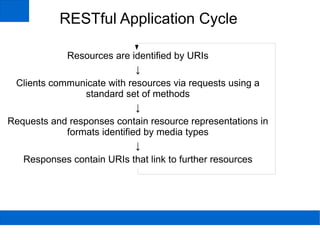
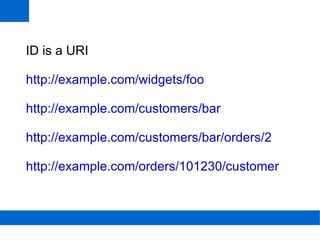
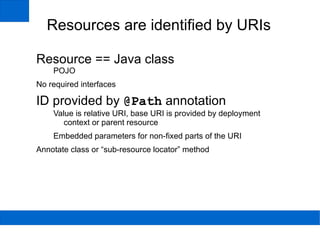
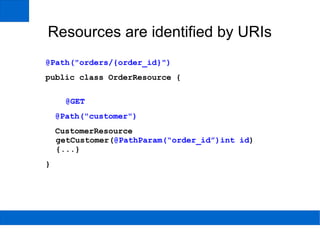
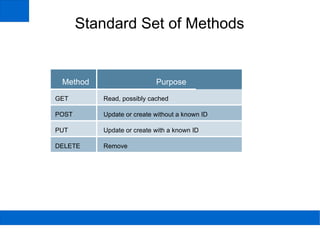
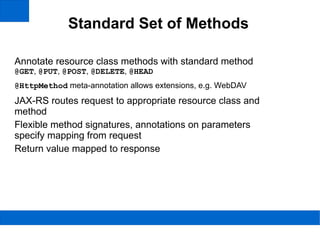
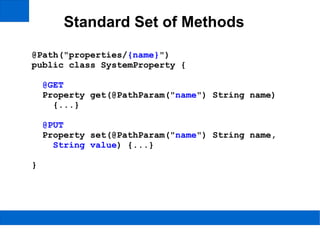
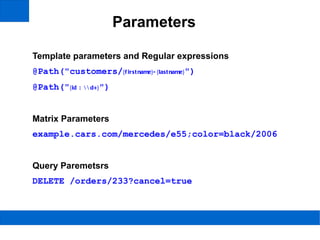
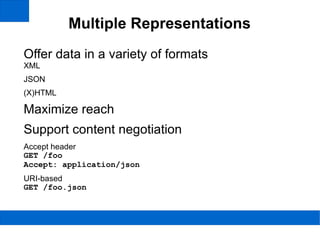
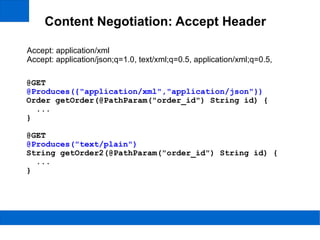
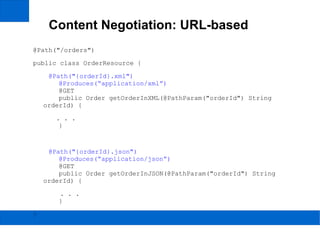
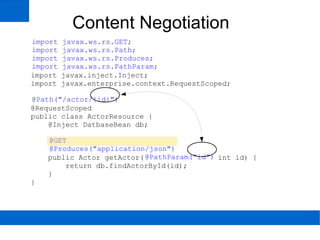
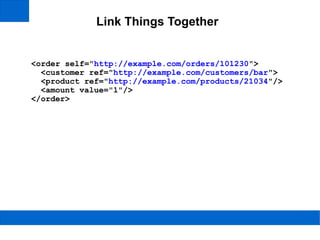
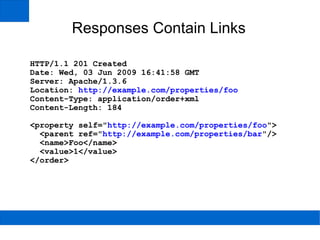
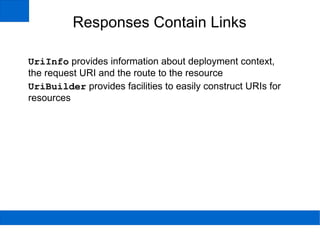
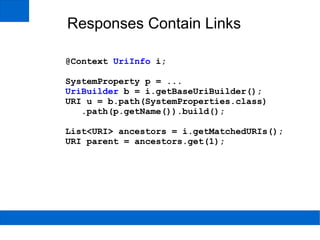
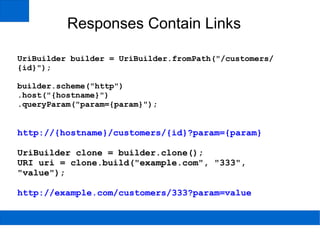
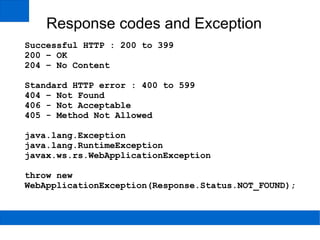
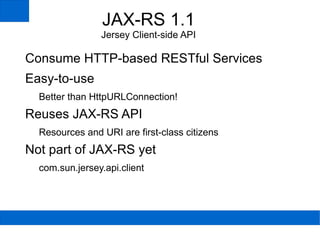
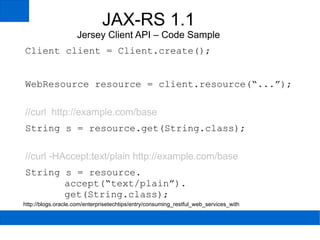
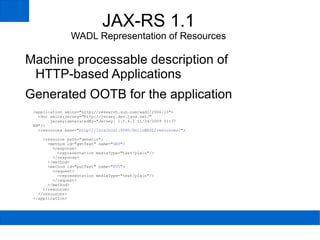
The document discusses developing RESTful web services using JAX-RS. It describes how JAX-RS allows identifying resources with URIs, communicating with standard HTTP methods, supporting multiple representations through content negotiation, and linking resources together through embedded URIs. Resources are represented as Java POJO classes annotated with JAX-RS annotations.