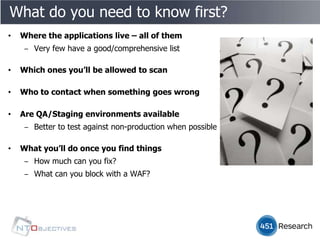
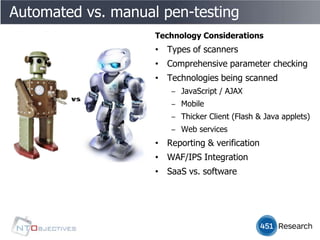
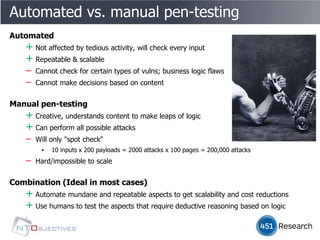
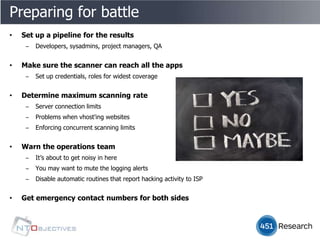
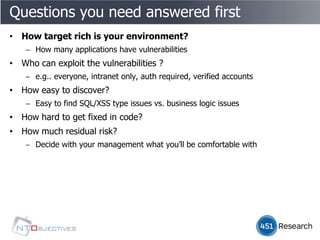
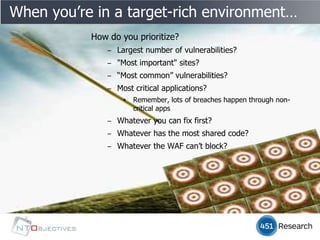
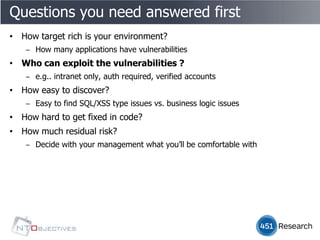
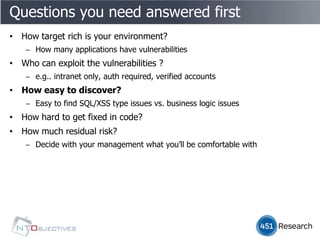
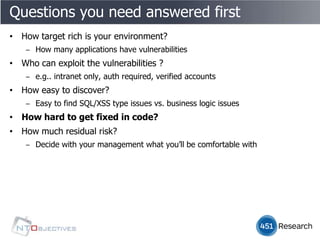
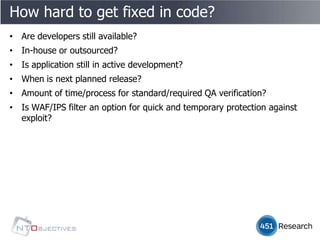
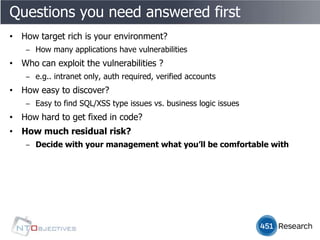
The document discusses the urgency of securing applications, especially when time is limited for audits or assessments. It emphasizes the need for a comprehensive understanding of the applications, the importance of both automated and manual penetration testing, and the challenges posed by various vulnerabilities. Additionally, it outlines the preparation required for effective vulnerability scanning and the necessity of communication among teams involved in application security.