UK Gov Report Summary
•
0 likes•253 views
Company names mentioned herein are the property of, and may be trademarks of, their respective owners and are for educational purposes only.
Report
Share
Report
Share
Download to read offline
Recommended
Security Lock Down Your Computer Like the National Security Agency (NSA)

NSA has developed and distributed configuration guidance for operating systems. These guides are currently being used throughout the government and by numerous entities as a security baseline for their systems.
Overview of asp .net

A basic overview of asp .net and its applications, fetures and all other basic things.
Discover the 5 New Windows 8 Security Features You Should Know - by Denver IT...

Are there any security features in Windows 8 you should know about? Learn About the 5 New Windows 8 Security Features - Presented by your Denver IT Support Specialists and Technology Consultants at North Star, Inc.
Visit http://www.nssit.com
Presentation designed by Social Media Virtual Assistant: Andrea Kalli at www.virtualassist.net
Recommended
Security Lock Down Your Computer Like the National Security Agency (NSA)

NSA has developed and distributed configuration guidance for operating systems. These guides are currently being used throughout the government and by numerous entities as a security baseline for their systems.
Overview of asp .net

A basic overview of asp .net and its applications, fetures and all other basic things.
Discover the 5 New Windows 8 Security Features You Should Know - by Denver IT...

Are there any security features in Windows 8 you should know about? Learn About the 5 New Windows 8 Security Features - Presented by your Denver IT Support Specialists and Technology Consultants at North Star, Inc.
Visit http://www.nssit.com
Presentation designed by Social Media Virtual Assistant: Andrea Kalli at www.virtualassist.net
December Patch Tuesday 2020

For all of you who have asked for a pause to Patch Tuesday, you did not get exactly what you wanted for Christmas, but close. December Patch Tuesday is the lightest of 2020. Only 58 unique CVEs were resolved, nine of which are rated as Critical. There is also one advisory (ADV200013), which provides guidance for addressing a spoofing vulnerability in DNS Resolver. There were no publicly disclosed or exploited vulnerabilities this month on the Microsoft side. Adobe released a couple of low severity updates for Adobe Reader for Android and Adobe Connect. The Adobe Reader release (APSB20-67) from December 3 resolved 14 vulnerabilities, four of which were Critical. This is the more urgent release from Adobe for the month. Adobe Flash had an update for December Patch Tuesday, but it did not include any resolved vulnerabilities.
Android Security

This presentation on Android Security was given for the course "Cryptography & Network Security" at the KU Leuven
Black Duck & IBM Present: Application Security in the Age of Open Source

Keeping applications secure, whether you're developing for internal use or for your customers, isn't easy. Today, applications are a mix of open source and custom code. Identifying and resolving security vulnerabilities in both requires the right tools and know-how. Black Duck and IBM are working together to help you keep your applications secure.
"Outsourcing Best Practices" Conference. Speaker Diploma 

Благодарность за участие в работе конференции "Оптимизация бизнес-процессов: лучшие практики"
Acotax Trademark Certificate

Свидетельство о регистрации наименования Acotax в качестве товарного знака (знака обслуживания)
Hojita evangelio domingo la sagrada familia c serie

COMUNIDAD PARROQUIAL NUESTRA SEÑORA DE LOS DOLORES
MISA DOMINICAL NIÑOS PARA LA PASTORAL NIÑOS
PEREIRA 27 DE DICIEMBRE DOMINGO LA SAGRADA FAMILIA
EVANGELIO SEGÚN SAN LUCAS 2, 41-52
- Los padres de Jesús lo encuentran en medio de los maestros -
PEREIRA – RISARALDA
COLOMBIA
2015
Typo3 Neos - Introduction - WebMardi - Lausanne

Présentation de CMS TYPO3 Neos dans le cadre des webmardi à Lausanne, le 3 février
Portfolio E. Keenan

Portfolio of various engineering projects and endeavors by Erica Keenan. Designed, built, and brought to life by yours truly.
More Related Content
What's hot
December Patch Tuesday 2020

For all of you who have asked for a pause to Patch Tuesday, you did not get exactly what you wanted for Christmas, but close. December Patch Tuesday is the lightest of 2020. Only 58 unique CVEs were resolved, nine of which are rated as Critical. There is also one advisory (ADV200013), which provides guidance for addressing a spoofing vulnerability in DNS Resolver. There were no publicly disclosed or exploited vulnerabilities this month on the Microsoft side. Adobe released a couple of low severity updates for Adobe Reader for Android and Adobe Connect. The Adobe Reader release (APSB20-67) from December 3 resolved 14 vulnerabilities, four of which were Critical. This is the more urgent release from Adobe for the month. Adobe Flash had an update for December Patch Tuesday, but it did not include any resolved vulnerabilities.
Android Security

This presentation on Android Security was given for the course "Cryptography & Network Security" at the KU Leuven
Black Duck & IBM Present: Application Security in the Age of Open Source

Keeping applications secure, whether you're developing for internal use or for your customers, isn't easy. Today, applications are a mix of open source and custom code. Identifying and resolving security vulnerabilities in both requires the right tools and know-how. Black Duck and IBM are working together to help you keep your applications secure.
What's hot (9)
PR21-Preventing-File-Based-Botnet-Growth-and-Persistence-ARMOUR

PR21-Preventing-File-Based-Botnet-Growth-and-Persistence-ARMOUR
G. Gritsai, A. Timorin, Y. Goltsev, R. Ilin, S. Gordeychik, and A. Karpin, “S...

