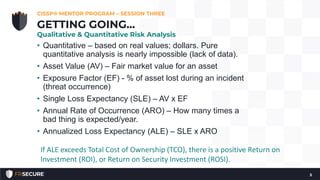
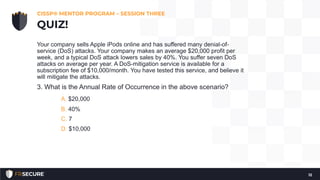
This document summarizes session 3 of a 2019 CISSP mentor program. It discusses risk analysis, including qualitative and quantitative approaches. Key terms like asset value, exposure factor, single loss expectancy, and annualized loss expectancy are defined. Examples of risk analysis calculations are provided. The session also covered risk management processes, risk choice options, and included a quiz to test understanding.