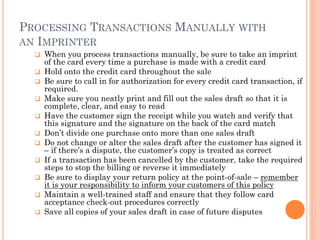
The document provides a comprehensive guide for small businesses on avoiding fraudulent chargebacks and other types of fraud, detailing common scams, risk factors, and preventative measures. It highlights the importance of adhering to merchant agreements, protecting against card-not-present fraud, and the handling of chargeback processes to mitigate financial losses. Furthermore, it emphasizes the need for training staff and employing security protocols to enhance transaction safety.