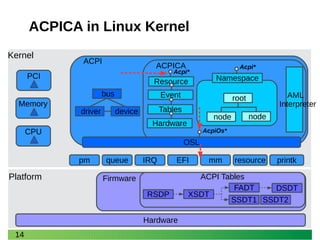
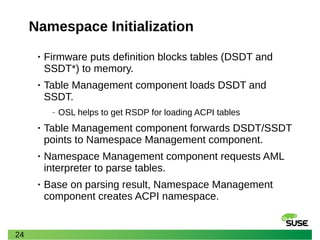
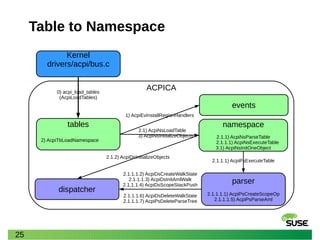
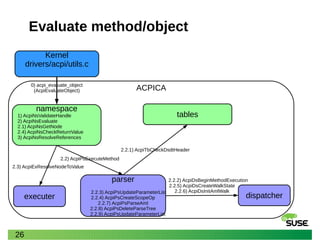
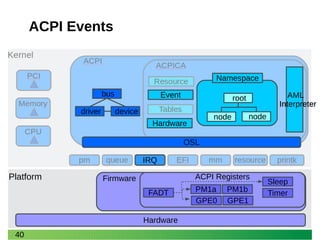
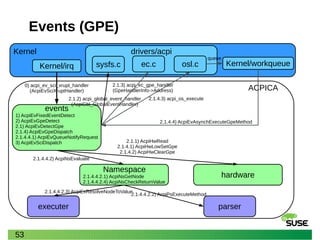
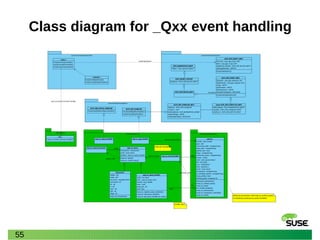
This document summarizes a presentation about profiling the ACPI namespace and event handling. It discusses the key components of ACPICA and how it interacts with the Linux kernel. It describes how definition blocks are parsed to build the ACPI namespace, and how fixed events and general purpose events (GPEs) are handled through event detection and dispatching to handlers in the kernel or by evaluating control methods.
![3
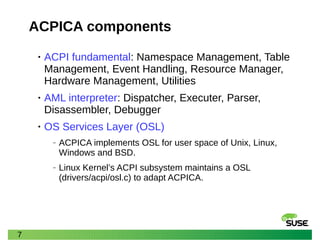
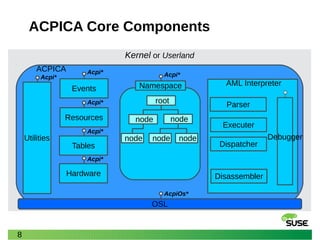
ACPICA
• The ACPI Component Architecture (CA) is the core
of Advanced Configuration and Power Interface
(ACPI) subsystem in Linux kernel.
• The ACPICA provides the fundamental ACPI
services that are independent of any operating
system. [1]
• Mainly maintained by Intel
‒ https://github.com/acpica/acpica.git](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-3-320.jpg)
![4
ACPICA (cont.)
• ACPICA’s services include an AML
parser/interpreter, ACPI namespace management,
ACPI table management and event handling [1].