G. Gritsai, A. Timorin, Y. Goltsev, R. Ilin, S. Gordeychik, and A. Karpin, “S...
Black Duck & IBM Present: Application Security in the Age of Open Source

Black Duck & IBM Present: Application Security in the Age of Open Source
Viewers also liked
"Outsourcing Best Practices" Conference. Speaker Diploma 

Благодарность за участие в работе конференции "Оптимизация бизнес-процессов: лучшие практики"
Acotax Trademark Certificate

Свидетельство о регистрации наименования Acotax в качестве товарного знака (знака обслуживания)
Hojita evangelio domingo la sagrada familia c serie

COMUNIDAD PARROQUIAL NUESTRA SEÑORA DE LOS DOLORES
MISA DOMINICAL NIÑOS PARA LA PASTORAL NIÑOS
PEREIRA 27 DE DICIEMBRE DOMINGO LA SAGRADA FAMILIA
EVANGELIO SEGÚN SAN LUCAS 2, 41-52
- Los padres de Jesús lo encuentran en medio de los maestros -
PEREIRA – RISARALDA
COLOMBIA
2015
Typo3 Neos - Introduction - WebMardi - Lausanne

Présentation de CMS TYPO3 Neos dans le cadre des webmardi à Lausanne, le 3 février
Portfolio E. Keenan

Portfolio of various engineering projects and endeavors by Erica Keenan. Designed, built, and brought to life by yours truly.
Ley de Contrataciones Públicas

Ley de Contrataciones Públicas vigente en Venezuela desde noviembre de 2014. esta ley rige los procedimientos de contrataciones por parte del sector publico.
Viewers also liked (17)
"Outsourcing Best Practices" Conference. Speaker Diploma 

"Outsourcing Best Practices" Conference. Speaker Diploma
Hojita evangelio domingo la sagrada familia c serie

Hojita evangelio domingo la sagrada familia c serie
Moving bed biofilm reactor for denitrification corey

Moving bed biofilm reactor for denitrification corey
Similar to UK Gov Report Summary
How BlackBerry Brings Android Security To Your Enterprise: White Paper

When Android first made its way into the consumer market, no one could have predicted the impact it would have. Android was an operating system developed with a simple idea at its core: Google’s founders wanted smarter mobile devices that better served their users. Today, that simple idea has helped make Android the most popular mobile OS on the market, with a global share of 66%.
Android’s popularity can largely be traced to its sheer diversity. Almost from the beginning, it has been an open platform, and there are countless devices from countless manufacturers that users can choose between. Therein lies the problem – due to its widespread popularity, Android finds itself targeted by criminals and malware with greater frequency than any other operating system. This means that although the OS is not inherently vulnerable, any vulnerabilities that do exist tend to be exploited if they aren’t patched in a timely fashion. Moreover, because so many different vendors count themselves as players in the Android space, it’s inevitable that some will lag behind with security patching. In the meantime, their devices will remain vulnerable, even as they’re being used to handle sensitive business data.
“Nearly every organization supporting smartphones and tablets must have a strategy to support Android devices, despite some of the security challenges,” reads a recent white paper by J. Gold Associates. “As we moved to a more mobile world over the past several years, the number of potential attack points increased dramatically, and many of them consisted of user-selected and often unsecured devices as a byproduct of BYOD,” the paper continues. “The ability to secure data and prevent corporate breaches consistently ranks among the top issues both IT and general management struggle with on a regular basis. A February 2016 Ponemon Institute survey shows that 67% of companies are either certain or very likely to have had a security breach due to a mobile device.”
Slow security patching is far from the only threat facing Android within the enterprise. To grant themselves additional freedoms and run certain applications, many users choose to root their devices, stripping away core security functionality in the interest of personalization. And though measures such as Samsung KNOX and Android for Work exist to separate corporate and private data, these software solutions can be fooled by a savvy enough user.
That’s where BlackBerry comes in. Security has always been in our blood, and we’ve always made it our priority to protect both our clients and their data. That’s why we’ve made our own foray into the Android device market, bringing our full security expertise to bear.
Android Security Maximized by Samsung KNOX

Safeguard enterprise mobility with tightly integrated security, compliance, and control features.
CodeMotion tel aviv 2015 - burning marshmallows

Android Security model updates, and Android Security discussions [Description to be updated later]
Tres formas de modernizar la TI del dispositivo y mejorar la productividad

Un enfoque más moderno para comprar y administrar dispositivos de punto final puede reducir los costos de TI y soporte al tiempo que mejora la seguridad y la productividad.
La fuerza laboral de hoy necesita la flexibilidad para ser productiva desde cualquier lugar. Pero las políticas BYOD flexibles pueden crear dolores de cabeza para los equipos de TI empresariales. Los diferentes hardware y sistemas operativos dificultan la gestión y actualización coherentes de dispositivos y software, creando vulnerabilidades de seguridad que aumentan el riesgo de ciberataques. Reducir la complejidad y el riesgo requiere un nuevo enfoque para la administración de dispositivos.
Con este nuevo ebook, aprenderás:
• Cómo el lugar de trabajo moderno está creando desafíos modernos para los equipos de TI
• Las tres áreas más importantes en las que centrarse para "modernizarse": implementación, administración y seguridad
• Cómo construir un caso de negocio para la compra de dispositivos, más allá del precio
ENHANCED SOFTWARE DESIGN FOR BOOSTED CONTINUOUS SOFTWARE DELIVERY

