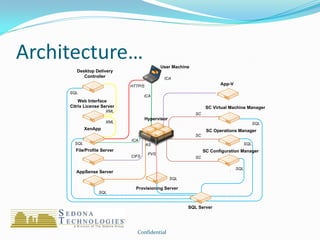
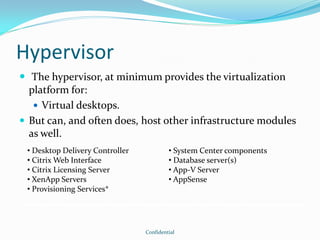
The document outlines the considerations for implementing Citrix XenDesktop as a desktop virtualization strategy, highlighting its flexibility, cost-effectiveness, and performance. It discusses the architecture, components, and user experience enhancements while posing several critical questions for organizations to define their goals and deployment strategy. Key factors include network and storage management, user categorization, and application delivery methods.