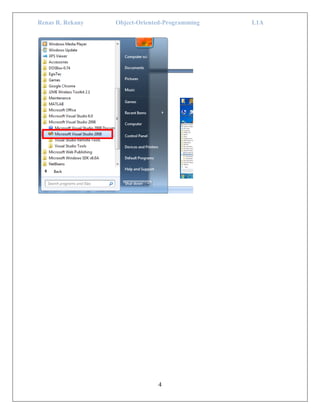
This document provides information about creating and running object-oriented programs in C# using Visual Studio. It discusses the .NET framework and different types of applications that can be created. It then provides step-by-step instructions on creating a simple Windows forms application with a button and message box, and a basic web application with a "Hello World" header. It also discusses opening and editing pages, building and running projects, and customizing project properties.




![Renas R. Rekany Object-Oriented-Programming L1A
7
In this designer view of the form (Form1.cs [Design]), you can design the user
interface of the single form. To do that, we use the 'Toolbox' which contains the
items that you can add to your form. Toolbox is placed on the left side of your
visual studio. If it is not visible go to View -> Toolbox to show the Toolbox.
Toolbox
It contains Labels, Buttons, Check Boxes, Combo Boxes and etc. This can be used
to design your interface. To add elements from the Toolbox to your form double
click the item or drag the item to your form.
Now add a Button Control to your form by simple dragging a Button control into
the form designer view. Finally it looks like below.
Now our form contains two elements. Those are form and the button control.
These elements have properties such as name, text, background color, fore color,](https://image.slidesharecdn.com/cp1-171231213454/85/C-p1-7-320.jpg)