Engineering efficiency in continuous software delivery can be impacted by multiple factors. In this paper, citing one ultra-large-scale software - Intel Media Driver as an example, we analyse the hotspots impacting the engineering efficiency in continuous software delivery, their challenges to our software design and the experiences on software delivery efficiency boost against the targeted design enhancements. We expect the identified hotspots can help more researchers to form the corresponding research agendas and the experiences shared can help following practitioners to apply similar enhanceme
LOUCA23 Yusuf Hadiwinata Linux Security BestPractice

LOUCA23 Yusuf Hadiwinata Linux Security BestPractice
Proving the Security of Low-Level Software Components & TEEs

Learn how it is possible to prove low-level software component and TEE security, as well as the Goodix driver example demoed in the webinar.
Check out the webinar replay here: https://www.youtube.com/watch?v=nG3DlejBd3k
Visit our website trust-in-soft.com for more information!
The Challenge of Integrating Security Solutions with CI.pdf

Informational article which will discuss the issues with code signing solutions as they relate to ci/cd workflows (including DIY and HSM solutions).
Targeted Persona: mostly technical decision makers and operational champions (devops/devsecops).
CoreTrace Whitepaper: Application Whitelisting And Energy Systems

Whitepaper Abstract
This white paper explains why application whitelisting is being rapidly adopted as a security and control solution for SCADA systems.
In three major sections, the paper:
Provides a detailed perspective on how application whitelisting technology works.
Discusses the use and benefits of whitelisting technologies in SCADA and Energy environments.
Explains how the technology is adapting to function in environments where controlled software changes are needed.
Implementing a Security strategy in IoT, Practical example Automotive Grade L...

Dominig ar Foll, Intel
Similar to UK Gov Report Summary (20)
How BlackBerry Brings Android Security To Your Enterprise: White Paper

How BlackBerry Brings Android Security To Your Enterprise: White Paper
Tres formas de modernizar la TI del dispositivo y mejorar la productividad

Tres formas de modernizar la TI del dispositivo y mejorar la productividad
ENHANCED SOFTWARE DESIGN FOR BOOSTED CONTINUOUS SOFTWARE DELIVERY

ENHANCED SOFTWARE DESIGN FOR BOOSTED CONTINUOUS SOFTWARE DELIVERY
LOUCA23 Yusuf Hadiwinata Linux Security BestPractice

LOUCA23 Yusuf Hadiwinata Linux Security BestPractice
Proving the Security of Low-Level Software Components & TEEs

Proving the Security of Low-Level Software Components & TEEs
Discussing Windows® XP End of Support with Management: 5 Key Factors

Discussing Windows® XP End of Support with Management: 5 Key Factors
What Linux is what you should also have on your computer.

What Linux is what you should also have on your computer.
The Challenge of Integrating Security Solutions with CI.pdf

The Challenge of Integrating Security Solutions with CI.pdf
CoreTrace Whitepaper: Application Whitelisting And Energy Systems

CoreTrace Whitepaper: Application Whitelisting And Energy Systems
Implementing a Security strategy in IoT, Practical example Automotive Grade L...

Implementing a Security strategy in IoT, Practical example Automotive Grade L...
Auditing the Workstation Domain for Compliance.docx

Auditing the Workstation Domain for Compliance.docx
More from - Mark - Fullbright
ISTR Internet Security Threat Report 2019

This report solely belongs to Symantec. Credit is due to all original authors and no financial gain was made from the report, Simply sharing for educational purposes,
IC3 2019 Internet Crime Report

The FBI is the lead federal agency for investigating malicious cyber activity by criminals, nation-state adversaries, and terrorists. To fulfill this mission, the FBI often develops resources to enhance operations and collaboration. One such resource is the FBI’s Internet Crime Complaint Center (IC3) which provides the public with a trustworthy and convenient mechanism for reporting information concerning suspected Internet-facilitated criminal activity. At the end of every year, the IC3 collates information collected into an annual report.
Credit is due to all original authors and no financial gain was made from the blog, Simply sharing an interesting story for educational purposes,
Police, Protesters, Press, 2020

This guide aims to help journalists understand their rights at protests and avoid arrest when reporting on these events. It summarizes the legal landscape and provides strategies and tools to help journalists avoid incidents with police and navigate them successfully should they arise. Credit RCFP.Org
Credit is due to all original authors and no financial gain was made from the blog, Simply sharing an interesting story for educational purposes,
2020 Data Breach Investigations Report (DBIR)

Verizon Publishes 2020 Data Breach Investigation Report (DBIR) With Insights From Thousands of Confirmed Breaches. Verizon's 2020 Data Breach Investigations Report (DBIR) is the most extensive yet, with 81 contributing organizations, and more than 32,000 incidents analyzed (of which 3,950 were confirmed breaches). Credit:Verizon
Credit is due to all original authors and no financial gain was made from the report, Simply sharing an interesting story for educational purposes,
FCPA Guidance 2020

A Resource Guide to theU.S. Foreign Corrupt Practices Act
Credit is due to all original authors and no financial gain was made from the report, Simply sharing an interesting story for educational purposes,
Consumer Sentinel Network Data Book 2019

