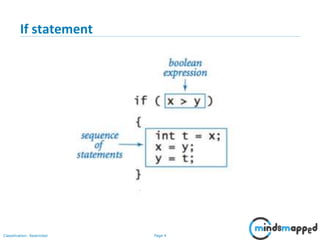
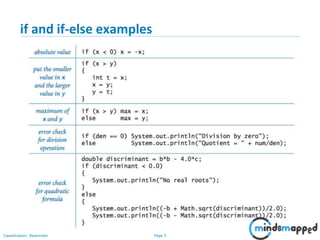
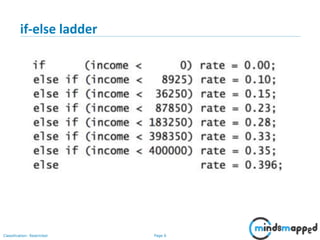
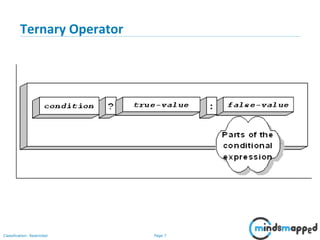
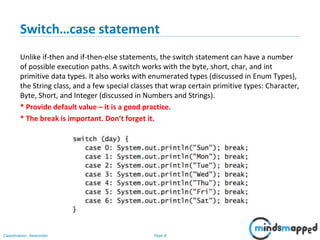
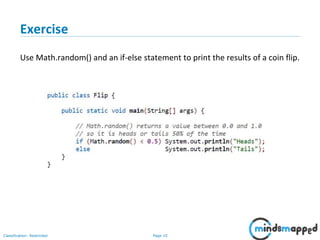
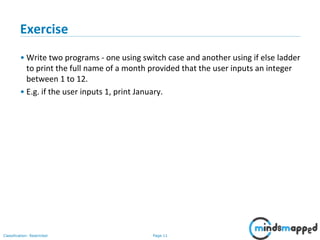
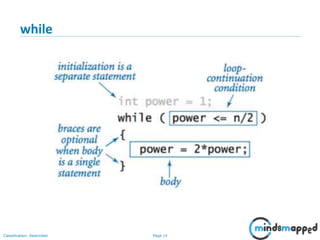
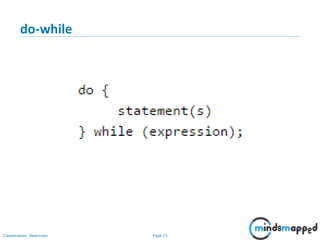
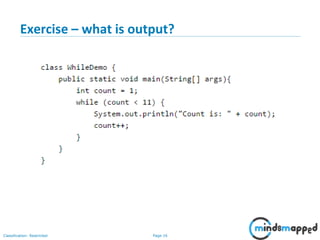
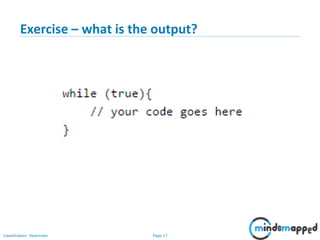
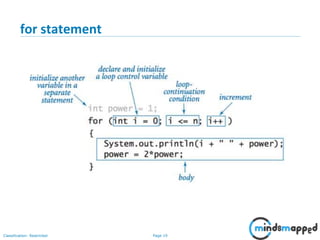
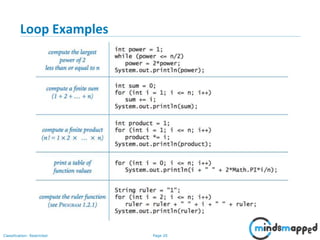
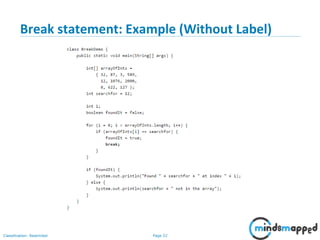
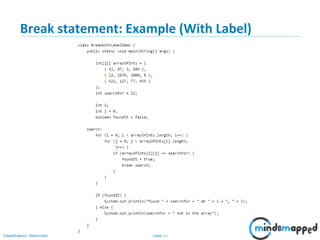
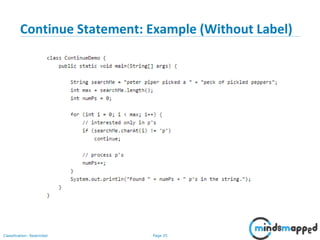
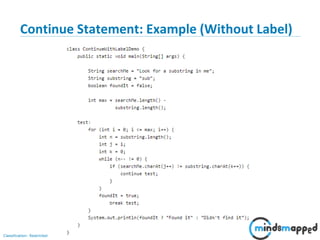
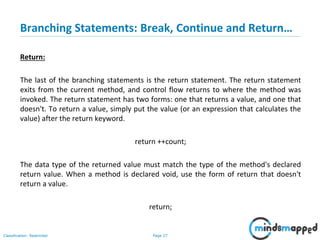
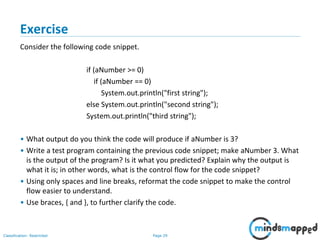