• The OS Services Layer (OSL) is a conversion layer
between the OS-independent ACPICA to a particular
host operating system. [1]](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-4-320.jpg)
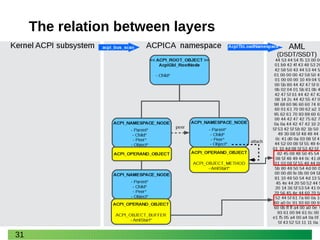
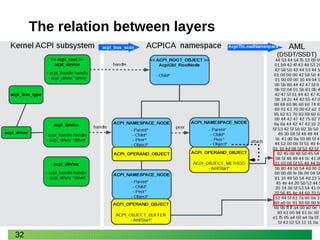
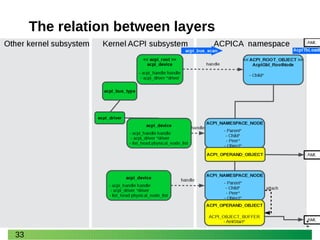
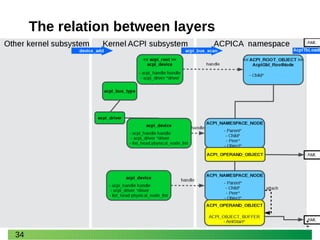
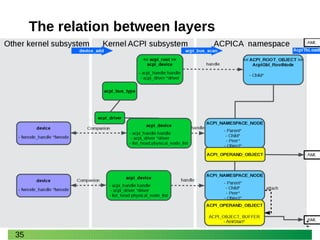
![12
ACPI host and ACPICA
• OSL in Linux Kernel: drivers/acpi/osl.c
• ACPICA-to-host: All ACPICA-to-host interactions
pass through the OSL via direct calls to the AcpiOs*
interfaces from ACPICA. [1]
• Host-to-ACPICA
‒ Synchronous: the host making direct calls to the various
public Acpi* interfaces. [1]
‒ Asynchronous: The host calls ACPICA to install an
appropriate handler at initialization time. This handler is
then invoked by ACPICA whenever the requested event
occurs. (handle fixed events or GPE) [1]](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-12-320.jpg)
![16
ACPI Tables
• Definition blocks tables
‒ AML (ACPI Machine Language) format
‒ DSDT (differentiated system description table), SSDT
(secondary system description tables)
• Data tables
‒ TDL (Table Definition Language)
‒ FADT, MADT, ECDT, SRAT, etc. - essentially any table
other than a DSDT or SSDT. [2]
• The iasl tool supports AML and TDL](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-16-320.jpg)
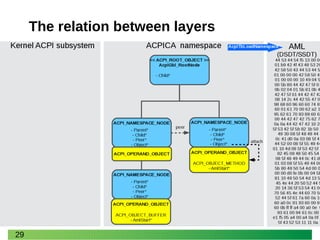
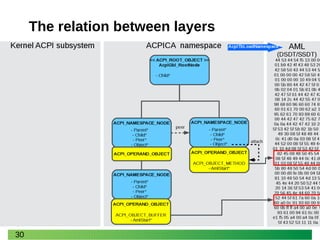
![17
ACPI Namespace
• The ACPI Namespace is a large data structure that
is constructed and maintained by the ACPICA
Subsystem component. [1]
• Constructed primarily from the AML defined within
an ACPI Differentiated System Description Table
(DSDT), the namespace contains a hierarchy of
named ACPI objects. [1]
root
Namespace
node node](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-17-320.jpg)
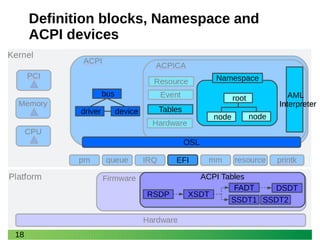
![19
Definition blocks, Namespace and
ACPI devices
[1]Load](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-19-320.jpg)
![20
Definition blocks, Namespace and
ACPI devices
[1]Load
[2]](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-20-320.jpg)
![21
Definition blocks, Namespace and
ACPI devices
[1]Load
[2]
[3] Parse](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-21-320.jpg)
![22
Definition blocks, Namespace and
ACPI devices
[1]Load
[2]
[3] Parse
[4] handle](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-22-320.jpg)
![23
Definition blocks, Namespace and
ACPI devices
[1]Load
[2]
[3] Parse
PCI
CPU
Memory
Companion
Companion
Companion
PCI
CPU
Memory
[4] handle](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-23-320.jpg)
![38
Event types in ACPICA
• ACPI Fixed Events and General Purpose Events
(GPEs)
‒ System Control Interrupts (SCIs) be generated
• Event types in control method
‒ Notify events that are generated via the execution of the
ASL Notify keyword in a control method. [1]
‒ Events that are caused by accesses to an address space
or operation region during the execution of a control
method. [1]](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-38-320.jpg)
![41
ACPI Events