The FTC takes in reports from consumers about problems they experience in the marketplace. The reportsare stored in the Consumer Sentinel Network (Sentinel), a secure online database available only to lawenforcement. While the FTC does not intervene in individual consumer disputes, its law enforcementpartners – whether they are down the street, across the nation, or around the world – can use informationin the database to spot trends, identify questionable business practices and targets, and enforce the law.
Credit is due to all original authors and no financial gain was made from the report, Simply sharing an interesting story for educational purposes,
CFPB Consumer Reporting Companies 2019

Below is a list of consumer reporting companies updated for 2019.1 Consumer reporting companies collect information and provide reports to other companies about you. These companies use these reports to inform decisions about providing you with credit, employment, residential rental housing, insurance, and in other decision making situations. The list below includes the three nationwide consumer reporting companies and several other reporting companies that focus on certain market areas and consumer segments. The list gives you tips so you can determine which of these companies may be important to you. It also makes it easier for you to take advantage of your legal rights to (1) obtain the information in your consumer reports, and (2) dispute suspected inaccuracies in your reports with companies as needed.
Advisory to Financial Institutions on Illicit Financial Schemes and Methods R...

Transnational criminal organizations (TCOs), foreign fentanyl suppliers, and Internet purchasers located in the United States engage in the trafficking of fentanyl, fentanyl analogues, and other synthetic opioids and the subsequent laundering of the proceeds from such illegal sales.
2018 IC3 Report

The mission of the IC3 is to provide the public with a reliable and convenient reporting mechanism to submit information to the FBI concerning suspected Internet-facilitated criminal activity, and to develop effective alliances with industry partners. Information is analyzed and disseminated for investigative and intelligence purposes, for law enforcement, and for public awareness.
Credit is due to all original authors and no financial gain was made from the report, Simply sharing an interesting story for educational purposes,
2019 Data Breach Investigations Report (DBIR)

This report is built upon analysis of 41,686 security incidents, of which 2,013 were confirmed data breaches. We will take a look at how results are changing (or not) over the years as well as digging into the overall threat landscape and the actors, actions, and assets that are present in breaches. Windows into the most common pairs of threat actions and affected assets also are provided.
2018 Privacy & Data Security Report

The Federal Trade Commission (FTC or Commission) is an independent U.S. law enforcement agency charged with protecting consumers and enhancing competition across broad sectors of the economy. The FTC’s primary legal authority comes from Section 5 of the Federal Trade Commission Act, which prohibits unfair or deceptive practices in the marketplace. The FTC also has authority to enforce a variety of sector specific laws, including the Truth in Lending Act, the CAN-SPAM Act, the Children’s Online Privacy Protection Act, the Equal Credit Opportunity Act, the Fair Credit Reporting Act, the Fair Debt Collection Practices Act, and the Telemarketing and Consumer Fraud and Abuse Prevention Act. This broad authority allows the Commission
to address a wide array of practices affecting consumers, including those that emerge with the development of new technologies and business models.
Consumer Sentinel Network Data Book 2018 

Sentinel sorts consumer reports into 29 top categories. Appendices B1 – B3 describe the categories,providing details, and three year figures. To reflect marketplace changes, new categories or subcategories are created or deleted over time.The Consumer Sentinel Network Data Book excludes the National Do Not Call Registry. A separate report about these complaint statistics is available at: https://www.ftc.gov/reports/national-do-not-call-registry-data-book-fiscal-year-2018. The Sentinel Data Book also excludes reports about unsolicited commercial email.Consumers can report as much or as little detail as they wish when they file a report. For the Sentinel Data Book graphics, percentages are based on the total number of Sentinel fraud, identity theft, and other report types in 2018 in which consumers provided the information displayed on each chart.Reports to Sentinel sometimes indicate money was lost, and sometimes indicate no money was lost.Often, people make these reports after they experience something problematic in the marketplace,avoid losing any money, and wish to alert others. Except where otherwise stated, numbers are based on reports both from people who indicated a loss and people who did not.Calculations of dollar amounts lost are based on reports in which consumers indicated they lost between $1 and $999,999. Prior to 2017, reported “amount paid” included values of $0 to $999,999.States and Metropolitan Areas are ranked based on the number of reports per 100,000 population.State rankings are based on 2017 U.S. Census population estimates (Annual Estimates of the Resident Population: April 1, 2010 to July 1, 2017). Metropolitan Area rankings are based on 2016 U.S. Census population estimates (Annual Estimates of the Resident Population: April 1, 2010 to July 1, 2016).This Sentinel Data Book identifies Metropolitan Areas (Metropolitan and Micropolitan Statistical Areas)with a population of 100,000 or more except where otherwise noted. Metropolitan areas are defined by Office of Management and Budget Bulletin No. 15-01, “Revised Delineations of Metropolitan Statistical Areas, Micropolitan Statistical Areas, and Combined Statistical Areas, and Guidance on Uses of the Delineations of These Areas” (July 15, 2015). Numbers change over time. The Sentinel Data Book sorts consumer reports by year, based on the date of the consumer’s report. Some data contributors transfer their complaints to Sentinel after the end of the calendar year, and new data providers often contribute reports from prior years. As a result, the total number of reports for 2018 will likely change during the next few months, and totals from previous years may differ from prior Consumer Sentinel Network Data Books. The most up to date information can be found online at ftc.gov/data
Credit Score Explainer

A credit score is a three -digit number that predicts how likely you are to pay back a loan on time, based on information from your credit reports.
Company names mentioned herein are the property of, and may be trademarks of, their respective owners and are for educational purposes only.
The Geography of Medical Identity Theft