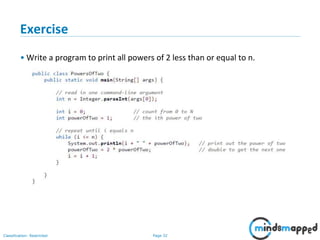
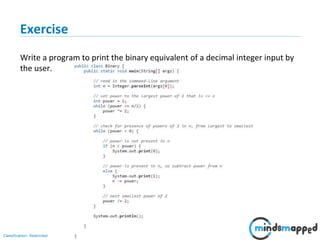
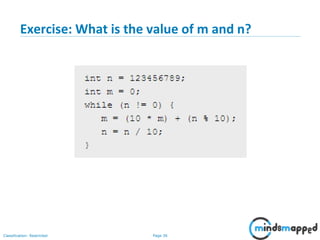
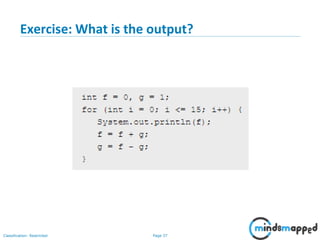
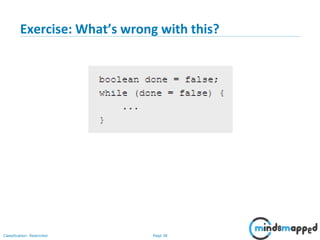
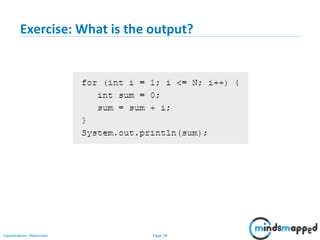
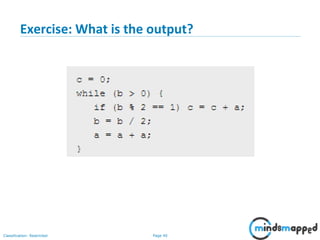
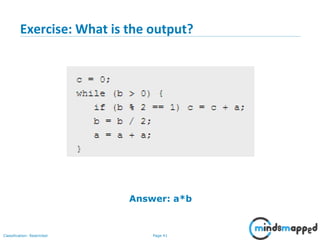
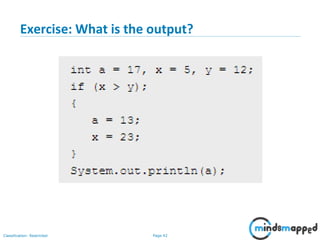
This document is a training session focused on Java programming elements, covering conditional statements, loops, and branching statements. It includes explanations and examples of if statements, switch-case structures, while loops, for loops, and the use of break and continue statements. Exercises are provided to reinforce learning, with plans for future topics such as autoboxing and handling arrays.