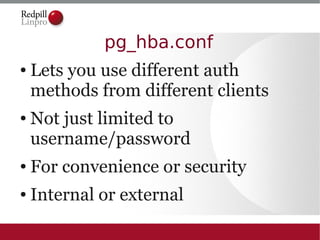
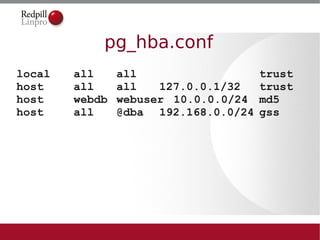
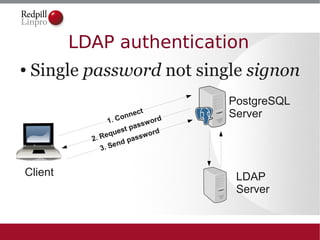
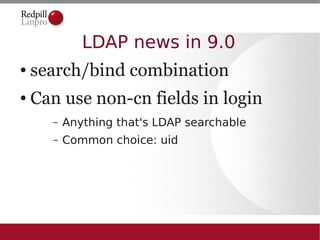
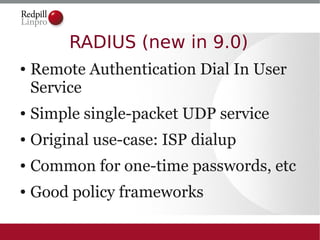
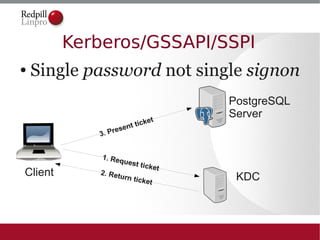
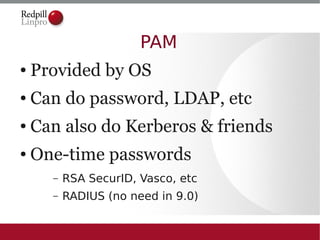
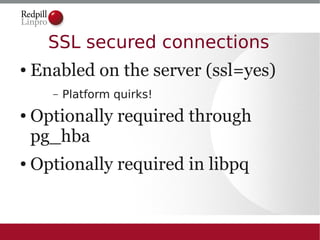
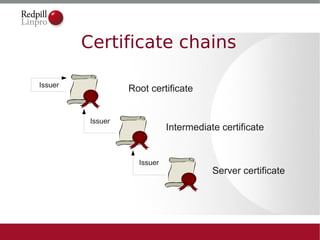
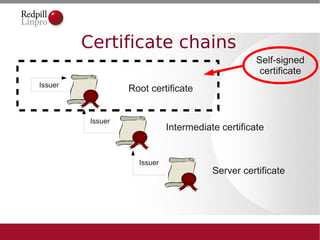
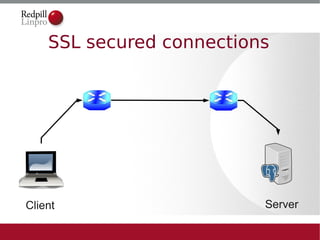
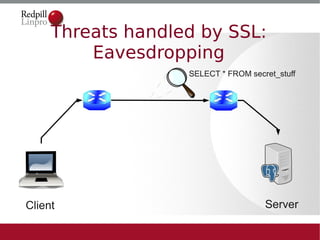
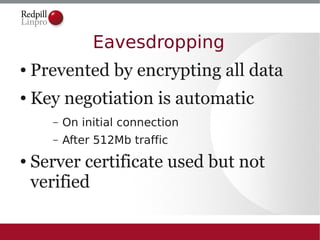
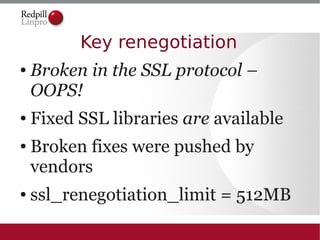
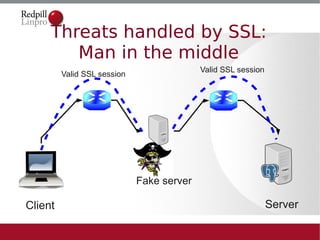
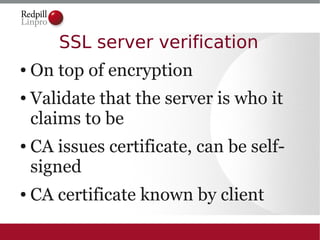
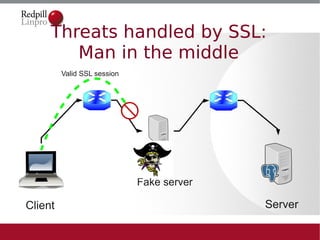
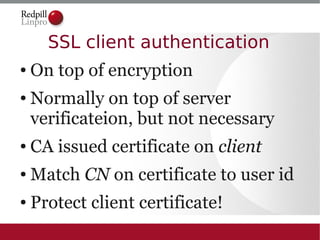
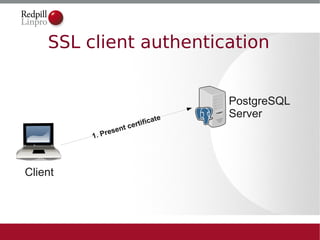
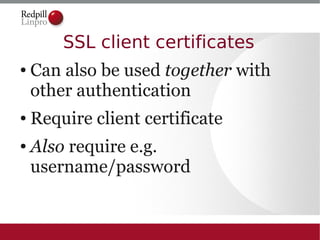
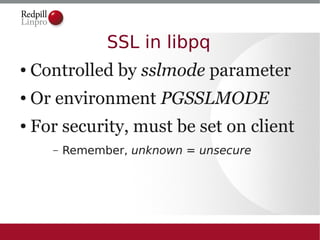
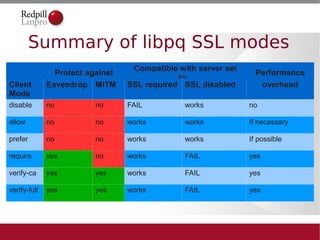
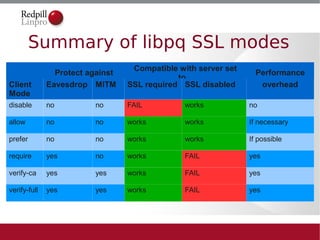
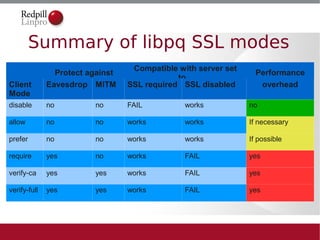
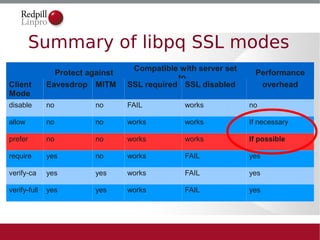
The document discusses secure PostgreSQL deployments, focusing on various security measures such as authentication methods, connection security, and data encryption. Key topics include the use of pg_hba.conf for authentication configuration, various authentication methods like LDAP and Kerberos, and the importance of SSL for secure connections and data protection. The document emphasizes best practices and potential threats in securing PostgreSQL databases.