Company names mentioned herein are the property of, and may be trademarks of, their respective owners and are for educational purposes only. - Medical identity theft has existed in various forms for decades, but it was in 2006 that World Privacy Forum published the first major report about the crime. The report called for medical data breach notification laws and more research about medical identity theft and its impacts. Since that time, medical data breach notification laws have been enacted, and other progress has been made, particularly in the quality of consumer complaint datasets gathered around identity theft, including medical forms of the crime. This report uses new data arising from consumer medical identity theft complaint reporting and medical data breach reporting to analyze and document the geography of medical identity theft and its growth patterns. The report also discusses new aspects of consumer harm resulting from the crime that the data has brought to light
Consumer Sentinel Data Book 2017

The FTC takes in reports from consumers about problems they experience in the marketplace. The reports are stored in the Consumer Sentinel Network (Sentinel), a secure online database available only to law enforcement. While the FTC does not intervene in individual consumer disputes, its law enforcement partners – whether they are down the street, across the nation, or around the world – can use information in the database to spot trends, identify questionable business practices and targets, and enforce the law.
Since 1997, Sentinel has collected tens of millions of reports from consumers about fraud, identity theft, and other consumer protection topics. During 2017, Sentinel received nearly 2.7 million consumer reports, which the FTC has sorted into 30 top categories. The 2017 Consumer Sentinel Network Data Book (Sentinel Data Book) has a vibrant new look, and a lot more information about what consumers told us last year. You'll know more about how much money people lost in the aggregate, the median amount they paid, and what frauds were most costly. And you'll know much more about complaints of identity theft, fraud, and other types of problems in each state, too. The Sentinel Data Book is based on unverified reports filed by consumers. The data is not based on a consumer survey. Sentinel has a five-year data retention policy, with reports older than five years purged biannually.
Protecting Personal Information: A Guide for Business

*Company names mentioned herein are the property of, and may be trademarks of, their respective owners and are for educational purposes only.
Data Breach Response: A Guide for Business

This guide addresses the steps to take once a
breach has occured. For advice on implementing a
plan to protect consumers’ personal information, to
prevent breaches and unauthorized access, check
out the FTC’s Protecting Personal Information: A
Guide for Business and Start with Security: A Guide
for Business.
*Company names mentioned herein are the property of, and may be trademarks of, their respective owners and are for educational purposes only.
2017 Data Breach Investigations Report

Company names mentioned herein are the property of, and may be trademarks of, their respective owners and are for educational purposes only.
Consumer Sentinel Network Data Book for January 2016 - December 2016

FTC Consumer Sentinel Network Law enforcement's source for consumer complaints.
All information, data, and material contained, presented, or provided on is for educational purposes only.
Company names mentioned herein are the property of, and may be trademarks of, their respective owners.
It is not to be construed or intended as providing legal advice.
Consumer Sentinel Data Book 2015

Company names mentioned herein are the property of, and may be trademarks of, their respective owners.
More from - Mark - Fullbright (20)
Advisory to Financial Institutions on Illicit Financial Schemes and Methods R...

Advisory to Financial Institutions on Illicit Financial Schemes and Methods R...
Protecting Personal Information: A Guide for Business

Protecting Personal Information: A Guide for Business
Consumer Sentinel Network Data Book for January 2016 - December 2016

Consumer Sentinel Network Data Book for January 2016 - December 2016
Recently uploaded
Acetabularia Information For Class 9 .docx

Acetabularia acetabulum is a single-celled green alga that in its vegetative state is morphologically differentiated into a basal rhizoid and an axially elongated stalk, which bears whorls of branching hairs. The single diploid nucleus resides in the rhizoid.
The French Revolution Class 9 Study Material pdf free download

The French Revolution, which began in 1789, was a period of radical social and political upheaval in France. It marked the decline of absolute monarchies, the rise of secular and democratic republics, and the eventual rise of Napoleon Bonaparte. This revolutionary period is crucial in understanding the transition from feudalism to modernity in Europe.
For more information, visit-www.vavaclasses.com
TESDA TM1 REVIEWER FOR NATIONAL ASSESSMENT WRITTEN AND ORAL QUESTIONS WITH A...

TESDA TM1 REVIEWER FOR NATIONAL ASSESSMENT WRITTEN AND ORAL QUESTIONS WITH ANSWERS.
The approach at University of Liverpool.pptx

How libraries can support authors with open access requirements for UKRI funded books
Wednesday 22 May 2024, 14:00-15:00.
Biological Screening of Herbal Drugs in detailed.

Biological screening of herbal drugs: Introduction and Need for
Phyto-Pharmacological Screening, New Strategies for evaluating
Natural Products, In vitro evaluation techniques for Antioxidants, Antimicrobial and Anticancer drugs. In vivo evaluation techniques
for Anti-inflammatory, Antiulcer, Anticancer, Wound healing, Antidiabetic, Hepatoprotective, Cardio protective, Diuretics and
Antifertility, Toxicity studies as per OECD guidelines
Embracing GenAI - A Strategic Imperative

