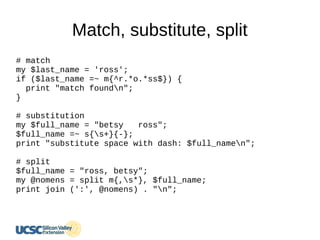
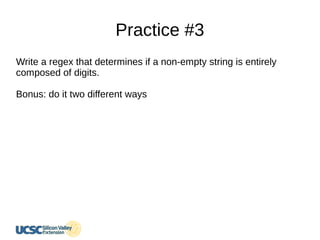
This document serves as an introductory guide to regular expressions (regex) for beginners, focusing on Perl-compatible regex and offering practical coding examples. It covers various concepts such as matching, substitution, character classes, and quantifiers, as well as offering exercises for application. The guide emphasizes understanding regex through direct practice and application in text manipulation tasks.
![Character class
split m{[.,;s]+}, $names;
$names =~ s{[^a-zA-Z0-9]}{-}g;
# leading ^ will negate the character class
# g modifier for global
# run character_class.pl](https://image.slidesharecdn.com/regularexpressionucsc-180111070453/85/Regular-Expression-25-320.jpg)
![Global match
@list = $str =~ m{[a-z]+}g;
$scalar = $str =~ m{[a-z]+}g;
$str =~ s{[^a-z]+}{-}g;](https://image.slidesharecdn.com/regularexpressionucsc-180111070453/85/Regular-Expression-28-320.jpg)
![Grouping
($prefix, $last_name)
= $str =~ m{(mr[s]?[.]?)s+(S+)}i;](https://image.slidesharecdn.com/regularexpressionucsc-180111070453/85/Regular-Expression-29-320.jpg)
![Alternation
($prefix, $last_name) = $str
=~ m{(mister|misses|miss|mr[s]?[.]?)s+(S+)}i;](https://image.slidesharecdn.com/regularexpressionucsc-180111070453/85/Regular-Expression-30-320.jpg)
![Alternation
non-capturing group
($prefix, $last_name) = $str
=~ m{(mister|miss(?:es)?|mr[s]?[.]?)s+(S+)}i;
# the 'es' is in a non-capturing group](https://image.slidesharecdn.com/regularexpressionucsc-180111070453/85/Regular-Expression-31-320.jpg)
![Alternation
non-capturing group
($prefix, $last_name) = $str
=~ m{(mi(?:ster|ss(?:es)?)|mr[s]?[.]?)s+(S+)}i;
# Too much non-capturing groups. Hard to read](https://image.slidesharecdn.com/regularexpressionucsc-180111070453/85/Regular-Expression-32-320.jpg)
![Practice #4
# what value is printed for year?
my $str = "Copyright 2013";
my $year;
($year) = $str =~ m{.*([0-9]+)};
print "$yearn";](https://image.slidesharecdn.com/regularexpressionucsc-180111070453/85/Regular-Expression-34-320.jpg)
![Greedy vs. non-greedy
($year) = $str =~ m{.*([0-9]+)};
# $year is 3
# greedy maximizes the matching
($year) = $str =~ m{.*?([0-9]+)};
# $year is 2013
# non-greedy minimizes the matching](https://image.slidesharecdn.com/regularexpressionucsc-180111070453/85/Regular-Expression-36-320.jpg)
![Back reference
my $str = "****Spangled****";
my ($star, $word) = $str =~ m{^([*]+)([^*]+)1$};](https://image.slidesharecdn.com/regularexpressionucsc-180111070453/85/Regular-Expression-38-320.jpg)