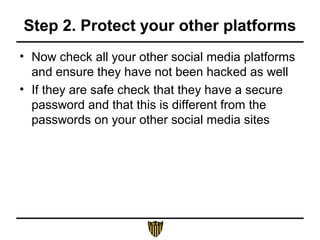
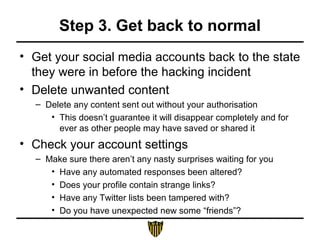
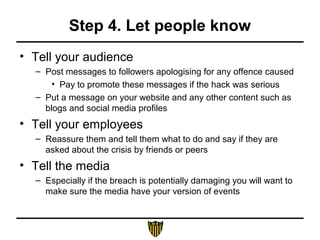
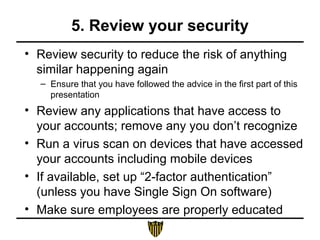
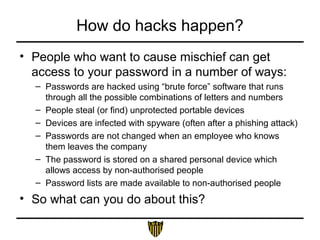
This document provides guidance on preventing social media hacks and responding if hacking occurs. To prevent hacking, it recommends using robust passwords, limiting account access, controlling cookies, educating users, and being careful with mobile devices. If hacked, the five steps are: 1) regain control by resetting passwords; 2) protect other platforms; 3) get accounts back to normal by deleting unwanted content and checking settings; 4) let your audience and employees know; and 5) thoroughly review security measures.

![Step 1. Regain control by resetting
passwords
• Change the password on the account (to
something harder to hack)
• If the hackers have changed the password, reset
it using the forgotten password link on the site
– At the same time change the password of the account
administrator’s email address as this may have been hacked too
• If the hackers have locked you out of your
account contact the social platform directly:
– Search [platform name] AND hacked OR compromised to find
the right page](https://image.slidesharecdn.com/socialmediasecurity-140502095513-phpapp01/85/Social-media-security-16-320.jpg)