Artificial Intelligence (AI) technologies such as Generative AI, Image Generators and Large Language Models have had a dramatic impact on teaching, learning and assessment over the past 18 months. The most immediate threat AI posed was to Academic Integrity with Higher Education Institutes (HEIs) focusing their efforts on combating the use of GenAI in assessment. Guidelines were developed for staff and students, policies put in place too. Innovative educators have forged paths in the use of Generative AI for teaching, learning and assessments leading to pockets of transformation springing up across HEIs, often with little or no top-down guidance, support or direction.
This Gasta posits a strategic approach to integrating AI into HEIs to prepare staff, students and the curriculum for an evolving world and workplace. We will highlight the advantages of working with these technologies beyond the realm of teaching, learning and assessment by considering prompt engineering skills, industry impact, curriculum changes, and the need for staff upskilling. In contrast, not engaging strategically with Generative AI poses risks, including falling behind peers, missed opportunities and failing to ensure our graduates remain employable. The rapid evolution of AI technologies necessitates a proactive and strategic approach if we are to remain relevant.
Thesis Statement for students diagnonsed withADHD.ppt

Presentation required for the master in Education.
Chapter 3 - Islamic Banking Products and Services.pptx

Chapter 3 - Islamic Banking Products and Services.pptxMohd Adib Abd Muin, Senior Lecturer at Universiti Utara Malaysia
This slide is prepared for master's students (MIFB & MIBS) UUM. May it be useful to all.BÀI TẬP BỔ TRỢ TIẾNG ANH GLOBAL SUCCESS LỚP 3 - CẢ NĂM (CÓ FILE NGHE VÀ ĐÁP Á...

BÀI TẬP BỔ TRỢ TIẾNG ANH GLOBAL SUCCESS LỚP 3 - CẢ NĂM (CÓ FILE NGHE VÀ ĐÁP Á...Nguyen Thanh Tu Collection
https://app.box.com/s/hqnndn05v4q5a4k4jd597rkdbda0fnii1.4 modern child centered education - mahatma gandhi-2.pptx

Child centred education is an educational approach that priorities the interest, needs and abilities of the child in the learning process.
"Protectable subject matters, Protection in biotechnology, Protection of othe...

Protectable subject matters, Protection in biotechnology, Protection of other biological materials, Ownership and period of protection
The Challenger.pdf DNHS Official Publication

Read| The latest issue of The Challenger is here! We are thrilled to announce that our school paper has qualified for the NATIONAL SCHOOLS PRESS CONFERENCE (NSPC) 2024. Thank you for your unwavering support and trust. Dive into the stories that made us stand out!
Unit 2- Research Aptitude (UGC NET Paper I).pdf

This slide describes the research aptitude of unit 2 in the UGC NET paper I.
A Strategic Approach: GenAI in Education

Artificial Intelligence (AI) technologies such as Generative AI, Image Generators and Large Language Models have had a dramatic impact on teaching, learning and assessment over the past 18 months. The most immediate threat AI posed was to Academic Integrity with Higher Education Institutes (HEIs) focusing their efforts on combating the use of GenAI in assessment. Guidelines were developed for staff and students, policies put in place too. Innovative educators have forged paths in the use of Generative AI for teaching, learning and assessments leading to pockets of transformation springing up across HEIs, often with little or no top-down guidance, support or direction.
This Gasta posits a strategic approach to integrating AI into HEIs to prepare staff, students and the curriculum for an evolving world and workplace. We will highlight the advantages of working with these technologies beyond the realm of teaching, learning and assessment by considering prompt engineering skills, industry impact, curriculum changes, and the need for staff upskilling. In contrast, not engaging strategically with Generative AI poses risks, including falling behind peers, missed opportunities and failing to ensure our graduates remain employable. The rapid evolution of AI technologies necessitates a proactive and strategic approach if we are to remain relevant.
June 3, 2024 Anti-Semitism Letter Sent to MIT President Kornbluth and MIT Cor...

Letter from the Congress of the United States regarding Anti-Semitism sent June 3rd to MIT President Sally Kornbluth, MIT Corp Chair, Mark Gorenberg
Dear Dr. Kornbluth and Mr. Gorenberg,
The US House of Representatives is deeply concerned by ongoing and pervasive acts of antisemitic
harassment and intimidation at the Massachusetts Institute of Technology (MIT). Failing to act decisively to ensure a safe learning environment for all students would be a grave dereliction of your responsibilities as President of MIT and Chair of the MIT Corporation.
This Congress will not stand idly by and allow an environment hostile to Jewish students to persist. The House believes that your institution is in violation of Title VI of the Civil Rights Act, and the inability or
unwillingness to rectify this violation through action requires accountability.
Postsecondary education is a unique opportunity for students to learn and have their ideas and beliefs challenged. However, universities receiving hundreds of millions of federal funds annually have denied
students that opportunity and have been hijacked to become venues for the promotion of terrorism, antisemitic harassment and intimidation, unlawful encampments, and in some cases, assaults and riots.
The House of Representatives will not countenance the use of federal funds to indoctrinate students into hateful, antisemitic, anti-American supporters of terrorism. Investigations into campus antisemitism by the Committee on Education and the Workforce and the Committee on Ways and Means have been expanded into a Congress-wide probe across all relevant jurisdictions to address this national crisis. The undersigned Committees will conduct oversight into the use of federal funds at MIT and its learning environment under authorities granted to each Committee.
• The Committee on Education and the Workforce has been investigating your institution since December 7, 2023. The Committee has broad jurisdiction over postsecondary education, including its compliance with Title VI of the Civil Rights Act, campus safety concerns over disruptions to the learning environment, and the awarding of federal student aid under the Higher Education Act.
• The Committee on Oversight and Accountability is investigating the sources of funding and other support flowing to groups espousing pro-Hamas propaganda and engaged in antisemitic harassment and intimidation of students. The Committee on Oversight and Accountability is the principal oversight committee of the US House of Representatives and has broad authority to investigate “any matter” at “any time” under House Rule X.
• The Committee on Ways and Means has been investigating several universities since November 15, 2023, when the Committee held a hearing entitled From Ivory Towers to Dark Corners: Investigating the Nexus Between Antisemitism, Tax-Exempt Universities, and Terror Financing. The Committee followed the hearing with letters to those institutions on January 10, 202
The Roman Empire A Historical Colossus.pdf

