The document provides detailed instructions for enabling various features and functionalities on Mellanox network adapters, including SR-IOV, RoCEv2, hardware offloads, and integration with Open vSwitch, across multiple hardware models like ConnectX-4 and XL710. It includes command-line steps for configuring the system, installing necessary software packages, and verifying configurations. Overall, the document serves as a comprehensive guide for networking professionals to optimize Mellanox adapters for enhanced performance and capabilities.
![Enable SR-IOV TIPS (Melalnox ConnectX-4 EN)
2
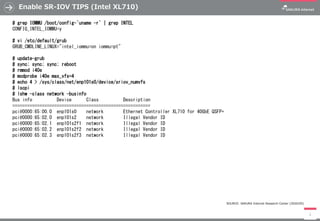
# grep IOMMU /boot/config-`uname -r` | grep INTEL
CONFIG_INTEL_IOMMU=y
# vi /etc/default/grub
GRUB_CMDLINE_LINUX="intel_iommu=on iommu=pt"
# update-grub
# cd /opt
# tar xzvf ./mlnx-en-4.4-2.0.7.0-ubuntu16.04-x86_64.tgz
# cd mlnx-en-4.4-2.0.7.0-ubuntu16.04-x86_64
# ./install
# cd /opt
# tar xzvf ./mft-4.10.0-104-x86_64-deb.tgz
# cd mft-4.10.0-104-x86_64-deb
# ./install.sh
# mst start
# mst status
# mlxconfig -d /dev/mst/mt4115_pciconf0 set SRIOV_EN=1 NUM_OF_VFS=4
# sync; sync; sync; reboot
# echo 4 > /sys/class/net/enp101s0/device/sriov_numvfs
# dmesg | grep IOMMU
# mlxconfig -d /dev/mst/mt4115_pciconf0 q
# lspci -D | grep Mellanox
# lshw -class network -businfo
Bus info Device Class Description
========================================================
pci@0000:65:00.0 enp101s0 network MT27700 Family [ConnectX-4]
pci@0000:65:00.1 enp101s0f1 network Illegal Vendor ID
pci@0000:65:00.2 enp101s0f2 network Illegal Vendor ID
pci@0000:65:00.3 enp101s0f3 network Illegal Vendor ID
pci@0000:65:00.4 enp101s0f4 network Illegal Vendor ID
SOURCE: SAKURA Internet Research Center (2020/05)](https://image.slidesharecdn.com/src20200506-ev1-200506140325/85/Network-Adapter-Deep-dive-2-320.jpg)
![Enable FD.io VPP TIPS (Intel XL710)
7
# update-grub
# apt remove --purge vpp*
# vi /etc/apt/sources.list.d/99fd.io.list
deb [trusted=yes] https://nexus.fd.io/content/repositories/fd.io.stable.1807.ubuntu.xenial.main/ ./
# apt update
# apt dist-upgrade -y
# apt install -y vpp vpp-lib vpp-plugins vpp-dpdk-dkms
# lshw -class network -businfo
# ifconfig enp101s0 down
# vi /etc/vpp/startup.conf
dpdk {
dev 0000:65:00.0
}
# service vpp restart
# vppctl show pci
Address Sock VID:PID Link Speed Driver Product Name
0000:65:00.0 0 8086:1584 8.0 GT/s x8 uio_pci_generic XL710 40GbE
# vppctl set int ip address FortyGigabitEthernet65/0/0 1.2.3.4/24
# vppctl set int state FortyGigabitEthernet65/0/0 up
# vppctl show interface addr
FortyGigabitEthernet65/0/0 (up):
L3 1.2.3.4/24
local0 (dn):
# vppctl show version
vpp v18.07-rc2~6-gdb6d6b3~b28 built by root on 10268b67c8b1 ...
SOURCE: SAKURA Internet Research Center (2020/05)](https://image.slidesharecdn.com/src20200506-ev1-200506140325/85/Network-Adapter-Deep-dive-7-320.jpg)
![Enable L4LB eBDF/XDP H/W Offload TIPS (Agilio CX SmartNIC)
8
# wget http://kernel.ubuntu.com/~kernel-ppa/mainline/v4.19-rc3/linux-headers-4.19.0-041900rc3...201809120832_all.deb
# wget http://kernel.ubuntu.com/~kernel-ppa/mainline/v4.19-rc3/linux-headers-4.19.0-041900rc3...201809120832_amd64.deb
# wget http://kernel.ubuntu.com/~kernel-ppa/mainline/v4.19-rc3/linux-modules-4.19.0-041900rc3...201809120832_amd64.deb
# wget http://kernel.ubuntu.com/~kernel-ppa/mainline/v4.19-rc3/linux-image-unsigned-4.19.0-041900rc3...20832_amd64.deb
# dpkg -i linux-headers-4.19.0-041900rc3_4.19.0-041900rc3.201809120832_all.deb
# dpkg -i linux-headers-4.19.0-041900rc3-generic_4.19.0-041900rc3.201809120832_amd64.deb
# dpkg -i linux-modules-4.19.0-041900rc3-generic_4.19.0-041900rc3.201809120832_amd64.deb
# dpkg -i linux-image-unsigned-4.19.0-041900rc3-generic_4.19.0-041900rc3.201809120832_amd64.deb
# sync; sync; sync; reboot
# dpkg -i agilio-bpf-firmware-2.0.6.121-1.deb
# dpkg -i bpftool-4.18_amd64.deb
# modprobe -r nfp; modprobe nfp
# ethtool -k enp101s0np0
# cd /opt; apt install elfutils libelf-dev libmnl-dev bison flex pkg-config
# git clone https://git.kernel.org/pub/scm/network/iproute2/iproute2-next.git
# cd iproute2-next; ./configure ; make; make install
# cd /opt; apt install -y clang llvm ; git clone https://github.com/Netronome/bpf-samples.git
# cd bpf-samples/l4lb/; make
# ip link set dev enp101s0np0 xdpoffload obj l4lb_xdp.o sec xdp
# bpftool prog show
12: xdp tag 803980e02b8beb36 dev enp101s0np0
loaded_at 2018-09-13T12:47:36+0900 uid 0
xlated 1784B jited 4024B memlock 4096B map_ids 12
# ./l4lb_map.py -i enp101s0np0 -f ./destination_samples/32_destinations.csv
# ./l4lb_stats.py -i enp101s0np0
== Load balancer outbound statistics [Offload] ==
1 10.0.0.57 0 pkts/s 0 bits/s
[Totals] 0 pkts/s 0 bits/s
SOURCE: SAKURA Internet Research Center (2020/05)](https://image.slidesharecdn.com/src20200506-ev1-200506140325/85/Network-Adapter-Deep-dive-8-320.jpg)