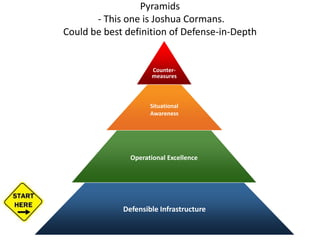
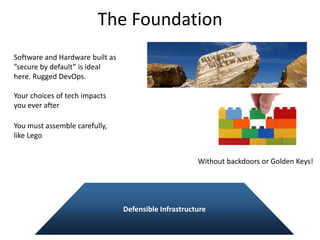
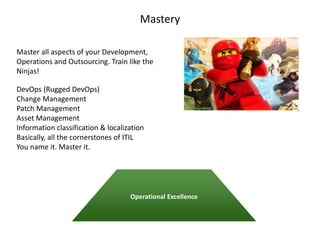
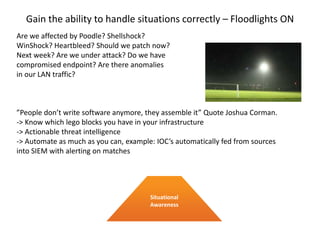
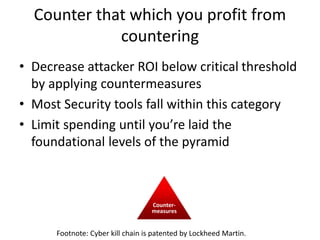
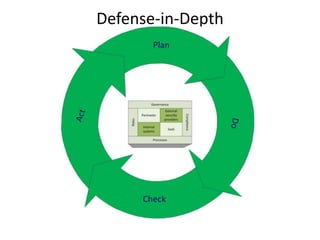
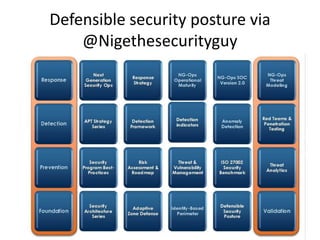
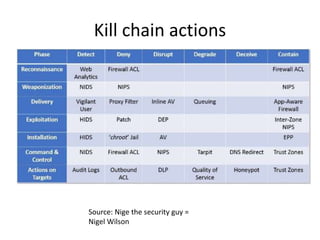
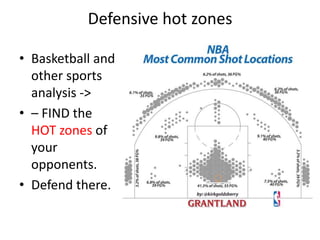
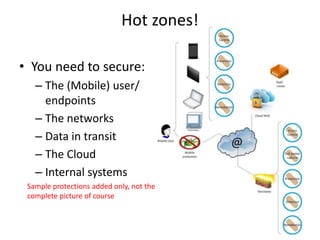
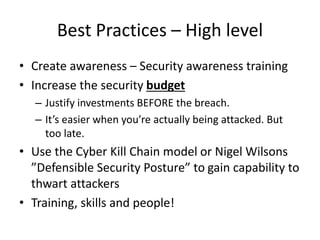
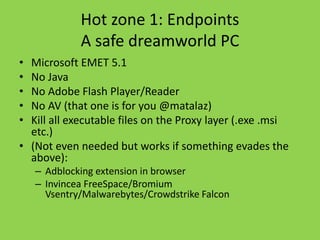
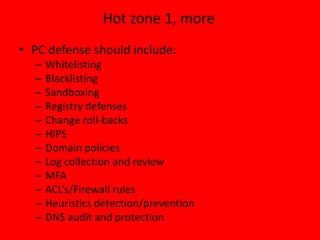
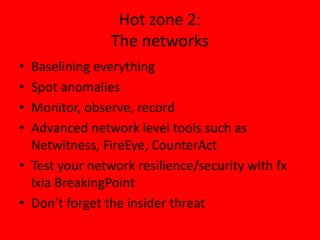
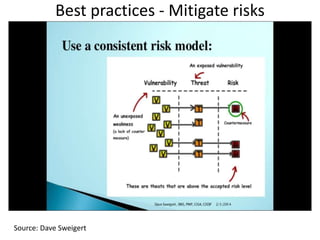
The document discusses the rising threats in cybersecurity and emphasizes the inadequacy of current tools in combatting these attacks. It suggests a strategic approach to security that includes training, situational awareness, and best practices like creating defensible infrastructure and using the cyber kill chain model. Overall, it highlights the importance of a proactive and informed cybersecurity strategy rather than relying solely on compliance.