The Roman Empire, a vast and enduring power, stands as one of history's most remarkable civilizations, leaving an indelible imprint on the world. It emerged from the Roman Republic, transitioning into an imperial powerhouse under the leadership of Augustus Caesar in 27 BCE. This transformation marked the beginning of an era defined by unprecedented territorial expansion, architectural marvels, and profound cultural influence.
The empire's roots lie in the city of Rome, founded, according to legend, by Romulus in 753 BCE. Over centuries, Rome evolved from a small settlement to a formidable republic, characterized by a complex political system with elected officials and checks on power. However, internal strife, class conflicts, and military ambitions paved the way for the end of the Republic. Julius Caesar’s dictatorship and subsequent assassination in 44 BCE created a power vacuum, leading to a civil war. Octavian, later Augustus, emerged victorious, heralding the Roman Empire’s birth.
Under Augustus, the empire experienced the Pax Romana, a 200-year period of relative peace and stability. Augustus reformed the military, established efficient administrative systems, and initiated grand construction projects. The empire's borders expanded, encompassing territories from Britain to Egypt and from Spain to the Euphrates. Roman legions, renowned for their discipline and engineering prowess, secured and maintained these vast territories, building roads, fortifications, and cities that facilitated control and integration.
The Roman Empire’s society was hierarchical, with a rigid class system. At the top were the patricians, wealthy elites who held significant political power. Below them were the plebeians, free citizens with limited political influence, and the vast numbers of slaves who formed the backbone of the economy. The family unit was central, governed by the paterfamilias, the male head who held absolute authority.
Culturally, the Romans were eclectic, absorbing and adapting elements from the civilizations they encountered, particularly the Greeks. Roman art, literature, and philosophy reflected this synthesis, creating a rich cultural tapestry. Latin, the Roman language, became the lingua franca of the Western world, influencing numerous modern languages.
Roman architecture and engineering achievements were monumental. They perfected the arch, vault, and dome, constructing enduring structures like the Colosseum, Pantheon, and aqueducts. These engineering marvels not only showcased Roman ingenuity but also served practical purposes, from public entertainment to water supply.
Recently uploaded (20)
The French Revolution Class 9 Study Material pdf free download

The French Revolution Class 9 Study Material pdf free download
TESDA TM1 REVIEWER FOR NATIONAL ASSESSMENT WRITTEN AND ORAL QUESTIONS WITH A...

TESDA TM1 REVIEWER FOR NATIONAL ASSESSMENT WRITTEN AND ORAL QUESTIONS WITH A...
Thesis Statement for students diagnonsed withADHD.ppt

Thesis Statement for students diagnonsed withADHD.ppt
Chapter 3 - Islamic Banking Products and Services.pptx

Chapter 3 - Islamic Banking Products and Services.pptx
BÀI TẬP BỔ TRỢ TIẾNG ANH GLOBAL SUCCESS LỚP 3 - CẢ NĂM (CÓ FILE NGHE VÀ ĐÁP Á...

BÀI TẬP BỔ TRỢ TIẾNG ANH GLOBAL SUCCESS LỚP 3 - CẢ NĂM (CÓ FILE NGHE VÀ ĐÁP Á...
1.4 modern child centered education - mahatma gandhi-2.pptx

1.4 modern child centered education - mahatma gandhi-2.pptx
"Protectable subject matters, Protection in biotechnology, Protection of othe...

"Protectable subject matters, Protection in biotechnology, Protection of othe...
June 3, 2024 Anti-Semitism Letter Sent to MIT President Kornbluth and MIT Cor...