[1]Set](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-41-320.jpg)
![42
ACPI Events
[1]Set
[2]SCI[2]SCI](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-42-320.jpg)
![43
ACPI Events
[1]Set
[2]SCI[2]SCI
[3]
[3]Read
Clear](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-43-320.jpg)
![44
ACPI Events (Fixed Event)
[1]Set
[2]SCI[2]SCI
[3]
[3]Read
Clear
[4] Button](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-44-320.jpg)
![45
ACPI Events (Fixed Event)
[1]Set
[2]SCI[2]SCI
[3]
[3]Read
Clear
[4] Button
Input [5] input
[5]Keycode](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-45-320.jpg)
![46
ACPI Events (GPE)
[1]Set
[2]SCI[2]SCI
[3]
[3]Read
Clear
_Exx _Lxx
_GPE](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-46-320.jpg)
![47
ACPI Events (GPE)
[1]Set
[2]SCI[2]SCI
[3]
[3]Read
Clear
[4]
_Exx _Lxx
_GPE
[5]](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-47-320.jpg)
![48
ACPI Events (GPE)
[1]Set
[2]SCI[2]SCI
[3]
[3]Read
Clear
[4]
_Exx _Lxx
_GPE
[5]
[6]Access
Address space
[6] Notify](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-48-320.jpg)
![49
ACPI Events (GPE)
[1]Set
[2]SCI[2]SCI
[3]
[3]Read
Clear
[4]
_Exx _Lxx
_GPE
[5]
[6]Access
Address space
[6] NotifyPCI
CPU
Memory
PCI
CPU
Memory
Interactive
Interactive
interactive](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-49-320.jpg)
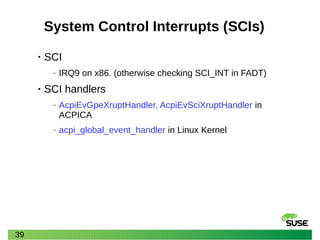
![50
Fixed Events
• Fixed Events
‒ ACPI events that have a predefined meaning in the ACPI
specification. e.g. power button, timer overflows.
‒ These events are handled directly by the OS handlers. [2]
‒ ACPI register: PM1 = PM1a | PM1b
‒ PM1x_STS.8: PWRBTN_STS
‒ PM1x_STS.9: SLPBTN_STS
‒ PM1x_STS.10: RTC_STS
….](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-50-320.jpg)
![51
ACPICA
Events (fixed)
events
1) AcpiEvFixedEventDetect
1.3) AcpiEvFixedEventDispatch
2) AcpiEvGpeDetect
3) AcpiEvSciDispatch
Kernel
0) acpi_ev_sci_xrupt_handler
(AcpiEvSciXruptHandler)
1.1) AcpiHwRegisterRead
Kernel/irq
drivers/acpi
1.2) acpi_global_event_handler
(AcpiGbl_GlobalEventHandler)
bus.csysfs.c
1.3.1) acpi_device_fixed_event
(AcpiGbl_FixedEventHandlers[Event].Handle)
button.c
1.3.1.x) notify
hardware](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-51-320.jpg)
![52
GPEs
• GPEs
‒ GPEs are ACPI events that are not predefined by the ACPI
specification.
‒ These events are usually handled by evaluating control
methods, which are objects in the namespace and can
access system hardware.
‒ ACPI registers: GPE0_BLK, GPE1_BLK
‒ Control Methods: _GPE._Lxx, _GPE._Exx
‒ X86: reference GPE0_STS register in the Intel I/O Controller Hub
(ICH) datasheet.
‒ watch -n 1 cat /sys/firmware/acpi/interrupts/gpe[012]
[0123456789ABCDEF]](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-52-320.jpg)

![58
Reference
• [1] ACPI Component Architecture User Guide and
Programmer Reference Revision 6.2, May 31, 2017
• [2] Advanced Configuration and Power Interface
(ACPI) Specification Version 6.3, January 2019](https://image.slidesharecdn.com/profiling-the-acpica-20190919-191006013352/85/Profiling-the-ACPICA-Namespace-and-Event-Handing-58-320.jpg)



