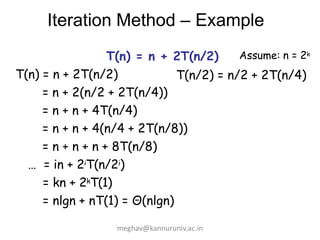
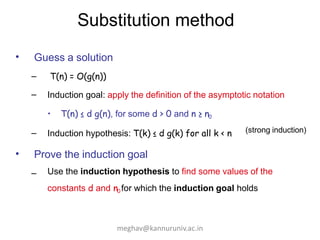
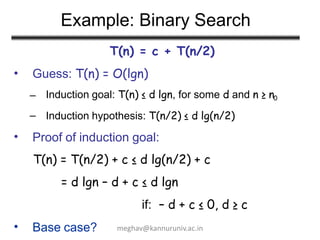
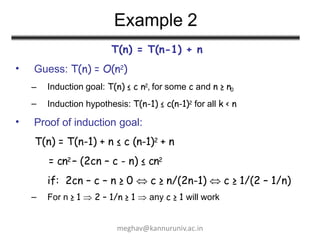
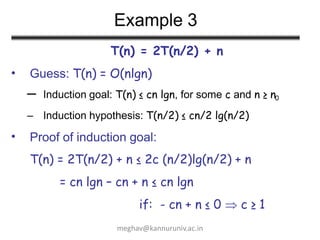
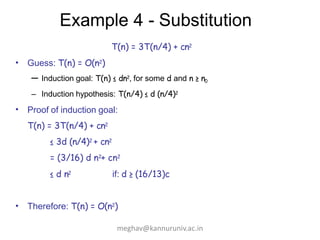
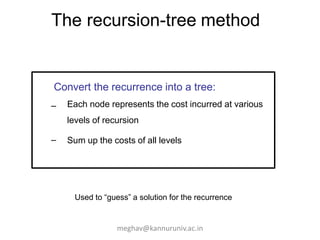
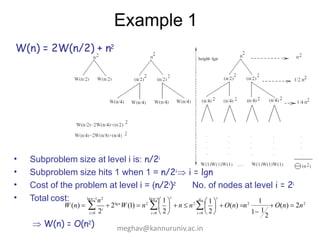
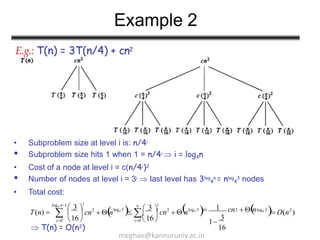
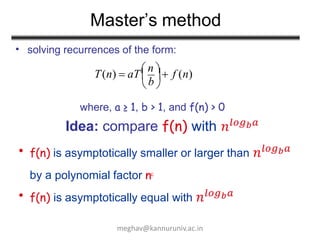
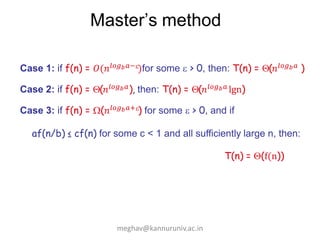
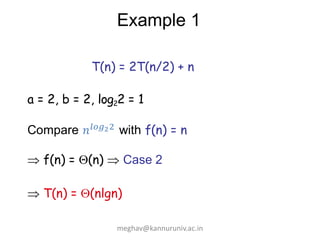
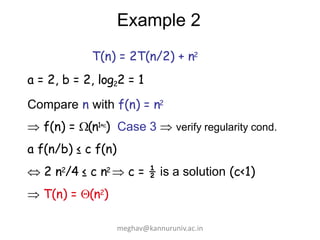
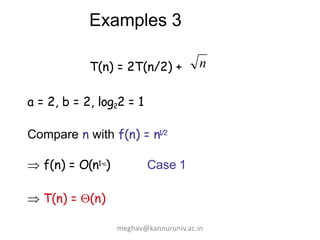
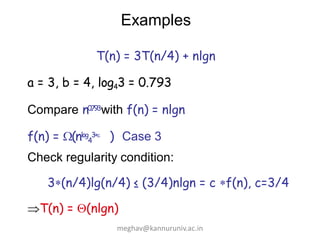
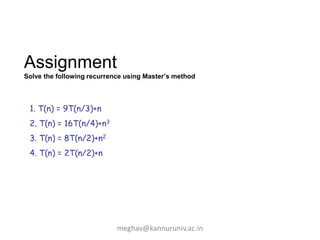
The document discusses methods for solving recurrences in algorithms, focusing on recursive and non-recursive algorithms. It presents various techniques such as the iteration method, substitution method, recursion tree method, and the master theorem, illustrated with examples. The content emphasizes finding explicit formulas for recurrences and understanding their running time in relation to algorithmic efficiency.