June 3, 2024 Anti-Semitism Letter Sent to MIT President Kornbluth and MIT Cor...
UK Gov Report Summary
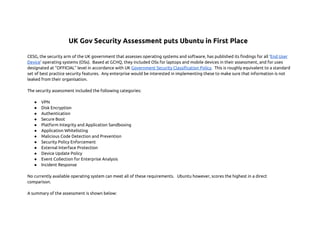
- 1. UK Gov Security Assessment puts Ubuntu in First Place CESG, the security arm of the UK government that assesses operating systems and software, has published its findings for all ‘End User Device’ operating systems (OSs). Based at GCHQ, they included OSs for laptops and mobile devices in their assessment, and for uses designated at “OFFICIAL” level in accordance with UK Government Security Classification Policy. This is roughly equivalent to a standard set of best practice security features. Any enterprise would be interested in implementing these to make sure that information is not leaked from their organisation. The security assessment included the following categories: ● ● ● ● ● ● ● ● ● ● ● ● VPN Disk Encryption Authentication Secure Boot Platform Integrity and Application Sandboxing Application Whitelisting Malicious Code Detection and Prevention Security Policy Enforcement External Interface Protection Device Update Policy Event Collection for Enterprise Analysis Incident Response No currently available operating system can meet all of these requirements. Ubuntu however, scores the highest in a direct comparison. A summary of the assessment is shown below:
- 2. Sections that were considered as having a “Significant Risk” are marked below as a red box; sections that have some notes about risks to be aware of are marked in orange; sections that passed the assessment are marked in green. Android 4.2 [1] VPN Disk Encrypti on Authenti cation Secure Boot Platfor m Integrity & Applicati on Sandbox Samsung Devices with Android 4.2[2] Apple iOS 6[3] Apple OSX 10.8 [4] Blackber ry 10.1 (EMM Corporat e) [5] Blackber ry 10.1 (EMM Regulate d) [6] Google Chrome OS 26 [7] Ubuntu 12.04 [8] Window s 7 and 8 [9] Window s 8 RT [10] Window s Phone 8 [11]
- 4. -se Analysis Incident Respons e GREEN 5 9 7 8 5 9 8 9 8 7 7 ORANGE 6 2 4 4 6 2 3 3 4 4 3 RED 1 1 1 0 1 1 1 0 0 1 2 As you can see from the table the only OS that passes as many as 9 requirements without any “Significant Risks” as independently assessed by CESG is Ubuntu 12.04 LTS. So, what about the 3 sections that have comments: VPN, Disk Encryption and Secure Boot? VPN The comments made by CESG were that “The built-in VPN has not been independently assured to Foundation Grade.” This means that the software does meet all the technical requirements of security to pass the assessment, but that the software itself has not been independently assessed to make sure that it hasn’t been tampered with during the development process. You can also see from the comments made on each detailed assessment that nobody meets this requirement fully at this time. The best you can hope for is technical compliance with independent assessment pending, which is the case for Ubuntu 12.04 or independent assessment complete but missing technical features, like Windows 8, for example. The independent assessment work for Ubuntu is being carried out by a partner and we expect CESG to provide additional guidance for meeting this requirement fully, in due course. We expect that this will be also available in time for the upcoming release of Ubuntu
- 5. 14.04 LTS and if so we expect to fully meet this requirement in this release. Disk Encryption Disk encryption is a similar case to the VPN assessment. For Ubuntu 12.04, CESG states: “LUKS and dm-crypt have not been independently assured to Foundation Grade.” LUKS and dm-crypt are used on Ubuntu to encrypt the data on the hard disk and to decrypt the data when starting up, by requesting a password from the user. Without the password, the computer cannot start the operating system or access any of the data. The technical requirements are all met, but the software has not been through an independent assessment to prove that it has not been tampered with in development. So, the independent assessment still needs to be done for LUKS and dm-crypt on Ubuntu to pass this requirement. However, every other operating system on the list has also yet to pass an independent assessment, but Ubuntu meets all the technical requirements already and we just need a sponsor to put the software through the assessment process. Secure Boot Secure boot is a Microsoft technology invented in co-operation with OEMs to ensure that software cannot be tampered with after the hardware has been shipped from the factory. It has provoked much debate in security circles, as the ability to install any software which you can control is desirable from a security perspective. The German government recently criticised secure boot [12] as preventing installation of specialised secure operating systems after sale of hardware. Ubuntu’s response, from Ubuntu 12.10 onwards is to adopt Grub2 as the default bootloader, with support for Secure Boot, but with an ability to turn off secure boot to modify the OS, if required. This is explained in John Melamut’s blog post here [13]. We believe this
- 6. gives users and enterprises the best compromise between security and ability to customise after sale. Summary All in all Ubuntu 12.04 LTS stacks up as the most secure of the current desktop and mobile operating systems. Supported by Canonical with free security updates for 5 years, and without malware problems, it’s hard to beat in official public sector applications. We are working hard to close the gap and make Ubuntu clearly stand out as the most trustworthy operating system for the future and we hope to make excellent progress before our next LTS release in April 2014, 14.04 LTS, which will be even better. Darryl Weaver Sales Engineer, EMEA, Canonical Further Reading The original CESG guidance is available to read here: https://www.gov.uk/government/collections/end-user-devices-security-guidance--2 References [1] https://www.gov.uk/government/publications/end-user-devices-security-guidance-android-42 [2] https://www.gov.uk/government/publications/end-user-devices-security-guidance-samsung-devices-with-android-42 [3] https://www.gov.uk/government/publications/end-user-devices-security-guidance-apple-ios-6 [4] https://www.gov.uk/government/publications/end-user-devices-security-guidance-apple-os-x-108 [5] https://www.gov.uk/government/publications/end-user-devices-security-guidance-blackberry-101-emm-corporate [6] https://www.gov.uk/government/publications/end-user-devices-security-guidance-blackberry-101-emm-regulated [7] https://www.gov.uk/government/publications/end-user-devices-security-guidance-google-chrome-os-26 [8] https://www.gov.uk/government/publications/end-user-devices-security-guidance-ubuntu-1204 [9] https://www.gov.uk/government/publications/end-user-devices-security-guidance-windows-7-and-windows-8 [10] https://www.gov.uk/government/publications/end-user-devices-security-guidance-windows-8-rt [11] https://www.gov.uk/government/publications/end-user-devices-security-guidance-windows-phone-8 [12] http://www.bmi.bund.de/SharedDocs/Downloads/DE/Themen/OED_Verwaltung/Informationsgesellschaft/trusted_computing_eng.html
