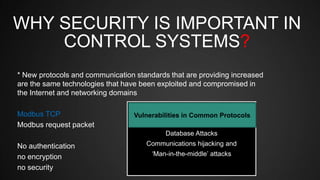
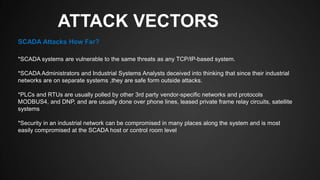
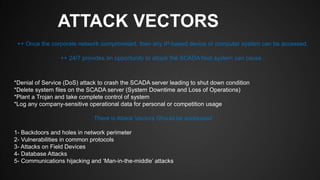
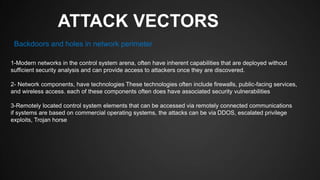
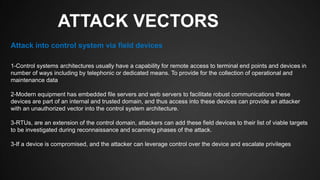
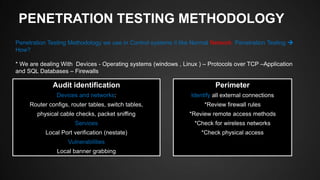
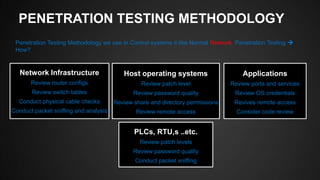
The document discusses SCADA (Supervisory Control and Data Acquisition) systems, detailing their purpose, benefits, communication methods, protocols, and the importance of cybersecurity. It outlines various types of SCADA networks, attack vectors, and penetration testing methodologies designed to identify vulnerabilities in these systems. Finally, it emphasizes the necessity of implementing security measures and policies to protect SCADA networks from potential cyber threats.














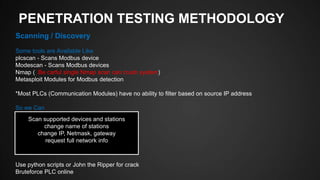


![PENETRATION TESTING METHODOLOGY
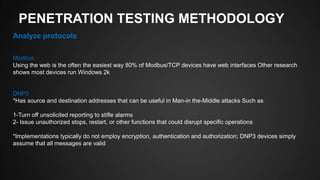
Data Manipulation
Available Tools
Web Application Test and SQL Injection
*As Scada Use Web application On HMI and SQL in Database we can test them for possible Vulnerabilities
Modlib - Scapy extention [python]
OpenDNP3 - Library [C++]
Metasploit Modules](https://image.slidesharecdn.com/penetrationtestingascadaindustrialcontrolsystems-141229233134-conversion-gate02/85/Scada-Industrial-Control-Systems-Penetration-Testing-36-320.jpg)