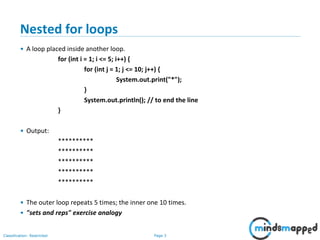
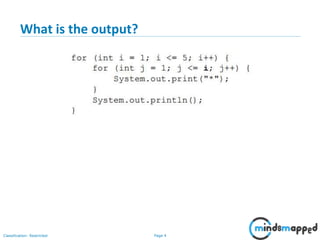
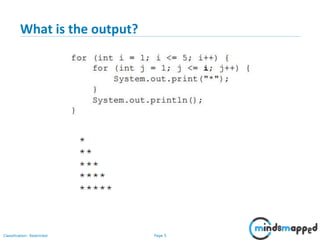
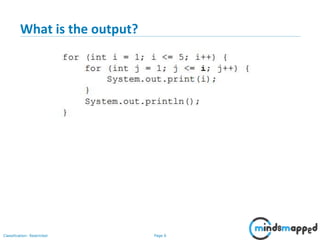
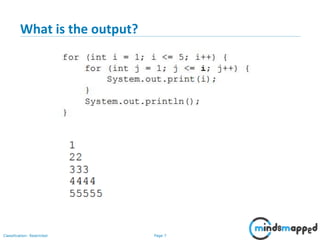
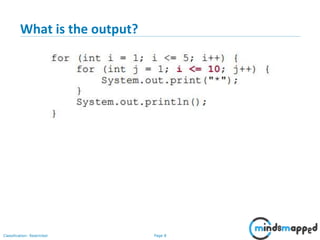
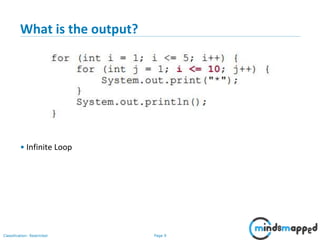
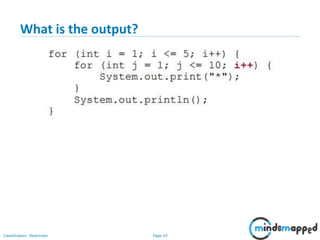
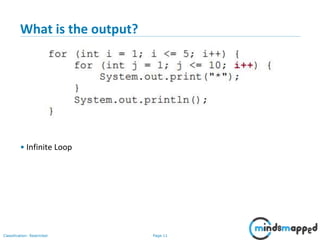
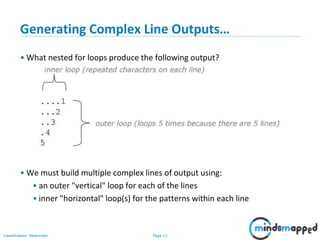
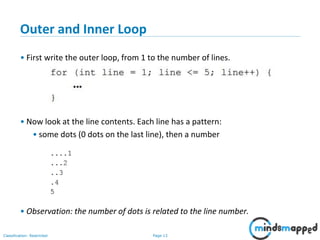
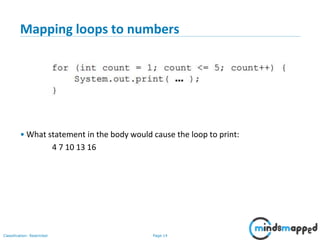
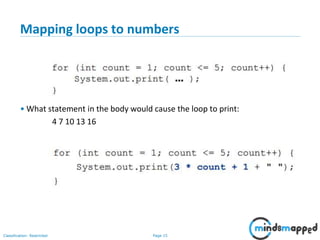
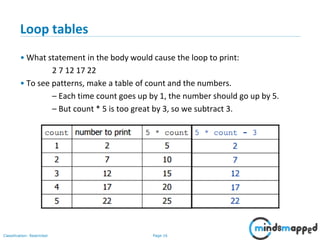
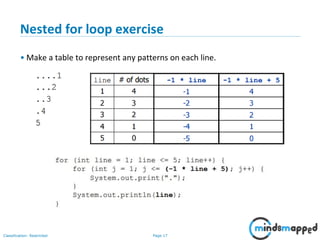
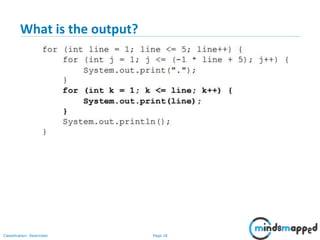
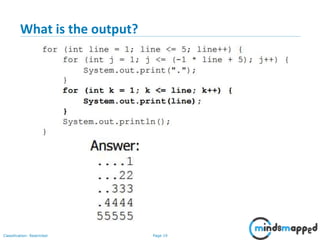
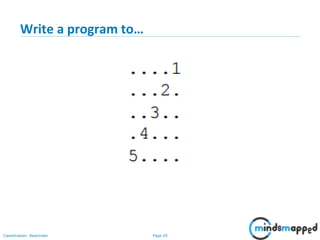
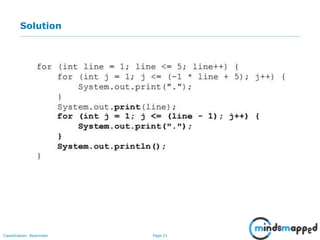
The document outlines the agenda for a Java and JEE training session focused on practice problems and object-oriented programming concepts. It includes exercises on nested for loops, generating complex outputs, and mapping loops to numbers. The session emphasizes understanding loops through practical examples and is set to cover additional topics in the next session.